Category: Microsoft
Category Archives: Microsoft
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Known issue: Voice calling on Apple devices running iOS/iPadOS 17.2
We’ve recently received a few cases where some users are experiencing issues with voice calls after updating their iOS/iPadOS devices to 17.2.
Apple’s aware of the issue and are actively working on a resolution. We’ll keep this post updated as we learn more, and a fix becomes available.
Microsoft Tech Community – Latest Blogs –Read More
Known issue: Voice calling on Apple devices running iOS/iPadOS 17.2
We’ve recently received a few cases where some users are experiencing issues with voice calls after updating their iOS/iPadOS devices to 17.2.
Apple’s aware of the issue and are actively working on a resolution. We’ll keep this post updated as we learn more, and a fix becomes available.
Microsoft Tech Community – Latest Blogs –Read More
Best practices for designing Word, Excel, and PowerPoint add-ins
Designing an add-in in Word, Excel, or PowerPoint can be a challenging task, but with the right approach you can inspire users and help them solve problems with a positive experience. In this blog post, we’ll explore some considerations and strategies to design an effective add-in. Whether you’re a seasoned developer or starting out, these tips will help you create an add-in that is intuitive, user-friendly, and valuable to your users. Let’s dive in and discover the best practices for designing an add-in that stands out from the crowd!
Name your add-in effectively
The average attention span for a user to a product or design is 8 seconds. Choosing the right name for your add-in is crucial to its success. Two key tips to keep in mind when selecting a name are:
1) Reflect the add-in’s core functionality
2) Be direct and memorable
If you already have a well-known branding name, don’t hesitate to include your brand first. Also, the name should give users a clear idea of what the add-in does and how it can benefit them. For example, if your add-in is a writing assistant, consider a name like ‘GrammarGuard’ or ‘ LanguageLift ‘ that clearly communicates its purpose. Additionally, the name should be easy to remember and stand out from other add-ins in the same category. Avoid using overly complex or generic names that get lost in the crowd. Don’t forget to check Microsoft Trademark and Brand guidelines.
Provide a detailed description
Your description provides a second chance to make a good impression. A well-crafted description succinctly conveys the key benefits and features of your add-in in a way that is easy to understand and memorable. Ideally, keep your description under two lines (less than 60 characters). It allows users to quickly understand what your add-in does and how it helps them in under ten seconds.
To create an effective two-line description, it’s important to include your add-in’s value proposition and the specific tasks it can help users accomplish. If your add-in is an artificial intelligent writing assistant, your description might read ‘Improve grammar, spelling, punctuation, and style in written content with our service.’
Design your UI to integrate with Office
Follow the Office design principles to create a positive add-in experience.
Design explicitly for Office. Your add-in UI design must integrate seamlessly with Office to provide efficient, natural interaction for your users. The functionality, as well as the look and feel, of an add-in must harmoniously complement the Office experience. Consider using Fluent UI for the web as your design language and tool set. The Fluent UI for the web has two versions.
For React UIs: use Fluent UI React, a React front-end framework designed to build experiences that fit seamlessly into a broad range of Microsoft products. It provides robust, up-to-date, accessible React-based components which are highly customizable using CSS-in-JS. To get started, see Fluent UI React Components. (More resources, see Fluent UI React in Office Add-ins).
For non-React UIs: Use Fabric Core, an open-source collection of CSS classes and Sass mixings that give you access to colors, animations, fonts, icons, and grids. To get started, see Fabric Core in Office Add-ins.
Favor content over chrome. Allow customers’ page, slide, or spreadsheet to remain the focus of the experience.
Make it enjoyable and keep users in control.
Design for all platforms and input methods.
Onboard inside the app
A first-run experience (FRE) is presented when a user opens an add-in for the first time. It provides them with insight into the functions, features, and benefits of the add-in. This experience helps shape the user’s impression of an add-in and strongly influences their likelihood to come back to and continue using your add-in.
Please remember, don’t make users register or sign up first. This can be a blocker for users to try the real functionality. A smooth and easy register experience gives users the opportunity to complete an action that positively affects their perception of the add-in. For more information, see First-run experience patterns for Office Add-ins – Office Add-ins | Microsoft Learn.
Choose the freemium business model
Lastly, consider monetizing your add-in after gaining sufficient traffic. The freemium business model is a great way to attract customers, build a user base, and generate revenue. Freemium is a pricing strategy where you offer a basic version of the product or service for free, while charging for advanced features or premium versions.
By offering a free version of a product, companies can attract a larger audience and build a user base that can later be converted into paying customers. Once users are familiar with the product, they are more likely to upgrade to the premium version to access additional features. Additionally, offering a free version of a product can reduce the cost of acquiring new customers, as users can try the product before they purchase. Finally, the freemium model makes it easier to increase brand awareness and generate buzz around a product.
