New Blog | Bridging the On-premises to Cloud Security Gap: Cloud Credentials Detection
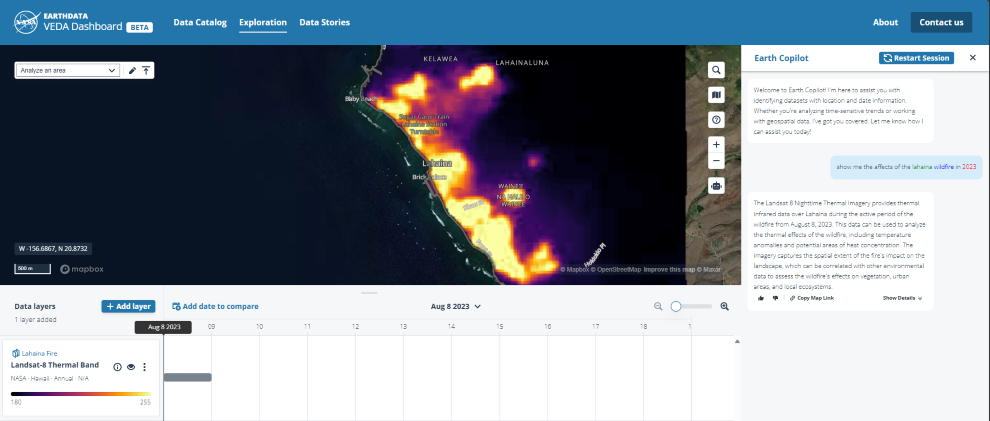
Identities lie at the heart of cloud security. One of the most common tactics used to breach cloud environments is Credential Access. User credentials may be obtained using various techniques. Credentials may be cracked through brute force attempts, obtained in social engineering campaigns, or stolen from compromised resources, where they are stored and used.
In this blog, we demonstrate that properly securing cloud environments requires securing credentials in the organization’s non-cloud environments. To this end, we dive into our innovative capability to detect cloud credentials in on-premises environments and user devices. By integrating it with Microsoft Security Exposure Management, customers are able to identify attack paths starting in non-cloud environments and reaching critical cloud assets using cloud credentials. Customers are then able to effectively prioritize and mitigate those attack paths, thereby improving their enterprise and cloud security posture.
Read the full post here: Bridging the On-premises to Cloud Security Gap: Cloud Credentials Detection
By Tamir Friedman
Identities lie at the heart of cloud security. One of the most common tactics used to breach cloud environments is Credential Access. User credentials may be obtained using various techniques. Credentials may be cracked through brute force attempts, obtained in social engineering campaigns, or stolen from compromised resources, where they are stored and used.
In this blog, we demonstrate that properly securing cloud environments requires securing credentials in the organization’s non-cloud environments. To this end, we dive into our innovative capability to detect cloud credentials in on-premises environments and user devices. By integrating it with Microsoft Security Exposure Management, customers are able to identify attack paths starting in non-cloud environments and reaching critical cloud assets using cloud credentials. Customers are then able to effectively prioritize and mitigate those attack paths, thereby improving their enterprise and cloud security posture.
Read the full post here: Bridging the On-premises to Cloud Security Gap: Cloud Credentials Detection