Category: Microsoft
Category Archives: Microsoft
Persisting Data Volumes With .NET Aspire
This post is written against the .NET Aspire Preview 2 release, so it may change when the final version is released.
Recently, I’ve been building an app using .NET Aspire which I’m using PostgreSQL as the database and Azure Storage Blobs and Queues in.
.NET Aspire is awesome for this, as you can setup a developer inner loop super simply with the components that ship, and the nice thing about this is that locally PostgreSQL is run in a Docker container and Azure Storage uses the Azurite storage emulator (which also happens to run in a container).
The problem with this is that when you restart your app, you lose all the data in the database and storage emulator, since they are started fresh each time.
Turns out, it’s a pretty easy fix – all that you need to do is mount a volume into the container where it would store it’s data.
Here’s the PostgreSQL example:
IResourceBuilder<PostgresContainerResource> postgresContainerDefinition = builder.AddPostgresContainer();
if (builder.Environment.IsDevelopment())
{
postgresContainerDefinition
// Mount the Postgres data directory into the container so that the database is persisted
.WithVolumeMount(“./data/postgres”, “/var/lib/postgresql/data”, VolumeMountType.Bind);
}
And here’s the Azure Storage example:
IResourceBuilder<AzureStorageResource> storage = builder.AddAzureStorage(“azure-storage”);
if (builder.Environment.IsDevelopment())
{
storage.UseEmulator()
.WithAnnotation(new VolumeMountAnnotation(“./data/azurite”, “/data”, VolumeMountType.Bind));
}
With this I’m mounting the ./data/<service name> folder from within the AppHost project into the respective data paths, but also wrapping them with a builder.Environment.IsDevelopment() check so that it only happens when running locally (since you don’t want to mount volumes in production – we’ll use the Azure services for that).
Note: The Azure Storage emulator doesn’t have a WithVolumeMount method, so we have to use the WithAnnotation method, which is what the WithVolumeMount method wraps anyway. Also, due to this pull request it’s likely there’ll be an easier way come Preview 3, where you provide the ./data/azurite path as part of the UseEmulator method.
Now when I restart my app, the data is persisted, meaning I don’t have to rebuild state each time. Just make sure you put those paths in the .gitignore file so that you don’t accidentally commit them to source control!
Microsoft Tech Community – Latest Blogs –Read More
Windows Server “Ask Microsoft Anything” January 25
This Thursday, January 25 at 9 a.m. Pacific time we’ll be having an Ask Microsoft Anything (AMA) session on Windows Server “v.Next.” Yes, we are hard at work on the next version of Windows Server and our Microsoft program managers, including @Ned Pyle and @Jeff Woolsey among others, will be on the chat to get your feedback and answer your questions.
We’d love to hear from you about:
Your thoughts on the Windows Server features previewed at Ignite
Your feedback on innovations and improvements you’d like to see in future versions of Windows Server
Here is the link to the session, where you can sign up to add it to your calendar. The team is looking forward to chatting with you!
Microsoft Tech Community – Latest Blogs –Read More
January 2024 – Microsoft 365 US Public Sector Roadmap Newsletter
Newsworthy Highlights
Lessons learned from a joint surveillance voluntary assessment for CMMC
Microsoft recently had an opportunity to sit down with Derek Kernus, Director of Cybersecurity Operation at DTS, to discuss their experience with the Joint Surveillance Voluntary Assessment (JSVA).
Microsoft 365 Government Community Call
Join Jay Leask and other members of the Government Community live on LinkedIn!
Where to Start with Microsoft Teams Apps in Gov Clouds
Customers in our Office 365 government clouds, GCC, GCCH, and DoD, are continuing to evolve how they do business in the hybrid workplace. As Microsoft Teams is the primary tool for communication and collaboration, customers are looking to improve productivity by integrating their business processes directly into Microsoft Teams via third-party party (3P) applications or line-of-business (LOB)/homegrown application integrations.
Microsoft 365 Government Adoption Resources
Empowering US public sector organizations to transition to Microsoft 365
What’s New in Microsoft Teams | Microsoft Ignite 2023
Teams Connect shared channels in GCCH & DoD – Work seamlessly and securely with those inside and outside your organization. With Microsoft Teams shared channels, multiple organizations can work together in a shared space – have conversations, schedule a meeting, share, and co-author files, and collaborate on apps, without ever switching tenants.
Release News
Teams
Simplified creation of Teams and Channels – GCC January, GCCH & DoD February
New meeting option and meeting policy “Turn off copying or forwarding of meeting chat” (Premium) – GCC February, GCCH & DoD March
Defender
Unified RBAC for Defender XDR – GCC December, GCCH & DoD Q1 2024
Purview
Updated admin experience for all DLP settings
eDiscovery (Premium) Jobs report – access for eDiscovery Manager
Identify OneDrive site associated with an inactive mailbox for Custodians
Out-of-box Advanced Hunting queries for Data Loss Prevention incidents in Microsoft 365 Defender
References and Information Resources
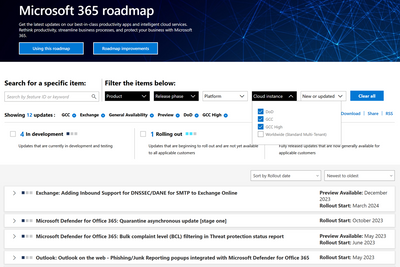
Microsoft 365 Public Roadmap
This link is filtered to show GCC, GCC High and DOD specific items. For more general information uncheck these boxes under “Cloud Instance”.
Stay on top of Microsoft 365 changes
Here are a few ways that you can stay on top of the Office 365 updates in your organization.
Microsoft Tech Community for Public Sector
Your community for discussion surrounding the public sector, local and state governments.
Microsoft 365 for US Government Service Descriptions
· Office 365 Platform (GCC, GCCH, DoD)
· Office 365 U.S. Government GCC High endpoints
· Office 365 U.S. Government DoD endpoints
· Microsoft Purview (GCC, GCCH, DoD)
· Enterprise Mobility & Security (GCC, GCCH, DoD)
· Microsoft Defender for Endpoint (GCC, GCCH, DoD)
· Microsoft Defender for Cloud Apps Security (GCC, GCCH, DoD)
· Microsoft Defender for Identity Security (GCC, GCCH, DoD)
· Azure Information Protection Premium
· Exchange Online (GCC, GCCH, DoD)
· Office 365 Government (GCC, GCCH, DoD)
· Power Automate US Government (GCC, GCCH, DoD)
· Outlook Mobile (GCC, GCCH, DoD)
Be a Learn-it-All
Public Sector Center of Expertise
We bring together thought leadership and research relating to digital transformation and innovation in the public sector. We highlight the stories of public servants around the globe, while fostering a community of decision makers. Join us as we discover and share the learnings and achievements of public sector communities.
Microsoft Teams for US Government Adoption Guide
Message Center Highlights
SharePoint Online / OneDrive for Business
MC698424 — Rename Topic Center site address from SharePoint Admin Center
<30 Days
You can now rename the Topic Center site address from SharePoint Admin Center. You will use the same flow that you do now for changing the site address. You can also use the PowerShell, Start-SPOSiteRename to make the change. Previously, the site address update could only be completed by making a request to Microsoft Support.
When this will happen:
We will begin rolling out early December 2023 and expect to complete by early January 2024.
How this will affect your organization:
There is no end-user impact for this change.
What you need to do to prepare:
You do not need to prepare for this change since the flow for changing the Topic Center site address is the same as changing the site address for any other SharePoint site.
MC698133 — Customize default verticals, add verticals and filters for Microsoft Search
<30 Days
This change is associated with Microsoft 365 Roadmap ID 192834
We’re making changes to Microsoft Search. This update will allow Microsoft Search administrators to customize Microsoft Search experience with the following capabilities: modify default verticals, add vertical and filters with SharePoint content.
The changes can be made for Organization level search applicable to Office.com and SharePoint home as well as site level search on SharePoint sites.
When this will happen:
This feature will begin rolling out gradually beginning late December 2023 and will complete in late January 2024
How this will affect your organization:
This feature does not change the current behavior on the Search page and requires Search administrations to make changes as required. Administrators will be able to modify verticals and add filters in Microsoft search. These new customization capabilities can be accessed in the Search & intelligence admin center under the “Customizations” tab as well as Site administration page.
What you need to do to prepare:
Review the resources below and configure for your organization as appropriate.
Manage search verticals
Manage filters
Create or modify search verticals
MC696169 — Legacy SharePoint Invitation Manager is being retired
30-60 Days
We are completing our retirement of the legacy SharePoint Invitation Manager for guests. This platform is currently used only when Document Libraries are shared externally or when an external user is shared to with a custom role. These flows will now use Entra B2B Invitation Manager instead.
When this will happen:
Targeted Release: We will begin rolling out early December 2023.
Standard Release: We will begin rolling out early January 2024 and conclude by late February 2024.
How this will affect your organization:
We are completing our retirement of the legacy SharePoint Invitation Manager for guests. This platform is current used only when Document Libraries are shared externally or when an external user is shared to with a custom role. These flows will now use Entra B2B Invitation Manager instead. This means that these flows will now also respect any policies or settings in the Entra B2B admin center.
What you need to do to prepare:
You may need to update your documentation for end users. You should also check your Entra B2B settings to ensure they are consistent with policies in the SharePoint Admin Center.
MC684224 — (Updated) Add Individual File Shortcuts in OneDrive Web
<30 Days
Microsoft 365 Roadmap ID 177873
Updated December 15, 2023: We have updated the rollout timeline below. Thank you for your patience.
You can create a shortcut to files stored in other people’s OneDrive’s and document libraries to be able to easily find it within your OneDrive. These file shortcuts can be moved and renamed without impacting the source content and will show up in OneDrive Android, iOS & sync client endpoints.
When this will happen:
We will begin rolling out in early November and expect to complete by mid-January 2024 (previously late December).
How this will affect your organization:
Users will see an Add Shortcut command in the command bar and context menu for a file. This command will be available across all OneDrive file lists (Home, My files, Shared, Favorites, etc.) as well as document libraries. It will also be available for document libraries browsed within SharePoint and Teams.
When a user selects a file and clicks Add Shortcut, they will see two options for where to add a shortcut to: My files and Other locations.
If the user selects My files, a .url file will be created within their My files list in OneDrive. If they select Other locations, a file picker will launch for users to choose a location for their file shortcut within their OneDrive as well as document libraries they have access to.
The default name of the shortcut will be the name of the source file appended with .url. For example, if you create a shortcut to IndividualFileShortcuts.docx, the name of the shortcut will be IndividualFileShortcuts.docx.url and will be differentiated with an arrow icon overlay.
The file shortcut is simply a pointer to a file. When a user renames, moves, deletes or shares a file shortcut, this only impacts the shortcut file and has no impact on the source file. A key implication of this behavior is that, if a user shares a shortcut file or moves a shortcut file to a shared location, it does not automatically grant access to the source file and users would need to share the source file directly to allow access. If the source file is renamed after the file shortcut was created, the file shortcut will not reflect the new source file name.
File shortcuts support the same commands as other .url files in OneDrive and SharePoint that were created through New > Link.
File shortcuts can only be added through OneDrive Web, SharePoint Web and Teams. File shortcuts can be accessed across OneDrive Web, SharePoint Web, OneDrive iOS & Android, OneDrive Sync Client and Teams. There is no meaningful distinction in file shortcut access behavior across endpoint.
What you need to do to prepare:
You may want to notify your users, update your user training, and prepare your help desk.
For your users: Add shortcuts to shared folders in OneDrive for work or school
Users cannot create a file shortcut to non-file content within their OneDrive (e.g., Lists, Whiteboard, PowerBI dashboards, etc.). However, users can create a file shortcut to Loop components within OneDrive.
Users cannot Favorite a file shortcut. Our expectation is that customers will Favorite the source file instead of a shortcut that points to the source file.
When a user shares a file shortcut or moves it to a shared location, it does not share the source file.
Users cannot preview file shortcuts since the shortcut file itself has no information to preview.
MC683663 — (Updated) Access Microsoft Lists, PowerBI, Loop and Whiteboard Content in OneDrive Web
<30 Days
Microsoft 365 Roadmap ID 177877
Updated December 11, 2023: We have updated the rollout timeline below. Thank you for your patience.
You will be able to easily find your Microsoft Lists, Loops, Power BI dashboards and Whiteboard content within OneDrive Web. This content will be available in the Recent, Shared with You and Favorites list within OneDrive.
When this will happen:
Rollout will begin in early November 2023 and expect to be complete by early January 2024 (previously late November).
How this will affect your organization:
Users will see Microsoft Lists, PowerBI, Loop and Whiteboard content appear within their Recent, Shared with You, and Favorites list within OneDrive Web. When opened, this content will open in a new tab. This content will support a limited set of commands compared to other content types.
There is no additional preparation needed for this content to show up. As users open this content in the related apps, it will automatically appear in their Recent list. If this content is shared with them, it will appear in their Shared with You list. Users can Favorite this content from Recent and Shared with You with the same experience as other content types.
Users will see a banner in their OneDrive experience to announce the availability of these content types. This banner will only appear for customers who have these content types present in their Recent or Shared with You list. It will not appear for customers who have no usage of Lists, Loops, Power BI dashboards or Whiteboard.
What you need to do to prepare:
You may want to notify users, update your user training, and prepare your help desk.
Power Platform
MC698439 — New Power Platform endpoint used by Power Apps
30-60 Days
Beginning February 2024, Microsoft Power Apps is introducing a new endpoint for the Power Platform API as a service dependency change in all clouds: *.content.powerplatform.com. The Power Apps end-user experiences will leverage this new endpoint. This change has been reflected in the documentation Power Platform URLs and IP address ranges.
What action do I need to take?
If you employ in-house firewall rules to restrict network traffic to various URLs or IP addresses, you may need to adjust them to allow traffic to flow to endpoints under the following domain *.powerplatform.com.
Why is this action needed?
Depending on your firewall configuration, you may experience service interruptions if this endpoint is not allow-listed. Please review the full, updated list of endpoints.
Microsoft Viva
MC697807 — New experiences for video and images in Viva Engage are coming to you in 2024!
>60 Days
As a Viva Engage customer you will enjoy the new video and image experiences as soon as they reach general availability early in 2024—no action needed.
When this will happen:
We will begin rolling out in mid-January 2024 and expect to complete by early March 2024.
The rollout will start with customers currently enrolled in the public preview of stories before rolling out to all customers.
If you wish to opt-out from this update to the stories public preview, you can do so from your Viva Engage admin settings before January 15th, 2024.
How this will affect your organization:
Customers that joined the stories public preview will be the best to benefit from these experiences.
We learned a lot from our customers, and we hope and expect you’ll love the final experiences. Here’s what you can expect from the update to the preview on or shortly after January 15th; and from the final experience that will be enabled worldwide, starting in March:
End of the story: stories will not be rolled out to general availability. The new video and image experiences are about making it easy to share news, knowledge and perspectives with media, integrated into the way people already work in Viva Engage.
Consumer-grade creation tools: You can still create beautiful content by uploading or recording using your device’s camera, webcam, or screen recording. You can augment your creation with text, ink, stickers and backgrounds; trim and rearrange video clips; these features are available worldwide: Look for the new Record and Upload buttons in the publisher!
One place to view & engage: We heard loud and clear that having two places to view and engage with content—the feed and the separate “carousel”—was creating challenges. Carousels will go away and, instead, your video and images will appear in the Viva Engage feeds and across Outlook, Teams, and Viva Connections—anywhere Viva Engage posts appear! We’re introducing a new way to showcase your videos and images that makes them “pop” in the feed—they’ll look great—and when people dive in to your post, they’ll see the same immersive viewing experience you loved with stories.
One place to create: We heard that two ways to share video & images—stories and posts with attachments—with two sets of rules about what you could share was creating “which tool when?” questions. So now, you’ll share video and images from the publisher just like you share text posts and articles. One place to create, with all the goodness you asked for: no limit to video length, support for announcements, and support for delegates to post. When you share a post on your storyline, and the post has one image or video, we’ll make it look great (see above), but you’ll have the option to show the image or video as an attachment, below the text, if that better suits the goals of your post.
What next:
The option “Generally available” located in the Viva Engage admin settings, following the path > Feature management >Storyline > Enable Stories > Generally available will be removed.
On or shortly after January 15th, stories carousels will be removed and all existing stories will appear integrated into feeds, featuring the new look that highlights the image or video.
If you are opted-in to the preview, your users can take advantage of the experience when they create a new post on their storyline with one image or video, and optional text. That post will appear in feeds with the new look that highlights the shared image or video.
If you are no longer in the preview, your users will not be able to create posts with the new look until the feature reaches general availability, currently targeted at March.
What you need to do to prepare:
Review your current configuration and opt-in, opt-out, or remain in the preview. Between now and January 15th, you can remain in the preview, opt-in, or opt-out. Manage your choice in the Viva Engage admin settings, following the path Feature management > Storyline > Enable stories > Public preview > On/Off. Between January 15th and general availability (currently targeted for March), submit a support ticket via Admin center to opt-in or opt-out.
Learn more about new experiences for video and images in Viva Engage here and stay tuned for more updates.
MC697805 — Expanded reactions in Viva Engage
>60 Days
Microsoft 365 Roadmap ID 178015
Viva Engage reactions help users participate in conversations. Reactions remain one of the most-used engagement features across customer networks. We’re offering a wider set of reactions in the product, like other M365 apps, to help everyone express themselves.
The new set adds 24 new icons to the existing six for a total of 30 reactions in Viva Engage. The current six reactions (like, love, laugh, celebrate, thank, sad) will see new additions, including icons to show laughter, support, checkmark confirmation, excitement, and more.
All expanded reactions support the user’s chosen skin tone for added inclusivity and remain compliant with accessibility standards.
All modern clients, including the browser, mobile, Outlook, SharePoint (incl. Embed), and Teams Engage experiences will be updated to use the new reaction set. Classic Engage (Yammer) experiences will not see the updated icon set, however the new icons are mapped to the old icons to ensure reaction counts remain the same.
Conversation analytics will show the updated reaction set and counts in post roll ups.
When this will happen:
Standard Release: All networks will begin to see the expanded reaction set and new iconography starting in January 2024 and complete by March 2024.
How this will affect your organization:
Users will be able to react with a wider set of icons as soon as the feature is deployed in your network. Reactions content is ingested and available via eDiscovery. There are no changes to any APIs related to reactions with this update.
