Tag Archives: microsoft
Defender Firewall rules – Event ID 2001
In my organization, we’re moving away from Trellix suite to MDE. All of my policies (DLP, AV, Exclusions, etc…) are working, but not the Firewall general settings nor the Firewall Rules. Defender portal indicates that the Firewall settings policy was successful, but the rules are not. Our workstations are hybrid-joined, but managed by SCCM/MDE. When I look at the Event View for SENSE (channel Microsoft-Windows-SENSE/Operational) related events, I get an event ID 2001, and the info is: SenseCM: WRN: FW VA: no rule TESTING POLICY
The rule TESTING POLICY exists in my Defender portal, under Endpoint security policies, so it seems like my test workstation can see that policy, but it doesn’t get applied, and also the Firewall settings don’t get applied, as it doesn’t appear to change the default block/allow for Outbound or Inbound for each of the Firewall profile (Public, Private, Domain).
Anything suggestion will be appreciated.
In my organization, we’re moving away from Trellix suite to MDE. All of my policies (DLP, AV, Exclusions, etc…) are working, but not the Firewall general settings nor the Firewall Rules. Defender portal indicates that the Firewall settings policy was successful, but the rules are not. Our workstations are hybrid-joined, but managed by SCCM/MDE. When I look at the Event View for SENSE (channel Microsoft-Windows-SENSE/Operational) related events, I get an event ID 2001, and the info is: SenseCM: WRN: FW VA: no rule TESTING POLICY The rule TESTING POLICY exists in my Defender portal, under Endpoint security policies, so it seems like my test workstation can see that policy, but it doesn’t get applied, and also the Firewall settings don’t get applied, as it doesn’t appear to change the default block/allow for Outbound or Inbound for each of the Firewall profile (Public, Private, Domain). Anything suggestion will be appreciated. Read More
Partner Blog | How Microsoft Copilot and ServiceNow Now Assist enhance employee & IT admin choice
As Microsoft works to enable AI at the enterprise level, our focus is on building sophisticated productivity tools that integrate with our ecosystem of partners. For example, during last year’s Microsoft Ignite conference, we provided an early preview of how ServiceNow’s integration with Microsoft Copilot would bring generative AI capabilities to IT and employee experiences. I recently had the pleasure of joining ServiceNow’s President and Chief Operating Officer CJ Desai on stage at the company’s marquee event, Knowledge 2024 in Las Vegas, to unveil three compelling scenarios that fulfill the promise of Copilot and Now Assist, ServiceNow’s generative AI experience.
Now Assist AI delivers direct, relevant, and conversational responses to employee requests, and connects exchanges to AI-powered workflows on ServiceNow’s platform to take actions on behalf of the employee. I’ll share more on how we’ve integrated Copilot and Now Assist to supercharge the workforce using the scenarios from Knowledge 2024, but first let’s discuss the extensibility model used by ServiceNow for the integration.
There are various ways to extend Copilot, which provide the starting point for partners looking to harness AI and bring Copilot capabilities to your apps. We are also working on a new approach to extensibility that makes it possible for independent software vendors (ISVs) to bring their own generative AI technologies into Copilot experiences and hand off users to their own third-party copilots, ensuring user experiences and workflows are streamlined. ServiceNow is taking advantage of this new option by allowing users to execute ServiceNow workflows via Now Assist to improve employee productivity and deliver an improved experience.
Continue reading here
Microsoft Tech Community – Latest Blogs –Read More
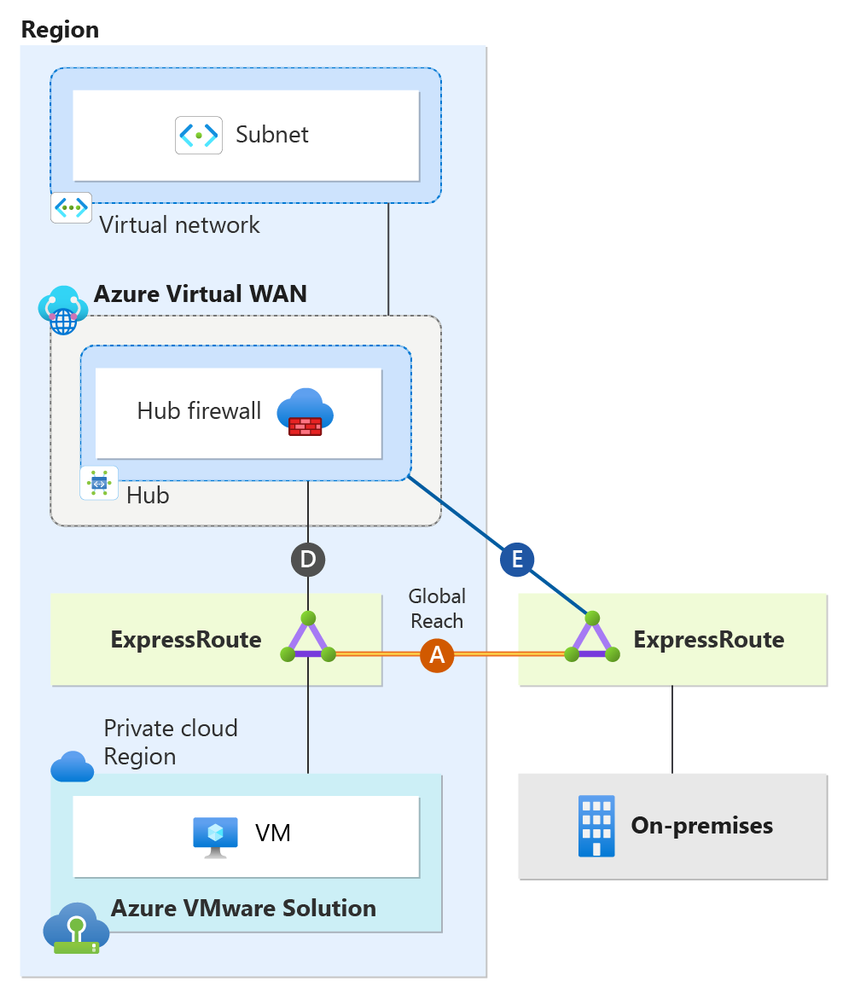
Single-region deployment using Secure Virtual WAN Hub with Routing-Intent and Global Reach
This article describes the best practices for connectivity, traffic flows, and high availability of single-region Azure VMware Solution when using Azure Secure Virtual WAN with Routing Intent. You will learn the design details of using Secure Virtual WAN with Routing-Intent, when using Global Reach. This article breaks down Virtual WAN with Routing Intent topology from the perspective of an Azure VMware Solution private cloud, on-premises sites, and Azure native. The implementation and configuration of Secure Virtual WAN with Routing Intent are beyond the scope and aren’t discussed in this document.