Get started
Make your first add-in in minutes:
Develop Office Add-ins
Sample add-ins:
Add AI-generated content to your Word document
Get data from an Excel spreadsheet for a mail merge
Create PowerPoint presentations with unique designs
Microsoft Tech Community – Latest Blogs –Read More
Dive into the World of AI with the Semantic Kernel Cookbook
If you’re interested in AI and looking for a hands-on way to dive deeper, the Semantic Kernel Cookbook on GitHub is a resource you won’t want to miss.
Since the release of Semantic Kernel in March of 2023, we’ve managed to see a community of AI engineers emerge from around the globe. And Kinfey Lo’s “Semantic Kernel Cookbook” is certain to enable even more “AI chefs” to find their path to combining native code with semantic code. How? By learning how to cook with AI in SK by discovering the joys of Plugins, Planners, and Personas.
We’re all learning together — in the open. And we know that the best way to build a community is through sharing recipes so we can all learn together. Faster. Open source has a wonderful capability to enable greater learning by just being a member of one of the open-source communities. Showing up counts! Since you’ve chosen to show up, definitely try out some of Kinfey’s cooking. And if you’re in the mood for it, make your own recipe for AI with SK and share it back.
With respect and love,
—The Semantic Kernel Team @ Microsoft
What is the Semantic Kernel Cookbook?
The Semantic Kernel Cookbook is a repository hosted by Microsoft on GitHub. It’s designed to help developers integrate cutting-edge Large Language Models (LLMs) like OpenAI, Azure OpenAI, and Hugging Face with conventional programming languages like C#, Python, and Java.
Session
Intro
.NET
Python
Getting started with LLM
Begin to know LLM, including OpenAI, Azure OpenAI Service and LLM on Hugging face
Using Azure OpenAI Service With SDK
Learn how to use Azure OpenAI Service with SDK
Click
Click
Foundations of Semantic Kernel
What is Semantic Kernel? What are its advantages and disadvantages? Semantic Kernel related concepts, etc.
Click
Click
The skills of LLM – Plugins
We know that communicating with LLM requires the use of prompt engineering?
For enterprise applications, there are many business-oriented prompt engineering.
In Semantic Kernel we call it Plugins. In this session we will introduce how to use Semantic
Kernel Plugins and how to define your own Plugins
Click
Click
Planner – Let LLM have planning work
Human beings need to complete a job step by step, and the same goes for LLMs.
Semantic Kernel has a very powerful task planning capability – Planner, in this session we will explain in detail how to define and use Planner to make your application more intelligent
Click
Click
Embedding Skills
Building RAG applications is the most commonly used LLM solution at this stage. It is very convenient to build RAG applications through Semantic Kernel.
This session will tell you how to use Semantic Kernel Embeddings
Click
Click
HandsOnLab
Through three hands on labs projects, let everyone truly understand the application
of Semantic Kernel
Click
Click
Why Use the Semantic Kernel Cookbook?
Using the Semantic Kernel Cookbook, you can define plugins that can be chained together in just a few lines of code. What makes Semantic Kernel special, however, is its ability to automatically orchestrate plugins with AI. With Semantic Kernel planners, you can ask an LLM to generate a plan that achieves a user’s unique goal. Afterwards, Semantic Kernel will execute the plan for the user.
Getting Started with Semantic Kernel Cookbook
Getting started with the Semantic Kernel Cookbook is simple. The Semantic Kernel SDK is available in C#, Python . To get started, choose your preferred language and follow the instructions provided in the repository.
Conclusion
The Semantic Kernel Cookbook is a unique opportunity to dive into the world of AI and programming languages. Whether you’re a beginner or an experienced developer, this resource offers valuable learning experiences and the chance to connect with a global community of tech enthusiasts. So why wait?
Visit the following resources and start your AI journey:
Semantic Kernel Cookbook
Semantic Kernel is at the center of the agent stack
Why use an SDK like Semantic Kernel?
Get started using the Semantic Kernel SDK
AI is suddenly everywhere. Do you need to go and get a shiny machine learning degree to remain competitive? John Maeda says not to worry. He’ll show you how to cook delicious dishes into your coding repertoire with his new show – Mr. Maeda’s Cozy AI Kitchen.
Mr. Maeda’s Cozy AI Kitchen (youtube.com)
Microsoft Tech Community – Latest Blogs –Read More
Best practices for designing Word, Excel, and PowerPoint add-ins
Designing an add-in in Word, Excel, or PowerPoint can be a challenging task, but with the right approach you can inspire users and help them solve problems with a positive experience. In this blog post, we’ll explore some considerations and strategies to design an effective add-in. Whether you’re a seasoned developer or starting out, these tips will help you create an add-in that is intuitive, user-friendly, and valuable to your users. Let’s dive in and discover the best practices for designing an add-in that stands out from the crowd!