What you need to do to prepare:
There is no action for admins beyond reviewing any internal help or guidance you have may have created for end users.
MC696569 — (Updated) New designs for post types in Viva Engage
>60 Days
Updated December 13, 2023: We have updated the content below with additional information. Thank you for your patience.
Starting in December 2023, Viva Engage customers will see a refreshed design for question, praise, and poll post types.
The new design for post types in Viva Engage simplifies the user experience, putting more emphasis on content. The streamlined approach will be available in all endpoints—web, SharePoint, mobile apps, interactive Outlook emails, and the Engage apps in Outlook and Teams.
Microsoft 365 Roadmap ID 190366
No functionality or data will be lost because of this change. The new designs are a refreshed user experience to help maintain a modern, content-first look and feel in Viva Engage.
When will this happen
Standard release: We’ll begin to rollout the change in December 2023. All customers are expected to have the new designs by the end of March 2024.
How this will affect your organization
Users will see a different design for polls, praises, and questions in Viva Engage communities and storylines. Only the frontend user experience is affected with this change. Users will continue to have the same capabilities available to create and view content in Viva Engage. There is no action required to adopt the new designs in your network.
Polls:
Praise:
Questions:
What you can do to prepare
There is no action required to adopt the new designs in your network. Admins may want to review any internal help or guidance they may have created for end users.
Microsoft Teams
MC700040 — The new Teams client is available in US Government clouds
>60 Days
The new Teams client will be available to all customers in DoD beginning December 15, 2023. (It is already available in the GCC and GCCH environments.) It will be enabled in stages with admin controls available until all Teams users are updated on March 31, 2024. We recommend updating your organization to the latest version of Teams at your earliest convenience. Tenants who do not choose to update sooner will update to the new Teams client in the following stages:
Admin opt-in: Initially, the new Teams update will only be available when administrators enable it for their users (link below). When the policy is enabled for a user, they may then click the “new Teams” toggle in their Teams client to initiate the update.
“New Teams” toggle shown: Beginning in early January 2024 (starting January 4th for GCC and GCC-H users, starting January 12th for Gallatin users), we will enable the “new Teams” toggle for all users of Teams. If they are still using the classic Teams client, they will not be updated unless they toggle the switch. Admins may choose to disable the new Teams toggle by setting the policy options appropriately.
New Teams becomes the default Client: Beginning February 15th, 2024, the new Teams client will become the default client for all active Teams users in GCC, GCCH, and DOD. All customers will receive the new Teams update, unless disallowed by policy. (Users may still toggle back to the classic Teams client.) Users will be switched once to the new Teams client. Users may choose to switch back to the classic Teams client by using the “new Teams” toggle in the Teams app.
New Teams only: After March 31st, 2024, all remaining users will be updated to the new Teams client. The policy settings in Admin Center and “new Teams” toggle switch in the Teams app will no longer be available at this time. (For more information on this update, see: Classic Teams users to be automatically updated to new Teams – Microsoft Teams | Microsoft Learn)
When this will happen:
We will begin rolling out early December 2023 and will reach all users by late March 2024, as detailed above.
How this will affect your organization:
Until March 31, 2024, administrators control the rollout of the new Teams update within their tenant. We recommend that tenants plan to update their users to the new Teams client soon to ensure that they receive all the latest features and capabilities as well as enhancements to existing features going forward.
What you need to do to prepare:
Administrators can develop their plan for updating their tenants and control the rollout of updates using policy, as documented here:
Upgrade to the new Teams client using policies – Microsoft Teams | Microsoft Learn
Bulk deploy the new Microsoft Teams desktop client – Microsoft Teams | Microsoft Learn
MC699716 — Breaking Security Change: Ability to chat with bots based on custom app policy
<30 Days
On January 31st, 2024, the ability to chat with bots that are not connected to a Microsoft Teams app (e.g. Azure and PVA bots that are not published as an app) will be blocked for users who are not assigned to an app setup policy which allows uploading custom apps.
When this will happen:
January 31, 2024
How this affects your organization:
Users who rely on these bots in their day-to-day work will be impacted if the bot is not connected to a published Microsoft Teams app in the org.
What you need to do to prepare:
For tenants who rely on such bots to perform their day-to-day work, the following options need to be considered:
Turn on the “Upload custom apps” setting in app setup policies for users who rely on such bots. The ability to interact with a bot that is not published as a Microsoft Teams app is generally meant for developers testing the bots before full distribution as a Teams app.
Incorporate bots into Microsoft Teams apps and publish them in your org to allow users without the permission to upload custom apps to access them. The process for doing this varies on the type of bot being developed.
Azure bots created through the Bot Framework
Power Virtual Agents bots
MC699715 — Audio and video flyout and settings in Teams meetings
<30 Days
Microsoft 365 Roadmap ID 187098
Audio and Video flyouts in Teams enable users to efficiently manage their audio and video settings during meetings. These features are easily accessible, allowing users to control their devices and adjust key audio and video features quickly and effortlessly, without needing to navigate through multiple layers of settings.
Users can access this feature in 3 ways:
During a meeting, you can access the audio flyout and video flyout by clicking the split button with a downward arrow right next to ‘camera’ and ‘microphone’ in the meeting toolbar.
From both the audio and video flyouts, you can access audio settings and video settings, which open as panels on the right side of the calling window. You can access these settings by clicking ‘more video options’ and ‘more audio options’ at the bottom of the flyout to open the side panel.
Users can also access ‘audio settings’ and ‘video effects and settings’ by clicking the ‘more’ menu in the meeting toolbar:
Audio settings: “More” menu > Audio settings
Video effects and settings: “More” menu > “Video effects and settings”
When this will happen:
Targeted Release: We will begin rolling out early January 2024 and expect to complete by mid-January 2024.
Standard Release: We will begin rolling out mid-January 2024 and expect to complete by late January 2024.
How this will affect your organization:
The AV framework is designed for quick access and discovery of Teams’ audio and video features, helping users manage their devices and meeting environment more effortlessly.
In this update, we’re focusing our efforts on 2 key areas: flyouts and panels for audio and video:
Flyout: A compact pop-over from the meeting toolbar menu, allowing to quickly confirm the state of key settings before turning on camera and microphone.
Panel: A side panel that opens from the right side of your meeting window and serves as the central hub for all audio and video features.
Video Flyout:
Audio Flyout:
What you need to do to prepare:
You may consider updating your internal documentation to inform users that the feature is now available for Teams users.
MC699711 — Upcoming Group Policy Assignment Service Upgrades
<30 Days
Microsoft will be performing an upgrade to the group policy assignment engine to expand performance improvements to all policy types. The upgrade will offer improvements to policy propagation for groups, group policy assignments to take effect for resource accounts and remove the limitation on the maximum number of groups per policy, which was previously capped at 64. During this upgrade, we will also update the group policy assignments based on the latest group memberships.
You are receiving this message because our report indicates that your organization has one or more group policy assignments for the policy types in scope of this upgrade. As part of this upgrade, Microsoft will be refreshing the group membership and assignment data to ensure the latest intended assignments are reflected as administered. With this update, in rare cases, some users may experience a change in policy inheritance if it was not propagated correctly previously.
When this will happen:
Microsoft estimates that this upgrade will begin starting January 22, 2024. The upgrade will happen in phases, and additional communications will be sent out once an exact date window has been planned for your organization.
How this will affect your organization:
As part of this upgrade:
The current limit of 64 groups per policy will be removed.
Group policy assignments will take effect for resource accounts as inherited from group membership, following the precedence rules.
During the upgrade, we will update the group policy assignments based on the latest group memberships. With this refresh, some users may experience a change in Teams behavior administered by group assignment if it was not propagated correctly previously.
Following policy types are in scope of the upgrade (all other types are on the upgraded engine):
CallingLineIdentity
TeamsAppSetupPolicy
TeamsAudioConferencingPolicy
TeamsCallingPolicy
TeamsCallParkPolicy
TeamsChannelsPolicy
TeamsComplianceRecordingPolicy
TeamsMeetingBroadcastPolicy
TeamsMeetingPolicy
TeamsMessagingPolicy
TeamsShiftsPolicy
TeamsUpdateManagementPolicy
TeamsVerticalPackagePolicy
TenantDialPlan
What will not change:
During the upgrade, admins can continue to take any group policy actions such as create or update group assignments, add or remove user to a group and any policy changes by group assignment inheritance will propagate appropriately.
What you can do to prepare:
Review how the policy assignment for groups work.
Review how policy takes effect for users due to precedence rules.
What you can do to monitor & validate after upgrade:
Monitor the above listed policy areas for any behavior change reported by users and verify alignment to the administered policy assignments.
For assignments with groups larger than 50,000 users, perform a spot check on few users to validate that group assignments are reflected as intended:
via Teams Admin Center by accessing Manage Users >> Policies tab for users
via Teams PowerShell Module and retrieve effective policy for a user with Get-CsUserPolicyAssignment cmdlet
MC698134 — New Meeting Option and Meeting Policy “Turn off copying or forwarding of meeting chat”
<30 Days
Microsoft 365 Roadmap ID 186675
“Turn off copying or forwarding of meeting chat” is a new meeting option that gives the meeting organizer the option to disable copying and sharing features on meeting chat messages for participants to reduce the risk of data leak. Once this restriction is enabled, meeting chat participants will not be able to copy chat messages using menu options or keyboard shortcuts, or forward or share messages to Outlook. There is also a new Meeting Policy setting in Teams admin center for admin to control whether users can see or use this feature in the Meeting Options page. Admins can also set the default value for this meeting option in Meeting Templates that they create. This meeting capability can also be configured within a sensitivity label policy: Configure Teams meetings with protection for highly sensitive data.
When this will happen:
Preview: We will begin rolling out mid-December 2023 and expect to complete within a few days.
Targeted Release: We will begin rolling out mid-January 2024 and expect to complete within a few days.
Standard Release: We will begin rolling out late January 2024 and expect to complete by late January 2024.
How this will affect your organization:
For users who have a Teams Premium license, “Turn off copying or forwarding meeting chat” will show in the Meeting Options page for the meetings they organize. If the organizer turns on the setting or if the meeting is using a sensitivity label or a custom meeting template that turns on this setting, participants will be restricted from copying chat content from the meeting chat.
If an admin does not want certain users to be able to see this option, the admin can go to Teams Admin Center > Meeting Policies and create a policy that disables the feature for these users. Then, these users will not be seeing this setting in the Meeting Options page. However, if the users apply a sensitivity label that enforces copy prevention, it will still take effect even if the policy disables it.
What you need to do to prepare:
The Meeting Policy to allow organizers to restrict participants from copying or forwarding meeting chat messages is by default in Teams Admin Center. That means the “Turn off copying or forwarding of meeting chat” Meeting Option will automatically be available to users with a Teams Premium license.
Create/Update any custom meeting template that should have this setting as a meeting option. From Team’s Admin Center, admins can control if meeting organizers will have access to control this setting in Meeting Options page for a meeting template. That means “Turn off copying or forwarding of meeting chat” in meeting templates can be hidden or visible to meeting organizers depending on how tenant admin sets it. They can also give control to meeting organizers to override the setting.
The tenant administrator may want to provide end user education in advance for this feature in case end users don’t understand why they cannot copy/paste in certain meeting chats.
MC698129 — Control your activity notifications from the activity card
30-60 Days
Microsoft 365 Roadmap ID 186571
Users will be able to control what shows in their activity feed by clicking on the ellipsis from the activity card, helping them to stay on top of the information that matters most to them.
When this will happen:
Targeted Release: We will begin rolling out by mid-January 2024 and expect to complete by late January 2024.
Standard Release: We will begin rolling out early February 2024 and expect to complete by mid-February 2024.
How this will affect your organization:
The experience will be available to all the new Teams users by default.
What you need to do to prepare:
You may consider updating your training and documentation as appropriate.
MC698125 — Agenda View Refresh in Teams Mobile
30-60 Days
Microsoft 365 Roadmap ID 98328
Teams calendar on mobile devices displays the live status of a meeting with avatars of the participants who are in the call, whether the meeting is being recorded and the duration of the meeting.
When this will happen:
Standard Release: We will begin rolling out late January 2024 and expect to complete by mid-February 2024.
How this will affect your organization:
With this update users will now have visibility to additional meeting information within the calendar:
Live status of the meetings
Participant avatars in the call
Recording status
Meeting duration
What you need to do to prepare:
You may consider updating your training and documentation as appropriate.
MC697808 — Promote channel creation
<30 Days
Microsoft 365 Roadmap ID 163363
Today, our experience focusses on letting users create team at the top level, with channel creation as a per team level option. Looking at the user behavior here, users end up creating more teams, where it could have been channels within teams, leading to team proliferation and difficulty in managing teams. To address this, we are looking to promote channel creation.
For users to collaborate effectively, they need to set-up the right collaboration space. Channels being the main hub of collaboration, we made it easier for users to create channels. With the channel creation option elevated to the top, users can now create the appropriate collab space by picking between team or channel. They will be able to host the channel into a team of their choosing.
When this will happen:
Targeted Release: We will begin rolling out early January 2024 and expect to complete by mid-January 2024.
Standard Release: We will begin rolling out mid-January and expect to complete by late January 2024.
How this will affect your organization:
End-users will now be able to go to + button in the teams and channels list to create a channel, which they can host in a channel of their choice.
What you need to do to prepare:
Ask users to pick the right team they want to host channels in, while creating channels from + button.
MC697434 — Simplified team creation
>60 Days
Microsoft 365 Roadmap ID 163364
Today, users go through multiple steps, selecting between options while creating teams. However, most users are inclined towards setting up their team from scratch and as private. Hence, we defaulted to a simpler experience, yet giving users the rich options of creating a team from a template or group and selecting privacy/sensitivity of the team. It is a simple by default, power on demand experience.
When this will happen:
Targeted Release: We will begin rolling out early January 2024 and expect to complete by mid-January 2024.
Standard Release: We will begin rolling out mid-January 2024 and expect to complete by late January 2024.
GCC High and DoD: We will begin rolling out late February 2024 and expect to complete by late March 2024.
How this will affect your organization:
Users will be able to create teams quickly from the + button.
What you need to do to prepare:
Users will need to go on a secondary level from the ‘create team from scratch’ dialog to create teams from templates or groups.
MC697433 — Affected Teams behavior in Chrome due to privacy sandboxing
>60 Days
Starting in January, Chrome will begin gradually rolling out privacy sandboxing in the web to 1% of their users, with general rollout happening in late 2024. This will impact some Teams experiences in Chrome. The recommendation is to use the Teams desktop client if you are part of the rollout cohort.
When this will happen:
Starting in January 2024 and continuing through the remainder of 2024.
How this will affect your organization:
Teams users who are using Google Chrome with this recent change will start seeing the following experiences:
The new Teams web app will display a banner and require users to click it every 24 hours to remain signed in. This will impact users in your organization who can’t use the Teams desktop app.
The new Teams web app may include embedded experiences, such as apps, that no longer work. When this happens, Teams will give users the option of opening the embedded experience in a separate browser tab, or using the Teams desktop app.
Classic Teams will show options to switch to the new Teams web app, and/or to use the desktop app.
Other affected experiences include Teams chat in Outlook web app and Dynamics 365. The ‘Share to Teams’ dialog found in Outlook and other web apps or sites is also affected.
What you need to do to prepare:
We are providing this information for your awareness. If your organization accesses Teams in the Chrome browser, some of your users may start being affected by this change. The recommendation is to use to the Teams desktop client.
Enterprise administrators can also use the BlockThirdPartyCookies and CookiesAllowedForUrls policies to ensure their users are not impacted, allowing them time to make necessary changes to not rely on this policy or third-party cookies.
MC696170 — (Updated) Intelligent Meeting Recap for scheduled channel meetings (Premium)
>60 Days
Microsoft 365 Roadmap ID 186429
Updated December 15, 2023: We have updated the rollout timeline below. Thank you for your patience.
Intelligent Meeting Recap is now available for scheduled channel meetings, and channel meeting users can now browse the recording by speakers and topics, as well as access AI-generated meeting notes, action Items, and @mentions for scheduled meetings.
When this will happen:
Targeted Release: We will begin rolling out mid-February 2024 and expect to complete by late February 2024.
Standard Release: We will begin rolling out late February 2024 and expect to complete by early March 2024.
How this will affect your organization:
Users with Teams Premium can now get Intelligent Recap for scheduled channel meetings. Please note that Intelligent Recap for Meet now meetings in channel will be available in a future release.
How to use Intelligent Recap:
In order to generate Recap after the meetings, users need to turn on recording & transcription during scheduled channel meeting.
After the meeting ends, users can tap the recording chiclet, the transcript chiclet, or the view recap button in the meeting chat or channel meeting post to launch Recap. More details on how Recap works can be found in this public doc.
What you need to do to prepare:
To prepare, update your training and documentation as appropriate.
MC695724 — Announcing general availability of the new Microsoft Teams app for virtual desktop infrastructure.
Rolled Out
Today, we’re announcing the general availability of the new Microsoft Teams app for Windows in virtual desktop infrastructure (VDI) environments.
When this will happen
New Teams is generally available our virtual desktop infrastructure (VDI) customers now.
How this will benefit your organization
Today, we’re excited to announce the general availability of new Teams for our Virtual Desktop Infrastructure (VDI) customers. New Teams now has full feature parity for almost all features in the classic Teams for VDI.
We announced the general availability of the new Teams desktop app for Windows and Mac on October 5, 2023. On the same date, we also announced the public preview of the new Teams app for Virtual Desktop Infrastructure (VDI). Read the message center post MC678853 for details of our public preview announcement.
How this will affect your organization:
The classic Teams in VDI will reach end of support on June 30th, 2024, after which users will not be able to use the classic Teams and will be asked to switch to new Teams app. Therefore, we recommend you update to new Teams today.
Our Citrix customers must add an additional registry key to the VDAs, see here for more information and the minimum versions needed.
Customers who use Azure Virtual Desktops, Windows 365, or VMware can keep the WebRTC Redirector Service and Horizon Agent as they are, as long as they meet the minimum version requirements listed here.
Administrators who have the ‘Use new Teams client’ setting in the Teams update policy set to ‘Not enabled’, please act and choose the correct value for this policy as explained here. For a better experience, we suggest choosing ‘New Teams as default’ or ‘Microsoft controlled’.
