Tag Archives: microsoft
Looking value in another sheet and returns the ID
Hi All,
I have excel file in that i have 2 sheets S1 (orange) & S2 (blue). I have CID column in S2 and I want to check D column value of S2 in C column of S1 and then i want to return the ID in CID column
for example, I have 5 entries in S2 sheet
BadakhshanAfghanistanBadakhshanAfghanistanBadakhshanAfghanistanBadakhshanAfghanistanBadakhshanAfghanistanBadakhshanAfghanistan
and in S1 i have this
CONCAT2ID
BadakhshanAfghanistan1
So I want the result in S2 to be
CONCAT1 CID
BadakhshanAfghanistan1BadakhshanAfghanistan1BadakhshanAfghanistan1BadakhshanAfghanistan1BadakhshanAfghanistan1BadakhshanAfghanistan1
i have added excel sheet as well for your reference. Thanks 🙂
Hi All, I have excel file in that i have 2 sheets S1 (orange) & S2 (blue). I have CID column in S2 and I want to check D column value of S2 in C column of S1 and then i want to return the ID in CID column for example, I have 5 entries in S2 sheetBadakhshanAfghanistanBadakhshanAfghanistanBadakhshanAfghanistanBadakhshanAfghanistanBadakhshanAfghanistanBadakhshanAfghanistan and in S1 i have this CONCAT2IDBadakhshanAfghanistan1 So I want the result in S2 to beCONCAT1 CIDBadakhshanAfghanistan1BadakhshanAfghanistan1BadakhshanAfghanistan1BadakhshanAfghanistan1BadakhshanAfghanistan1BadakhshanAfghanistan1 i have added excel sheet as well for your reference. Thanks 🙂 Read More
Start and Wait for approval
I want to utilize the functionality provided by the Microsoft Graph API to initiate and await approval for timesheets stored in SharePoint. Could someone please assist me in understanding the process for implementing this?
I want to utilize the functionality provided by the Microsoft Graph API to initiate and await approval for timesheets stored in SharePoint. Could someone please assist me in understanding the process for implementing this? Read More
Update 2403 for Microsoft Configuration Manager current branch is now available.
Update 2403 for Configuration Manager current branch is available as an in-console update. Apply this update on sites that run version 2211 or later. When installing a new site, it will also be available as a baseline version soon after general availability. This article summarizes the changes and new features in Configuration Manager, version 2403.
Site infrastructure
Starting Configuration Manager version 2403, Microsoft Azure Active Directory is renamed to Microsoft Entra ID within Configuration Manager.
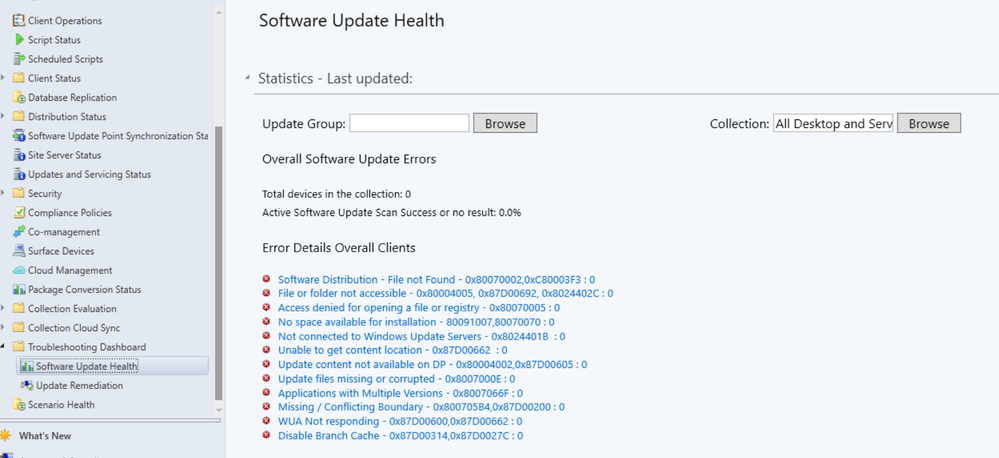
Automated diagnostic Dashboard for Software Update Issues
A new dashboard is added to the console under monitoring workspace, which shows the diagnosis of the software update issues in your environment this feature can easily identify any issues related to software updates. You can fix software update issues based on troubleshooting documentations.
Special credit to Shankar Subramanian and Smita Jadhav for their details and troubleshooting notes.
For more information, see Software update health dashboard.
Users can now use the global search box in CM console, which streamlines the search experience and centralizes access to information. This feature enhances the overall usability, productivity and effectiveness of CM. Users no longer need to navigate through multiple nodes or sections/ folders to find information they require, saving valuable time and effort.
For more information, see Improvements to console search.
You can now organize scripts by using folders. This change allows for better categorization and management of scripts. Full Administrator and Operations Administrator roles can manage the folders.
For more information, see Folder support for scripts.
HTTPS or Enhanced HTTP should be enabled for client communication from this version of Configuration Manager
HTTP-only communication is deprecated, and support is removed from this version of Configuration Manager. Enable HTTPS or Enhanced HTTP for client communication.
For more information, see Enable site system roles for HTTPS or Enhanced HTTP. and Deprecated features
Windows Server 2012/2012 R2 operating system site system roles are not supported from this version of Configuration Manager
Starting 2403, Windows Server 2012/2012 R2 operating system site system roles aren’t supported in any CB releases. Clients with extended support (ESU) will continue to support.
For more information, see Supported-operating-systems-for-site-system-servers.
Any configured Resource access profiles and deployments block Configuration manager upgrade. Consider deleting them and moving the co-management workload for Resource Access (if co-managed) to Intune.
For more information, see FAQ and Resource access policies are no longer supported.
A new parameter SoftwareUpdateO365Language is now added to PowerShell Save-CMSoftwareUpdate cmdlet. Customers now don’t have to check a specific language in the SUP Properties (causing a metadata download for that language for all updates).
PowerShell Commandlet: Save-CMSoftwareUpdate – SoftwareUpdateO365Language <language name> (<region name>)”
Note
Languages need to be in O365 format to be consistent with Admin Console UI. E.g. “Hungarian (Hungary)”.
Configuration Manager operating system deployment support is now added on Windows 11 ARM 64 devices. Currently Importing and customizing Arm 64 boot images, Wipe and load TS, Media creation TS, WDS PXE for Arm 64 and CMPivot is supported.