Secure Virtual WAN with Routing Intent is only supported with Virtual WAN Standard SKU. Secure Virtual WAN with Routing Intent provides the capability to send all Internet traffic and Private network traffic to a security solution like Azure Firewall, a third-party Network Virtual Appliance (NVA), or SaaS solution. In the scenario, we have a single region network. There’s a Virtual WAN with one hub. The hub has an Azure Firewall deployed, essentially making it a Secure Virtual WAN hub. Having a Secure Virtual WAN hub is a technical prerequisite to Routing Intent. The Secure Virtual WAN hub has Routing Intent enabled.
Note
When configuring Azure VMware Solution with Secure Virtual WAN Hubs, ensure optimal routing results on the hub by setting the Hub Routing Preference option to “AS Path.” – see Virtual hub routing preference
The single region consists of its own Azure VMware Solution Private Cloud and an Azure Virtual Network. Additionally, there’s an on-premises site connecting back to the hub. Furthermore, Global Reach connectivity exists within the environment. Global Reach establishes a direct logical link via the Microsoft backbone, connecting Azure VMware Solution to on-premises. As shown in the diagram, Global Reach connections don’t transit the Hub firewall. So, Global Reach traffic between on-premises and Azure VMware Solution, and vice versa, remains uninspected.
Note
When utilizing Global Reach, consider enhancing security between Global Reach sites by inspecting traffic within the Azure VMware Solution environment’s NSX-T or an on-premises firewall.
Understanding Topology Connectivity
Connection
Description
Connections (D)
Azure VMware Solution private cloud managed ExpressRoute connection to the hub.
Connection (A)
Azure VMware Solution Global Reach connection back to on-premises.
Connections (E)
on-premises ExpressRoute connection to the hub.
The following sections cover traffic flows and connectivity for Azure VMware Solution, on-premises, Azure Virtual Networks, and the Internet.
This section focuses only on the Azure VMware Solution Cloud’s perspective. Azure VMware Solution private cloud has an ExpressRoute connection to its hub (connection labeled as “D”).
The Azure VMware Solution Cloud Region establishes a connection to on-premises via ExpressRoute Global Reach, depicted as Global Reach (A) in the diagram. It’s important to note that traffic via Global Reach doesn’t transit the Hub firewall.
Ensure that you explicitly configure Global Reach (A). It’s imperative to do this step to prevent connectivity issues between on-premises and Azure VMware Solution. For more information, see traffic flow section.
The diagram illustrates traffic flows from the perspective of the Azure VMware Solution Private Cloud.
Traffic Flow Chart
Traffic Flow Number
Source
Direction
Destination
Traffic Inspected on Secure Virtual WAN Hub firewall?
1
Azure VMware Solution Cloud
→
Virtual Network
Yes, traffic is inspected at the Hub firewall
2
Azure VMware Solution Cloud
→
on-premises
No, traffic bypasses firewall and transits Global Reach (A)
This section focuses only on the on-premises site. As shown in the diagram, the on-premises site has an ExpressRoute connection to the hub (connections labeled as “E”). On-premises systems can communicate to Azure VMware Solution via connection Global Reach (A).
Ensure that you explicitly configure Global Reach (A). It’s imperative to do this step to prevent connectivity issues between on-premises and Azure VMware Solution. For more information, see traffic flow section.
The diagram illustrates traffic flows from an on-premises perspective.
Traffic Flow Chart
Traffic Flow Number
Source
Direction
Destination
Traffic Inspected on Secure Virtual WAN Hub firewall?
3
on-premises
→
Azure VMware Solution Cloud
No, traffic bypasses firewall and transits Global Reach (A)
4
on-premises
→
Virtual Network
Yes, traffic is inspected at the Hub firewall
This section focuses only on connectivity from the Azure Virtual Network perspective. As depicted in the diagram, the Virtual Network is peering directly to the hub.
A Secure Hub with enabled Routing Intent always sends the default RFC 1918 addresses (10.0.0.0/8, 172.16.0.0/12, 192.168.0.0/16) to peered Virtual Networks, plus any other prefixes that are added as “Private Traffic Prefixes” – see Routing Intent Private Address Prefixes. In our scenario, with Routing Intent enabled, all resources in the Virtual Network currently possess the default RFC 1918 addresses and use the Hub firewall as the next hop. All traffic ingressing and egressing the Virtual Network will always transit the Hub firewall. For more information, see traffic flow section.
Traffic Flow Chart
Traffic Flow Number
Source
Direction
Destination
Traffic Inspected on Secure Virtual WAN hub firewall?
5
Virtual Network
→
Azure VMware Solution Cloud
Yes, traffic is inspected at the Hub firewall
6
Virtual Network
→
Azure VMware Solution Cloud
Yes, traffic is inspected at the Hub firewall
This section focuses only on how internet connectivity is provided for Azure native resources in the Virtual Network and the Azure VMware Solution Private Cloud. There are several options to provide internet connectivity to Azure VMware Solution. – see Internet Access Concepts for Azure VMware Solution
Option 1: Internet Service hosted in Azure
Option 2: VMware Solution Managed SNAT
Option 3: Azure Public IPv4 address to NSX-T Data Center Edge
Although you can use all three options with Single Region Secure Virtual WAN with Routing Intent, “Option 1: Internet Service hosted in Azure” is the best option when using Secure Virtual WAN with Routing Intent and is the option that is used to provide internet connectivity in the scenario. The reason why “Option 1” is considered the best option with Secure Virtual WAN is due to its ease of security inspection, deployment, and manageability.
With Routing Intent, you can choose to generate a default route from the hub firewall. This default route is advertised to your Virtual Network and to Azure VMware Solution. This section is broken into two sections, one that explains internet connectivity from an Azure VMware Solution perspective and another from the Virtual Network perspective.