Classic Teams users in persistent VDI environments (with the per-user install) will be automatically updated to new Teams in the coming months. For non-persistent VDI environments, IT Admins would still have to update the golden or master image with the new Teams client, and either can have it run together with classic Teams so users can switch between them or fully uninstall classic Teams (known as rip and replace).
To learn more about how you can deploy new Teams in your organization, visit the new Teams VDI page.
MC695502 — (Updated) IntelliFrame experiences on new Teams app and Recognition expansion
<30 Days
Microsoft 365 Roadmap ID 161427
Updated December 15, 2023: We have updated the rollout timeline below. Thank you for your patience.
This is a two-part update, with:
IntelliFrame experiences availability on new Teams app for Desktop,
Expanding recognition support to cover scenarios such as meeting invite forwarding and Teams meeting nudge among others (Please See below for details)
IntelliFrame experiences from Edge cameras like Yealink Smartvision 60 are currently available on Teams Desktop platform. With this update, we want to announce the availability of IntelliFrame on New Teams app.
Recognition expansion: This update applies to both existing and new Teams desktop app. Previously recognition was only supported when an organizer invited the meeting room with Intelligent camera connected. With this update, we are able to support the following scenarios.
Meeting forward (both one time and recurring meetings)
Teams nudge (using Roster>add participant)
Join by meeting ID (Using MTR to join a meeting by ID)
Also, under “Recognition” feature, we heard our users and renamed unrecognized users from “Guest” to “Participant”. Moving forward, with this update anyone who is unrecognized will see their name label as “Participant.”
When this will happen:
Targeted Release: We will begin rolling out early January 2024 and expect to complete by mid-January 2024.
Standard Release: We will begin rolling out mid-January 2024 and expect to complete by late January 2024.
How this will affect your organization:
IntelliFrame support on new Teams app, so users switching to new Teams app will be able to experience IntelliFrame from the MTR connected Intelligent cameras.
With additional recognition scenarios, users will be able to see their name labels generated across majority of meeting scenarios, with exceptions like multi-tenant meetings which are not supported yet.
What you need to do to prepare:
You may consider updating your training and documentation as appropriate.
MC690921 — (Updated) Microsoft Teams Voice isolation
>60 Days
Microsoft 365 Roadmap ID 125387
Updated December 11, 2023: We have updated the rollout timeline below. Thank you for your patience.
With “Voice isolation”, you can enjoy clear and uninterrupted calls or meetings, no matter where you are. This feature uses AI to filter out all background noise, including other people’s voices. By leveraging your voice profile, this advance noise suppression capability ensures only the user’s voice is transmitted. Whether you are in a busy office, a noisy cafe, or a crowded airport, you can communicate with confidence and clarity. “Voice isolation” is powered by our advanced deep learning, speech services, and audio processing technology, and it shows our dedication to solving user problems with AI and enhancing audio quality and experience.
When this will happen:
Targeted Release: We will begin rolling out early February 2024 (previously mid-January) and expect to complete by mid-February 2024.
Standard Release (if applicable): We will begin rolling out late February 2024 (previously mid-February) and expect to complete by early March 2024 (previously late February).
How this will affect your organization:
The Voice isolation feature will be enabled by default for your organization. End-users will need to enroll their voice profile via the Recognition tab under the Teams Global Device settings to enable the Voice isolation feature to have better audio input quality.
If you want to disable this feature for your organization, you will need to do so via PowerShell: Set-CsTeamsMeetingPolicy
What you need to do to prepare:
You should consider communicating this with your users and update training and documentation as appropriate.
MC689496 — (Updated) Microsoft Teams: Meeting chat invitations from unmanaged users
<30 Days
Updated December 13, 2023: We have updated the rollout timeline below. Thank you for your patience.
When using external access for Teams, users receiving a meeting chat invitation from an unmanaged Teams user will be prompted with the option to acknowledge or leave the meeting chat.
When this will happen:
Standard Release: We will begin rolling out early December 2023 and expect to complete by late January 2024 (previously late December).
How this will affect your organization:
There are no admin controls related to this feature. Users will see an invitation screen when added to a meeting chat by an external unmanaged Teams user. At this point, they can choose to acknowledge the invitation or leave the meeting chat. Users continue to have the option to block and unblock external unmanaged Teams users.
Users will not see this update if external access with unmanaged Teams users is disabled or if incoming chats from unmanaged Teams users are disabled.
Review this doc to understand external access settings with unmanaged Teams users.
What you need to do to prepare:
If external access with unmanaged Teams users is enabled, consider notifying your users of this update.
MC688109 — (Updated) Co-organizer experience updates in Teams Webinars and Townhalls
30-60 Days
Microsoft 365 Roadmap ID 168524
Updated December 11, 2023: We have updated the rollout timeline below. Thank you for your patience.
Scheduling, setting up, and managing an event is not a simple task. Which is why we allow co-organizer to be added to the event so they can work alongside or on behalf of the organizer. So far co-organizers were able to set up event theming, manage registration, meeting options, view reports and more but were not able to edit event details like title, date/time, description, event group; nor publish or cancel event. Now they can! Co-organizer can edit event details, publish, and cancel the event like the organizer can. So once the co-organizer is added they will have full parity of experience as organizer and control/manage/edit event.
When this will happen:
Targeted release: We will begin rolling out early February 2024 (previously mid-January) and expect to complete by mid-February 2024 (previously late January).
Standard release: We will begin rolling out early February 2024 and expect to complete by late February 2024.
How this will affect your organization:
When co-organizer opens the event scheduling page, they should have the ability to edit the details page, publish, and cancel the event.
What you need to do to prepare:
Nothing required to prepare.
MC687791 — (Updated) Custom Backgrounds for Announcement Posts in Channels
<30 Days
Microsoft 365 Roadmap ID 183785
Updated December 13, 2023: We have updated the rollout timeline below. Thank you for your patience.
Microsoft Teams users will soon be able to create custom backgrounds for their Announcement posts with the generative AI power of Microsoft Designer. As part of the advanced Teams Premium capabilities, users will have access to DALL-E, a text to image generator, which they can use for their backgrounds. This release of Custom Backgrounds for Announcement Posts will be rolling out across Microsoft Teams Desktop and Web for Channels 2.0 in English – US markets only. In line with current announcement behavior, Mobile will only support the consumption of custom backgrounds. Feature is disabled for EDU tenants while the team implements a policy setting.
Note: Non-US tenants may notice a temporary loss in the ability to upload an image. For tenants who do not have access to Designer, the ability to upload image will be made available again in early 2024, while the team works on Designer support for more languages.
When this will happen:
Targeted Release: We will begin rolling out early November and expect to complete by mid-November 2023.
Standard Release: We will begin rolling out late November and expect to complete by mid-January 2024 (previously early December).
How this will affect your organization:
Before, in Channels 1.0, users struggled to “find the right picture,” to “find images that work correctly with banner sizing so it takes ages,” etc.
Now, whether users have their own image or an idea in mind, or absolutely nothing at all, they can create rich, engaging backgrounds for their announcement posts through the generative AI power of Microsoft Designer. A few clicks is all it takes–let the imagination run wild!
You can find the entry point icon to the Designer integration at the bottom right corner of the announcement.
The Designer Mini Dialog is where all the magic happens. You can write a description, upload an image, generate an image using DALL-E, or click one of the examples we have provided for you to start.
When you click on “Generate image,” you’ll be able to create an image from a text description to include in your announcement background.
Once you have selected a background you like, you’ll see the option to press “Customize” or “Done.” “Done” inserts the background into your Announcement while “Customize” launches the Microsoft Designer App where you can further customize your background.
The Designer App provides flexibility and endless power for you to create exactly what you want.
What you need to do to prepare:
You may want to notify your users about this new capability to better express themselves and engage their audience in their Announcements. Additionally, due to the inevitable generative AI learning curve, you may want to provide additional training/documentation as you see fit. You can also lead by example and show your users what’s possible.
While we work on making a policy setting available to tenants, this feature will be enabled by default (except in EDU). If there are concerns, please contact support.
We can’t wait to see what announcement backgrounds you and your team come up with.
MC687207 — (Updated) Microsoft Teams: Files App Updating to OneDrive App Experience in Teams
<30 Days
Microsoft 365 Roadmap ID 145798
Updated December 22, 2023: We have updated the rollout timeline below. Thank you for your patience.
The Files app accessed from the left side of the Teams desktop client will be updated with the new OneDrive app experience, bringing performance improvements, more views, and the latest features of OneDrive to both classic and new Teams. All existing features of the Files app will also be available via this new OneDrive app experience. For more details, please visit the blog page.
As part of this change, Files app on left side of the new Teams desktop client will also become OneDrive app. There is no change in the name of Files app in either classic Teams desktop client or Teams mobile client.
When this will happen:
Targeted Release: We will begin rolling out in mid-November 2023 and expect to complete rollout by late November 2023.
Standard Release: We will begin rolling out in late November 2023 and expect to complete rollout by late January 2024 (previously mid-December).
How this will affect your organization:
Additionally, for Teams desktop users, a one-time indication will be shown for awareness when Files app is updated to OneDrive app.
What you need to do to prepare:
There is no action required since any existing policies or settings done through Teams Admin Center for Files app will automatically be applicable.
MC686919 — (Updated) Simplified Compose Experience for Teams
>60 Days
Microsoft 365 Roadmap ID 123486
Updated December 13, 2023: We have updated the content below for clarification. Thank you for your patience.
Teams Compose is the heart of collaboration, where all Teams messages flow each month. It’s also the gateway to a wealth of features, from Copilot to Files, Loops, Video, and Platform Apps.
While Teams’ capabilities have grown by leaps and bounds, the compose experience has remained largely unchanged. This update addresses usability, scalability, and information density challenges. We’ve simplified the compose experience, enhancing usability for various rich authoring scenarios, establishing scalable patterns for all compose actions, and optimizing it for your everyday needs. Get ready to enjoy a more seamless and efficient collaboration experience! This is for the new Teams experience only.
When this will happen:
Targeted Release: We will begin rolling out early-December 2023 and expect to complete by mid-December 2023.
Standard Release: We will begin rolling out mid-February 2024 and expect to complete by early March 2024.
GCC: We will begin rolling out mid-March 2024 and expect to complete by late March 2024.
GCCH: We will begin rolling out early April 2024 and expect to complete by mid-April 2024.
DoD: We will begin rolling out mid-April 2023 and expect to complete by late April 2024.
How this will affect your organization:
All Teams users will still be able to do everything they have previously done in Teams, but now, accessing these features will be easier and clearer.
What you need to do to prepare:
No changes are required to prepare for this change.
MC686281 — (Updated) New Gallery in Teams Meetings
>60 Days
Microsoft 365 Roadmap ID 118467
Updated December 18, 2023: We have updated the content below with additional information.
We are introducing a revamped version of the gallery in Teams meetings and calls. The new gallery will be the default view when users join their meetings, so that they can use it without the need of taking an action.
When this will happen:
Targeted Release: We will begin rolling out late January 2024 (previously early January) and expect to complete by early February 2024 (previously mid-January).
Production and GCC: We will begin rolling out mid-February 2024 (previously mid-January) and expect to complete by late February 2024 (previously late January).
GCC High: We will begin rolling late February 2024 (previously late January) and expect to complete by early March 2024 (previously early February).
DoD: We will begin rolling out late February 2024 (previously late January) and expect to complete by early March 2024 (previously early February).
How this will affect your organization:
This new version introduces a series of changes to help users in their meetings:
16:9 aspect ratio participant tiles for more predictability. A consistent aspect ratio maintains a more predictable experience when users turn their videos on or off. It also provides more visibility into users’ body language and hand gestures.
An audio-video mixed gallery for a more inclusive representation. Audio and video users share now the same space by default.
Meeting rooms are displayed larger than individual participants. In certain meeting sizes, we display Microsoft Teams Rooms video in a larger size than the rest of the participants to give an equivalent weight to participants joining from a meeting room. Non-Teams rooms joining Teams meeting via Direct Guest Join will remain the same tile size as today.
You appear next to the rest of the participants. Your own tile will now be included next to the rest of the participants.
Customization of the gallery. Users can adapt the gallery to their needs or preferences. The customization options include:
Gallery size: Users can choose the maximum number of tiles that will be represented per page. The entry point for this action is available through the meeting toolbar: “View” > “Change gallery size”.
Placement of your own tile: For users who prefer to keep themselves separated from the rest of the participants. If chosen, the self-tile will be placed in an area separate from the rest of the participants. The entry point for this action is available through the meeting toolbar: “View” > “More options” > “Remove me from gallery”.
Prioritizing videos: For users who want to give a higher weight to participants with their video on. If chosen, video participants will be displayed more prominently than audio participants. The entry point for this action is available through the meeting toolbar: “View” > “Prioritize video”.
Meeting room tile size: Users can decide if they want to resize the meeting room tile to the same size as the rest of the participants. The entry point for this action is available in the contextual menu of the room tile.
What you need to do to prepare:
Please notify your users about this change and update any training documentation, as appropriate.
MC686279 — (Updated) Stream App in Microsoft Teams will be updated to Stream (on SharePoint)
Rolled Out
Updated December 11, 2023: We have updated the rollout timeline below. Thank you for your patience.
We are transitioning the Stream experience in the desktop client of Microsoft Teams from Stream (Classic) to Stream (on SharePoint). Once transitioned the Stream app in Microsoft Teams will display only Stream (on SharePoint) content–it will no longer display Stream (Classic) content. The new Stream (on SharePoint) app in Teams will feature similar content and features as found on the Stream start page.
The Stream app is currently accessible across multiple touchpoints on Teams, including the Stream app on Teams left rail, Stream on Teams message extension, and the Stream Tab on Chats/Channels. You can find the app by tapping the three dots on the Teams left rail and then search for Stream. As a first step, Stream app on Teams left rail will be updated to Stream (on Sharepoint). This updated version of Stream app will allow users to access the Stream start page within Teams, and quickly find and watch videos without switching apps. Users will have the option to pin the Stream app on the side panel for more convenient access in the future.
In the coming months, we will also transition the Stream app for Teams web and Teams mobile.
When this will happen:
Standard Release: We will begin rolling out early November 2023 and expect to complete by mid-December 2023 (previously mid-November).
How this will affect your organization:
All users will see the Stream Start page when they access Stream App from Teams desktop client after this updated version is rolled out.
What you need to do to prepare:
There is no action needed to prepare for this change. You may want to notify your users about this change and update any relevant documentation as appropriate.
MC683927 — (Updated) Microsoft Teams: Remote Setting for QR code on Teams Panels
<30 Days
Updated December 13, 2023: We have updated the content below with additional information. Thank you for your patience.
With this update, admins can remotely turn the Teams Panel QR code setting on/off through Teams Admin Center. On the device, this setting is called ‘Allow room reservations by QR code’, and it controls whether there is a QR code shown in the top left of the home screen. In Teams Admin Center, it will be called ‘People can scan a QR code to reserve a room.’
When this will happen:
Roll out is expected to begin in early December 2023 and complete by early January 2024 (previously early December).
What you need to do to prepare:
In order to use this feature, make sure Teams Panels is updated to 1449/1.0.97.2023111003. For more information, please see What’s new in Microsoft Teams devices – Microsoft Support.
MC683923 — (Updated) Nightly Reboot Window for Microsoft Teams Rooms on Android
Rolled Out
Updated December 11, 2023: Nightly reboot window setting will be unavailable for Neat based Microsoft Teams Rooms on Android devices. We will be rolling out support for Neat devices shortly.
With the Microsoft Teams Rooms on Android update U2B, a nightly reboot maintenance window feature is being introduced.
By default, devices taking update will have a daily reboot window from 1AM-3AM in their time zone. The reboot only occurs if the device isn’t being used and if the device fails to reboot in the window, the reboot will occur the during the following window. Customers will also have the option to turn off the reboot window or change the timing for the reboot window.
By introducing nightly reboots, Microsoft Teams Rooms on Android devices will benefit from improved reliability and recovery from some potential issues like memory leaks, pairing loss and network connectivity problems.
When this will happen:
Preview: We will begin rolling out late November 2023 (previously late October)
Standard Release: We will begin rolling out mid-December 2023 (previously mid-November) and expect to complete by late December 2023 (previously late November)
How this will affect your organization:
Devices running Microsoft Teams Rooms on Android will automatically reboot each night unless the maintenance window is turned off by the admin.
MC683659 — (Updated) Microsoft Teams: Additional manager-controlled privacy settings in Shifts
<30 Days
Microsoft 365 Roadmap ID 152119
Updated December 11, 2023: We have updated the rollout timeline below. Thank you for your patience.
We are thrilled to announce exciting product enhancements on frontline managers-controlled privacy settings for frontline workers.
When this will happen:
We will roll out in November 2023 and complete by mid-January 2024.
How this will affect your organization:
Frontline managers now have the power to manage shift information visibility for their employees through the newly available privacy controls in Shifts settings.
Here’s what this feature includes:
Limited Past Views: Managers can restrict how far back frontline workers can view their co-workers’ schedules, ensuring historical data privacy.
Generic Time Off View: Frontline workers can see their co-workers’ time off in a generic way, without viewing the specific reasons and notes.
Limited Shift Details: Managers can limit the level of detail frontline workers can access about their co-workers’ schedules, excluding sensitive information like Shift notes, activities and break durations.
What you need to do to prepare:
There is nothing you need to do to prepare for these changes, besides you may want to notify your frontline managers about these updates.
MC680963 — (Updated) Bring-Your-Own-Device IT Admin Experience in Teams Pro Management Portal
30-60 Days
Microsoft 365 Roadmap ID 161728
Updated December 13, 2023: We have updated the rollout timeline below. Thank you for your patience.
BYOD (Bring Your Own Device) rooms are identified as rooms with no MTR (Microsoft Teams Rooms) but equipped with other peripherals such as camera, microphone.
In Teams Pro Management Portal, IT admins will finally have the capability to manage and track these specific BYOD rooms. They will get a comprehensive overview of their BYOD rooms and devices activities. With this new addition, they will gain valuable insights into how these spaces are being utilized and enabling them to make data driven decisions.
When this will happen:
We will begin rolling out in late January 2024 (previously late November) and expect to complete rollout by early February 2024 (previously early December).
How this will affect your organization:
IT admins will gain visibility of the BYOD rooms in the Teams Pro Management Portal upon logging in. To have access the portal, they will need at least one Pro, premium or Teams Shared Device license.