Administrators while deploying the “Install Software Package” via Dynamic variable with “Continue on error” unchecked to clients, will not be notified with task sequence failures even if package versions on the distribution point are updated.
For more information, see Options for Install Application.
The option to upgrade Configuration Manager 2403 is blocked if you’re running cloud management gateway V1 (CMG) as a cloud service (classic). All CMG deployments should use a virtual machine scale set.
For more information, see Check for a cloud management gateway (CMG) as a cloud service (classic).
Learn about support changes before they’re implemented in removed and deprecated items.
System Center Update Publisher (SCUP) and integration with ConfigMgr planned end of support Jan 2024.
For more information, see Removed and deprecated features for Configuration Manager.
This release includes the following improvements to BitLocker:
Starting in this release, this feature ensures proper verification of key escrow and prevents message drops. We now validate whether the key is successfully escrowed to the database, and only on successful escrow we add the key protector.
This feature now prevents a potential data loss scenario where BitLocker is protecting the volumes with keys that are never backed up to the database, in any failures to escrow happens.
For more information on BitLocker management, see Deploy BitLocker management. and Plan for BitLocker management..
From this version of Configuration Manager, the Windows 11 readiness dashboard shows charts for Windows 23H2.
Defender Exploit Guards policy for controlled folder now accepts regex in the file path for apps. For example, [C:FolderSubfolderapp?.exe] [C:Folder1Sub*Name]
At this time, version 2403 is released for the early update ring. To install this update, you need to opt in. For more information, see Early update ring.
Thank you,
The Configuration Manager team
Additional resources:
What’s New in Configuration Manager
Documentation for Configuration Manager
Microsoft Configuration Manager announcement
Microsoft Configuration Manager vision statement
Evaluate Configuration Manager in a lab
Upgrade to Configuration Manager
Configuration Manager Forums
Configuration Manager Support
Report an issue
Provide suggestions
Microsoft Tech Community – Latest Blogs –Read More
Wired for Hybrid – What’s New in Azure Networking – April 2024 edition
Hello Folks,
Azure Networking is the foundation of your infrastructure in Azure. Each month we bring you an update on What’s new in Azure Networking.
In this blog post, we’ll cover what’s new with Azure Networking in April 2024. In this blog post, we will cover the following announcements and how they can help you.
Listener TLS certificates management in the Azure portal
Application Gateway for Containers
Application Gateway (v2) IPv6 support
Microsoft open sources Retina: A cloud-native container networking observability platform
Azure Virtual Network encryption now in additional regions
Listener TLS certificates management in the Azure portal
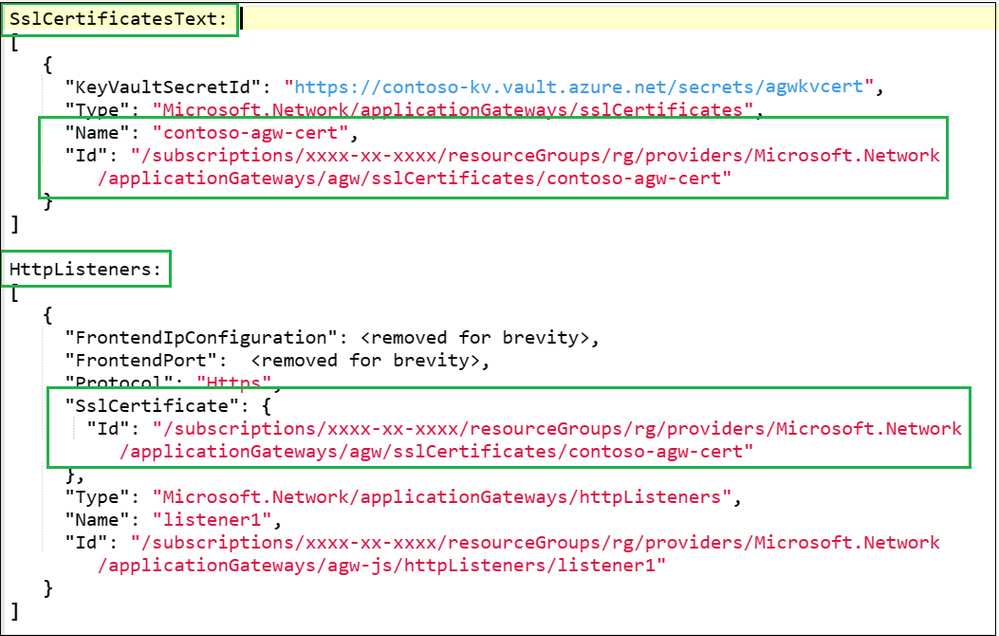
With this GA release, you can more easily manage TLS certificates for your Application Gateway workloads in the Azure Portal.
The Azure Application Gateway is a proxy load balancer that operates at Layer-7, the application layer of the OSI model. Now it supports Layer-4 proxy with TCP and TLS protocols as well. This provides scalable, highly available, and secure application delivery. One of its key features is the ability to secure client traffic through TLS termination, which requires TLS server certificates for listeners. For large gateways with multiple HTTPS or TLS listeners, this means managing multiple .PFX certificates.
For certificate management in the portal, you can list and manage your certificates.
Expiry
Common Name
Thumbprint
Issuer Name
Each certificate includes the following details for quick identification:
Managing certificates in any organization can be a challenge. This is a great addition for reducing friction for admins responsible for secure workloads utilizing certificates.
References:
Application Gateway TCP/TLS proxy overview (Preview)
Listener TLS certificate management in Application Gateway
Quickstart: Direct web traffic using the portal – Azure Application Gateway
TLS termination with Azure Key Vault certificates
General availability: Application Gateway for Containers
Application Gateway for Containers is GA. With this release, you get application (layer 7) load balancing and dynamic traffic management capabilities for workloads running in a Kubernetes cluster.
Application Gateway for Containers is the evolution of the Application Gateway Ingress Controller (AGIC), a Kubernetes application that enables Azure Kubernetes Service (AKS) customers to use Azure’s native Application Gateway application load-balancer. In its current form, AGIC monitors a subset of Kubernetes Resources for changes and applies them to the Application Gateway, utilizing Azure Resource Manager (ARM).
Features – Public preview and GA has added support for Custom Health Probes, URL Redirect, URL / Header Rewrite.