Name your add-in effectively
The average attention span for a user to a product or design is 8 seconds. Choosing the right name for your add-in is crucial to its success. Two key tips to keep in mind when selecting a name are:
1) Reflect the add-in’s core functionality
2) Be direct and memorable
If you already have a well-known branding name, don’t hesitate to include your brand first. Also, the name should give users a clear idea of what the add-in does and how it can benefit them. For example, if your add-in is a writing assistant, consider a name like ‘GrammarGuard’ or ‘ LanguageLift ‘ that clearly communicates its purpose. Additionally, the name should be easy to remember and stand out from other add-ins in the same category. Avoid using overly complex or generic names that get lost in the crowd. Don’t forget to check Microsoft Trademark and Brand guidelines.
Provide a detailed description
Your description provides a second chance to make a good impression. A well-crafted description succinctly conveys the key benefits and features of your add-in in a way that is easy to understand and memorable. Ideally, keep your description under two lines (less than 60 characters). It allows users to quickly understand what your add-in does and how it helps them in under ten seconds.
To create an effective two-line description, it’s important to include your add-in’s value proposition and the specific tasks it can help users accomplish. If your add-in is an artificial intelligent writing assistant, your description might read ‘Improve grammar, spelling, punctuation, and style in written content with our service.’
Design your UI to integrate with Office
Follow the Office design principles to create a positive add-in experience.
Design explicitly for Office. Your add-in UI design must integrate seamlessly with Office to provide efficient, natural interaction for your users. The functionality, as well as the look and feel, of an add-in must harmoniously complement the Office experience. Consider using Fluent UI for the web as your design language and tool set. The Fluent UI for the web has two versions.
For React UIs: use Fluent UI React, a React front-end framework designed to build experiences that fit seamlessly into a broad range of Microsoft products. It provides robust, up-to-date, accessible React-based components which are highly customizable using CSS-in-JS. To get started, see Fluent UI React Components. (More resources, see Fluent UI React in Office Add-ins).
For non-React UIs: Use Fabric Core, an open-source collection of CSS classes and Sass mixings that give you access to colors, animations, fonts, icons, and grids. To get started, see Fabric Core in Office Add-ins.
Favor content over chrome. Allow customers’ page, slide, or spreadsheet to remain the focus of the experience.
Make it enjoyable and keep users in control.
Design for all platforms and input methods.
Onboard inside the app
A first-run experience (FRE) is presented when a user opens an add-in for the first time. It provides them with insight into the functions, features, and benefits of the add-in. This experience helps shape the user’s impression of an add-in and strongly influences their likelihood to come back to and continue using your add-in.
Please remember, don’t make users register or sign up first. This can be a blocker for users to try the real functionality. A smooth and easy register experience gives users the opportunity to complete an action that positively affects their perception of the add-in. For more information, see First-run experience patterns for Office Add-ins – Office Add-ins | Microsoft Learn.
Choose the freemium business model
Lastly, consider monetizing your add-in after gaining sufficient traffic. The freemium business model is a great way to attract customers, build a user base, and generate revenue. Freemium is a pricing strategy where you offer a basic version of the product or service for free, while charging for advanced features or premium versions.
By offering a free version of a product, companies can attract a larger audience and build a user base that can later be converted into paying customers. Once users are familiar with the product, they are more likely to upgrade to the premium version to access additional features. Additionally, offering a free version of a product can reduce the cost of acquiring new customers, as users can try the product before they purchase. Finally, the freemium model makes it easier to increase brand awareness and generate buzz around a product.
Get started
Make your first add-in in minutes:
Develop Office Add-ins
Sample add-ins:
Add AI-generated content to your Word document
Get data from an Excel spreadsheet for a mail merge
Create PowerPoint presentations with unique designs
Microsoft Tech Community – Latest Blogs –Read More
Embedding a Microsoft 365 Chat (Copilot) Window on a SharePoint Site
We are looking to embed Microsoft 365 Chat on a SharePoint site as a web part or have it appear as a modal/dialog window when this site is launched or a button is clicked. I have seen instructions to do this for custom Copilot chatbot experiences created with Copilot Studio. Has anyone done this with Microsoft 365 Chat?
We are looking to embed Microsoft 365 Chat on a SharePoint site as a web part or have it appear as a modal/dialog window when this site is launched or a button is clicked. I have seen instructions to do this for custom Copilot chatbot experiences created with Copilot Studio. Has anyone done this with Microsoft 365 Chat? Read More
Optimizing Vector Similarity Search on Azure Data Explorer – Performance Update
This post is co-authored by @Anshul_Sharma (Senior Program Manager, Microsoft).