Under the Inventory tab, they will find a comprehensive list of all rooms within their organization, including information about BYOD rooms and devices.
Within the Inventory tab under the device page, IT admins will also have the capability to associate each device to its specific BYOD room. This association will be done in two different methods, with the “Import” function by importing the list of devices and adding the room information, or through auto discovery by selecting the specific room from list of available rooms.
In the Report tab, admins can finally see the BYOD rooms specific utilization metrics. However, an 8$ Teams Shared Device license will need to be assigned per room to have access to the BYOD usage report.
What you need to do to prepare:
To have access to the BYOD in Teams Pro Management Portal, at least one pro/premium or Teams Shared Device license is required on tenant level.
MC680348 — (Updated) Custom Backgrounds for Announcement Posts in Channels
30-60 Days
Microsoft 365 Roadmap ID 123501
Updated December 15, 2023: We have updated the rollout timeline below. Thank you for your patience.
Microsoft Teams users will soon be able to create custom backgrounds for their Announcement posts with the generative AI power of Microsoft Designer. This release of Custom Backgrounds for Announcement Posts will be rolling out across Microsoft Teams Desktop and Web for Channels 2.0 in English – US markets only. In line with current announcement behavior, Mobile will only support the consumption of custom backgrounds. Feature is disabled for EDU tenants while the team implements a policy setting.
When this will happen:
Preview: We will begin rolling out mid-October and expect to complete by late October. – Complete
Targeted Release: We will begin rolling out mid-October and expect to complete by late October. – Complete
Standard Release: We will begin rolling out early November and expect to complete by mid-November. – Complete
GCC/GCC High/DoD: We will begin rolling out in mid-January 2024 and expect to complete by late February 2024.
How this will affect your organization:
Before, in Channels 1.0, users struggled to “find the right picture,” to “find images that work correctly with banner sizing, so it takes ages,” etc.
Now, whether users have their own image or an idea in mind, or absolutely nothing at all, they can create rich, engaging backgrounds for their announcement posts through the generative AI power of Microsoft Designer. A few clicks is all it takes–let the imagination run wild!
You can find the entry point icon to the Designer integration at the bottom right corner of the announcement.
The Designer Mini Dialog is where all the magic happens. You can write a description, upload an image, or click one of the examples we have provided for you to start.
Once you have selected a background you like, you’ll see the option to press “Customize” or “Done.” “Done” inserts the background into your Announcement while “Customize” launches the Microsoft Designer App where you can further customize your background.
The Designer App provides flexibility and endless power for you to create exactly what you want
What you need to do to prepare:
You may want to notify your users about this new capability to better express themselves and engage their audience in their Announcements. Additionally, due to the inevitable generative AI learning curve, you may want to provide additional training/documentation as you see fit. You can also lead by example and show your users what’s possible.
While we work on making a policy setting available to tenants, this feature will be enabled by default (except in EDU). If there are concerns, please contact support.
We can’t wait to see what announcement backgrounds you and your team come up with.
MC679733 — (Updated) Microsoft Teams Rooms on Windows- All-in-one experience
Rolled Out
Microsoft 365 Roadmap ID 170740
Updated December 11, 2023: We have updated the rollout timeline below. Thank you for your patience.
With update 4.19 coming in November, Teams Rooms on Windows will support all-in-one and board device form factors, such as the Surface Hub 3.
When this will happen:
Standard Release: We will begin rolling out early November 2023 and expect to complete by mid-December 2023 (previously late November).
What you need to do to prepare:
There is no action needed to prepare for this change. You may want to notify your users about this change and update any relevant documentation as appropriate.
MC679525 — (Updated) End-to-end encrypted Meetings – 200 participants (Premium)
<30 Days
Updated January 2, 2024: We have updated the rollout timeline below. Thank you for patience.
For meetings that require heightened confidentiality, end-to-end encryption (E2EE) is an extra layer of security that encrypts data at its origin and decrypts it at its destination. Only audio, video, and video-based screen sharing is end-to-end encrypted. Apps, avatars, reactions, chat, and Q&A are not end-to-end encrypted.
We had launched end-to-end encryption (E2EE) for meetings with 50 participants in February 2023. We are increasing the meeting size to 200 participants. We support:
One can schedule an end-to-end encrypted meeting from desktop (Windows and Mac) and mobile (iOS or Android).
To join an end-to-end encrypted meeting
One can join an end-to-end encrypted meeting from desktop (Windows or Mac) or mobile (iOS or Android) or Teams Room Device (Windows or Surface Hub).
For the 200-participant meeting, the first person joining should be from desktop (Windows or Mac) or mobile (iOS or Android).
All other platforms are blocked from joining an end-to-end encrypted meeting.
When this will happen:
Standard Release: We will begin rolling out late October and expect to complete by early November.
GCC Release: We will begin rolling out late October and expect to complete by early November.
GCCH Release: We will begin rolling out early November and expect to complete by early January 2024 (previously mid-December).
DoD Release: We will begin rolling out late November and expect to complete by early January 2024 (previously mid-December).
How this will affect your organization:
With this update, end-to-end encrypted meetings can have a meeting size up to 200 participants instead of 50 participants.
What you need to do to prepare:
Please inform your users that now end-to-end encrypted meetings support larger meeting size (i.e.,200 participants).
For more details how to use the feature, you can refer to: Use end-to-end encryption for Teams meetings – Microsoft Support
MC677231 — (Updated) Microsoft Teams: Engagement Information in Teams Attendance Report (Premium)
<30 Days
Microsoft 365 Roadmap ID 162171
Updated December 22, 2023: We have updated the rollout timeline below. Thank you for your patience.
The new engagement information will enable organizers to view meeting engagement data such as total reactions, raised hands, cameras turned on, and more in the “Attendance” tab after a meeting or webinar.
When this will happen:
Targeted Release: We will begin rolling out in early October 2023 and expect to complete rollout by late October 2023 (previously mid-October).
Standard Release: We will begin rolling out in early November 2023 (previously late October) and expect to complete rollout by mid-January 2024 (previously mid-December).
How this will affect your organization:
If your tenant turns ON the Attendance Report, organizers will see engagement information in the “Attendance” tab in calendar or meeting chat. Information will include count of reactions, raised hands, unmutes and cameras turned on at meeting level and attendee level.
What you need to do to prepare:
If you need engagement information in Attendance Report, please make sure the “Attendance Report” policy is turned ON by both the admin and the organizer.
Note: If the end user opts out of the Attendance Report in Teams settings, then the user’s engagement information will not be shown in the Attendance Report.
MC675503 — (Updated) Meeting Protection Support for Teams Rooms on Android
30-60 Days
Microsoft 365 Roadmap ID 161423
Updated December 11, 2023: We have updated the rollout timeline below as well as the content. Thank you for your patience.
The latest version of Teams Rooms on Android Update 3 (2023) includes the meeting protection support – End-to-end Encryption for meetings and Sensitivity labels.
When this will happen:
We will begin rolling out in early February 2024 (previously early January) and expect to complete rollout by mid-February 2024 (previously mid-January).
How this will affect your organization:
Teams Rooms on Android devices applies the Teams Premium meeting security features including end-to-end encryption and sensitivity labels if the meeting organizer has them turned ON.
Note: Features need to be activated through the Meeting options in Teams Calendar or Outlook on desktop or mobile devices. To enable the features a Teams premium license may be required.
If End-to-end Encryption is enabled, the Teams Rooms on Android will display a shield with a lock icon next to the view switcher. This icon includes a 20-digit group key that can be verified with other meeting participants. If a Teams meeting is set with a Sensitivity Label, room users will be informed that the label has been applied when clicking the shield with a lock icon.
Note: Together mode and Large Gallery are not available during End-to-end Encrypted Meetings, but meeting chat is permitted.
What you need to do to prepare:
Please notify your users about this new experience and update your training and documentation as appropriate.
MC673709 — (Updated) Microsoft Teams: New calendar views on Teams Rooms on Android
30-60 Days
Microsoft 365 Roadmap ID 157123
Updated December 11, 2023: We have updated the rollout timeline below. Thank you for your patience.
Microsoft Teams Rooms on Android users will soon be able to get a refreshed look and feel of the room calendar along with expanded functionalities. The release of this calendar upgrade will be rolling out with Microsoft Teams Rooms on Android Update 3 2023. This feature enhancement will be available in all Teams Rooms licenses.
When this will happen:
Standard Release: We will begin rolling out in early February 2024 (previously late January) and will be completed by mid-February 2024 (previously mid-December).
Note: There can be a delay between when features are released by Microsoft and when they become available on a device model and make. You can reach out to your device manufacturer to confirm the exact timeline of when this app update will be available on your device.
How this will affect your organization:
Users can view the room calendar for the current and next day. There is a date separator to distinguish today vs. tomorrow’s calendar items.
Like other Teams devices, a visual indicator in the form of green and purple vertical bar is added to each calendar slot so users can easily tell whether a room is booked or available at a glance. Any available 11-minute or more time slot is shown, allowing users who are searching for rooms in the office to easily determine whether a room can be used ad hoc.
Any meetings that are happening now or starting within the next 10 minutes are promoted to the top of the calendar as a focus tile with the same one touch join experience. Upcoming meetings that are happening later are shown as a non-focus tile, listed under the focus tile. Users can scroll trough the calendar to view the full list of room bookings and availabilities.
Users can tap anywhere on the non-focus tile to view the meeting details of upcoming meetings and access the Join button.
For better organization, when there are all day meetings scheduled, they are stacked together under the ‘All day’ page which can be accessed via the ‘All day’ bar found on top of the calendar. Non all day meetings remain on the first page of the calendar.
What you need to do to prepare:
Please plan on updating all Microsoft Teams Rooms on Android in your tenant to the latest version through the Teams Admin Center. Once devices are updated, you can notify your users about this change and update your training and documentation as appropriate.
MC671824 — (Updated) Power Automate app changing name to “Workflows” within Microsoft Teams
<30 Days
Microsoft 365 Roadmap ID 131294
Updated December 11, 2023: We have updated the rollout timeline below. Thank you for your patience.
To provide a unified workflow experience within Microsoft Teams we will be merging the existing Workflows app with the Power Automate app. With this merger the Power Automate app will be changing its name to “Workflows”.
There will be no change to user experience within the app. Users will still be able to manage all their flows within the app along with browsing workflow templates or creating a new flow from scratch. Whether you have existing workflows in the Power Automate app or the Workflows app your workflows will persist in the new unified app. Users will still be able to configure new workflows through the various app entry points (tab, bot, message extension, message action, personal app).
When this will happen:
Targeted Release: We will begin rolling out early October 2023 (previously mid-September) and expect to complete by mid-October 2023 (previously late September).
Standard Release: We will begin rolling out mid-October 2023 (previously late September) and expect to complete by early November 2023 (previously early October).
GCC Release: We will begin rolling out early November and expect to complete by mid-January 2024 (previously mid-December 2023).
How this will affect your organization:
Power Automate app will be changing its name to “Workflows”.
The app will be pre-installed for all Teams users when this merger is released. If users had uninstalled this app previously it will show for them again and they will need to uninstall.
Teams Admin Center: If admins previously disabled the Power Automate app it will still remain disabled after the merger. However, if admins had previously disabled the old Workflow app, since that app no longer exists, they will need to go back into TAC and disable the new Workflows app.
What you need to do to prepare:
Consider bringing awareness to your users about this change if your tenant uses the Power Automate app within Microsoft Teams.
MC666172 — (Updated) Microsoft Teams: Live Translated Transcript for Teams Premium Users
Rolled Out
Microsoft 365 Roadmap ID 126321
Updated December 11, 2023: We have updated the rollout timeline below. Thank you for your patience.
Teams’ users will be able to experience a live translated transcript during the meeting on the transcript side-pane. Users can choose their spoken language and translated transcript language.
When this will happen:
Public Preview: We will begin rolling out in early September and expect to complete rollout in mid-September.
Targeted Release: We will begin rolling out in early September and expect to complete rollout in mid-September.
Standard Release and GCC: We will begin rolling out in mid-September and expect to complete rollout by late September.
GCC High and DoD: We will begin rolling out in late October and expect to complete rollout by mid-December 2023 (previously late November).
How this will affect your organization:
To turn on transcription during the meeting: Go to the meeting toolbar, select More, select Record and transcribe, choose Start transcription.
By default, live transcriptions are displayed in the language that’s chosen as the “spoken language“ in the transcript option. Live translated transcription allows users to see transcriptions translated into the language they’ve chosen in the option “transcript language“ that can be accessed from the Settings icon :gear: in the Transcript pane.
What you need to do to prepare:
Please make sure you have a Teams Premium license to experience the feature. In the Teams admin center, admins can turn ON or turn OFF the Transcription setting within a meeting policy located under Meetings > Meeting policies. This setting is OFF by default. For additional information on configuring transcription and captions for Teams meetings, please visit this documentation.
MC661825 — (Updated) Microsoft Teams: On-Demand Recording Feature in Webinars
<30 Days
Microsoft 365 Roadmap ID 123052
Updated January 2, 2024: We have updated the rollout timeline below. Thank you for your patience.
Organizers can soon publish the recording of their webinars and automatically send an update to their attendees, in which they will receive a link to watch the on-demand recording hosted on their event page.
When this will happen:
We will begin rolling out in late September 2023 (previously late August) and expect to complete rollout by late January 2024 (previously mid-December).
How this will affect your organization:
The organizer would have the ability to pre-approve the recording prior to publishing it for attendees to view. This provides the opportunity for the organizer to either publish the default recorded event or upload their own custom video from their personal OneDrive.
Additionally, the organizer can also customize and preview the attendee notification prior to sending it out. Once sent, the attendees would then receive a link in their event invite and email to watch the on-demand recording on the event page.
What you need to do to prepare:
Tenant admins may need to apply the following policy changes to allow publishing of recordings:
Policy property will be under: CSTeamsEventsPolicy
Policy Property name:
AllowedWebinarTypesForRecordingPublish
Policy Values:
None
InviteOnly
EveryoneInCompanyIncludingGuests
Everyone
MC649917 — (Updated) Microsoft Teams: Stream Preview and Playback in Teams Chat and Channels
<30 Days
Microsoft 365 Roadmap ID 127596
Updated December 15, 2023: We have updated the rollout timeline below. Thank you for your patience.
Users can preview and play Stream videos directly in Teams Chat and Channel without having to open them in a browser and going to Stream.
When this will happen:
We will begin rolling out in late July 2023 and is expect to complete rollout by late January 2024 (previously mid-December).
How this will affect your organization:
Stream videos that are saved in OneDrive and SharePoint are now embedded in chat and channels enabling users to preview and play them directly in Teams without the need to open a browser window.
What you need to do to prepare:
There is nothing required from you at this time. You may want to notify your users and update any relevant training documentation as appropriate.
MC642265 — (Updated) Cloud IntelliFrame: A New Way to See People in Teams Rooms
<30 Days
Microsoft 365 Roadmap ID 130219
Updated December 18, 2023: We have updated the rollout timeline below. Thank you for your patience.
Cloud IntelliFrame is a new experience that allows online meeting attendees to see people in Teams Rooms more clearly, enhancing the hybrid meeting experience by creating smart video feeds of in-room participants. The smart video feed is created by zooming into their faces and eliminating distractions. You can see the expressions and gestures of the people in the room more easily, which will help improve collaboration in hybrid meetings. It creates equity in hybrid meetings as everyone can be seen and heard.
Cloud IntelliFrame will be rolling out across Microsoft Teams Rooms on Windows with Pro license and can be viewed on Microsoft Teams Desktop (Windows & Mac) with any license.
When this will happen:
Standard Release and GCC: We will begin rolling out to commercial tenants in mid-August and expect to complete rollout by late January 2024 (previously mid-November).
GCC High will begin rollout by late January 2024 (previously mid-November).
How this will affect your organization:
All Microsoft Teams Rooms on Windows with a Pro license equipped with cameras in the supported camera list will automatically opt-in to Cloud IntelliFrame. Online participants on Microsoft Teams Desktop (Windows and Mac) will see the IntelliFrame video feed by default from Rooms with these cameras.
An icon on the top right of the Room video feed indicates that Cloud IntelliFrame is being displayed.
People in the Room can disable IntelliFrame by using in-meeting settings on the console. This turns off IntelliFrame and switches back to standard view for the Room. All online attendees would then see the standard view from the respective Room.
People on Teams Desktop can also toggle IntelliFrame on/off by right clicking on the Room video tile and selecting ‘Turn off IntelliFrame’. This switches off the IntelliFrame view just on their Teams client.
The following camera models when deployed in a Microsoft Teams Room on Windows with a Pro license will automatically use Cloud IntelliFrame:
AVer CAM520 Pro
AVer CAM520 Pro2
BRIO 4K Stream Edition
EagleEye Cube USB
HD Pro Webcam C920
Jabra PanaCast
Logi Rally Camera
Logitech BRIO
Logitech ConferenceCam CC3000e
Logitech MeetUp
Logitech Webcam C925e
Logitech Webcam C930e
Microsoft® LifeCam Studio
Polycom EagleEye IV USB Camera
PTZ Pro 2
PTZ Pro Camera
ThinkSmart Cam
Yealink UVC30
Yealink UVC34
Yealink UVC50
Yealink UVC80
Yealink UVC86
What you need to do to prepare:
You may want to notify your users about this capability. Cloud IntelliFrame shows the smart feed when there are 9 or less people in the room. It automatically switches between the standard room view and IntelliFrame view based on in-room activity. For example, if someone enters the meeting room, the view would automatically switch to standard room view until the individual settles down.
Cloud IntelliFrame is ideal for focus rooms and medium spaces. Large spaces may not be ideal as people furthest from the camera may appear blurry after digital zoom. You may also want to switch off Cloud IntelliFrame in Rooms with glass walls without any privacy filter.
To switch off Cloud IntelliFrame in a room:
Follow this guide to create an XML configuration file
Add the following element: <CloudIntelliFrame>False</CloudIntelliFrame>
Restart the console to process the configuration changes.
MC499441 — (Updated) The Room Remote feature for desktop
30-60 Days
Microsoft 365 Roadmap ID 95482
Updated December 11, 2023: We have updated the content below with additional information. Thank you for your patience.
The Room Remote feature enables touchless meetings by allowing users to control a nearby shared meeting room device from their Desktop/PC with Teams client.