Controller High Availability – Have peace of mind if a node goes down, changes within your cluster will continue to be propagated to the network.
Gateway API v1 – Bring the familiarity and role based access control provided by Gateway API to your network configuration.
Additional Region Availability – Take advantage of Application Gateway for Containers in a region closest to you.
SLA for Production Workloads – Feel confident in running your production workloads with Application Gateway for Containers.
References:
What is Application Gateway for Containers?
Application Gateway for Containers components
Quickstart: Deploy Application Gateway for Containers ALB Controller
What is Azure Application Gateway Ingress Controller?
Application Gateway (v2) IPv6 support
We are announcing that IPv6 support for Azure Application Gateway (v2) is now generally available.
With the addition of IPv6 support, you can take advantage of the increased address space and improved routing efficiency that IPv6 provides. This is especially important for customers who are running out of IPv4 addresses or who need to support IPv6 clients.
To get started with IPv6 support for Azure Application Gateway (v2), simply create a new Application Gateway and select both IPv4 and IPv6 frontends during the creation process. You can also find more information about IPv6 support in our documentation.
References:
Configure Application Gateway with a frontend public IPv6 address using the Azure portal
What is Azure Application Gateway v2?
Microsoft open sources Retina: A cloud-native container networking observability platform
Retina is an open-source Kubernetes Network Observability platform designed to assist with DevOps, SecOps, and compliance use cases. It acts as a centralized hub for monitoring the health, security, and performance of applications and networks within Kubernetes clusters. The platform caters to Cluster Network Administrators, Cluster Security Administrators, and DevOps Engineers.
Provides actionable network insights for cloud-native applications: Retina offers users a way to see how their containerized microservices interact on the network, helping them troubleshoot issues like latency, packet drops and many more.
Non-intrusive and easy to use: Retina works with existing applications without requiring any code changes and provides users with simple ways to observe and troubleshoot network issues.
Supports diverse environments: Designed to be adaptable, Retina works seamlessly with any CNI’s (container network interface), OS, or cloud provider, making it a valuable tool across different environments.
Resources:
Introduction to Retina
Microsoft open sources Retina: Announcement
Azure Virtual Network encryption now in additional regions
Whenever Azure customer traffic moves between datacenters, Microsoft applies a data-link layer encryption method using the IEEE 802.1AE MAC Security Standards (MACsec). This encryption is implemented to secure the traffic outside physical boundaries not controlled by Microsoft or on behalf of Microsoft. This method is applied from point-to-point across the underlying network hardware. Virtual network encryption enables you to encrypt traffic between Virtual Machines and Virtual Machines Scale Sets within the same virtual network. It also encrypts traffic between regionally and globally peered virtual networks. Virtual network encryption enhances existing encryption in transit capabilities in Azure.
With Virtual Network encryption, customers can enable encryption of traffic between Virtual Machines and Virtual Machines Scale Sets within the same virtual network and between regionally and globally peered virtual networks. This new feature enhances the existing encryption in transit capabilities in Azure.
Azure Virtual Network encryption is available in the following additional regions:
West Us
West US 2
East US 2
US East
Europe North
Europe West
France Central
India Central
UAE North
East Asia
Japan West
Japan East
Resources:
What is Azure Virtual Network?
What is Azure Virtual Network encryption?
That’s it for this month.
Cheers
Pierre
Microsoft Tech Community – Latest Blogs –Read More
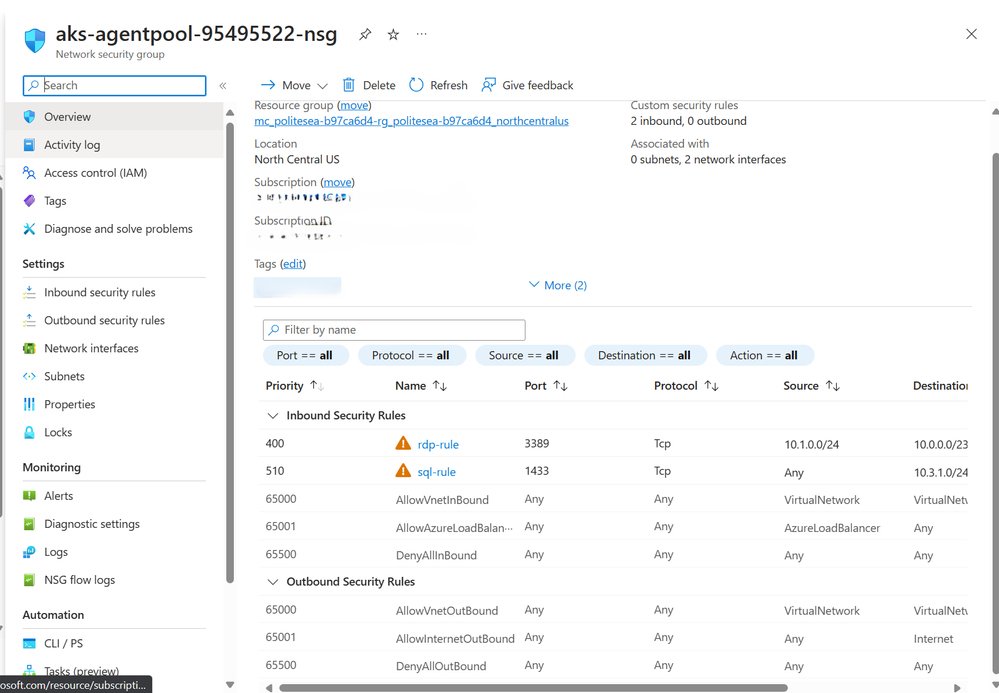
Perform bulk NSG rule rollout across multiple target NSGs
Network Security Groups (NSGs) are a fundamental aspect of Azure networking, providing a layer of security to control traffic flow within virtual networks. However, managing NSG rules across multiple NSGs can be a daunting task, especially when done manually. This article introduces a powerful PowerShell script that allows you to perform bulk NSG rule rollouts across multiple target NSGs, saving you time and ensuring consistency across your network.
The Challenge
In a large-scale Azure environment, you may have hundreds or even thousands of NSGs, each with its own set of rules. Updating these rules manually is not only time-consuming but also prone to errors. Furthermore, it’s difficult to ensure consistency across all NSGs, which is crucial for maintaining a secure and reliable network.