This blog is an update of Optimizing Vector Similarity Searches at Scale. We continue to improve the performance of vector similarity search in Azure Data Explorer (Kusto). We present the new functions and policies to maximize performance and the resulting search times.
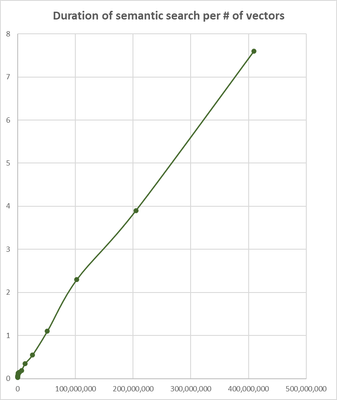
The following table and chart present the search time for the top 3 most similar vectors to a supplied vector:
# of vectors
Total time
[sec.]
25,000
0.03
50,000
0.035
100,000
0.047
200,000
0.062
400,000
0.094
800,000
0.125
1,600,000
0.14
3,200,000
0.15
6,400,000
0.19
12,800,000
0.35
25,600,000
0.55
51,200,000
1.1
102,400,000
2.3
204,800,000
3.9
409,600,000
7.6
This benchmark was done on a medium size Kusto cluster (containing 29 nodes), searching for the most similar vectors in a table of Azure OpenAI embedding vectors. Each vector was generated using ‘text-embedding-ada-002’ embedding model and contains 1536 coefficients.
These are the steps to achieve the best performance of similarity search:
Use series_cosine_similarity(), the new optimized native function to calculate cosine similarity
Set the encoding of the embeddings column to Vector16, the new 16 bit encoding of the vectors coefficients (instead of the default 64 bit)
Store the embedding vectors table on all nodes with at least one shard per processor. This can be achieved by limiting the number of embedding vectors per shard by altering ShardEngineMaxRowCount of the sharding policy and RowCountUpperBoundForMerge of the merging policy.
Suppose our table contains 1M vectors and our Kusto cluster has 20 nodes each has 16 processors. The table’s shards should contain at most 1000000/(20*16)=3125 rows. These are the KQL commands to create the empty table and set the required policies and encoding:
.create table embedding_vectors(vector_id:long, vector:dynamic) // more columns can be added
.alter-merge table embedding_vectors policy sharding ‘{ “ShardEngineMaxRowCount” : 3125 }’
.alter-merge table embedding_vectors policy merge ‘{ “RowCountUpperBoundForMerge” : 3125 }’
.alter column embedding_vectors.vector policy encoding type = ‘Vector16’
Now we can ingest the vectors into the table.
And here is a typical search query:
let searched_vector = repeat(1536, 0); // to be replaced with real embedding vector.
embedding_vectors
| extend similarity = series_cosine_similarity_fl(vector, searched_vector, 1, 1)
| top 10 by similarity desc
The current semantic search times enable usage of ADX as embedding vectors storage platform for RAG (Retrieval Augmented Generation) scenarios and beyond,
We continue to improve vector search performance, stay tuned!
Microsoft Tech Community – Latest Blogs –Read More
Skilling snack: Windows hardware security introduction
In today’s Zero Trust and chip-to-cloud security efforts, hardware plays an important role. Whether your organization is renewing hardware or hardening the existing one, let’s cover some basics. Even if these concepts are already familiar to you, consider sharing them with your users or those earlier in the career. Otherwise, choose your own adventure among resources on hardware root-of-trust, silicon-assisted security, and secured-core PCs.
Time to learn:132 minutes
READ
Device protection in Windows Security
Windows Security provides built-in security options to help protect your organization’s device from malicious software attacks. Start your security training with Device security. Walk through details and options for core isolation, security processor, secure boot, and different levels of hardware security capability.
(4 mins)
Windows + Device + Security + VBS + TPM + UEFI + Rootkit + Secure Boot + SMM
LEARN
Start here to learn how Zero Trust principles apply from chip to cloud. Complete this beginner 700-XP learning module to learn about infrastructure as one of the components, and how it fits into your overall security strategy.
(12 mins)
Zero Trust + Security + Identity + Endpoints + Applications + Network + Infrastructure + Data
Hardware root-of-trust
READ
How System Guard helps protect Windows (12 mins)
Ensure trustworthiness of your Windows OS firmware and hardware with System Guard. Maintain the integrity of the system against advanced attacks targeting the most foundational layers of a system with Dynamic Root of Trust for Measurement (DRTM) and System Management Mode (SMM) protections. Learn about integrity validation from boot to run time. Finally, review your requirements to use System Guard.