When Routing Intent is enabled for internet traffic, the default behavior of the Secure Virtual WAN Hub is to not advertise the default route across ExpressRoute circuits. To ensure the default route is propagated to the Azure VMware Solution from the Azure Virtual WAN, you must enable default route propagation on your Azure VMware Solution ExpressRoute circuits – see To advertise default route 0.0.0.0/0 to endpoints. Once changes are complete, the default route 0.0.0.0/0 is then advertised via connection “D” from the hub. It’s important to note that this setting shouldn’t be enabled for on-premises ExpressRoute circuits. Even though connection “D” advertises the default route 0.0.0.0/0 to Azure VMware Solution, the default route is also advertised to on-premises via Global Reach (A). As a result, the recommendation is to implement a BGP Filter on your on-premises equipment to exclude learning the default route. This step ensures that on-premises internet connectivity isn’t impacted.
When Routing Intent for internet access is enabled, the default route generated from the Secure VWAN Hub is automatically advertised to the hub-peered Virtual Network connections. You’ll notice under Effective Routes for the Virtual Machines’ NICs in the Virtual Network that the 0.0.0.0/0 next hop is the hub firewall.
For more information, see the traffic flow section.
Traffic Flow Chart
Traffic Flow Number
Source
Direction
Destination
Traffic Inspected on Secure Virtual WAN hub firewall?
7
Azure VMware Solution Cloud
→
Internet
Yes, traffic is inspected at the Hub firewall
8
Virtual Network
→
Internet
Yes, traffic is inspected at the Hub firewall
For more information on Virtual WAN hub configuration, see About virtual hub settings .
For more information on how to configure Azure Firewall in a Virtual Hub, see Configure Azure Firewall in a Virtual WAN hub.
For more information on how to configure the Palo Alto Next Generation SAAS firewall on Virtual WAN, see Configure Palo Alto Networks Cloud NGFW in Virtual WAN.
For more information on Virtual WAN hub routing intent configuration, see Configure routing intent and policies through Virtual WAN portal.
Microsoft Tech Community – Latest Blogs –Read More
Azure Developers – .NET Day 2024 – Recap
Hi friends!
I’m happy to share the insights from the recent Azure Developers – .NET Day 2024. This event was a treasure full of knowledge for .NET developers looking to harness the power of the cloud. With a focus on AI and .NET, the day was packed with sessions that explored the cutting-edge of cloud-native capabilities, AI advancements, and app development efficiencies .
General Recap
The event kicked off with a warm welcome and quickly moved into practical AI coding sessions, demonstrating how to infuse AI into .NET applications, making them smarter and more intuitive. We also have sessions on how GitHub Copilot for SQL Development is a game-changer, showcasing how AI can streamline database development processes.
Midway through the day, a session on Redis & .NET Apps highlighted the importance of consistency and smart capabilities in applications. A presentation on Change Data Streams with Azure SQL was a hit, offering insights into real-time data manipulation and analysis.
The final sessions of the day focused on developer productivity and cloud-native computing. A talk on Azure API Center unveiled new tools to boost productivity, and a session on VS Code Project Setups provided valuable tips for streamlining development workflows.
Recordings
If you missed the live event or want to revisit the highlights, these videos are your gateway to the wealth of knowledge shared by our experts. You can find the full recordings here:
00:00:00 – Countdown
00:05:00 – Opening – Hailey Huber
00:07:20 – Practical (and fun) AI Coding Session – Bruno Capuano
00:17:40 – GitHub Copilot for SQL Development: Integrating the Power of AI into Database Development – Subhojit Basak
00:49:40 – Making .NET intelligent apps smarter and consistent with Redis – Catherine Wang & Stanley Small
01:19:15 – Event-Driven Architectures with Azure SQL, .NET and Azure Functions – Davide Mauri
01:50:20 – T-SQL for cloud-native developers – Abhiman Tiwari
02:09:20 – Unlocking Scalability: Azure SQL DB Hyperscale and the Power of Named Replicas – Attinder Pal Singh
02:50:00 – MongoDB for .NET and Azure Developers – Luce Carter
03:21:55 – Unlocking Azure API Center: Empowering .NET Developers – Justin Yoo
03:54:20 – Testing web apps with Playwright – Debbie O’Brien & Vansh Singh
04:05:30 – Dev Productivity Dojo: Master Project Setups Using VS Code – Ori Bar-ilan
04:32:20 – Migrating apps to Azure with Code Assessment tooling – McKenna Barlow
04:42:40 – Create a Change Data Stream in Minutes with .NET, Azure SQL, and Azure Functions – Brian Spendolini
04:57:25 – Auto-Generate and Host Data API Builder on Azure Static Web Apps – Frank Boucher & Jerry Nixon
05:08:30 – .NET Extensibility in Azure Logic Apps – Kent Weare
05:38:00 – The most minimal API code of all… none – Frank Boucher & Jerry Nixon
06:11:00 – Host your gRPC workloads on App Service with .NET on Windows – Jeff Martinez & Byron Tardif
06:36:45 – Closing – Hailey Huber
Full Recording
Thank you for joining us on this journey through Azure Developers – .NET Day 2024. We hope these sessions inspire you to build amazing solutions with .NET and Azure.
Best,
Bruno Capuano
Microsoft Tech Community – Latest Blogs –Read More
Building securely: Microsoft Build 2024
This year’s Microsoft Build event is shaping up to be a must-attend event. The high demand for secure software development continues to grow. And with the complexity of today’s digital world, developers are being asked to do even more to keep apps, AI, and code secure—with more focus on built-in security and more integrated security at every phase of design, development, and deployment. Developers who attend Microsoft Build can learn how to manage and govern AI, securely. Our commitment is to provide developers with the knowledge, tools, and practices needed to build safely. It’s a commitment to ensuring security isn’t an afterthought, but a fundamental component of the entire development lifecycle. And Microsoft Build is a great time and place to connect with other developers globally, grow your skills, and learn more about building secure copilots, generative AI, securing applications, and more. Register now for live keynotes, breakout sessions, demos, and social events. Or if you can’t make it in person, access sessions online and on-demand.
Building on a trusted platform
Building on a trusted platform is crucial in today’s digital-first world. At Microsoft, our platforms—from Azure, GitHub, Visual Studio, PowerApps, and more—are designed with security at their core. This provides developers with the tools and integrations they need to innovate securely. And by building on a trusted platform, whether it be with Microsoft or multicloud strategy, developers can focus on innovation and great end-user experiences.