Scenario
The requirements were to empower the customers using an automation that could perform the mass assignment, updating, or deletion of the NSG rules across a set of NSGs. The NSG rules would have a common definition across all the NSGs except the source address prefix range and the destination address prefix range that would change based on the NSGs subnet address range, and if the rule’s direction is outbound or inbound.
The Solution
The solution consists of three PowerShell scripts that perform add, update, and delete operations on Network Security Group (NSG) rules in Azure.
Add Operation
Our PowerShell script, nsg_rule_add_csv.ps1, simplifies the process of adding NSG rules in bulk. The script reads from a CSV file, nsg_rule_definitions.csv, which contains the definitions of the rules to be added. It then applies these additions to the target NSGs specified in another CSV file, target_nsgs.csv. If the rule already exists in the NSG, the script skips the addition. Otherwise, it adds the rule to the NSG. Find the code for nsg_rule_add_csv.ps1.
function Add-NsgRule ($SubscriptionId, $ResourceGroup, $NsgName, $ruleDefinition, $SubnetAddressPrefix) {
if ($ruleDefinition.Direction -ieq ‘Inbound’) {
$rule = New-AzNetworkSecurityRuleConfig -Name $ruleDefinition.Name -Description $ruleDefinition.Description -Priority $ruleDefinition.Priority -Direction $ruleDefinition.Direction -Access $ruleDefinition.Access -SourceAddressPrefix $ruleDefinition.SourceAddressPrefix -SourcePortRange $ruleDefinition.SourcePortRange -DestinationAddressPrefix $subnetAddressPrefix -DestinationPortRange $ruleDefinition.DestinationPortRange -Protocol $ruleDefinition.Protocol
} elseif ($ruleDefinition.Direction -ieq ‘Outbound’) {
$rule = New-AzNetworkSecurityRuleConfig -Name $ruleDefinition.Name -Description $ruleDefinition.Description -Priority $ruleDefinition.Priority -Direction $ruleDefinition.Direction -Access $ruleDefinition.Access -SourceAddressPrefix $subnetAddressPrefix -SourcePortRange $ruleDefinition.SourcePortRange -DestinationAddressPrefix $ruleDefinition.DestinationAddressPrefix -DestinationPortRange $ruleDefinition.DestinationPortRange -Protocol $ruleDefinition.Protocol
}
Try {
# Switch the context to the appropriate subscription
Set-AzContext -SubscriptionId $SubscriptionId -ErrorAction Stop
$nsg = Get-AzNetworkSecurityGroup -Name $NsgName -ResourceGroupName $ResourceGroup -ErrorAction Stop
$nsg.SecurityRules.Add($rule)
Set-AzNetworkSecurityGroup -NetworkSecurityGroup $nsg -ErrorAction Stop
Write-Host “Rule added to NSG: $NsgName ($ResourceGroup)”
$timestamp = Get-Date -Format “yyyy-MM-dd_HH-mm-ss”
$logEntry = “$timestamp, $($ruleDefinition.Name), $nsgName, $ResourceGroup, Added Successfully”
$logFileName = “$($run_time)_$($ruleDefinition.Name)_add_success.log”
Add-Content -Path “.$logFileName” -Value $logEntry
} Catch {
$timestamp = Get-Date -Format “yyyy-MM-dd_HH-mm-ss”
$logEntry = “$timestamp, $($NsgName), $($_.Exception.Message)”
$logFileName = “$($run_time)_$($ruleDefinition.Name)_add_fail.log”
Add-Content -Path “.$logFileName” -Value $logEntry
Write-Error “Failed to add rule to NSG: $NsgName ($ResourceGroup) – $($_.Exception.Message)”
}
}
Update Operation
Our PowerShell script, nsg_rule_update_csv.ps1, simplifies the process of updating NSG rules in bulk. The script reads from a CSV file, nsg_rule_definitions_update.csv, which contains the rule definitions to be updated. It then applies these updates to the target NSGs specified in another CSV file, target_nsgs.csv. If the rule exists in the NSG, and the rule name (immutable) and old rule priority (additional input in the nsg_rule_definitions_update.csv for validating the rule before update operation) matches, the script updates the rule to the new rule definition. If the rule doesn’t exist, it logs an error message. Find the code for nsg_rule_update_csv.ps1.
function Update-NsgRule ($SubscriptionId, $ResourceGroup, $NsgName, $ruleDefinition, $subnetaddrprefix) {
Try {
# Switch the context to the appropriate subscription
Set-AzContext -SubscriptionId $SubscriptionId
# Get the Network Security Group
$nsg = Get-AzNetworkSecurityGroup -Name $NsgName -ResourceGroupName $ResourceGroup -ErrorAction Stop
$existingRule = Get-AzNetworkSecurityRuleConfig -Name $ruleDefinition.Name -NetworkSecurityGroup $nsg -ErrorAction Stop
if ($existingRule) {
# if existing PN= OLd PN-> Update
# existing PN != OLd PN -> throw error
if ($existingRule.Priority -eq $ruleDefinition.OldPriority) {
$existingRule.Priority = $ruleDefinition.Priority
$existingRule.Direction = $ruleDefinition.Direction
$existingRule.SourceAddressPrefix = [System.Collections.Generic.List[string]]@($ruleDefinition.SourceAddressPrefix)
$existingRule.DestinationAddressPrefix = [System.Collections.Generic.List[string]]@($ruleDefinition.DestinationAddressPrefix)
$existingRule.SourcePortRange = [System.Collections.Generic.List[string]]@($ruleDefinition.SourcePortRange)
$existingRule.DestinationPortRange = [System.Collections.Generic.List[string]]@($ruleDefinition.DestinationPortRange)
$existingRule.Description = $ruleDefinition.Description
$existingRule.Protocol = $ruleDefinition.Protocol
$existingRule.Access = $ruleDefinition.Access
if ($ruleDefinition.Direction -ieq ‘Inbound’ ) {
$existingRule.DestinationAddressPrefix = [System.Collections.Generic.List[string]]@($subnetaddrprefix)
} elseif ($ruleDefinition.Direction -ieq ‘Outbound’) {
$existingRule.SourceAddressPrefix = [System.Collections.Generic.List[string]]@($subnetaddrprefix)
}
# Update the existing rule
$nsg | Set-AzNetworkSecurityRuleConfig -Name $existingRule.Name -Description $existingRule.Description -Access $existingRule.Access -Protocol $existingRule.Protocol -Direction $existingRule.Direction -Priority $existingRule.Priority -SourceAddressPrefix $existingRule.SourceAddressPrefix -SourcePortRange $existingRule.SourcePortRange -DestinationAddressPrefix $existingRule.DestinationAddressPrefix -DestinationPortRange $existingRule.DestinationPortRange -ErrorAction Stop
# Save the changes to the Network Security Group
$nsg | Set-AzNetworkSecurityGroup -ErrorAction Stop
$timestamp = Get-Date -Format “yyyy-MM-dd_HH-mm-ss”
$logEntry = “$timestamp, $($ruleDefinition.Name), $nsgName, $ResourceGroup, Updated Successfully”
$logFileName = “$($run_time)_$($ruleDefinition.Name)_update_success.log”
Add-Content -Path “.$logFileName” -Value $logEntry
Write-Host “Rule updated in NSG: $NsgName ($ResourceGroup)”
}
else{
$errorMessage = “Cannot update the rule in NSG: $NsgName ($ResourceGroup) – Priority does not match for rule in NSG.”