Trusted Platform Module Technology Overview (5 mins)
Let’s define and describe TPM as a measure of access control and authentication. Review requirements for using this feature as well as practical applications. While Windows 11 and Windows 10 systems automatically start the TPM, review considerations for Group Policy settings and device health attestation.
Hardware Root of Trust + System Guard + Integrity + TPM + SRTM + DRTM + UEFI + SMM + Silicon + Group Policy + RSA + SoC + CPU + Firmware
Silicon-assisted security
READ
Virtualization-based Security (VBS) (5 mins)
VBS is an isolated virtual environment that hosts security solutions that are protected from even the most highly privileged malware running on the OS. Follow an example of a VBS solution related to memory integrity or hypervisor-protected code integrity (HVCI). Review hardware requirements for VBS and nested virtualization support.
Enable memory integrity (12 mins)
Memory integrity is a VBS feature that protects against exploitations of the Windows kernel. Read about its features, enablement guidance, troubleshooting, and deployment in virtual machines. You can use Windows Security settings, Microsoft Intune, Configuration Manager, various policies, or registry keys.
Kernel Direct Memory Access (DMA) Protection (7 mins)
Additional protections are available for drive-by DMA attacks, which happen in the absence of the user. Get an overall understanding of this threat and how Kernel DMA Protection works. Check if you meet compatibility and licensing requirements. This feature will normally be enabled automatically, but you can follow simple steps to check if it is. Browse frequently asked questions for additional details.
VBS + Memory Integrity + HVCI + VM + TPM + Kernel + MDM + Intune + ConfigMgr + Policies + UEFI + Reg + WDAC + PowerShell + DMA
READ
Do you know how Microsoft collaborates with original equipment manufacturers (OEMs) for built-in hardware security capabilities? The capabilities include baseline Windows security, virtualization-based security, and System Guard. Read about the features and benefits of Secured-core PCs.
(3 mins)
Secured-Core PC + VBS + TPM + Secure Boot + BitLocker + Baseline + HVCI + ESS + Windows Hello + Firmware
LISTEN
Pluton: The New Bedrock for Device Security – Security Unlocked
Curious about Microsoft Pluton security processor? Listen to this podcast to learn about its history and its architecture. Dive deep into some threat factors today and prepare for the future. Furthermore, find practical insights from a Threat Intel Librarian who joins the conversation about tools and platforms for hardware security.
(48 mins)
Pluton + Security + CPU + Secure Boot + SoC + Xbox + Intel
WATCH
Windows 11 Security — Our Hacker-in-Chief Runs Attacks and Shows Solutions
Peek behind the curtain of common remote and in-person attacks. Watch how our security expert uses Virtualization-based Security, Trusted Platform Module, UEFI, Secure Boot, and Trusted Boot to deflect sophisticated malware and attacks at the hardware level.
(17 mins)
Hardware + Security + Attacks + VBS + TPM + UEFI + Secure Boot + Trusted Boot + Windows 11
Bookmark the Windows 11 Security Book for the complete chip-to-cloud story!
Did you find anything particularly fit for your taste? How can we spice it up for you?
Our collection of Windows skilling snacks: bite-sized learning for IT pros is always growing, and we’d love to hear your thoughts and ideas!
Continue the conversation. Find best practices. Bookmark the Windows Tech Community, then follow us @MSWindowsITPro on X/Twitter. Looking for support? Visit Windows on Microsoft Q&A.
Microsoft Tech Community – Latest Blogs –Read More
Can i setup teams meetings to only show on the teams device tablet in the room and not on the tv ?
I have a request to not show the upcoming meetings on the television connected to the teams device. Is this possible ? They want to show them only on the tablet
I have a request to not show the upcoming meetings on the television connected to the teams device. Is this possible ? They want to show them only on the tablet Read More
Ethical AI: Nurup Naimju’s Vision for Responsible Growth in AI Entrepreneurship
About the series: Build it with AI is a Microsoft Reactor series hosting AI entrepreneurs who share their experiences and learnings in their path of building innovative solutions with AI.
About this episode: Register Now Events | Microsoft Reactor 23rd January 2024
In this episode Nurup Naimju Co Founder of 3-2-1 GoCheck | Background checking made easy
Nurup discusses Responsible AI and ethical AI Decision Making, the potential growth and exciting possibilities in the AI industry today, empowering businesses worldwide and enhancing productivity and digital transformation.
He shares some insights of AI impact in terms of automation and processing and the challenges of an AI entrepreneur in this landscape, together with some tips and tricks on how to face them daily.
Next steps:
– Learn more about 3-2-1 Go Check
– Subscribe to the Build It With AI and watch past episodes on-demand
– Learn about the Microsoft for Startups Founders Hub program and start building your AI business today!