How to build AI securely
AI—the most transformative technology of our era—is rapidly reshaping our world, offering incredible opportunities but also introducing new risks. Microsoft is at the forefront, ensuring our AI is developed securely, by embedding security and safety in all our products and building on pioneering efforts like Microsoft’s Responsible AI Framework. Our goal is to make security a priority in AI development, empowering developers to create exciting and impactful AI tools without compromising safety.
The conference attendee experience
Connect with experts – Meet up with Microsoft security experts who are ready to answer your deep technical questions. Meet-up topics include GitHub advanced security, DevSecOps, Microsoft Entra, Microsoft Purview, Microsoft Defender, Microsoft Intune, and multicloud security. Stop by the expert meet-up area to connect and learn.
Join demonstrations – Stop by The Hub to see live demos of topics including AI, Copilot, and low-code tools. You can learn how to fix security leaks at scale, combat fraud with real-time identity verification, and create secure apps in minutes. We’ll also be demonstrating simple and secure app authentication with authentication brokers, how to create pixel perfect authentication experiences, and more.
AI for good – Connect with experts and peers about social impact and how AI can be utilized to make the world a better place for all. Find us right outside The Hub.
Security-focused sessions – We’re preparing multiple in-depth sessions focused on how to build secure apps using Microsoft platforms. In our Microsoft Build sessions—which you can join in person or online—we aim to help all developers increase the security of their AI development by learning from our experienced engineers sharing real-life examples and first-hand accounts of how we embed security and safety into all our products.
We’re really excited about our content this year. There will be sessions on workflows and API security testing to multiple sessions on LLMs; securing generative AI applications; AI red teaming, AI security; and more. You can find more about them all in the session catalog. Among the sessions you do not want to miss are:
Inside AI Security with Mark Russinovich – Join Mark Russinovich, Chief Technology Officer and Technical Fellow for Microsoft Azure, as he explores the landscape of AI security, focusing on threat modeling, defense tactics, our red teaming approaches, and the path to confidential AI.
How Microsoft approaches AI red teaming – AI Red Team (AIRT) serves as the independent red team for high-risk AI across Microsoft. This session will cover processes, techniques, and tools including PyRIT—AIRT’s open-source automation framework. Presented by Tori Westerhoff, Principal Technical Program Management, Responsible AI Red Teaming, Microsoft and Pete Bryan, AI Security Researcher, Microsoft.
Unwind with Microsoft experts and peers
Develop the vibe. Join us at the Microsoft Security Developer Kickback on May 22 from 6:00pm – 9:00pm at the Seattle Collective. Celebrate the new era of security with Microsoft subject matter experts and peers, all while enjoying heavy appetizers and beverages. You must be registered to attend this event, so be sure to RSVP today.
Please note that transportation to and from the event venue will not be provided. Kindly arrange for your own transportation to ensure a safe return to your hotel or accommodation.
Learn more and register now
Check out the session catalog to start building your own itinerary and maximize your Microsoft Build 2024 attendee experience. With 400+ sessions and 90+ focused on AI, you’re sure to find just the right mix of content tailored to your specific development interests. Register now. We’re excited for you to join us and hope to see you there!
Microsoft Tech Community – Latest Blogs –Read More
Restore a deleted User Account from a server backup to a new HD and get OS and apps included?
Hello,
Apologies in advance if this is in the wrong forum. If so I appreciate a pointer in the right direction. Thanks.
I have arrived in a predicament and would appreciate feedback from the community about the feasibility of my imagined solution.
Description of the situation
A server running Windows Server Essentials 2016. Up to date.A domain connected workstation with Windows 11 Pro. Latest update circa 7 days ago.I mistakenly deleted the User Account used to log into the workstation from the WSE Dashboard. The workstation was regularly backed up so the User Account should have a backup from circa 14 days ago. That would be fine.The most recent attempted back up of the workstation could not be completed because space on the workstation hard drive was too low (M.2 256GB PCIe NVMe Class 40 SSD). I need to add a new hard drive I purchased ((1TB 7200rpm SATA HD).
My summary of the issues I am facing
Need to get the new hard drive into workstationNeed to get Windows 11 Pro onto the new hard driveNeed to restore User Account from server backup
Questions
Is it possible to restore the User Account to the new hard drive and get the Windows OS, apps, and User Account automatically through the restore process?Is there any benefit to keeping the OS on the existing hard drive and having all the apps on the new hard drive?
This is what I can think of now. In case I have missed important aspects around this I appreciate any information that could help me achieve my goal i.e. get the new hard drive installed and operational with the OS, User Account and apps.
Thanks in advance!
Hello, Apologies in advance if this is in the wrong forum. If so I appreciate a pointer in the right direction. Thanks. I have arrived in a predicament and would appreciate feedback from the community about the feasibility of my imagined solution. Description of the situationA server running Windows Server Essentials 2016. Up to date.A domain connected workstation with Windows 11 Pro. Latest update circa 7 days ago.I mistakenly deleted the User Account used to log into the workstation from the WSE Dashboard. The workstation was regularly backed up so the User Account should have a backup from circa 14 days ago. That would be fine.The most recent attempted back up of the workstation could not be completed because space on the workstation hard drive was too low (M.2 256GB PCIe NVMe Class 40 SSD). I need to add a new hard drive I purchased ((1TB 7200rpm SATA HD). My summary of the issues I am facingNeed to get the new hard drive into workstationNeed to get Windows 11 Pro onto the new hard driveNeed to restore User Account from server backup QuestionsIs it possible to restore the User Account to the new hard drive and get the Windows OS, apps, and User Account automatically through the restore process?Is there any benefit to keeping the OS on the existing hard drive and having all the apps on the new hard drive? This is what I can think of now. In case I have missed important aspects around this I appreciate any information that could help me achieve my goal i.e. get the new hard drive installed and operational with the OS, User Account and apps. Thanks in advance! Read More
Maximum file size for Azure BLOB
Hey Azure storage team,
What is the maximum single file size that is allowable inside of an Azure BLOB?
I have a 15TB backup repository that I need to ensure is loaded to BLOB in full.
I know that Wasabi has a limit of 5TB and this has caused a delay in the project.
Any input/confirmation welcome!
Ref: Scalability and performance targets for Blob storage – Azure Storage | Microsoft Learn
Hey Azure storage team, What is the maximum single file size that is allowable inside of an Azure BLOB? I have a 15TB backup repository that I need to ensure is loaded to BLOB in full. I know that Wasabi has a limit of 5TB and this has caused a delay in the project. Any input/confirmation welcome!Ref: Scalability and performance targets for Blob storage – Azure Storage | Microsoft Learn Read More
Is there anyone actually paying attention to the Discussions and Ideas?