Write-Error $errorMessage
$logFileName = “$($run_time)_$($ruleDefinition.Name)_update_fail.log”
Add-Content -Path “.$logFileName” -Value $logEntry
}
}
else {
Write-Error “Rule ‘$($ruleDefinition.Name)’ not found in NSG: $NsgName ($ResourceGroup)”
$timestamp = Get-Date -Format “yyyy-MM-dd_HH-mm-ss”
$logEntry = “$timestamp, $($NsgName), Rule not found in NSG.”
$logFileName = “$($run_time)_$($ruleDefinition.Name)_update_fail.log”
Add-Content -Path “.$logFileName” -Value $logEntry
}
}
Catch {
$timestamp = Get-Date -Format “yyyy-MM-dd_HH-mm-ss”
$logEntry = “$timestamp, $($NsgName), $($_.Exception.Message)”
$logFileName = “$($run_time)_$($ruleDefinition.Name)_update_fail.log”
Add-Content -Path “.$logFileName” -Value $logEntry
Write-Error “Failed to update rule in NSG: $NsgName ($ResourceGroup) – $($_.Exception.Message)”
}
}
Delete Operation
Our PowerShell script, nsg_rule_delete_csv.ps1, simplifies the process of deleting NSG rules in bulk. The script reads from a CSV file, nsg_rule_definitions.csv, which contains the definitions of the rules to be deleted. It then applies these deletions to the target NSGs specified in another CSV file, target_nsgs.csv. The script verifies if the existing rule’s name and priority matches the priority specified in the rule definition. If they match, the script removes the rule. If they don’t match, it logs an error message. Find the code for nsg_rule_delete_csv.ps1.
function Remove-NsgRule ($SubscriptionId, $ResourceGroup, $NsgName, $ruleDefinition) {
Try {
# Switch the context to the appropriate subscription
Set-AzContext -SubscriptionId $SubscriptionId -ErrorAction Stop
# Get the Network Security Group
$nsg = Get-AzNetworkSecurityGroup -Name $NsgName -ResourceGroupName $ResourceGroup -ErrorAction Stop
# Get the rule
$rule = Get-AzNetworkSecurityRuleConfig -Name $ruleDefinition.Name -NetworkSecurityGroup $nsg -ErrorAction Stop
# Check if the priority matches the user-provided priority
if ($rule.Priority -eq $ruleDefinition.Priority) {
# Remove the rule
$nsg | Remove-AzNetworkSecurityRuleConfig -Name $ruleDefinition.Name -ErrorAction Stop
$nsg | Set-AzNetworkSecurityGroup -ErrorAction Stop
$timestamp = Get-Date -Format “yyyy-MM-dd_HH-mm-ss”
$dateOnly = $timestamp.Substring(0, 10)
$logEntry = “$timestamp, $($ruleDefinition.Name), $nsgName, $ResourceGroup, Updated Successfully”
$logFileName = “$($run_time)_$($ruleDefinition.Name)_delete_success.log”
$logFileName = $logFileName -replace ‘[/:*?”<>|]’, ‘_’ # replace invalid characters
Add-Content -Path “.$logFileName” -Value $logEntry
Write-Host “Rule removed from NSG: $NsgName ($ResourceGroup)”
} else {
Write-Error “Priority does not match for rule in NSG: $NsgName ($ResourceGroup)”
$timestamp = Get-Date -Format “yyyy-MM-dd_HH-mm-ss”
$logEntry = “$timestamp, $($NsgName), Priority does not match for rule in NSG.”
$logFileName = “$($run_time)_$($ruleDefinition.Name)_delete_fail.log”
Add-Content -Path “.$logFileName” -Value $logEntry
}
} Catch {
$timestamp = Get-Date -Format “yyyy-MM-dd_HH-mm-ss”
$logEntry = “$timestamp, $($NsgName), $($_.Exception.Message)”
$logFileName = “$($run_time)_$($ruleDefinition.Name)_delete_fail.log”
Add-Content -Path “.$logFileName” -Value $logEntry
Write-Error “Failed to remove rule from NSG: $NsgName ($ResourceGroup) – $($_.Exception.Message)”
}
}
In all three scripts, the operations are performed using the Azure PowerShell module. The scripts also handle errors and log them to a file. The scripts prompt the user for confirmation before performing the operations. This way, you can easily manage NSG rules across multiple target NSGs, saving time and ensuring consistency across your network.
How It Works
The script works on the principle that the rules to be added, updated or modified must be consistent across all the target NSGs. For this, the script validates the rules for mass rollout on two baseline rule definition parameters i.e. rule name and rule priority, only on successful validation of these baseline, the script performs the required operations. For instance, the general flow of the nsg_rule_delete_csv.ps1 begins by prompting the user for confirmation, as the operation is irreversible. Once the user confirms, the script loops through each target NSG. For each NSG, it checks if the required variables (subscription ID, resource group, and NSG name) are null or empty. If they are, it logs an error message to a log file and skips to the next NSG.
Next, the script prints a message indicating that it’s deleting the rule from the NSG. It then loops through each rule definition and calls the Remove-NsgRule function to delete the rule.
If the user chooses not to proceed with the deletion, the script prints a message indicating that the operation was cancelled by the user.