Microsoft Tech Community – Latest Blogs –Read More
Zero Touch Enrollment of MDE on iOS/iPadOS devices managed by Intune
Introduction
Microsoft Defender for Endpoint (MDE) is a unified endpoint security platform that helps protect your devices from advanced threats. MDE on iOS/iPadOS devices provides protection against phishing and unsafe network connections. To use MDE on iOS devices, you need to enroll them in Microsoft Intune, a cloud-based service that helps you manage and secure your mobile devices.
This blog post helps you prepare your environment for zero-touch aka silent enrollment of MDE on your Intune managed iOS/iPadOS devices. Zero Touch enrollment is not available for all scenarios, below is a matrix for reference:
In this post, we will discuss the two selected scenarios which support silent onboarding of MDE. This does not include Shared/Kiosk or user-less devices.
Prerequisites
Before you enroll MDE on iOS/iPadOS devices, make sure you have the following:
An Intune enrolled device with a valid user license for MDE. For MAM (Microsoft Application Management) and 3rd party MDM’s there is a separate onboarding process I will discuss in a future blog post.
An iOS/iPadOS version 15 or above.
Tip: You may want to create a Device group for these target devices since the configuration policies below are recommended to be deployed against devices.
Deploy the Defender App
You may choose to deploy the Microsoft Defender App from Intune either via VPP (volume purchasing programs) or the Public App Store. What’s important is to ensure that the App Configuration Policy you will create later targets the same app source (VPP Or Public App Store).
Assign the App to the target User/Device Group for assignment.
Supervised Devices
These are company owned devices enrolled via the Apple Device Enrollment Program (ADE formerly DEP) or using Apple Configurator profiles. When you onboard a Supervised Device into MDE, it does not create a local loopback VPN.
At a high-level, you need an App Configuration Policy and a Device Configuration Policy targeted to these devices.
Step1: App Configuration Policy for Supervised Devices
From the Intune Console create an App Configuration policy of Managed devices type with Microsoft Defender as the target App.
In the Settings page, select Use configuration designer and add issupervised as the key, value type as String, value as {{issupervised}}
Assign the policy to the target Device Group for assignment.
Step2: Device Configuration Profile for Supervised Devices
The next step is to create a Custom Configuration Profile which enables Web Protection without the need for any local loopback VPN.
Download the Configuration file from: https://aka.ms/mdeiosprofilesupervisedzerotouch
Specify a profile name and browse to the location of .mobileconfig file you downloaded from the link above.
Assign the policy to the target Device Group for assignment.
Screenshot of the custom .mobileconfig file highlighting the silent onboarding configuration.
Onboarding Experience
Since this is a silent enrollment of MDE, the end user would only notice the MDE App installed. They do not need to launch the app for any activation. In the GIF below you will notice before the MDE App is installed, I am able to browse a malicious site (https://smartscreentestratings2.net) and after the deployment and silent configuration of MDE the same site is immediately blocked by Defender.
Unsupervised Devices
These devices are primarily BYOD or Corporate owned devices however not enrolled via Apple ADE/Configurator profiles. These devices are enrolled through App or Web-based Device Enrollment scenario.
Please note that Apple User Enrollment does not support MDE Zero-Touch silent enrollment, refer my previous blog post for deployment guidance: Onboarding Intune Managed iOS User Enrollment Devices to Microsoft Defender for Endpoint – Microsoft Community Hub
A VPN is created for Web Protection Feature on Unsupervised devices. This is not a regular VPN and is a local/self-looping VPN that does not take traffic outside the device.
VPN FAQ: Will this conflict with my corporate VPN?
Guidance: Use a Per-App VPN profile to allow your Enterprise Apps access to corporate resources while leaving the Defender Device-Wide VPN to protect the device. Alternatively, if you switch to Microsoft Tunnel as your corporate VPN gateway, the Defender App will suffice both the requirements.
Configuration
For these devices all you need is a Configuration Profile of type VPN.
This is a Custom VPN profile, for instructions refer our learn docs here.
Assign the policy to the target Device Group for assignment.
The key differentiator is the Key-value pair highlighted in the screenshot below which enables Silent onboarding of the Defender VPN profile.
Onboarding
The device onboarding experience is like Supervised device as called out in the GIF above. As an end user one would only notice the MDE App installed. They do not need to launch the app for any activation.
Post enrollment the device reports to the Microsoft Defender Security Portal.
The device name in Defender for Endpoint console is of the format <username_iPhone/iPad model>. You can also use Microsoft Entra device ID to identify the device in the Defender for Endpoint console.
Additionally, you will see an active Alert from the suspicious site browsed by the user on that device.
Things to know.
MAM Conditional App launch requirement for Defender App existence will interfere with the zero-touch experience since it requires the user to launch the app.