I have only been using Microsoft Bookings for about 2 months. I reported an issue to Microsoft, and they suggest that I review the Discussions and the Ideas for the Booking Specific area…
Well, All 94 ideas status is currently “NEW” and, from the couple of discussion posts I have read, I see the community trying to help each other out, but I do not actually see any participation by Microsoft Bookings…
The sad thing is, some of the ideas are really good, and have just been sitting there for 3+ years with no action…
Thanks,
I have only been using Microsoft Bookings for about 2 months. I reported an issue to Microsoft, and they suggest that I review the Discussions and the Ideas for the Booking Specific area… Well, All 94 ideas status is currently “NEW” and, from the couple of discussion posts I have read, I see the community trying to help each other out, but I do not actually see any participation by Microsoft Bookings… The sad thing is, some of the ideas are really good, and have just been sitting there for 3+ years with no action… Thanks, Read More
Option for Transferring Call to Voicemail Using the Consult then Transfer Option
Scenario: A user is on a call with a customer (external number), they would like to speak to a manager or another internal employee (MS Teams user) so they select the Consult then Transfer option. After consulting the manager they decide they don’t want to speak to the customer and would like the call transferred directly to their voicemail without the line ringing.
Is this possible using the Consult then Transfer option?
If not, is there a way to go back a step after consulting select Transfer, and send directly to voicemail?
For context, we use 8X8 as our phone system.
Scenario: A user is on a call with a customer (external number), they would like to speak to a manager or another internal employee (MS Teams user) so they select the Consult then Transfer option. After consulting the manager they decide they don’t want to speak to the customer and would like the call transferred directly to their voicemail without the line ringing. Is this possible using the Consult then Transfer option? If not, is there a way to go back a step after consulting select Transfer, and send directly to voicemail? For context, we use 8X8 as our phone system. Read More
Changing page number coding in mid document
I need some layout help with a WORD document. My document consists of a main document and three appendices The Page numbering will be continuous, but I want to label the pages differently. EG. In the main document the page numbers will be – X – centered on the bottom of the page. But I want the appendices to be identified separately as “Appendix A — [Page #] —” and “Appendix B — [Page #] —” and “Appendix C — [Page #] —. I know I need to separate the last page before each Appendix and the Appendix with some combination of “Page Break” and/or “Section Break (Continuous)” and/or “Section Break (Continuous)” and maybe something else, but I don’t know what. Help Please. Alan W == email address removed for privacy reasons
I need some layout help with a WORD document. My document consists of a main document and three appendices The Page numbering will be continuous, but I want to label the pages differently. EG. In the main document the page numbers will be – X – centered on the bottom of the page. But I want the appendices to be identified separately as “Appendix A — [Page #] —” and “Appendix B — [Page #] —” and “Appendix C — [Page #] —. I know I need to separate the last page before each Appendix and the Appendix with some combination of “Page Break” and/or “Section Break (Continuous)” and/or “Section Break (Continuous)” and maybe something else, but I don’t know what. Help Please. Alan W == email address removed for privacy reasons Read More
New Blog | Secure your data to confidently take advantage of Generative AI with Microsoft Purview
By Liz Willets
Security teams often find themselves in the dark when it comes to data security risks associated with AI usage. An alarming 80% of leaders cite the leakage of sensitive data as their primary concern [1]. And more than 30% of decision makers say they don’t know where or what their sensitive business critical data is [2], and with generative AI generating more data, getting that visibility into how sensitive data is flowing through AI and how your users are interacting with generative AI applications is essential. Without proper visibility, organizations struggle to safeguard their assets effectively. Organizations want to get ahead of and minimize the inherent risks of data being shared with generative AI applications, such as data oversharing, data leakage and non-compliant use of GenAI apps. Instead of restricting AI use to avoid these outcomes, security teams can mitigate and manage risks more effectively by proactively gaining visibility into AI usage within the organization and implementing corresponding protection and governance controls.
On top of that, evolving regulatory environments and rapid technological advancements create complex challenges for customers. Adhering to new regulations, particularly those pertaining to cutting-edge technologies like GenAI, is essential for devising an effective security and compliance strategy. In this era where AI regulations and standards, such as the EU AI Act and NIST AI RMF, are taking shape, it is imperative for organizations to develop and use AI applications in a manner that is safe, transparent and responsible. According to Gartner®, “by 2027 at least one global company will see its AI deployment banned by a regulator for noncompliance with data protection or AI governance legislation.” [3] AI will be a catalyst for regulatory changes, and having secure and compliant AI will become fundamental.
At Microsoft Ignite 23’ and Microsoft Secure 24’, we introduced new capabilities to help organizations discover, protect and govern data in an AI-first world with Microsoft Purview.
Today, we are excited to announce new innovations from Microsoft Purview to help you secure and govern AI:
Microsoft Purview AI Hub, which helps organizations discover how AI applications such as Copilot for M365 and third-party AI apps are being used in their organization and provides ready-to-use policies to protect data, is now available in public preview.
New insights into unlabeled files and SharePoint sites referenced by Microsoft Copilot for Microsoft 365 will also be included in the public preview release of the AI Hub. This helps organizations prioritize the most critical data risks and put in place protection policies to prevent potential oversharing of sensitive data.
New insights into non-compliant and unethical use of AI interactions will also be included in the public preview release of the AI Hub. This helps organizations quickly gain insight into unethical use such as regulatory collusion, money laundering, targeted harassment and more.
New Compliance Manager assessment templates for EU AI Act, NIST AI RMF, ISO/IEC 23894:2023 and ISO/IEC 42001 to help assess, implement and strengthen compliance controls to meet AI regulatory requirements and standards. These insights will also be surfaced in the AI Hub and available in public preview.
Discover how AI applications are being used
To help customers gain a better understanding of which AI applications are being used and how – we are announcing the public preview of Microsoft Purview AI Hub – which includes insights like sensitive data shared with AI apps (whether Copilot for M365 or third-party AI apps), total number of users interacting with AI apps and their associated risk level, pulled from Microsoft Purview Insider Risk Management, and more.