This feature was first launched on Mobile and will now be available on your Desktop device formfactor.
When this will happen
Rollout to commercial tenants is expected to start mid-January 2024 and will complete early February 2024 (previously mid-December). GCCH and DoD will be announced in a separate message at a later date.
How this will affect your organization
Room Remote is and existing mobile feature that’s arriving on Windows desktop, and will be automatically available on the Teams desktop client on your Windows Desktop PC so long that the Room Remote feature is enabled on the shared meeting room device and in TAC.
When users proximity join a meeting, a banner will appear, prompting the user to take control of the room system.
Any time during a meeting, in-room users can also access Room Remote on their desktop client through the roster. The room menu in roster will show an option to Control Room System. That option will launch Room Remote.
What you need to do to prepare:
You may want to notify your users about this new capability and update your training and documentation as appropriate. Room Remote requires Bluetooth to be enabled, and the feature to be enabled on the shared meeting room device and in TAC.
Microsoft Stream
MC699712 — Microsoft Stream: Improved block download experience for video files
<30 Days
Some videos are meant to be viewed but not downloaded. In the previous experience, customers had to change their permissions inside the share link settings to “Can view” before they could enable the ‘block download’ feature toggle:
For video files, it is now easier than ever to enable this feature. To keep your videos secure, we’ve added the “Can view, but not download” option to the permission drop down for share links in the Microsoft 365 Share Dialog for Stream videos.
When this will happen:
Targeted Release: We will begin rolling out mid-December 2023 and expect to complete by late December 2023.
Standard Release: We will begin rolling out late December 2023 and expect to complete by early January 2024.
How this will affect your organization:
This change is specific to video files only on OneDrive, SharePoint, and Stream. Once available, users will be able to use “Can View, but not download” as an option.
What you need to do to prepare:
Update your training documentation as appropriate.
MC698135 — Microsoft Stream: View and Edit mode toggle
<30 Days
Microsoft 365 Roadmap ID 124992
You will be able to toggle between View and Edit modes when viewing a Stream video. In View mode users can only view the video. In Edit mode users with edit permission can edit the video metadata such as title, description, chapters, and transcript. The default mode will be View. The View/Edit mode toggle is designed to prevent accidental edits to video metadata.
When this will happen:
These additional features will be rolled out to Production in mid-December 2023 and complete in January 2024.
How this will affect your organization:
This feature allows users with editing permissions on videos to toggle between View and Edit modes when viewing a Stream video. In View mode users can only view the video. In Edit mode users with edit permission can edit the video metadata such as title, description, chapters, and transcript. The default mode will be View. The View/Edit mode toggle is designed to prevent accidental edits to video metadata.
Note: Some users may see this feature before other users with your organization.
What you need to do to prepare:
You may consider updating your training and documentation as appropriate.
MC688631 — (Updated) Microsoft Stream: Add a hyperlink or text callout to a video at specific times
<30 Days
Microsoft 365 Roadmap ID 180795
Updated December 13, 2023: We have updated the rollout timeline below. Thank you for your patience.
Make your video interactive and more engaging by adding annotations that can include hyperlinks and text. Call out important moments or share documents and other links to additional resources. You can add text and links anywhere in the video timeline to help guide your viewers to the right information. Viewers can use video timeline markers to navigate interactive content.
When this will happen:
Targeted release will begin rolling out in early January 2024 (previously early December).
Standard Release will begin rolling out in late January 2024.
How this will affect your organization:
Users will be able to make interactive videos in Microsoft Stream by adding a hyperlink or text callout at specific times.
Note: Some users may see this feature before other users with your organization.
What you need to do to prepare:
There is no action required from you at this time.
Intune
MC699709 — Expanded capabilities in the Microsoft Intune Suite
30-60 Days
We are adding new solutions to the Intune Suite to further unify your advanced endpoint management solutions in one place. This includes adding three new solutions to the license for Intune Suite and offering these additional solutions as standalone add-ons to Microsoft 365 plans that include Intune.
Global and Billing administrators can add trial licenses or choose to purchase licenses from the centralized Intune Add-ons experience in the Intune admin center.
How this will affect your organization:
If you have already purchased licenses for the Intune Suite, the following new solutions will be added to your service plan and start to roll out to tenants based on the following timeline (roll out may take a few days):
Microsoft Intune Advanced Analytics – February 1, 2024
Microsoft Intune Enterprise Application Management – February 1, 2024
Microsoft Cloud PKI – in the February (2402) release of Intune approximately February 26, 2024
These same solutions will be added to the Intune Add-ons page in the Intune admin center and available for use as standalone solutions, available for trial (up to 250 users for 90 days) or for purchase.
What you need to do to prepare:
If you have already purchased sufficient licenses of the Intune Suite to cover users with these additional solutions, no action is required. Once these new solutions roll out in Intune, they will be automatically added to your service plan for the Intune Suite.
If you have not purchased licenses for the Intune Suite, the new add-ons and trial options for Advanced Analytics and Enterprise App Management will be available February 1, 2024 and Cloud PKI will be available on March 1, 2024.
MC696846 — (Updated) Plan for Change: Update your macOS Company Portal minimum version to v5.2312.0
<30 Days
Updated January 2, 2024: We have updated the timing of this change below.
We will soon release an updated Company Portal for macOS (v5.2312.0) that is a required app update. Starting on January 22, 2024, or soon after, the minimum supported version of the macOS Company Portal will change to v5.2312.0.
How this will affect your organization:
User impact: Most users have app updates set to automatic, so they receive the updated Company Portal app without taking any action. Users that have an earlier app version will be prompted to update to the latest Company Portal app and will need to update to continue using the app.
What you need to do to prepare:
No action is needed, but if you have a helpdesk, you may want to make them aware of the prompt to update the Company Portal app.
Additional information:
Microsoft Defender XDR
MC698829 — Feature retirement – Evaluation Lab retirement
<30 Days
As we continue to evaluate the value of the features and services to provide, we have made the decision to retire the Defender Evaluation Lab.
When this will happen:
This change will rollout in mid-January 2024 and expect to complete by late January 2024.
How this affects your organization:
After this change is implemented, the following resources will no longer be available or supported:
https://security.microsoft.com/evaluation
https://security.microsoft.com/tutorials
subsequent APIs
Whay you need to do to prepare:
You may consider updating training and documentation as appropriate.
MC698130 — Threat Protection report page retirement
<30 Days
Updated December 18, 2023: We have updated the content below to show as intended. Thank you for your feedback.
We will be retiring the Threat Protection report page – https://security.microsoft.com/mde-reports/threatProtection (accessed through Reports > Endpoints > Threat protection). Instead, we recommend the utilization of Advanced hunting queries and Alert queue filter in Defender XDR, which is where we will continue to invest our development resources.
When this will happen:
Late January 2024
How this will affect your organization:
Once this change is implemented the Threat Protection report page will no longer be accessible.
What you need to do to prepare:
Review supporting documentation and make adjustments as appropriate for your organization.
Threat protection report in Microsoft Defender for Endpoint
Prioritize incidents in Microsoft Defender XDR
Proactively hunt for threats with advanced hunting in Microsoft Defender XDR
MC697431 — WDAC Advanced Hunting Retired ActionTypes and Fields
<30 Days
Microsoft will be renaming the PolicyNameBuffer and PolicyIdBuffer fields in MDE Advanced Hunting WDAC events. These fields will be renamed to PolicyName and PolicyID, respectively. We will continue to improve the experience and richness of WDAC event data in Advanced Hunting.
Additionally, we will be retiring the following WDAC action types from Advanced Hunting:
AppControlCodeIntegrityImageAudited (3035)
AppControlCodeIntegrityPolicyAudited (3078)
AppControlCodeIntegrityPolicyBlocked (3079)
AppControlCodeIntegrityPolicyAudited (3080)
AppControlCodeIntegrityPolicyBlocked (3081)
When this will happen:
We will begin rolling out this change in mid-January 2024 and expect to complete by late January 2024.
How this will affect your organization:
For customers currently using the WDAC “AppControl” action types, here is a list of the fields that will be retired, alongside their alternatives in Advanced Hunting:
What you can do to prepare:
Your organization might be using PolicyNameBuffer or PolicyIdBuffer in your Advanced Hunting queries and custom detections which will be retired soon. Please update your queries with the new fields to continue to leverage this valuable data and avoid breaking your current custom detections.
An example of your old query:
DeviceEvents
| where ActionType startswith ‘AppControl’
| extend PolicyName = parsejson(AdditionalFields).PolicyNameBuffer
| extend PolicyId = parsejson(AdditionalFields).PolicyIdBuffer
| project ActionType,PolicyId,PolicyName
Your new query:
DeviceEvents
| where ActionType startswith ‘AppControl’
| extend PolicyName = parsejson(AdditionalFields).PolicyName
| extend PolicyId = parsejson(AdditionalFields).PolicyID
| project ActionType,PolicyId,PolicyName
MC696570 — Service health and Message center: ‘Microsoft 365 Defender’ rebranding to ‘Microsoft Defender XDR’
Rolled Out
We recently announced at Ignite that ‘Microsoft 365 Defender’ has been rebranded as ‘Microsoft Defender XDR’. As a continuation of that announcement, the service listings on Service health and Message center will also be rebranded. In the month of December, the service titled ‘Microsoft 365 Defender’ will be renamed to ‘Microsoft Defender XDR’.
When this will happen:
This will be rolled out to Service health and Message center by end of December 2023.
How this will affect your organization:
Communications related to “Microsoft 365 Copilot” and its family of products may appear under “Microsoft Copilot for Microsoft 365” in Service health and Message center.
What you need to do to prepare:
You might consider updating your administrator training and documentation as needed.
MC675279 — (Updated) Reminder – Microsoft Defender for Identity: Classic portal automatic forced redirection
<30 Days
Updated December 11, 2023: We have updated the rollout timeline below. Thank you for your patience.
Beginning on mid-October, access to Microsoft Defender for Identity legacy portal at portal.atp.azure.com will be unavailable for Gov environments (MC567494 June ’23). Any request will be automatically redirected to Microsoft 365 Defender portal at security.microsoft.com. All new and existing tenants will be automatically redirected to the M365 Defender portal, and the option to opt-out will no longer be available.
When this will happen:
This will begin rollout on mid-October 2023 (previously late September) and is expected to be complete by late January 2024 (previously late November).
How this will affect your organization:
Once the forced redirection takes place, any requests to the standalone Defender for Identity portal (portal.atp.azure.com) will be redirected to Microsoft 365 Defender (securtiy.microsoft.com) along with any direct links to its functionality.
Organizations cannot manually opt-out and disable the setting.
What you need to do to prepare:
Ensure your security teams are familiar with Defender for Identity’s features and settings as they are represented in Microsoft 365 Defender. If your security teams need help, please direct them to the updated documentation available here.
Microsoft Purview
MC697428 — Microsoft Purview: Data Lifecycle and Records Management – Scope the administration of retention and label policies
<30 Days
Microsoft 365 Roadmap ID 117353
To assist in the implementation of security best practices, we are introducing new way to assign administrative privileges in the Microsoft Purview Data Lifecycle Management and Microsoft Purview Records Management solutions that will provide admins the least privilege access required for their job duties.
With this change, organizations can leverage Administrative Units in Azure Active Directory (AAD) to define who can configure and manage policies in Microsoft Purview. This update will include the ability to set up a Data Lifecycle Management or Records Management admin for a specific geography, department, or other unit, who can manage retention and label policies for their unit.
When this will happen:
Rollout will begin in late December 2023 and is expected to be complete by early January 2024.
How this will affect your organization:
Once this feature rolls out, Data Lifecycle Management and Records Management administrators in your organization will have the ability to use administrative units to granularly define access to who can manage retention policies and label policies for different parts of the organization.
Previously, you were only able to assign a tenant-wide admin for Data Lifecycle Management. These people would configure and administer retention and label policies for every part of the organization. Now, you can associate Data Lifecycle Management administrators to one or more admin units. This enables administrators who can view and manage policies for only part of an organization to do so confidently without affecting other units. For example, you can designate an administrator for the Finance Admin Unit. This person can then create polices that apply only to Finance users, groups, or sites.
What you need to do to prepare:
You may consider updating any training or reference material for your Data Lifecycle Management and Records Management administrators and evaluate if you would like to use this new capability.
Get started with Data Lifecycle Management and Records Management in the Microsoft Purview compliance portal – https://compliance.microsoft.com/homepage.
Learn more: Permissions in the Microsoft Purview compliance portal
MC696856 — Changes to data from Microsoft Purview Audit in the Management Activity API WW endpoint
<30 Days
Starting 10 January 2024, activity data from Exchange will only be available from the Microsoft 365 Management Activity API endpoint scoped to GCC. You must ensure you are using the GCC-specific endpoint to continue accessing these activity logs through the Management Activity API.
How this will affect your organization:
You are receiving this message because your organizations is hosted in Microsoft’s Government Community Cloud (aka “GCC”) and our reporting indicates your organization may be using the global Microsoft 365 Management Activity API endpoint to retrieve activity data from Microsoft Purview Audit. To avoid being affected by the upcoming changes, you must ensure you are using the GCC-specific endpoint to access activity data from the Management Activity Feed API. This change does not impact other cloud environments, nor does this affect your organization’s ability to access activity telemetry through the Microsoft Purview Audit Search.
What you need to do to prepare:
You must update each instance where your organization is calling the WW endpoint, and change this to call the correct endpoint for your organization in GCC.
Management Activity Feed API Endpoints
Endpoint reserved for customers in GCC cloud: https://manage-gcc.office.com/
Endpoint reserved for customers in WW cloud: https://manage.office.com/
Learn more about Activity API endpoints here https://learn.microsoft.com/en-us/office/office-365-management-api/office-365-management-activity-api-reference#activity-api-operations
Common affected scenarios:
For any code/script instances where your organization has requested access tokens [https://aka.ms/ActivityAPIGetAccessToken} to access data from the M365 Management Activity API, change the resource endpoint address from “https://manage.office.com/“to “https://manage-gcc.office.com/“
For any code/script instances where your organization is calling the M365 Management Activity API [https://aka.ms/ActivityAPICheckSubscription], change the endpoint address from https://manage.office.com/ to https://manage-gcc.office.com/
If you have enabled API notifications, then you will have to re-create the API notification subscriptions [https://aka.ms/ActivityAPICreateSubscription] using the https://manage-gcc.office.com/ endpoint.
MC696855 — Microsoft Purview compliance portal: Ux support to identify ODB site for an inactive mailbox in eDiscovery (Premium)
<30 Days
Microsoft 365 Roadmap ID 189639
Updated December 22, 2023: We have updated the rollout timeline below. Thank you for your patience.
We are rolling out support through the user interface to auto identify the OneDrive sites associated with an Inactive mailbox when adding Custodians in an eDiscovery (Premium) case.
When this will happen:
Rollout will begin in late December 2023 (previously mid-December) and is expected to be complete by early January 2024 (previously late December).
How this will affect your organization:
When a user having the roles and permissions to add Custodians to a case, adds a user with an inactive mailbox as a custodian, the OneDrive site associated with the inactive mailbox will be auto selected to be added as a data source to the case.
This is currently supported through the user interface only.
What you need to do to prepare:
Notify your users about this new capability in eDiscovery (Premium).
Learn more about Microsoft Purview eDiscovery solutions – Microsoft Purview (compliance) | Microsoft Docs.
MC695500 — (Updated) Microsoft Purview Information Protection: Tracking and Revocation in Compliance Portal
Rolled Out
Microsoft 365 Roadmap ID 177890
Updated December 7, 2023: After review we have determined we won’t be moving forward with this change at this time. We will communicate a new timeline via Message center when we are ready to proceed. Thank you for your patience.
Users can access the Microsoft Purview compliance portal to check who has tried accessing their sensitivity labeled and encrypted local Office files and revoke access when needed.
When this will happen:
We will communicate a new timeline via Message center when we are ready to proceed.
How this will affect your organization:
Within Office, end users will see Track & Revoke Access within the Sensitivity button. When end users are the owners of a local file and they click on this button, they will be taken to the Microsoft Purview compliance portal where they can see user access attempts for the local file and have the option to revoke access.
In addition, admins will be able to view the tracking logs for all users and revoke access to local Office files using PowerShell commandlets.
Get-AipServiceDocumentLog searches for a document using the filename or the email address of the user who applied protection.
Get-AipServiceTrackingLog uses the file’s ContentID to return tracking data.
Set-AIPServiceDocumentRevoked uses the file’s ContentID to revoke access.
Clear-AipServiceDocumentRevokeduses the file’s ContentID to restore the access.
What you need to do to prepare:
The Microsoft Purview Information Protection Tracking and Revocation feature will be turned on by default. To disable the feature, use the Disable-AipServiceDocumentTrackingFeature commandlet.
MC693861 — (Updated) Exchange auto-labeling supports non-mail enabled security groups
30-60 Days
Microsoft 365 Roadmap ID 184909
Updated December 22, 2023: We have updated the rollout timeline below. Thank you for your patience.
Service side auto-labeling now allows scoping of exchange workload to non-mail enabled security groups.
When this will happen:
Rollout will begin in late November and is expected to be complete by mid-February 2024 (previously mid-December).
How this will affect your organization:
Admins can create new or edit existing auto-labeling policies to include Exchange locations for non-mail enabled security groups.
What you need to do to prepare:
Determine if your organization has any non-mail enabled security groups that should have their mail automatically labeled.
Automatically apply a sensitivity label in Microsoft 365 | Microsoft Learn
MC692463 — (Updated) Microsoft Purview Insider Risk Management: General availability of SharePoint site selection enhancement
30-60 Days
Microsoft 365 Roadmap ID 169880
Updated January 2, 2024: We have updated the rollout timeline below. Thank you for your patience.
Microsoft Purview Insider Risk Management will be rolling out general availability of SharePoint site selection enhancement.
When this will happen:
Rollout will begin mid-January 2024 (previously late November) and is expected to be complete by early February 2024 (previously mid-December).
How this will affect your organization:
With this update, Insider Risk Management admins can add any SharePoint sites as priority content or exclude certain SharePoint sites in Insider Risk Management policies by searching the site names or using the exact URLs.
What you need to do to prepare:
You can add SharePoint sites to exclusion at insider risk settings > intelligent detections.
You can add SharePoint sites to priority content at Policies > create/ edit policy.