New devices leveraging JIT Registration or Setup Assistant with Modern Auth may have an initial delay of around 5 minutes before MDE zero touch silent onboarding. This is the time between the Authenticator app registering the device and triggering MDE onboarding.
Thanks,
Arnab Mitra
Special thanks to Michael and Yuji for their valuable inputs in this blog post.
Microsoft Tech Community – Latest Blogs –Read More
Analyze Videos with Azure Open AI GPT-4V and Data Factory
Azure Open AI’s GPT-4V is revolutionizing how businesses utilize video data. This powerful AI tool, built on Azure’s robust cloud platform, offers scalable video analysis with enterprise-level security. Whether it’s streamlining quality control in manufacturing with precise defect detection, accessing damage of products in transit, detecting a specific image in a video, or summarizing videos, GPT-4V provides a swift and accurate analysis, saving valuable time and resources.
Yet, for those not versed in Python or .Net, tapping into Azure Open AI’s potential can seem daunting. Azure Data Factory (ADF) steps in as a low-code solution to orchestrate Azure Open AI service calls and manage output ingestion. ADF has features that allow for easy configuration, customization and parameterization of prompts and other AOAI inputs as well as data sources. These customizations and parameterization make the pipelines reusable for ingesting from different data sources, such as the storage account that contains the videos for GPT-4V analysis as well as for different prompts and system messages. ADF seamlessly and securely connects with Azure Open AI services and other Azure resources, like Key Vault, Storage Accounts, and databases such as Azure Cosmos DB or Azure SQL. With ADF, data developers can swiftly craft secure, maintainable, and reusable pipelines.
In this blog post, I will cover an ADF solution which loops through a folder of videos and calls a pipeline to create the video retrieval index, ingest the video into the index, call the GPT-4V deployment and store the results in a database.
This solution is ideal for a development/test environment where you can refine the system prompt, user message, and other inputs until you are satisfied with the GPT-4V output. You can then schedule the pipeline for batch processing or change the solution to analyze the video as soon as blob storage event occurs.
Architecture
Land videos in Azure Blob storage with Azure Event Grid, Azure Logic Apps, Azure Functions, other ADF pipelines or other applications.
The ADF pipeline retrieves the Azure AI API endpoints, keys and other configurations from Key Vault.
The blob storage URL for the video file is retrieved.
With Azure Computer Vision, a video retrieval index is created for the file and the video is ingested. Depending on your use case, you could ingest multiple videos to the same index.
Call GPT4-V deployment in Azure Open AI, passing in video URL and the video retrieval index, system message, system prompt and other inputs.
Save the response to Azure Cosmos DB.
If the video processes successfully, move the video to an archive folder.
Resources Used in this Solution
Azure Open AI with a GPT-4V Deployment (Preview)
Check here for available models and regions for deployment
Azure Computer Vision with Image Analysis 4.0 (Preview)
Follow the prerequisites in the above link and note the region availability and supported video formats
Azure Blob Storage and container for your videos
This must be in the same region as your Azure Open AI resource
Azure Blob Storage and container for archiving videos
Azure Cosmos DB Account (NoSQL API), database and container
Security Requirements
The ADF managed identity needs the following access to the following resources:
Key Vault- Key Vault Secrets User role
Cosmos – Contributor
Storage Account that contains videos – Storage Blob Data Reader
Storage Account for archive of videos – Storage Blob Data Contributor
Computer Vision – Cognitive Services Contributor
Store the following Secrets in Azure Key Vault:
Computer Vision Endpoint and Key
A Shared Access Signature Token for the container that has the videos. (This is required for Computer Vision Video Retrieval and Azure OpenAI to access the storage container)
Open AI Endpoint and Key
GPT-4V deployment name. This is really not an input that needs to be secure, but I saved here for ease of use.
ADF Orchestration Pipeline
The ADF orchestration pipeline utilizes parameter inputs and gets secrets from Azure Key Vault, then loops through a Storage Account container, calling another pipeline to ingest the video into a Computer Vision Video Retrieval Index, call GPT-4V, and ingest the results into a Cosmos DB.
Input parameters for pipeline
sys_message – initial instructions to the model about the task GPT-4V is expected to perform
user_prompt – the query to be answered by GPT-4V
storageaccounturl – endpoint for the storage account
storageaccountcontainer – the container that contains the videos
temperature – value between 0 and 2 where 0 is the most accurate and consistent result and 2 is the most creative
top_p – value between 0 and 1 to consider a subset of tokens
Get the secrets from key vault and store them as return variables
Set a variable which contains the name/value pair for temperature. The parameter above for temperature returns “temperature” : 0.5
Set a variable which contains the name/value pair for top_p. The parameter above is not set so it will be blank.