As organizations adopt Copilot for Microsoft 365, data security controls become paramount to avoid potential overexposure of sensitive data or SharePoint sites. And we know that it is challenging to manage and label vast amounts of information, often leaving sensitive data vulnerable to data oversharing. Microsoft Purview AI Hub addresses this challenge by surfacing unlabeled files and SharePoint sites referenced by Copilot, helping you prioritize your most critical data risks and prevent potential oversharing of sensitive data.
Read the full post here: Secure your data to confidently take advantage of Generative AI with Microsoft Purview
By Liz Willets
Security teams often find themselves in the dark when it comes to data security risks associated with AI usage. An alarming 80% of leaders cite the leakage of sensitive data as their primary concern [1]. And more than 30% of decision makers say they don’t know where or what their sensitive business critical data is [2], and with generative AI generating more data, getting that visibility into how sensitive data is flowing through AI and how your users are interacting with generative AI applications is essential. Without proper visibility, organizations struggle to safeguard their assets effectively. Organizations want to get ahead of and minimize the inherent risks of data being shared with generative AI applications, such as data oversharing, data leakage and non-compliant use of GenAI apps. Instead of restricting AI use to avoid these outcomes, security teams can mitigate and manage risks more effectively by proactively gaining visibility into AI usage within the organization and implementing corresponding protection and governance controls.
On top of that, evolving regulatory environments and rapid technological advancements create complex challenges for customers. Adhering to new regulations, particularly those pertaining to cutting-edge technologies like GenAI, is essential for devising an effective security and compliance strategy. In this era where AI regulations and standards, such as the EU AI Act and NIST AI RMF, are taking shape, it is imperative for organizations to develop and use AI applications in a manner that is safe, transparent and responsible. According to Gartner®, “by 2027 at least one global company will see its AI deployment banned by a regulator for noncompliance with data protection or AI governance legislation.” [3] AI will be a catalyst for regulatory changes, and having secure and compliant AI will become fundamental.
At Microsoft Ignite 23’ and Microsoft Secure 24’, we introduced new capabilities to help organizations discover, protect and govern data in an AI-first world with Microsoft Purview.
Today, we are excited to announce new innovations from Microsoft Purview to help you secure and govern AI:
Microsoft Purview AI Hub, which helps organizations discover how AI applications such as Copilot for M365 and third-party AI apps are being used in their organization and provides ready-to-use policies to protect data, is now available in public preview.
New insights into unlabeled files and SharePoint sites referenced by Microsoft Copilot for Microsoft 365 will also be included in the public preview release of the AI Hub. This helps organizations prioritize the most critical data risks and put in place protection policies to prevent potential oversharing of sensitive data.
New insights into non-compliant and unethical use of AI interactions will also be included in the public preview release of the AI Hub. This helps organizations quickly gain insight into unethical use such as regulatory collusion, money laundering, targeted harassment and more.
New Compliance Manager assessment templates for EU AI Act, NIST AI RMF, ISO/IEC 23894:2023 and ISO/IEC 42001 to help assess, implement and strengthen compliance controls to meet AI regulatory requirements and standards. These insights will also be surfaced in the AI Hub and available in public preview.
Discover how AI applications are being used
To help customers gain a better understanding of which AI applications are being used and how – we are announcing the public preview of Microsoft Purview AI Hub – which includes insights like sensitive data shared with AI apps (whether Copilot for M365 or third-party AI apps), total number of users interacting with AI apps and their associated risk level, pulled from Microsoft Purview Insider Risk Management, and more.
As organizations adopt Copilot for Microsoft 365, data security controls become paramount to avoid potential overexposure of sensitive data or SharePoint sites. And we know that it is challenging to manage and label vast amounts of information, often leaving sensitive data vulnerable to data oversharing. Microsoft Purview AI Hub addresses this challenge by surfacing unlabeled files and SharePoint sites referenced by Copilot, helping you prioritize your most critical data risks and prevent potential oversharing of sensitive data.
Read the full post here: Secure your data to confidently take advantage of Generative AI with Microsoft Purview Read More
Time is almost up! Upgrade your Azure Logic Apps Integration Service Environment workloads
Calling all Azure Logic Apps Integration Service Environment users! As we near the August 31, 2024, deadline, it has become imperative for you to complete your upgrade from Integration Service Environments (ISE) to Logic Apps Standard. After that date, your currently deployed ISE instances will no longer be supported, and service will be disrupted. We understand, however, that this migration may cause some disruption to your existing systems—that’s why we’re committed to making this transition as smooth and secure as possible for our valued customers.
Find more about the many benefits of upgrading to Logic Apps Standard and explore the tools and resources available from Microsoft to help you expedite your upgrade. Our commitment goes beyond providing these resources – our support team is here to assist you throughout the migration process. Let’s work together to ensure your workloads continue to run flawlessly on Azure Logic Apps Standard.
Experience the power of Logic Apps Standard
After August 31st, 2024, access to deployed Azure Logic Apps Integration Service Environments will be terminated, meaning any workflows currently running on these ISEs will cease execution, all historical data associated with these workflows will be permanently deleted, and any integration accounts linked to the retired ISEs will be removed.
To ensure your integration solutions continue to function smoothly, we strongly encourage you to prioritize migrating to Logic Apps Standard before the deadline. Logic Apps Standard is more than just an upgrade — it’s a leap forward. By upgrading your workloads from Integration Service Environment you’ll enjoy these exciting new features:
Align enterprise-level workflows with the broader application PaaS ecosystem, leveraging improvements in the ecosystem.
Cost optimizations get a timely remedy – the granular and elastic scaling, both help in dynamically adapting cost with load changes.
Cloud-native development advancements – local development, debugging, enhanced support for source controls – helping you achieve better ROI.
Seamless extensibility, with support for code extensions to be executed natively within logic apps workflows – minimizing your footprint and taking the most out of your compute.
Automated deployment and code logic decoupled from infra deployment are instrumental in accelerating value to customers, including support for mission critical applications with zero-downtime deployment options.
Support for network isolation and access to on-premises resources is available natively in Logic Apps Standard.
With Logic Apps Standard, you get all this and more with built-in connectors for connector execution isolation, like ISE connectors.
Start your upgrade today with our migration tool
We’ve worked hard to make migrating your workflows to Logic Apps Standard as worry free as possible. The “Export to Logic Apps Standard” tool, now generally available in the Visual Studio Code extension, simplifies exporting and organizing workflows into a Logic Apps Standard project. You can then leverage the power of Visual Studio Code for local updates, testing, and debugging before redeploying directly or integrating seamlessly into your DevOps processes.