Finally, the script prints a message indicating that it has completed. (Source: code repository)
Conclusion
With our PowerShell script, you can easily perform bulk NSG rule rollouts across multiple target NSGs. This not only saves you time but also ensures consistency across your network, enhancing its security and reliability.
Azure Portal: Manage your NSG rules at bulk
Stay tuned for more articles on how to automate and simplify your Azure networking tasks!
Microsoft Tech Community – Latest Blogs –Read More
print only odd pages?
In Excel, how do I print only odd pages? I’m on a pc.
In Excel, how do I print only odd pages? I’m on a pc. Read More
Azure Migrate availability for Southeast Asia
Just to check whether any of you facing any issue on testing Azure Migrate in Southeast Asia region ?
I’m facing a issue where the Azure Migrate dashboard can’t identify the “source appliance” that configured and discovering the VMs on source location, which causing problem on setting up “Target appliance”.
Just to check whether any of you facing any issue on testing Azure Migrate in Southeast Asia region ? I’m facing a issue where the Azure Migrate dashboard can’t identify the “source appliance” that configured and discovering the VMs on source location, which causing problem on setting up “Target appliance”. Read More
April V1 Title Plan out now!
The Monthly Title Plan for April V1 is attached to this post. The Title Plan can also be found in the following locations:
MPN Partner Portal Learning Resources page Resource page for Training Services Partners (Title Plan publishing takes 2-3 business days)
MCT Lounge Brand-new lounge for MCTs
We have removed retired courses from the Title Plan after they have been retired for 30 days. For future reference, a list of all retired courses can be found here: https://learn.microsoft.com/en-us/certifications/retired-courses
The Monthly Title Plan for April V1 is attached to this post. The Title Plan can also be found in the following locations:
MPN Partner Portal Learning Resources page Resource page for Training Services Partners (Title Plan publishing takes 2-3 business days)
MCT Lounge Brand-new lounge for MCTs
We have removed retired courses from the Title Plan after they have been retired for 30 days. For future reference, a list of all retired courses can be found here: https://learn.microsoft.com/en-us/certifications/retired-courses Read More
Renew Edge Subscription in Exchange Server 2019 after upgrade Cumulative Update 14
My environment is Exchange 2019. I have upgraded all mailbox server from CU12 to CU14.
Question: Do I need to renew Edge Subscription and run Hybrid Wizard again when I upgrade on Edge Server?
Hope to receive reply soon. Thanks a lot
My environment is Exchange 2019. I have upgraded all mailbox server from CU12 to CU14.Question: Do I need to renew Edge Subscription and run Hybrid Wizard again when I upgrade on Edge Server?Hope to receive reply soon. Thanks a lot Read More
Images in Power Apps Rich Text Editor
There is an issue where the app’s rich text fields no longer save images. If an image is pasted into one of the rich text fields in edit mode the image will appear in the text box. However, after saving the image disappears.
The Power App is integrated with a SharePoint list. The app also has a Power Automate flow that runs when the user clicks a button which creates an HTML file for the item in the list:
Does anyone know if Microsoft changed how the rich text field for Power Apps handles images? Or is it possible that a setting in the app or list was changed by mistake so that images are no longer allowed in the rich text field? The columns with rich text all have enhanced rich text enabled so I’m not sure what’s causing the issue. The flow has also not been modified since February and the issue started about 2 weeks ago.
There is an issue where the app’s rich text fields no longer save images. If an image is pasted into one of the rich text fields in edit mode the image will appear in the text box. However, after saving the image disappears. The Power App is integrated with a SharePoint list. The app also has a Power Automate flow that runs when the user clicks a button which creates an HTML file for the item in the list: Does anyone know if Microsoft changed how the rich text field for Power Apps handles images? Or is it possible that a setting in the app or list was changed by mistake so that images are no longer allowed in the rich text field? The columns with rich text all have enhanced rich text enabled so I’m not sure what’s causing the issue. The flow has also not been modified since February and the issue started about 2 weeks ago. Read More
URL to on prem server
Hello,
How do I setup Intune to access on prem https services from my phone? We have Intune managing our phones and would like to be able to access on prem URL https://myservice.mycompany.pri?
Thanks
Grant
Hello, How do I setup Intune to access on prem https services from my phone? We have Intune managing our phones and would like to be able to access on prem URL https://myservice.mycompany.pri? ThanksGrant Read More
Can MFA duration be set per-user with/without a P1/P2 Entra license?
My leadership is looking to roll out a new company policy that will forces shorter MFA duration times on specific users based on various criteria. Not looking for changes to persistent browser sessions or sign-in frequency. Just a way to set how long a specific user/group has before that are required to respond to another MFA challenge.
I thought that any manual changes to MFA duration were tenant-wide. I know there are risk-based CA policies but we want to be able to manually set the duration instead of waiting for the system to flag them as “risky” — risk-based CA policies have limited reporting capabilities without a Premium license anyway, so that’s kind of a non-starter.
I found this article that talks about changing session duration (not MFA duration) for select users but, again, this requires a P1/P2 license.
Am I totally incorrect with the “MFA duration is tenant-level only” idea? Just don’t want to break the news to my leadership only to find out it was possible all along.
My leadership is looking to roll out a new company policy that will forces shorter MFA duration times on specific users based on various criteria. Not looking for changes to persistent browser sessions or sign-in frequency. Just a way to set how long a specific user/group has before that are required to respond to another MFA challenge. I thought that any manual changes to MFA duration were tenant-wide. I know there are risk-based CA policies but we want to be able to manually set the duration instead of waiting for the system to flag them as “risky” — risk-based CA policies have limited reporting capabilities without a Premium license anyway, so that’s kind of a non-starter. I found this article that talks about changing session duration (not MFA duration) for select users but, again, this requires a P1/P2 license. Am I totally incorrect with the “MFA duration is tenant-level only” idea? Just don’t want to break the news to my leadership only to find out it was possible all along. Read More
Organizing Photos
I digitizing all of my parents’ photos and a lot of them have written descriptions on the back. How do I keep both sides of a photo together when uploading? Is this possible? It seems that when I upload them, they become scrambled. Is this possible to keep them organized the way I have them on my hard drive?