Get the child items (video file name) in the locations specified by the storageaccounturl and storageaccountcontainer values.
For each video, call the pipeline childAnalyzeVideo, passing in the following values for the parameters pipeline parameters:
Video Ingestion/GPT-4V with Pipeline childAnalyzeVideo
The child pipeline will create an index, ingest the video into the index, call GPT-4V to analyze the video, store the results in Cosmos DB, and move the file to the appropriate folder.
Parameters for processing the video file (see previous section, bullet point 6, on parameters and inputs to this pipeline)
Set the indexName variable – the index name must be unique and can only include letters, numbers and hypens
Create an Index Id – this also must be unique
Create the Computer Vision Video Retrieval Index. The next 3 steps for creating the index, ingesting the video, and checking for ingestion completion follow the first 3 steps of this How-To Guide. Here’s the complete Video Retrieval API Reference.
Ingest the video into the index
Call the Computer Vision Video Retrieval API until ingestion is complete or has timed out
If the index has been created and the video successfully ingested …
a. Call GPT-4V with inputs including system message and prompt and store results in Cosmos DB
Copy Data Source properties – REST API Linked Service to GPT-4V Deployment. This article shows a good example of this REST API POST for GPT-4V. Here’s the Chat Completion API Reference.
I also added Additional Columns to the source:
Sink properties is simply the Cosmos DB Container
Set mapping properties including content from GPT-4V return message, prompt_tokens and completion_tokens and additional columns from source
b. Do a Lookup on the Cosmos DB item just added and to get the Damage Probability (See next section on creating results that can easily be queried)
c. If the Damage Probability value is greater than one, set the processedfolder value to “reviewfordamage” otherwise set it to “processed”.
d. Move the video to the folder specified by the processedfolder variable and delete from the source storage location
That’s it! The videos can be analyzed with GPT-4V, without having to worry about environment variables or config files for API Keys and Endpoints! I don’t have to worry about coding in Python and deploying apps to Azure Functions! I could also use this same ADF Pipeline and just change the system message, prompt and storage location to analyze and other videos for each ADF trigger that calls it!
Author comments:
Crafting the system message or user prompt to create data fields
In this solution, I wanted very specific output for analyzing the videos. The videos I have are of vehicles that may or may not have damage. So I composed my system message so GPT-4V would assess the likelihood of any damage, the severity of the damage, the location of the damage as well as the type of vehicle it is viewing in return that information in a specific format. Below is my system message:
Your task is to analyze vehicles for damage. You need to inspect the video closely and describe any damage to the vehicle, such as dents, scratches, broken lights, broken windows, etc. Sometimes duct tape may be used to cover up damage which may be potential damage and should be described as well. You need to pay close attention, especially to distinguish between damage to the vehicles body and glare from the lights in the garage. First provide a summary of the vehicle and the damage or potential damage to the vehicle in the video. Also return a description for what type of vehicle it is in the format of VehicleType[vehicletype] for example VehicleType[Ford F150]. If you can’t identify the exact model type, return what type of vehicle it is such as VehicleType[Sedan] or VehicleType[Truck]. Rank each video on a scale of 1 to 10 where 1 is the probability of no damage and 10 is a high probability of damage. Describe your reasoning for the rank and output your rank in the format of DamageProbability[rank], for example DamageProbability[4]. If there is damage, along with describing what the damage is, provide a short description of the damage in the format of Damage[damages]. For example Damage[dent] or Damage[dent, scratch]. If there is no damage, return Damage[NA]. Also rank the severity of the damage where a scratch or small dent would be Low; multiple scratches, many scratches, larger dents, broken headlights would be Medium; broken windows, very large dents would be High. Provide the severity ranking in the format of Severity[severityranking]. For example Severity[medium]. If there is no damage, return Severity[NA]. Provide a short description of the location of the damage for example, Location[damagelocation]. For example, Location[hood] or Location[front passenger door, hood]. If there is no damage, return the general location of the portion of the vehicle being examined, for example Location[passenger side low].
I can then query the results in the database:
One video per index? Or many videos per index?
In this solution, I create a separate index for each video. You can also create an index and ingest many videos. I created one index per video because I wanted very specific questions about each video and wanted each video analyzed separately. If I had broader questions about all the videos, such as “count how many blue trucks are being transported”, I would have created an index with many video ingestions.
I hope you enjoyed this article! This solution will soon be available in our FTA Github Repo, AI-in-a-Box! Checkout the other Open AI Solutions there that are already there and ready to be deployed into your Azure subscription! Also check out Analytics-in-a-Box for solutions on Data Factory, Synapse and Fabric!
Microsoft Tech Community – Latest Blogs –Read More