Microsoft Purview Insider Risk Management correlates various signals to identify potential malicious or inadvertent insider risks, such as IP theft, data leakage, and security violations. Insider Risk Management enables customers to create policies based on their own internal policies, governance, and organizational requirements. Built with privacy by design, users are pseudonymized by default, and role-based access controls and audit logs are in place to help ensure user-level privacy.
You can access the Insider Risk Management solution in the Microsoft Purview compliance portal.
Learn more: Learn about insider risk management settings | Microsoft Learn
MC690611 — (Updated) Data Loss – “Deliver the message to the hosted quarantine” in DLP EXO
30-60 Days
Microsoft 365 Roadmap ID 124975
Updated January 2, 2024: We have updated the rollout timeline below. Thank you for your patience.
We’re rolling out a new action for Data Loss Prevention in Exchange Online called “Deliver the message to the hosted quarantine”.
When this will happen:
Rollout will begin in late January 2024 (previously late December) and is expected to be complete by mid-February 2024 (previously early January).
How this will affect your organization:
Previously while managing messages delivered to hosted quarantine, admins had to filter these messages under transport rules. With this update, we are adding a new column where the messages delivered to quarantine can be viewed under “Data Loss Prevention”.
What you need to do to prepare:
If you are currently not using this action, there is no impact to your organization, but if you are using this action and were monitoring messages that are being quarantined in the Quarantine/ Threat Explorer/Mailflow Status/TPS/Adv Hunting reports you will need to update your Quarantine reason/Policy Type filter from “Transport Rule” to “Data Loss Prevention” to look for the messages that were quarantined because of DLP.
Get started with Data Loss Prevention in the Microsoft Purview compliance portal.
Learn more: DLP policy conditions, exceptions, and actions.
MC690178 — (Updated) Information Protection – Keyword highlight support for document trainable classifiers
>60 Days
Microsoft 365 Roadmap ID 170738
Updated December 22, 2023: We have updated the rollout timeline below. Thank you for your patience.
The keyword highlighting feature for Trainable Classifiers emphasizes the top 10 distinct keywords/phrases that influence the classification, showcasing up to 10 occurrences of each keyword.
The feature is being enabled through:
Content Explorer:
Viewing the classified document through Content explorer will highlight the keywords that match the Trainable classifiers detected.
Test Trainable classifier:
Uploading a document and testing it for a specific classifier OR selecting the document in the classifier’s matched item will highlight the keywords that match the Trainable classifier detected.
Note:
This feature will only work on the new/edited documents after the date “keyword highlight” has been enabled.
When this will happen:
Rollout will begin in mid-February 2024 (previously early December) and will complete by mid-March 2024 (previously late December).
How this will affect your organization:
The keyword highlight feature enables you to:
Quickly locate text that caused the positive outcome in the classifier.
Establish trust in the effectiveness of trainable classifiers.
Reduce the time to decide and take further actions.
What you need to do to prepare:
This feature will only work on new/edited documents after the date “keyword highlight” has been enabled.
Release of Keyword Highlighting for Train & new Business Context Classifier (microsoft.com)
Trainable classifiers definitions
Increase Classifier Accuracy | Microsoft Learn
MC686920 — Microsoft Purview Information Protection – Discover and co-author documents labeled with user-defined permissions
30-60 Days
Microsoft 365 Roadmap ID 109570
Updated December 11, 2023: We have updated the rollout timeline below. Thank you for your patience.
Coming soon SharePoint and OneDrive will support discovery and coauthoring of files labeled with user-defined permissions.
When this will happen:
This is currently rolling out and is expected to be complete by early February 2024 (previously late November).
How this will affect your organization:
With this feature, SharePoint and OneDrive can process labeled documents that are encrypted with custom permissions, also referred to as user-defined permissions. As a result they can also be opened, edited, seamlessly co-authored, and support AutoSave in Word, Excel, and PowerPoint apps on all platforms (including Office for the web).
Note: Support for user search and eDiscovery is coming soon by December 2024.
What you need to do to prepare:
No special action is needed to enable this feature. However, as this changes existing behavior for files labeled with user-defined permissions, we recommend educating your users and updating documentation as needed.
Review and define label policies and settings, and access Microsoft Purview Information Protection, Data Loss Prevention, and eDiscovery solutions in the Microsoft Purview compliance portal.
Learn more:
Get started with sensitivity labels
Enable co-authoring for encrypted documents
MC683661 — (Updated) Announcing GA of Admin units in Microsoft Purview Information Protection and Data Loss Prevention
Rolled Out
Microsoft 365 Roadmap ID 165027
Updated December 13, 2023: We have updated the rollout timeline below. Thank you for your patience.
We’re rolling out a new capability in GCC, GCC-H, DoD that enables admins to delegate management and remediation authority for different people in different regions or organization units with role-based access control (RBAC) via Azure Active Directory Administrative Units. For example, German Admin Unit investigators would be able to investigate alerts and audit events for only German users.
When this will happen:
GCC, GCC-H, DoD rollout will begin in late October and is expected to be complete by late December 2023 (previously mid-December).
How this will affect your organization:
If you choose to not use this Admin Units feature, there is no impact to your organization. If your organization requires delegations of tasks based on users in specific regions or organization units, please follow the steps to set up this capability:
Set up Administrative Units (AU) in Azure Portal
Ring-fence Purview Admin Permissions to Administrative Unit scopes
Create and manage Admin Unit scoped MIP/DLP policies
Investigate user scoped DLP Alerts, Incidents, and Logs in Purview
Investigate user scoped Activities and events in Activity Explorer
Note- This Admin Units capability will be extended to Data Loss Prevention alerts in the Microsoft 365 Defender portal and can be tracked as part of the roadmap ID here: 162292
What you need to do to prepare:
Get started with Information Protection and Data Loss Prevention in the Microsoft Purview compliance portal.
Learn more: Permissions in the Microsoft Purview compliance portal
MC683034 — (Updated) Microsoft Purview: Moving from Audit Classic experience to New Search experience
Rolled Out
Updated December 11, 2023: We have updated the rollout timeline below. Thank you for your patience.
In our ongoing efforts to enhance your search experience and provide you with the best possible service, we are replacing the Audit Classic Search with our improved Audit New Search feature, as customers have had since October 2022 to adopt the more robust experience. We want to ensure all affected customers are aware that the Classic Search experience will be retired and no longer accessible from the Compliance Portal starting in mid-December 2023 (previously late November). Customers are encouraged to adopt the new more robust experience now,
When this will happen:
Mid-December 2023 (previously late November)
How this will affect your organization:
This improved Audit search has been meticulously designed and engineered to be more efficient, powerful, and user-friendly, enabling you to find the information you need with even greater speed and accuracy. We have listened to your feedback and incorporated many of your suggestions into this updated search functionality. During this period, we encourage you to familiarize yourself with the new search and take advantage of its advanced capabilities.
What you can do to prepare:
You may consider updating your training and documentation as appropriate.
We appreciate your understanding and cooperation during this transitional period. Our goal is to continuously improve our services to better serve your needs, and we firmly believe that the new search will exceed your expectations.
For additional information on the Audit New Search feature, see: Audit New Search.
MC682084 — (Updated) Microsoft Purview Insider Risk Management: Public preview of administrative units support
30-60 Days
Microsoft 365 Roadmap ID 171717
Updated December 22, 2023: We have updated the rollout timeline below. Thank you for your patience.
Coming soon, Microsoft Purview Insider Risk Management will be rolling out public preview of administrative units support.
When this will happen:
Rollout will begin mid-January 2024 (previously late November) and is expected to be completed by mid-February 2024 (previously late December).
How this will affect your organization:
Administrative units allow admins with appropriate permissions to subdivide the organization into smaller units, and then assign specific admins or role groups that can manage only the members of those units. For example, German administrators can only create/manage policies for only German users, and German investigators can only investigate alerts and activities from only German users.
What you need to do to prepare:
Admins can configure administrative units in Azure by adding users and groups to new or existing administrative units. Admins can then assign these administrative units to solution admins or members of Insider Risk Management role groups from the permissions area of Microsoft Purview compliance portal. After the configuration, when these restricted administrators create or edit policies that support administrative units, they can select only the users in those administrative units as part of the policy.
Microsoft Purview Insider Risk Management correlates various signals to identify potential malicious or inadvertent insider risks, such as IP theft, data leakage, and security violations. Insider Risk Management enables customers to create policies based on their own internal policies, governance, and organizational requirements. Built with privacy by design, users are pseudonymized by default, and role-based access controls and audit logs are in place to help ensure user-level privacy.
You can access the Insider Risk Management solution in the Microsoft Purview compliance portal.
Learn more: Permissions in the Microsoft Purview compliance portal |Microsoft Learn
MC675959 — Microsoft Information Protection: Microsoft Purview: Exact Data Match to support multi-token corroborative evidence.
Rolled Out
Microsoft 365 Roadmap ID 124847
Updated November 30, 2023: We have updated the rollout timeline below. Thank you for your patience.
Exact Data Match (EDM) will support string match detection of multi-token (i.e., fields with multiple words separated by spaces or punctuation) corroborative evidence without requiring mapping Sensitive Information Types (SITs) to multi-token corroborative evidence fields.
When this will happen:
Rollout will begin in mid-November 2023 and is expected to be complete by mid-December 2023.
How this will affect your organization:
With this release, multi-token corroborative evidence can be detected as a string match, without requiring it to be mapped to a Sensitive Information Type (SIT) that is able to detect that content as a single entity, which may result in more accurate EDM detection.
In some cases, it may still make sense to map a SIT to a corroborative evidence field, both to reduce latency by limiting the amount of content that needs to be compared for each match, and to eliminate some potential false positives. For example, if you have indicated multiple characters as ignored delimiters using configurable match, but still want to only detect matches on strings which are formatted with some of the delimiters or where multiple delimiters match each other.
In general, if a SIT can be accurately matched to a corroborative evidence column, it is preferred to do so rather than to rely on automatic single-word or multi-token matching.
What you need to do to prepare:
To use this feature, you need to opt-in for multi-token support for each corroborative evidence field that you want enabled. You can do this either through the new EDM UI experience (see screenshot above) or through a schema XML file update. Before doing so, you will need to first uninstall your current version of the EDM Upload Agent and download / install the latest version from: https://learn.microsoft.com/en-us/purview/sit-get-started-exact-data-match-hash-upload#links-to-edm-upload-agent-by-subscription-type.
Once this feature has been released, additional details will be found in our EDM public documentation:
Learn about exact data match based sensitive information types | Microsoft Learn
MC663629 — (Updated) Microsoft Purview: General Availability of Microsoft Purview Insider Risk Management forensic evidence add-on
30-60 Days
Microsoft 365 Roadmap ID 117565
Updated December 13, 2023: We have updated the timing of this change, below. Thank you for your patience.
Microsoft Purview Insider Risk Management forensic evidence add-on is an optional, additional capacity feature in Microsoft Purview Insider Risk Management that gives security teams visual insights into potential insider data security incidents, with user privacy built in.
Organizations with Microsoft 365 E5/G5, Microsoft 365 E5/G5 Compliance, or Microsoft 365 E5/G5 Insider Risk Management are eligible to purchase Insider Risk Management Forensic Evidence 100GB Add-on.
Microsoft Purview Insider Risk Management correlates various signals to identify potential malicious or inadvertent insider risks, such as IP theft, data leakage, and security violations. Insider Risk Management enables customers to create policies based on their own internal policies, governance, and organizational requirements. Built with privacy by design, users are pseudonymized by default, and role-based access controls and audit logs are in place to help ensure user-level privacy.
When this will happen:
This new SKU, Insider Risk Management Forensic Evidence 100GB add-on, will be available starting mid-February 2024 (previously mid-January).
What you need to do to prepare:
Once available, organizations can purchase Insider Risk Management Forensic Evidence 100GB add-on.
MC609873 — Microsoft Purview Data Loss Prevention: Configure policy tips as pop-up dialog for emails with sensitivity labels
<30 Days
Microsoft 365 Roadmap ID 139511
Updated December 13, 2023: We have updated the rollout timeline below. Thank you for your patience.
Data Loss Prevention policies can be configured to display policy tips as a pop-up dialog for emails with sensitivity labels.
When this will happen:
Rollout will begin in early December 2023 (previously mid-October) and is expected to be complete by late January 2024 (previously mid-December).
How this will affect your organization:
Admins can configure DLP policies to show policy tips as a dialog to end users when they attempt to send email messages that include a sensitivity label on the email or attachment. With this capability, admins can set up rules to warn or block or request for an explicit acknowledgement or a business justification from users before sending emails. Furthermore, admins can customize a learn more URL in a DLP rule, ensuring that end users receive valuable guidance through the popup.
Note: Users included in these policies must hold E5/G5 or equivalent licenses.
What you need to do to prepare:
Configure policy tips for Data Loss Prevention in the Microsoft Purview compliance portal:
Microsoft Purview compliance portal for GCC cloud environments
Microsoft Purview compliance portal for GCC-High cloud environments
Microsoft Purview compliance portal for DoD cloud environments
Learn more:
Learn how to configure a DLP rule with oversharing popups: Create and Deploy data loss prevention policies
View the AIP migration playbook: Migrate Oversharing Popups from AIP
MC598630 — (Updated) Microsoft Purview Data Loss Prevention – DLP Policy tips revamp for Outlook for Windows for E5/G5 users
<30 Days
Microsoft 365 Roadmap ID 138577
Updated December 13, 2023: We have updated the rollout timeline below. Thank you for your patience.
We’re rolling out new and improved DLP Policy tips in Outlook for Windows to support top DLP predicates and exceptions, all advanced classifiers, and override capabilities for E5/G5 users.
When this will happen:
Rollout will begin in early December 2023 (previously mid-November) and is expected to be complete by late January 2024 (previously mid-December).
How this will affect your organization:
You can now alert or restrict your users from unauthorized or accidental sharing of any sensitive information via email in Outlook win32 by leveraging new and improved DLP Policy tips in new or existing DLP policies. These real time alerts and recommendations empower your organization to accurately identify sensitive information being shared with unauthorized recipients or domains and take appropriate action.
DLP Policy tips now support a richer set of DLP conditions (and corresponding exceptions), including the following:
Content Contains Sensitive Information
Content contains Sensitivity label
Content is shared internally/externally
Sender is
Sender domain is
Sender is member of
Recipient is
Recipient domain is
Recipient is a member of
Subject contains words
Additionally, DLP Policy tips now support advanced classifiers like Trainable classifiers, Exact data match (EDM), Named Entities, and Credential scanning SITs, as well as an override feature that gives end users the ability to quickly and easily modify or override policies (if allowed in the DLP rule configuration), ensuring that the sensitive data is always protected, while still allowing end users to work efficiently.
What you need to do to prepare:
You can create new DLP policies or leverage the existing ones to use DLP Policy tips as an additional layer of security for sensitive data.
Get started with Data Loss Prevention in the Microsoft Purview compliance portal:
Microsoft Purview compliance portal for GCC cloud environments
Microsoft Purview compliance portal for GCC-High cloud environments
Microsoft Purview compliance portal for DoD cloud environments
Learn more:
Create, test, and tune a DLP policy
Data Loss Prevention policy reference
Learn about data loss prevention
MC455516 — (Updated) Automatic migration of legacy Office 365 Message Encryption to Microsoft Purview Message Encryption
<30 Days
Updated January 2, 2024: We have updated the timing of this change below.
After retirement, any encrypted mail sent to shared mailbox protected with Microsoft Purview Message Encryption will have a link that can open the mail in Outlook on the web. This provides an equivalent flow to open messages protected using Office 365 Message Encryption.
As a reminder, the following PowerShell cmdlet parameter will be retired in New/Set-Transport rule cmdlet:
-ApplyOME
-RemoveOME
Note: If you use the Exchange Admin Center to create/modify a mail flow rule, the action will fail with a message to indicate the above functions have been retired.
Microsoft Purview Message Encryption will replace and retire the legacy Office 365 Message Encryption (OME) in the Exchange admin center. If you don’t do anything, Microsoft will process all mail flow rules that currently applies OME protection to Microsoft Purview Message Encryption protection. With this change, recipients will receive a much more customizable notification mail.
Retirement of OMEv1 is coming in 2 phases
on June 30th OMEv1 mail flow rules become read-only or delete-only. No new rules or rule modifications will be allowed. These rules will be encrypt/decrypt with OMEv1
mid-January 2024 (previously) the OME v1 mail flow rules will be fully retired. All the OMEv1 rules will be automatcially process as OMEv2
For customers who need an exception to do OMEv1 mail flow rule updates between June 30th and Dec 31st, open a support ticket to request the exception.
Finally, we recommend all customers that use OMEv1 to receive email into a shared mailbox we highly recommend requesting the exception. We are targeting to release additional changes in Q3CY23 that will improve the shared mailbox experience.
How this will affect your organization:
Microsoft Purview Message Encryption is a more secure and flexible solution to provide encrypted mail to anyone inside or outside your organization, with an enhanced user experience for recipients. For example, with OME, all recipients receive an HTML attachment to open an encrypted mail. This has been greatly improved with Outlook clients for Microsoft 365 users who can now view the message inline. Non-Microsoft 365 users will instead receive a linked-based experience to open the mail. Additionally, supported attachments are also encrypted on download to protect sensitive data at rest.
The behavioral differences and different types of recipients are described in the following table.
*The encrypted attachments provide extra security by protecting the stored file at rest. Applications that can open Office documents may not be compatible with RMS protected Office documents. Admins can provide the same behavior as OME by enabling a global configuration to download Encrypt-only attachments without encryption: Set-IrmConfiguration – DecryptAttachmentForEncryptOnly $true
**By modifying existing the mail flow rules to apply Purview Message Encryption protection, external M365 recipients will receive encrypted mail containing a message.rpmsg attachment and supported Outlook clients can provide show the mail content directly in the application.
What you need to do to prepare:
If you want to compare the behavior before the deprecation, you can modify and test the changes with your mail flow rules by following the steps outlined in this documentation: Define mail flow rules to use Microsoft Purview Message Encryption
Learn more: How Microsoft Purview Message Encryption works
MC669740 — (Updated) Microsoft Purview Information Protection Tracking and Revocation – End-User Tracking and Revocation
TBD
This change is associated with Microsoft 365 Roadmap ID 164210
Updated December 7, 2023: After review we have determined that we will not proceed with this rollout at this time. This has been rolled back from the limited number of customers that received it. When we are ready to proceed we will communicate the new timeline via Message center. Thank you for your patience.