I digitizing all of my parents’ photos and a lot of them have written descriptions on the back. How do I keep both sides of a photo together when uploading? Is this possible? It seems that when I upload them, they become scrambled. Is this possible to keep them organized the way I have them on my hard drive? Read More
Full trash bin
I’ve emptied a user’s trash bin twice now, after finding that it was 99% full. After emptying the first time, it seemed to be fixed, but then it happened again. I repeated the process, but now the mailbox is 99% full again.
I need help with two things 1) Why is the user’s mailbox/trash bin still filled mail I thought I deleted? 2) where do you access the feature within Office 365 Admin to delete the user’s trash bin?
I’ve emptied a user’s trash bin twice now, after finding that it was 99% full. After emptying the first time, it seemed to be fixed, but then it happened again. I repeated the process, but now the mailbox is 99% full again. I need help with two things 1) Why is the user’s mailbox/trash bin still filled mail I thought I deleted? 2) where do you access the feature within Office 365 Admin to delete the user’s trash bin? Read More
How To Stop Ctrl + Shift + V From Periodically Recalculating All Data Tables
Hi all,
Loving the Ctrl + Shift + V keyboard shortcut; however, I can’t get it to stop recalculating the data tables in my open workbooks.
I have my calculation settings set to “Automatic Except For Data Tables” and ‘Recalculate workbook before saving unchecked.” Is there some setting that I am forgetting or a workaround?
I’ve included screenshots of what I think are the relevant settings.
Thanks!
Hi all, Loving the Ctrl + Shift + V keyboard shortcut; however, I can’t get it to stop recalculating the data tables in my open workbooks. I have my calculation settings set to “Automatic Except For Data Tables” and ‘Recalculate workbook before saving unchecked.” Is there some setting that I am forgetting or a workaround? I’ve included screenshots of what I think are the relevant settings. Thanks! Read More
M365 Adoption User Group – Answers in Viva Deep Dive
Do you have Answers?
I’m excited to have James Tyer (and engineers) from the Microsoft Viva team return to showcase Answers in Viva, including answers in communities and its intelligent importer. Nothing like having direct access to the source! The Microsoft Viva team will also showcase where they are headed with Answers and answer all your questions on both the journey and next steps.
Afterwards, stick around to hear all the latest on what’s new and coming to Microsoft 365 & the ACM space!
Online Teams Meeting Link: https://aka.ms/M365UG
DETAILS
AGENDA:
12:00 – 12:05 Welcome: Kirsty McGrath
12:05 – 12:45 Viva Answers with James Tyer, Microsoft
12:45 – 1:25 What’s New & Coming to Microsoft 365 & ACM
1:25 – 1:30 What’s Next & Close: Kirsty McGrath
BIO:
James is the Senior Program Manager on the Viva Engage & Answers Customer Experience team at Microsoft. He has previously helped launch Yammer & Viva Engage networks for companies such as Coca-Cola and Kellogg’s. James also advises interesting enterprise startups, such as www.soundbite.ai. He regularly presents at conferences and in 2021 had his first book published: Social by Design: How to create and scale a collaborative company
SOCIAL MEDIA:
LinkedIn: https://www.linkedin.com/in/jtyer/
LinkedIn: Kirsty McGrath
X: @M365Adoption, @KirstyMcGrath13,
Facebook: www.facebook.com/Microsoft365Adoption
YouTube: https://aka.ms/M365Adoption or @Microsoft365Adoption
#M365AdoptionUG #M365Adoption #MSFTAdoption #VivaEngage #VivaAnswers
Do you have Answers?
I’m excited to have James Tyer (and engineers) from the Microsoft Viva team return to showcase Answers in Viva, including answers in communities and its intelligent importer. Nothing like having direct access to the source! The Microsoft Viva team will also showcase where they are headed with Answers and answer all your questions on both the journey and next steps.
Afterwards, stick around to hear all the latest on what’s new and coming to Microsoft 365 & the ACM space!
Online Teams Meeting Link: https://aka.ms/M365UG
DETAILS
AGENDA:12:00 – 12:05 Welcome: Kirsty McGrath12:05 – 12:45 Viva Answers with James Tyer, Microsoft12:45 – 1:25 What’s New & Coming to Microsoft 365 & ACM1:25 – 1:30 What’s Next & Close: Kirsty McGrath
BIO:James is the Senior Program Manager on the Viva Engage & Answers Customer Experience team at Microsoft. He has previously helped launch Yammer & Viva Engage networks for companies such as Coca-Cola and Kellogg’s. James also advises interesting enterprise startups, such as www.soundbite.ai. He regularly presents at conferences and in 2021 had his first book published: Social by Design: How to create and scale a collaborative company
SOCIAL MEDIA:LinkedIn: https://www.linkedin.com/in/jtyer/
LinkedIn: Kirsty McGrathX: @M365Adoption, @KirstyMcGrath13,Facebook: www.facebook.com/Microsoft365AdoptionYouTube: https://aka.ms/M365Adoption or @Microsoft365Adoption#M365AdoptionUG #M365Adoption #MSFTAdoption #VivaEngage #VivaAnswers Read More
M365 Adoption User Group – How to run a successful intranet
SWOOP Analytics has analysed the behaviours of more than 177,000 intranet readers across 57,000+ intranet news pages and 37,000+ content pages over 20 organisations to produce its latest SharePoint intranet benchmarking report.
The findings from the report will show exactly how people are using and accessing company intranets. These findings are used to give achievable goals and benchmarks to get more colleagues reading and engaging on your intranet.
SWOOP Analytics’ benchmarking data will give you real-life insights into when people are reading the intranet, what they’re reading on the intranet, how they’re accessing the intranet and how you can best shape your content to get maximum engagement.
Here’s a sneak peek at some of SWOOP’s early findings:
Almost everyone accesses the intranet via their desktop computer, with less than 2% accessing the intranet via their phone and less than 0.2% via a tablet.
Employees spend, on average, almost 15 minutes a day reading the intranet.
However, only about a minute a day, on average, is spent reading intranet news pages.
Join the meetup to learn more from report authors Dr Laurence Lock Lee and Sharon Dawson.
Afterwards, stick around to hear all the latest on what’s new and coming to Microsoft 365 & the ACM space!