Migrating unlocks valuable features like native networking, enterprise connectors, improved performance, and freedom from throttling limits. Learn more with these detailed instructions and empower your workflows with the full potential of Logic Apps Standard!
Need extra support? Azure experts are here to help
We understand that migration can seem daunting, but we’re here to help! Other users have found useful our recent Learn Live session, hosted by Azure experts, for demystifying the process of migrating an Integration Service Environment to Logic Apps Standard. The session provides an overview of the process, the recommended migration tools, how to organize and export logic apps, and insights into running, testing, and debugging locally.
For any questions you might have during your migration, we have an FAQ page and a dedicated thread you can reference. You can also reach out to Azure support for assistance or solutions. Let’s work together to ensure a seamless transition and keep your integration solutions running flawlessly.
Microsoft Tech Community – Latest Blogs –Read More
Custom Rule to qurantine emails in M365 based on total Number of Recipients
Lately we have been getting thousands of emails from Gmail which have pdfs and links. Last week we were hit with around 1.5 million emails which the ATP could not stop( we have A5 license). We created rules which says if attachment has specific name example Oddname.pdf then delete the email.
We are not in position to block gmail domain or block all emails which has pdf attachments.
Can we have a custom rule which based on number of recipients. Example —>if email has more then 100 recipients and gmail.com domain then quarantine the email or delete them.
Lately we have been getting thousands of emails from Gmail which have pdfs and links. Last week we were hit with around 1.5 million emails which the ATP could not stop( we have A5 license). We created rules which says if attachment has specific name example Oddname.pdf then delete the email. We are not in position to block gmail domain or block all emails which has pdf attachments. Can we have a custom rule which based on number of recipients. Example —>if email has more then 100 recipients and gmail.com domain then quarantine the email or delete them. Read More
On the SharePoint Start Page is there any way to moderate the news that shows there?
On SharePoint.com (start page) news items from various sites that you may have access to shows up. Is there any way to modify/configure what news is visible on this page? Thanks,
On SharePoint.com (start page) news items from various sites that you may have access to shows up. Is there any way to modify/configure what news is visible on this page? Thanks, Read More
File Transfer for Entra ID Join Devices
Hello,
We recently moved to Intune Suite Licenses to give us better control and analytics of our endpoints. One feature requested now is the ability to file transfer to endpoints. We are strictly an Entra ID/Azure organization, so the normal \endpointname/c$ doesn’t work.
Any suggestions?
Hello, We recently moved to Intune Suite Licenses to give us better control and analytics of our endpoints. One feature requested now is the ability to file transfer to endpoints. We are strictly an Entra ID/Azure organization, so the normal \endpointname/c$ doesn’t work. Any suggestions? Read More
How Do I Fix QuickBooks Error 15241 When Payroll Update Failed Error
QuickBooks, the renowned accounting software, serves as a lifeline for countless businesses, aiding in financial management with efficiency and precision. However, like any software, it isn’t immune to errors. One such common hiccup is QuickBooks Error 15241, which can disrupt your workflow if left unresolved. In this article, we’ll delve into the depths of this error, exploring its origins, reasons behind its occurrence, and offering comprehensive solutions to tackle it effectively.
What is QuickBooks Error 15241?
QuickBooks Error 15241 manifests as an issue related to the QuickBooks payroll function, primarily impacting the update process. Typically, users encounter this error when attempting to update their QuickBooks Desktop or payroll software. The error message usually reads: “Error 15241: The payroll update did not complete successfully. A file cannot be validated.” This error impedes the smooth functioning of the software, causing frustration and hampering productivity.
Reasons Behind QuickBooks Error 15241:
Incomplete Installation: One of the primary culprits behind Error 15241 is an incomplete installation of QuickBooks Desktop software or a corrupted download. If any files related to the software are missing or damaged, it can trigger this error during the update process.
Insufficient User Permissions: Limited user permissions or restrictions can also lead to Error 15241. QuickBooks requires adequate permissions to perform various tasks, including updates. If the user account lacks the necessary permissions, it can result in this error.
Damaged Windows Registry: Issues within the Windows registry, such as corrupt entries related to QuickBooks or payroll, can contribute to Error 15241. Registry errors often occur due to improper uninstallation of software or malware infections.
Conflicting Third-Party Applications: Sometimes, conflicts with other third-party applications installed on the system can interfere with QuickBooks updates, triggering Error 15241. Antivirus programs, firewall settings, or anti-malware software may mistakenly flag QuickBooks processes as potential threats, causing update failures.
Solutions to QuickBooks Payroll Update Failed Error 15241
Solution 1: Re-enable QuickBooks FCS
Close QuickBooks and ensure no QuickBooks processes are running in the background.Press Windows + R to open the Run dialog, then type “services.msc” and hit Enter.In the Services window, locate “Intuit QuickBooks FCS” and double-click on it.In the Properties window, set the Startup type to “Manual” and click Apply.Click on Start to initiate the service and then click OK.Restart QuickBooks and check if the issue persists.
Solution 2: Run QuickBooks Desktop as Administrator
Right-click on the QuickBooks Desktop icon.Select “Run as administrator” from the context menu.Try performing the task that triggered Error 15241 again.
Solution 3: Update QuickBooks Desktop
Close QuickBooks Desktop.Download and install the latest updates for QuickBooks Desktop.After the update is complete, restart your computer and reopen QuickBooks.Check if the error has been resolved.
Solution 4: Verify Windows FCS Settings
Press Windows + R to open the Run dialog.Type “services.msc” and hit Enter.In the Services window, locate “Windows File Copy Service (FCS)” and double-click on it.Set the Startup type to “Automatic” and click Apply.If the service is stopped, click on Start, then click OK.Restart your computer and check if the issue persists.
By following these solutions, users can effectively resolve QuickBooks Error 15241 and resume their payroll and other financial activities without interruption.