From the sensitivity menu, owners of Office files protected with a sensitivity label can access the Microsoft Purview compliance portal to view user access attempts and revoke access if needed.
When this will happen:
When we are ready to proceed we will communicate the new timeline via Message center.
How this will affect your organization:
The Microsoft Purview Information Protection Tracking and Revocation feature will be turned on by default. To disable the feature, use the Disable-AipServiceDocumentTrackingFeature commandlet.
What you need to do to prepare:
There is no action needed to prepare for this change. You may want to notify your users about this change and update any relevant documentation as appropriate.
MC668524 — (Updated) Microsoft Purview Information Protection: Tracking and Revocation in Compliance Portal
TBD
Microsoft 365 Roadmap ID 152126
Updated December 7, 2023: After review we have determined that we will not proceed with this rollout at this time. This has been rolled back from the limited number of customers that received it. When we are ready to proceed, we will communicate the new timeline via Message center. Thank you for your patience.
Users can access the Microsoft Purview compliance portal to check who has tried accessing their sensitivity labeled and encrypted local Office files and revoke access when needed.
When this will happen:
When we are ready to proceed we will communicate the new timeline via Message center.
What you need to do to prepare:
The Microsoft Purview Information Protection Tracking and Revocation feature will be turned on by default. To disable the feature, use the Disable-AipServiceDocumentTrackingFeature commandlet.
MC649937 — (Updated) Outlook: Support Pop-up Messages in Outlook that Warn/Justify/Block Emails being sent with Sensitivity Labels
Rolled Out
Microsoft 365 Roadmap ID 139754
Updated December 11, 2023: We have updated the rollout timeline below. Thank you for your patience.
Outlook for desktop native sensitivity labeling will support the oversharing pop-up dialogue to warn, justify or block emails being sent.
When this will happen:
Rollout will begin in late October 2023 (previously early September) and is expected to be complete by late December 2023 (previously late November).
How this will affect your organization:
When enabled by the admin, Outlook will use the values set on the Purview portal to show Pop-up messages that warn, block or request for an explicit acknowledgement/ justification from users when they attempt to send email messages that include a sensitivity label on the email or attachment.
Furthermore, based on the customization Outlook will show a “learn more” URL to ensure that end users receive valuable guidance on the rule that initiated the display of the pop-up.
What you need to do to prepare:
Configure policy tips for Data Loss Prevention in the Microsoft Purview compliance portal:
Microsoft Purview compliance portal for GCC cloud environments
Microsoft Purview compliance portal for GCC-High cloud environments
Microsoft Purview compliance portal for DoD cloud environments
Learn more:
Learn how to configure a DLP rule with oversharing popups: Create and Deploy data loss prevention policies
View the AIP migration playbook: Migrate Oversharing Popups from AIP
Exchange Online / Microsoft Defender for Office 365
MC700934 — Global Address List updates in New Outlook for Windows and Outlook on the Web
>60 Days
Microsoft 365 Roadmap ID 185475
We are making some adjustments to the GAL search and browse experiences in New Outlook and Outlook on the web. Users will be asked to type in more characters to refine their search in some cases.
When this will happen:
Standard Release: This is currently rolling out and expected to complete it within the next few months.
How this will affect your organization:
Users will be asked to type in more characters to refine their search in some cases. There will be some other visual improvements in error messaging. Another way to find recipients is by using the suggestion dropdown picker in the To/Cc/Bcc lines. We will continue our investments in the latter for both New Outlook and Outlook on the Web.
What you need to do to prepare:
We recommend you start communicating the change to users across your organization. Microsoft will publish content support on the changes for all users to better understand what is changing.
MC700037 — Outlook for iOS: High and Low importance
<30 Days
Microsoft 365 Roadmap ID 185704
You can now send email with High or Low importance from Outlook for iOS just like you can on Outlook for Windows and Web. You can find the Importance button in the command bar when drafting an email, and you can set the importance level to High, Normal, or Low.
When this will happen:
We will begin rolling out to production environments in mid-December 2023 and expect to complete in mid-January.
What you need to do to prepare:
There is no action needed to prepare for this change. You may want to notify your users about this change and update any relevant documentation as appropriate.
MC698422 — Microsoft 365 Icon Update in Outlook for iOS
Rolled Out
The Office 365 logo will be replaced throughout Outlook Mobile for iOS with the Microsoft 365 logo, as will references to the account type.
When this will happen:
Standard Release: We will begin rolling out mid-December 2023 and expect to complete by late December 2023.
How this will affect your organization:
When this update rolls out, users may see their account represented with the updated icon in their accounts list as well as in other areas of the app.
What you need to do to prepare:
You may want to notify your users about this change and update any training documentation as appropriate.
MC698146 — Microsoft Defender for Office 365: Update of blocked transport rule count volume in Mailflow status report
Rolled Out
We are updating the aggregate count volume of blocked transport rule emails in Mailflow status report.
When this will happen:
Standard: starting mid-December 2023
Government: starting late December 2023
How this will affect your organization:
Previously, the aggregate count of Transport rule email blocked that was shown in the Mail flow status report included the count of all filtered email that matched a transport (not necessarily blocked by the transport rule it matched)
We are updating this behavior to ensure that aggregate count of Transport rule emails blocked actually represent the total volume of emails that match a transport rule and was blocked by that transport rule.
What you need to do to prepare:
As a result of this change, Admins will notice a reduction in the volume of emails that are blocked by transport rules which is shown in the Mail flow status report. This reduction is expected.
The purpose of this communication is for awareness. Admins should also update their training documentation as they see fit.
MC696850 — Microsoft Defender for Office 365 enable admins to provide intent while submitting
<30 Days
Microsoft 365 Roadmap ID 183907
This applies to customers with Exchange Online Protection, Microsoft Defender for Office plan 1 or plan 2 service plans.
Soon, admins can provide intent when submitting messages (email and Microsoft Teams), email attachments, or URLs to Microsoft.
Admins can convey whether they are submitting for a second opinion from Microsoft or they are submitting because a true malicious message was missed by Microsoft. With this change, Microsoft analysis of admin submitted messages (email and Microsoft Teams), URLs, and email attachments will be further streamlined and will result in more accurate analysis.
When this will happen:
This change will start rolling out in mid-December 2023 and should be complete by mid-January 2024.
How this will affect your organization:
You will see this experience when you start making new admin submissions from Submissions, Threat Explorer, or Quarantine.
What you need to do to prepare:
This new feature will not impact any existing submissions, filtering, or grouping functionality in submissions.
Note: Today, end user reporting and admin submission of Teams messages is available only in Microsoft Defender for Office plan 2.
MC692461 — (Updated) Outlook: Update to Play My Emails
<30 Days
Updated December 11, 2023: We have updated the rollout timeline below. Thank you for your patience.
Play My Emails is a feature in Outlook Mobile that allows users to listen to new messages in their Focused Inbox and changes to their day hands-free through a voice-driven experience.
When this will happen:
We will begin rolling out the update in early January 2024 (previously early December) and expect to complete by late January 2024 (previously early January).
How this will affect your organization:
After this update, Play My Emails will no longer attempt to prioritize which messages are read out first. Messages will be read out solely based on chronological order.
What you need to do to prepare:
You may want to notify your users about this change and update any relevant documentation as appropriate.
MC692016 — (Updated) Outlook: Track Read Receipts within Outlook on the Web and the New Outlook for Windows
>60 Days
Microsoft 365 Roadmap ID 184504
Updated December 15, 2023: We have updated the rollout timeline below. Thank you for your patience.
We’re developing the ability to view the updated Read Receipt status of recipients from the sent item directly.
When this will happen:
Standard Release: We will begin rolling out early January 2024 and expect to complete by early February 2024.
GCC: We will begin rolling out early February 2024 and complete by early March 2024.
How this will affect your organization:
When the feature becomes available to you, you will be able to find entry points to the Track Read Receipts view on messages in your Sent Items folder.
What you need to do to prepare:
You may want to notify your users about this change and update any relevant documentation as appropriate.
MC690173 — (Updated) Microsoft to stop honoring mail flow rules tracking user reporting
<30 Days
Updated December 11, 2023: We have updated the content below for clarity. Thank you for your feedback.
Microsoft will stop honoring the mail flow rule which helps you track end user reporting. To improve the availability and reduce the latency of the submission service so that you can respond to threats (false negatives) more quickly and efficiently, we moved the submission service ahead of the exchange transport rule agent. Now the mail flow rules (or exchange transport rules) which you have for the following addresses – phish@office365.microsoft.com, junk@office365.microsoft.com, not_junk@office365.microsoft.com, phish@senpluspluseop.onmicrosoft.com, unjunk@senpluspluseop.onmicrosoft.com and junk@senpluspluseop.onmicrosoft.com won’t be honored as the agent won’t be receiving signals for these addresses.
Moreover, the message tracking logs will show that reports going to phish@office365.microsoft.com, junk@office365.microsoft.com and not_junk@office365.microsoft.com as deleted or failed.
For example: [{LED=550 4.3.2 QUEUE.TransportAgent; message deleted by transport agent};{MSG=};{FQDN=};{IP=};{LRT=}]. Please ignore it as it is by design while we look for a better way to address it.
When this will happen:
We’ll be gradually rolling this out to customers starting late December 2023 and the roll out will be completed by late January 2024.
How this will affect your organization:
You will no longer be able to track end user report using mail flow rules for the following addresses – phish@office365.microsoft.com, junk@office365.microsoft.com, not_junk@office365.microsoft.com once the change is implemented.
What you need to do to prepare:
If you are routing report messages to a mailbox, we recommend going to user reported settings and under “reported message destinations”, setting the “send reported messages” to “My reporting mailbox only” and then providing the mailbox address you are routing to. Distribution groups and routing to an external or on-premises mailbox aren’t allowed.
If you are routing report messages to a mailbox for a particular report type, take the above step and create rules in the mailbox using the outlook client. You can specify which report “phish” or “junk” or “not junk”, you want to be ignored and filtered from your view. The report type is specified in the subject of the notification email sent to the mailbox (1| for Junk, 2| for Not junk, 3| for Phishing).
If you are concerned that your phish simulations will get analyzed by Microsoft, please add the third party phish simulation tool as phish simulation under advanced delivery. With this change, the phish simulation will get delivered unfiltered and on user report, it won’t be analyzed by Microsoft. It will even show up as a phish simulation in the user report tab of submissions.
If you are using exchange transport rule to forward phish simulation from user report to third party tool, we recommend going to user reported settings and under “reported message destinations”, setting the “send reported messages” to “Microsoft and My reporting mailbox only” or “My reporting mailbox only”. Then provide a mailbox address you want the user report to route to (not the third party mailbox). Distribution groups and routing to an external or on-premises mailbox aren’t allowed for this address. Now you configure an exchange transport rule which forward phish simulation coming to this mailbox address to the third-party tool.
If you are routing report messages to Microsoft via a custom add-in or another mechanism, we recommend either using the report button in Outlook for web or the report message add-in or the report phish add-in as described here.
MC684892 — (Updated) Control Inbox and Calendar Sharing Options in Outlook on the Web and in the New Outlook for Windows
Rolled Out
Microsoft 365 Roadmap ID 182261
Updated December 11, 2023: We have updated the content below to show as intended. Thank you for your feedback.
Outlook on the Web and the new Outlook for Windows provides users with the ability to share mail and calendar with other users at different permission levels.
Starting in November 2023, tenant admins will be able to turn off the ability for users to share inbox and calendar folders by utilizing the new Office Cloud Policy Service “Turn off sharing recommendation.”
When will this happen:
The rollout for this feature will begin in early November 2023 and we expect to complete by late November 2023.
How this affects your organization:
This feature matches the existing capabilities available in Outlook for Windows (Win32).
When this policy is turned on, users will be able to block future sharing of inbox and calendar folders in OWA.
Existing users that have been granted permissions to the inbox and calendar will not be affected.
If admins wish to continue to allow users to delegate their inboxes and calendars, no action is necessary.
This capability is only active when the policy is turned on.
What you can do to prepare:
You may consider updating your training and documentation as appropriate.
For more information on applying Cloud policy, please visit: Overview of Cloud Policy
For more information on sharing policies in Exchange Online, please visit: Sharing Policies in Exchange Online
MC676125 — Instructions to avoid opening safelinks to Office documents on SharePoint or OneDrive from Outlook email in read only
<30 Days
Updated December 13, 2023: We have updated the rollout timeline below. Thank you for your patience.
The ability to click on Safe Links from an Outlook message and open Office files hosted in OneDrive or SharePoint Online directly into Microsoft 365 Apps for Windows will require Version 2108 (SEC) or later. Devices running versions older than Version 2108 (SEC) will open the document in the Microsoft 365 Apps in read only mode.
When this will happen:
This change will roll out in late October 2023 and complete by late January 2024.
How this affects your organization:
You are receiving this message because our reporting indicates one or more users in your organization are using safelinks and are on a version older than 2108 (SEC).
Impact to administrators
Administrators who manage the deployment of Microsoft 365 Apps should ensure their user devices are updated to at least Version 2108 (SEC). To be fully supported, devices should be updated to the latest supported version for their chosen update channel as listed on Update history for Microsoft 365 Apps (listed by date).
Current Channel: Version 2301 or later
Monthly Enterprise Channel: 2211 or later
Semi-Annual Enterprise Channel (Preview): Version 2202 or later
Semi-Annual Enterprise Channel: Version 2108 or later
For administrators that allow Microsoft to manage their devices through the Microsoft 365 Apps Installation options in the Microsoft 365 admin center, there is nothing to do.
Impact to users
Users with older versions and have the Links Open Right setting enabled in Microsoft 365 apps, will end up in read-only mode when they click on a SafeLink URL contained within an email message in Outlook to open the document, workbook, or presentation.
The Links Open Right setting is available from File > Options > Advanced > Link Handling > Open supported hyperlinks to Office files in Office desktop apps.
When the user’s device opens a document as read-only, the following workarounds are available if the user cannot immediately update their device to Version 2008 or later.
Close and re-open the document from the recently used file list within Excel, Word, or PowerPoint.
In their Outlook settings, uncheck Open supported hyperlinks to Office files in Office desktop apps.
Right click on the URL in the Outlook message, copy the hyperlink and paste into a browser to open the document in the web app.
What you can do to prepare:
Ensure your organization is running Microsoft 365 Apps for Windows Version 2108 (SEC) or later.
MC666613 — (Updated) Local Contacts Search
30-60 Days
Microsoft 365 Roadmap ID 135281
Updated December 13, 2023: We have updated the rollout timeline below. Thank you for your patience.
Users will now have access to a quicker and easier method to search their Outlook Mobile contact list within the app. We are adding a search bar at the top of a user’s in app contact list that will allow users to type the name of a contact to easily find a contact. This search is limited only to the contacts within the Outlook Mobile app, and this feature does not search any device contacts that have not been synced with Outlook.
When this will happen:
Preview: We will begin rolling out mid-September 2023.
Standard Release: We will begin rolling out mid-October 2023 and expect to complete by mid-February 2024.
How this will affect your organization:
There are no added settings or training needed for you as an admin. This feature will work for all users who have access to and/or use contacts in Outlook Mobile.
What you need to do to prepare:
There is nothing required to prepare.
Microsoft 365
MC698136 — Retiring Delve Web
>60 Days
We will be retiring Delve on December 16th, 2024. Most of the features and value offered by Delve today are already available and improved in other experiences in Microsoft 365. The main one being Profile Cards in Microsoft 365. Here is a list of features offered in Delve and the experiences we recommend using instead:
Delve Home – discover relevant documents recommended on Office.com, in Office apps and in Profile Cards.
Delve Profile – view profile data in the Profile Cards cross M365, through people in search on Office.com and search in SharePoint.
Edit profile – a new edit profile experience tightly coupled with Profile Cards are being developed and will be released in second half of 2024. It is also possible for users to edit their profile data in the SharePoint profile edit experience (editprofile.aspx).
Organizational view – exists in the Profile Card and as a dedicated experience in Org Explorer
Favorites – favorites on Office.com and OneDrive is not connected to Delve and is a good option for users with similar functionality and improved availability.
Boards – will not be replaced.
When this will happen:
December 16, 2024
How this will affect your organization:
You are receiving this message because Delve web is available to most customers in Microsoft 365. The number one feature offered in Delve is the ability for users to update their profile properties, and this will be replaced with a new dedicated profile editing experience in the second half of 2024. Please note that Delve and the new edit profile experience will work side by side until Delve is retired.
Users will no longer be able to create new boards, add documents to existing boards, view boards or search for boards when this change is implemented. Please note that documents themselves will NOT be removed. It is only the association with one or multiple boards that will be removed.
We will soon enable banners in Delve, letting users know that the feature will be retired and link to suggested alternatives.
The new edit profile experience will for now read and write to the same source as Delve does, thus there are no changes in how admins can modify user profile properties.
What you need to do to prepare:
We recommend updating internal documentation and training related to Delve with the suggested alternatives. When the new edit profile experience is available this will also need to be shared broadly and documentation updated. We will make sure that the new edit profile experience is easy to access and easy to use and that there is public documentation in place before releasing.
Please click additional information to learn more about existing alternatives.
Profile cards in Microsoft 365
“For you” recommendation in OneDrive
Favorites in OneDrive
Org Explorer (requires Viva license)
Using search efficiently for organizational content
MC696575 — (Updated) Action Required – Changes to Get & Transform Data (aka Power Query) features in Excel
>60 Days
Updated December 11, 2023: We have updated the content below to show as intended. Thank you for your feedback.
We will be making changes to Get & Transform Data (aka Power Query) features in Excel.
Note: If you don’t use Power Query, you may dismiss this message.
When this will happen:
Starting March 11th, 2024, we will be introducing important changes to the Get & Transform Data (aka Power Query) features in Excel.
How does this affect your organization:
Any user who tries to use Power Query after March 11th, 2024, and falls under one of the scenarios, below, will receive a relevant error message.
As we are modernizing the Get & Transform Data (aka Power Query) experience in Excel for Windows, some of the Get & Transform Data capabilities will require Microsoft Edge WebView2 (Microsoft Edge WebView2 | Microsoft Edge Developer) to be installed on the client machine. In the future, all the Get & Transform Data features in Excel for Windows will require Microsoft Edge WebView2 hence we recommend installing this library now.