Online Teams Meeting Link: https://aka.ms/M365UG
DETAILS
AGENDA:
12:00 – 12:05 Welcome: Kirsty McGrath
12:05 – 12:45 How to run a successful intranet
12:45 – 1:25 What’s New & Coming to Microsoft 365 & ACM
1:25 – 1:30 What’s Next & Close: Kirsty McGrath
BIO:
Dr Laurence Lock Lee, SWOOP Analytics, Chief Data Scientist & Co-founder – Laurence is an experienced professional, with over 40 years’ experience as a researcher, technology leader, educator and management consultant. He is a leading practitioner in Social Network Analysis (SNA) for organisational change, having conducted more than 100 consulting assignments for clients around the world. At SWOOP he is responsible for the science that underpins the SWOOP dashboard measures. He holds a PhD on corporate social capital from the University of Sydney.
Sharon Dawson, SWOOP Analytics, Director, External Relations & Communications – With an impressive career as a journalist covering news, politics, sport and finance for Australian Associated Press and other news organisations, Sharon joined SWOOP to lead our external communication and relationship activities. She has a special talent for bringing to life our customers’ stories and a passion to help customers become better, more effective collaborators.
Emily O’Brien, SWOOP Analytics, Director, Global Operations & APAC – With a background in marketing and communication, Emily has experience in the community management space, previously implementing the internal communication strategy for a large company of 30,000+ field-based employees. Emily is enthusiastic about helping our customers unlock the full value of the collaboration insights available in SWOOP by facilitating training on leadership engagement, running effective groups and communication campaigns.
SOCIAL MEDIA:
Dr. Laurence Lock Lee | LinkedIn
Sharon Dawson (Mathieson) | LinkedIn
Emily O’Brien | LinkedIn
LinkedIn: Kirsty McGrath
X: @M365Adoption, @KirstyMcGrath13,
Facebook: www.facebook.com/Microsoft365Adoption
YouTube: https://aka.ms/M365Adoption or @Microsoft365Adoption
#M365AdoptionUG #M365Adoption #MSFTAdoption #SWOOPAnalytics #Intranet #SharePoint
SWOOP Analytics has analysed the behaviours of more than 177,000 intranet readers across 57,000+ intranet news pages and 37,000+ content pages over 20 organisations to produce its latest SharePoint intranet benchmarking report.The findings from the report will show exactly how people are using and accessing company intranets. These findings are used to give achievable goals and benchmarks to get more colleagues reading and engaging on your intranet.SWOOP Analytics’ benchmarking data will give you real-life insights into when people are reading the intranet, what they’re reading on the intranet, how they’re accessing the intranet and how you can best shape your content to get maximum engagement.Here’s a sneak peek at some of SWOOP’s early findings:
Almost everyone accesses the intranet via their desktop computer, with less than 2% accessing the intranet via their phone and less than 0.2% via a tablet.
Employees spend, on average, almost 15 minutes a day reading the intranet.
However, only about a minute a day, on average, is spent reading intranet news pages.
Join the meetup to learn more from report authors Dr Laurence Lock Lee and Sharon Dawson.
Afterwards, stick around to hear all the latest on what’s new and coming to Microsoft 365 & the ACM space!
Online Teams Meeting Link: https://aka.ms/M365UG
DETAILS
AGENDA:12:00 – 12:05 Welcome: Kirsty McGrath12:05 – 12:45 How to run a successful intranet12:45 – 1:25 What’s New & Coming to Microsoft 365 & ACM1:25 – 1:30 What’s Next & Close: Kirsty McGrath
BIO:Dr Laurence Lock Lee, SWOOP Analytics, Chief Data Scientist & Co-founder – Laurence is an experienced professional, with over 40 years’ experience as a researcher, technology leader, educator and management consultant. He is a leading practitioner in Social Network Analysis (SNA) for organisational change, having conducted more than 100 consulting assignments for clients around the world. At SWOOP he is responsible for the science that underpins the SWOOP dashboard measures. He holds a PhD on corporate social capital from the University of Sydney.
Sharon Dawson, SWOOP Analytics, Director, External Relations & Communications – With an impressive career as a journalist covering news, politics, sport and finance for Australian Associated Press and other news organisations, Sharon joined SWOOP to lead our external communication and relationship activities. She has a special talent for bringing to life our customers’ stories and a passion to help customers become better, more effective collaborators.
Emily O’Brien, SWOOP Analytics, Director, Global Operations & APAC – With a background in marketing and communication, Emily has experience in the community management space, previously implementing the internal communication strategy for a large company of 30,000+ field-based employees. Emily is enthusiastic about helping our customers unlock the full value of the collaboration insights available in SWOOP by facilitating training on leadership engagement, running effective groups and communication campaigns.
SOCIAL MEDIA:Dr. Laurence Lock Lee | LinkedInSharon Dawson (Mathieson) | LinkedInEmily O’Brien | LinkedInLinkedIn: Kirsty McGrathX: @M365Adoption, @KirstyMcGrath13,Facebook: www.facebook.com/Microsoft365AdoptionYouTube: https://aka.ms/M365Adoption or @Microsoft365Adoption#M365AdoptionUG #M365Adoption #MSFTAdoption #SWOOPAnalytics #Intranet #SharePoint Read More
Cannot close “ghost” window, application killed
Please see the image. I had a popup for a software update, I tried to close the window but it turned see through. I cannot click x, I restarted explorer.exe, I killed the offending application, I’ve logged out, I’ve restarted my graphics driver but this window will not close. This window is stuck in the middle of my display and I cannot restart at the moment. Nothing I can find will get this box out of my way.
Thanks in advance.
Can someone help me navigate this issue? Windows 11 is really working hard at the WOAT OS title.
Please see the image. I had a popup for a software update, I tried to close the window but it turned see through. I cannot click x, I restarted explorer.exe, I killed the offending application, I’ve logged out, I’ve restarted my graphics driver but this window will not close. This window is stuck in the middle of my display and I cannot restart at the moment. Nothing I can find will get this box out of my way. Thanks in advance.Can someone help me navigate this issue? Windows 11 is really working hard at the WOAT OS title. Read More
Usability around retention labels
Some of our key stakeholders are complaining that the interface to assign a retention label is not very usable in that it displays just as one big dropdown and doesn’t provide any hierarchical grouping or search capability. Are there any workaround to this?
Some of our key stakeholders are complaining that the interface to assign a retention label is not very usable in that it displays just as one big dropdown and doesn’t provide any hierarchical grouping or search capability. Are there any workaround to this? Read More