QuickBooks, the renowned accounting software, serves as a lifeline for countless businesses, aiding in financial management with efficiency and precision. However, like any software, it isn’t immune to errors. One such common hiccup is QuickBooks Error 15241, which can disrupt your workflow if left unresolved. In this article, we’ll delve into the depths of this error, exploring its origins, reasons behind its occurrence, and offering comprehensive solutions to tackle it effectively.What is QuickBooks Error 15241?QuickBooks Error 15241 manifests as an issue related to the QuickBooks payroll function, primarily impacting the update process. Typically, users encounter this error when attempting to update their QuickBooks Desktop or payroll software. The error message usually reads: “Error 15241: The payroll update did not complete successfully. A file cannot be validated.” This error impedes the smooth functioning of the software, causing frustration and hampering productivity.Reasons Behind QuickBooks Error 15241:Incomplete Installation: One of the primary culprits behind Error 15241 is an incomplete installation of QuickBooks Desktop software or a corrupted download. If any files related to the software are missing or damaged, it can trigger this error during the update process.Insufficient User Permissions: Limited user permissions or restrictions can also lead to Error 15241. QuickBooks requires adequate permissions to perform various tasks, including updates. If the user account lacks the necessary permissions, it can result in this error.Damaged Windows Registry: Issues within the Windows registry, such as corrupt entries related to QuickBooks or payroll, can contribute to Error 15241. Registry errors often occur due to improper uninstallation of software or malware infections.Conflicting Third-Party Applications: Sometimes, conflicts with other third-party applications installed on the system can interfere with QuickBooks updates, triggering Error 15241. Antivirus programs, firewall settings, or anti-malware software may mistakenly flag QuickBooks processes as potential threats, causing update failures.Solutions to QuickBooks Payroll Update Failed Error 15241Solution 1: Re-enable QuickBooks FCSClose QuickBooks and ensure no QuickBooks processes are running in the background.Press Windows + R to open the Run dialog, then type “services.msc” and hit Enter.In the Services window, locate “Intuit QuickBooks FCS” and double-click on it.In the Properties window, set the Startup type to “Manual” and click Apply.Click on Start to initiate the service and then click OK.Restart QuickBooks and check if the issue persists.Solution 2: Run QuickBooks Desktop as AdministratorRight-click on the QuickBooks Desktop icon.Select “Run as administrator” from the context menu.Try performing the task that triggered Error 15241 again.Solution 3: Update QuickBooks DesktopClose QuickBooks Desktop.Download and install the latest updates for QuickBooks Desktop.After the update is complete, restart your computer and reopen QuickBooks.Check if the error has been resolved.Solution 4: Verify Windows FCS SettingsPress Windows + R to open the Run dialog.Type “services.msc” and hit Enter.In the Services window, locate “Windows File Copy Service (FCS)” and double-click on it.Set the Startup type to “Automatic” and click Apply.If the service is stopped, click on Start, then click OK.Restart your computer and check if the issue persists.By following these solutions, users can effectively resolve QuickBooks Error 15241 and resume their payroll and other financial activities without interruption. Read More
Removing personal accounts when enrolled
Hello,
My IT manager has enforced conditional access so everyone needs to enrol. My iPhone is enrolled but I can no longer sign in to Outlook or OneDrive with my personal account (this account is a O365 tenant that I made for learning and is used as my personal address).
He is unsure what’s been changed to cause this.
Can someone advise what we need to do to allow more than 1 O365 address to use Outlook & OneDrive, along side the company enrolled details?
Kind regards
Hello, My IT manager has enforced conditional access so everyone needs to enrol. My iPhone is enrolled but I can no longer sign in to Outlook or OneDrive with my personal account (this account is a O365 tenant that I made for learning and is used as my personal address). He is unsure what’s been changed to cause this. Can someone advise what we need to do to allow more than 1 O365 address to use Outlook & OneDrive, along side the company enrolled details? Kind regards Read More
CDC: how to read history records of master->detail tables?
I have 2 tables T1(master), T2(detail). CDC works on these both tables.
I’d like to restore history tables to th new 2 tables T11->T21 using stored procedure.
The question is: how to process the history tables correctly?
If I get and process all T1 history records and after it all T2 there is can be referential integrity conflict.
For example: my SP processes all master rows: D, I, D, I and then details from the start to end of the history.
What is the best way?
I have 2 tables T1(master), T2(detail). CDC works on these both tables.I’d like to restore history tables to th new 2 tables T11->T21 using stored procedure.The question is: how to process the history tables correctly?If I get and process all T1 history records and after it all T2 there is can be referential integrity conflict.For example: my SP processes all master rows: D, I, D, I and then details from the start to end of the history.What is the best way? Read More
New Feedback Opportunity
Hello!
I am pleased to inform you of a new enhancement to your Microsoft E5 license. We have introduced Enterprise IoT, a solution that enables the monitoring and protection of IoT devices within office environments, including printers, cameras, and scanners. By turning on Enterprise IoT apart from getting alerts and recommendations, you will get vulnerability and misconfiguration data, purpose-built for IoT devices.
Activation is a breeze: Getting started is as easy as turning on a toggle in your Defender XDR Portal. Follow this documentation to set it up.
Bonus Protection: For every E5 license you have, we provide complimentary protection for 5 IoT devices. That means if you have 20 E5 licenses, you can secure up to 100 devices at no extra cost! Curious about the details? Our documentation will guide you on how to calculate the number of devices you can protect.
Your Experience Matters: We are dedicated to continuous improvement and your input is invaluable. Please take a moment to share your thoughts through a short survey.
Let’s Connect: Interested in a deeper dive into Enterprise IoT or other Microsoft Security solutions? Simply reply to this email and we’ll arrange a conversation with a product manager from our Microsoft Engineering team.
Thank you!
Hello!
I am pleased to inform you of a new enhancement to your Microsoft E5 license. We have introduced Enterprise IoT, a solution that enables the monitoring and protection of IoT devices within office environments, including printers, cameras, and scanners. By turning on Enterprise IoT apart from getting alerts and recommendations, you will get vulnerability and misconfiguration data, purpose-built for IoT devices.
Activation is a breeze: Getting started is as easy as turning on a toggle in your Defender XDR Portal. Follow this documentation to set it up.
Bonus Protection: For every E5 license you have, we provide complimentary protection for 5 IoT devices. That means if you have 20 E5 licenses, you can secure up to 100 devices at no extra cost! Curious about the details? Our documentation will guide you on how to calculate the number of devices you can protect.
Your Experience Matters: We are dedicated to continuous improvement and your input is invaluable. Please take a moment to share your thoughts through a short survey.
Let’s Connect: Interested in a deeper dive into Enterprise IoT or other Microsoft Security solutions? Simply reply to this email and we’ll arrange a conversation with a product manager from our Microsoft Engineering team.
Thank you! Read More