In addition, and to provide the best-in-class encryption to our customers, we are planning to deprecate the support of TLS (Transport Layer Security) 1.1 or lower in Get & Transform Data (aka Power Query) on all platforms. If a certain external data source a user tries to connect to only supports TLS version 1.1 or lower, they will not be able to access the relevant data source via Get & Transform Data tools in Excel.
What you need to do to prepare:
You will need to:
Install Microsoft Edge WebView2 run-time for upcoming Get Data features.
Ensure all of the external data sources you use with Power Query support TLS version 1.2 or higher – for Power Query, in general.
Please Inform your helpdesk and update documentation as appropriate.
For additional information, please refer to:
About Get & Transform (Power Query) in Excel
Preparing for TLS 1.2 in Office 365 and Office 365 GCC | Microsoft Learn
How to enable Transport Layer Security (TLS) 1.2 on clients – Configuration Manager | Microsoft Learn
MC690608 — App name change for Microsoft Project for the web, Project Teams tab, and Project Power app to “Planner (Project)”
TBD
Updated December 11, 2023: We have made the decision not to proceed with this change at this time. We will communicate via Message center when we are ready to proceed. Thank you for your patience.
We are updating the app names for Project for the web, Project Teams tab, and Project Power app to “Planner (Project)” – all existing functionality across these apps will remain the same.
When this will happen:
We will communicate via Message center when we are ready to proceed.
How this will affect your organization:
We are updating the app names for Project for the web, Project Teams tab, and Project Power app to “Planner (Project)” – all existing functionality across these apps will remain the same.
A dismissible banner will appear in the app before the name change to set user expectations and a new banner will appear once the name change occurs to inform users.
We don’t expect this change to impact any existing user scenarios or functionality.
This name change aligns these apps with the roadmap and Ignite announcement of the new Planner app. The new Planner app will bring together your to-dos, plans, and projects into a single unified experience which is simple, flexible, scalable, and intelligent. Existing Project for the web customers will get access to the premium capabilities in the new Microsoft Planner app as part of their Project for the web subscriptions, with no additional licenses required.
You can find out more information about the new Planner here: Planner Blog
Project Server, Project Online, and Project Desktop client are not subject to this name change.
What you need to do to prepare:
Your organization should update any internal documentation for Project for the web, Project Teams tab, and Project Power app which references the previous app name “Project” to use the new app name “Planner (Project)”. Otherwise we do not expect any other preparation is needed.
MC664477 — (Updated) See your Recent Microsoft Planner plans and Microsoft To Do Lists on Microsoft 365 Homepage
30-60 Days
Microsoft 365 Roadmap ID 149272
Updated December 11, 2023: We have updated the rollout timeline below. Thank you for your patience.
Currently, you cannot see your recently accessed Planner plans or Microsoft To Do lists in your Microsoft 365 homepage. With this update, you will be able to see and access all your recent plans and lists alongside your Microsoft Project for the web projects, Word documents, PowerPoint decks, and more on office.com.
When this will happen:
This update will begin rolling out in late January 2024 (previously early November) and is expected to be completed by late February 2024 (previously late November 2023).
How this will affect your organization:
With this update, your organization’s plans and lists will be visible from the office.com home page as opposed to solely from Planner and Microsoft To Do apps. This means you will be able to open your plans and lists directly from the Microsoft 365 homepage, just as you are able to open your Project projects, Word documents, Excel sheets, and all other Microsoft Office files.
What you need to do to prepare:
There is no action required to prepare for this change. Plans and lists for users in your tenant will begin to appear on the Microsoft 365 homepage as soon as the rollout reaches your tenant.
MC517336 — (Updated) Microsoft Visio Viewer on iOS Retirement
<30 Days
Updated December 11, 2023: We have updated the timing of this change below. Thank you for your patience.
Microsoft Visio Viewer app on iOS will be retired and removed from the App Store and will no longer work on iPhones and iPads.
When this will happen:
late January 2024 (previously mid-November)
How this affects your organization:
Once the Visio Viewer iOS app is discontinued, users will no longer be able to download the app from the iOS app store.
As a substitute, users can view their drawing in Visio for the web. Just save a file in OneDrive or SharePoint to be able to open it in the web app.
What you can do to prepare:
You may consider updating your training and documentation as appropriate.
Transitioning from the Visio Viewer app on iOS to Visio for the web is easy. To learn more about which browsers work with Visio for the web, or how to view and comment on diagrams created with a Visio Plan 1 or Visio Plan 2 subscription, visit Visio for the web FAQ.
Microsoft 365 IP and URL Endpoint Updates
Documentation – Office 365 IP Address and URL web service
Microsoft Tech Community – Latest Blogs –Read More
Concurrency support for Service Bus built-in connector in Logic Apps Standard
Concurrency Support for Service Bus (Logic Apps Standard)
If you are interested to learn about other Service Bus enhancements, refer to these articles: Session support for Service Bus
Concurrency support in Logic Apps refers to the capability of running multiple runs concurrently for a workflow. Logic Apps provide built-in features to support concurrency, allowing you to design workflows that can execute multiple runs simultaneously. By default, Logic Apps would always try to run things in parallel to the maximum extent.
While this is great for most scenarios, in many cases, users want to have control on the concurrency. Concurrency control is important for several reasons, primarily related to managing resources, avoiding performance bottlenecks, not overwhelming backend systems and ensuring the efficient execution of workflows.
Concurrency control is available for triggers and actions. In this blog post, we’ll talk about how you can use concurrency control with Service Bus built-in connector in Logic Apps Standard. This feature is only available in code-view at the moment but the designer support is planned. [Until this feature is available in designer, if you make changes to code view we recommend to stay in the code view as you may loose these changes if you switch to designer view]
Key concepts
Before we go into the specifics, here are the three properties that are important for concurrency control.
Concurrency control and Degree of Parallelism. The concurrency control property is used to enable concurrency control. The degree of parallelism by default is set to 20 and can be set to any value from 1 to 100
Maximum batch size (Maximum message count) . The Maximum batch size property is used to specify the number of messages to be processed in a single batch. The trigger reads the batch of messages as specified in this property
Split On . The split on property is used to enable the split on feature. When enabled, the items read by the trigger are split resulting in a separate run for each item. For example, if you have a batch size of 50 and split on enabled, then 50 runs would start and each run will process one item from that batch. If split on is disabled, only 1 run will process the 50 items.
Enabling concurrency control for Service Bus built-in or InApp connector
To enable concurrency control for Service Bus built-in connector (aka In App connector), you need to follow these steps. Please note that in future, these capabilities will be available in designer but for now you need to configure them through code view
Update workflow settings through code view
Create a new workflow and use Service Bus trigger or open your existing workflow with Service Bus trigger
Open the workflow in code view. Add the runtimeConfiguration section to the workflow definition. In the runtime configuration, add the concurrency and set the runs to the desired concurrency. Here is an example workflow:
The the split on settings are enabled by default and can be disabled if you do not want to split the batch and process all messages read in the batch in a single run.
Update host.json through code view
Until the feature becomes available through designer, you also need to update batch setting in host.json file. To open host.json file, open your Standard Logic Apps, and select under Development Tools : Advanced Tools > Go > Debug console > CMD. In the file system open, sitewwwroot. You can update host.json using the command line or Edit button.
Update these two properties in host.json
Currently this feature is behind a flag. To opt into this capability, you need to set the flag to true. In the host.json, set Runtime.ServiceProviders.FunctionTriggers.ConcurrencySupported to true
Maximum messages batch size – The maxMessagesBatchSize property specifies the number of messages that are being read from the service bus queue or topic. The higher the number, the more messages will be read and processed in parallel. We recommend you choose this number based on the limits of your downstream systems. If you have used managed Service Bus connector in Logic Apps (consumption or ISE) before, you may find this field similar to Maximum message count property in the existing connector.
Note: As you configure batch size, we recommend to keep the number of concurrent runs larger than the overall batch size so that the messages read do not go in the waiting state and are always picked as soon as they are read. It is also possible in some cases for the trigger to reach upto twice the batch size.
Here is an example of host.json with concurrency enabled:
You are now ready to use the Service Bus trigger with concurrency enabled. In the next section, we’ll attempt to answer questions regarding some advanced use cases or related configurations.
FAQ
What are other configurations available or important for the connector
The Service Bus connector leverages function bindings. You can refer to these settings and defaults for more information.
How does split on limits work with concurrency limits
When concurrency is enabled, split on limit is reduced to 100 items. This is true for all triggers including Service Bus trigger
Microsoft Tech Community – Latest Blogs –Read More
Advanced Monitoring for PostgreSQL Using Log Analytics
Monitoring your database resources is critical to being able to detect issues or opportunities for improvements. When it comes to Azure Database for PostgreSQL Flexible Server, the monitoring story can be a bit overwhelming with multiple different services seeming to offer similar. There is often discussion between two services, Azure Monitor Metrics, and Azure Log Analytics . In this blog post, we are going to look at these two services and when you would use them. Let us start by looking at what these services do.
Azure Monitor metrics
Azure Monitor is a comprehensive solution for collecting, analyzing, and alerting time-series metrics from services like Azure Postgres Flexible Server. It helps to understand how service is performing and proactively identifies issues affecting them and the resources they depend on. For monitoring Azure Database PostgreSQL Flexible Server, we have over 60 metrics for monitoring various database aspect including resource utilization, database activity, replication, saturation, connections etc. Azure monitor is a provides powerful tools for the collection, visualization, and alerting the time series data. To learn more, refer Azure Monitor Metrics overview .
Azure Log Analytics (LA)
Azure Log Analytics is a service that monitors cloud resources and applications. It allows you to collect and analyze logs generated by resources in your cloud and on-premises environments. Azure Log Analytics is a service that provides advanced analytics capabilities and the aggregation of log data. Log analytics will collect and store your data from various log sources and allow you to query over them using a custom language called Kusto Query Language (KQL).
While Azure Monitor metrics focuses on time series data such as performance and resource usage metrics, Azure Log Analytics offers more complex querying and log data analysis. It is especially useful for long-term trend analysis and combining data from multiple sources to gain deeper insight into operations and performance across Azure services. To learn more, refer Overview of Log Analytics in Azure Monitor.
Combining Metrics with Log Analytics
For single-instance monitoring and troubleshooting, Azure Monitor metrics is the go-to tool. Say, if you are having a slowness issue with a database server and you want to go and look at its CPU utilization, you can do this through Azure Monitor metrics using the portal and generate some great charts to learn what is happening now. Also, you can pin this chart to the Azure dashboard and Use the Azure portal to set up alerts on metrics for a specific resource. When debugging a specific issue on a small number of instances Azure monitor is great and will do exactly what is needed.
For complex monitoring tasks across numerous Azure PostgreSQL instances, Azure Log Analytics offers extensive data monitoring capabilities. This becomes invaluable when managing large server fleets, such as analyzing memory usage across 100 servers. With Log Analytics, data from all servers can be consolidated into a single log analytics workspace. This enables comprehensive visualization and alerting using the Kusto Query Language (KQL), simplifying what would otherwise be a daunting task of individually analyzing each server. This approach highlights Log Analytics’ strength in handling large-scale, detailed data analysis scenarios.
As with Azure Monitor, we can pin these LA charts to Azure Dashboard. You can also configure alerts, but again we now only need one alert for multiple resources, and it will trigger when one or more breaches the threshold, rather than requiring an alert per resource. By sending Azure monitor metrics to Log Analytics you also gain more functionality:
Monitoring at scale – Consolidate log entries from multiple Azure subscriptions and tenants.
Long-term analysis – Log analytics offers retention for up to 2 years.
Metrics correlation – We can query multiple different metrics and display them together to look for correlation.
Complex queries – Log analytics leverages Kusto query language which can be used to undertake complex queries over large data series.
Query other data – Azure monitor is obviously focused on timeseries metrics, versus with Log Analytics you can collect any sort of log data, including custom logs.
Combining Azure Monitor metrics and Azure Log Analytics offers a comprehensive monitoring solution. Azure Monitor provides real-time insights for individual instances, while Log Analytics offers depth for multiple instances. Azure monitor metrics data is stored in AzureMetrics table that holds metrics for all Azure resources. Once the metrics are enabled in the diagnostic settings for a resource, information is stored in this table. In the example below, I am using the below Kusto query on AzureMetrics table to visualize cpu_percent across a fleet of Azure Postgres Flexible Server Instances.
Create a Log Query Alert for Monitoring CPU metrics
Metrics data in a Log Analytics workspace is stored in a table called AzureMetrics that you can retrieve with a log query in Log Analytics. The structure of this table varies depending on the category of the log entry. For a description of the table properties, see the AzureMetric data reference. For a complete lists of metrics available for Azure Postgres, refer Supported Metrics.
For example, to view a count of metrics log records for each resource, use the following Kusto query.
AzureMetrics | summarize count() by Resource
To retrieve all metrics in the specific Azure Postgres Resource
AzureMetrics | where Resource == “VARUND-QPI-DEMO”
To set up a log query alert for monitoring CPU usage across fleet of Azure PostgreSQL servers, you start by selecting a prebuilt log query or creating one using Kusto Query Language (like one above). This query should leverage cpu_percent metrics from your Azure resources.
Sample Kusto Query
//KQL to visualize average cpu percent for multiple Flexible Server instances across multiple regions
AzureMetrics
| where TimeGenerated > ago(30m) //Filter for the last 30 minutes
| where ResourceProvider == “MICROSOFT.DBFORPOSTGRESQL”
| where MetricName == “cpu_percent”
| where ResourceId contains “FLEXIBLESERVERS” //Filter for ResourceId containing “FLEXIBLESERVERS”
| extend LocalTimeGenerated = datetime_utc_to_local(TimeGenerated, “US/Central”) // Convert to local time
| project LocalTimeGenerated, Resource, Average
| summarize AvgCpuUsage = avg(Average) by LocalTimeGenerated, Resource
| render timechart
Output
After verifying the query’s results, proceed to create an alert rule in the Azure portal. Key steps involve:
Configuring the condition based on the log query results.
Setting alert logic with appropriate thresholds for CPU usage (e.g., alert if CPU usage is greater than 60%).
Choosing an action group for notifications (email, SMS, etc.).
Finalizing alert details like name, description, and severity.
When an alert fires, it sends notifications in its action groups. You can also view the alert in the Azure portal.
For detailed steps, refer to the Tutorial: Create a log query alert for an Azure resource.
Some things to consider when using Log Analytics
While Log Analytics offers comprehensive data analysis, it is important to note some key considerations:
Data Ingestion and Alert Delay: The average latency to ingest log data is between 1 minute and 5 minutes. The specific latency for any data will vary depending on several factors that can cause delays in alert triggering compared to Azure Monitor’s near real-time alerts. For details, refer Log data ingestion time.
Additional Costs: Azure Log analytics cost is based on two plans: Basic Logs, currently free for search but with future billing to be announced, and Analytic Logs, offering Pay-As-You-Go (first 5 GB/month free) and Commitment Tiers (discounted rates starting at 100 GB/day with a 31-day commitment period, with overage billed at the tier rate). For details, refer Azure monitor logs pricing.
Log Analytics data ingestion strategies
So hopefully now it is clear that Azure Monitor is the service to aggregate the time series metrics from the Azure resources, and Log Analytics is the service to aggregate logs, and can be used if you want to monitor multiple Azure Postgres resources. Given this, the question is How do we get that data into Log Analytics. Fortunately, Azure Monitor comes with options for exporting metrics data. For PostgreSQL Flexible Server you have the ability to export logs data to following logging destinations:
A storage account.
An Event Hub.
A Log Analytics Workspace.
This can be configured through the portal, underneath the diagnostic settings tab for the resource you want to configure. In here you configure which of the 3 destination you want to send the data too and then what data you want to send. This will usually include options for both Logs and Metrics, and often the metrics option will just be “All metrics” which as the name suggests, sends all metrics that are available for that service. Below are the options for Azure database for PostgreSQL Flexible Server.
It is important to note that a single Log Analytics workspace can monitor resources across multiple subscriptions as long as they are under the same Tenant. For example, if you have an Azure PostgreSQL database in Subscription A and Log Analytics Workspace in Subscription B, you can send the logs and metrics from that PostgreSQL database to the Log Analytics workspace.
Conclusion
For large enterprises, the combination of Azure Monitor and Log Analytics forms a robust solution for monitoring Azure Database for PostgreSQL Flexible Server ‘at scale.’ This integrated approach is critical for monitoring a vast array of Azure resources through a single pane of glass, ensuring not just immediate issue resolution but also facilitating long-term, strategic oversight across the entire enterprise infrastructure. This strategy enhances both performance and reliability, aligning with the needs of large-scale, complex deployments.
Microsoft Tech Community – Latest Blogs –Read More
How to get started with Microsoft technology grants and discounts for nonprofits
A woman smiles while working outside with volunteers
Microsoft Tech for Social Impact is dedicated to providing affordable and accessible technology to help nonprofits of all sizes achieve their mission. That’s why we offer grants and discounts for our products and services to eligible nonprofits around the world, including solutions like Azure, Dynamics 365, and Microsoft 365, as well as solutions custom-built for nonprofits like Fundraising and Engagement for Dynamics 365 Sales. Get started with free technology grants and discounts today.
What are the most popular nonprofit grants and discounts?
Improve cybersecurity, reduce costs, and empower staff and volunteers to work from anywhere with Microsoft 365 and Microsoft Teams. Free for up to 10 users and discounted pricing of $5.50 (USD) per user/month for additional users.
Move to the cloud with the Azure grant for nonprofits. Leverage $2,000 (USD) Azure services credits per year and access the complete portfolio of Azure products and cloud services.
Easily develop mobile and web apps to support your mission—even if you have no technical or development experience. Power Apps is now free for up to 10 users with discounted pricing of $2.50 per user per month for additional users.
In addition to nonprofit grants, nonprofits of all sizes and stages of application are invited to participate in the Nonprofit Community to connect with Microsoft experts, partners, and fellow nonprofits, where you’ll receive peer support, learning resources, mentoring, and funding opportunities.
What are the eligibility criteria for Microsoft nonprofit grants and discounts?
Review the eligibility criteria:
Nonprofits Grants & Credits Eligibility | Microsoft Nonprofits
Where to get started
The application process is simple and the form only takes 10 minutes. Follow these steps:
Start with our quick pre-check to confirm your nonprofit’s eligibility Nonprofit offers (microsoft.com)
Once you’ve completed the pre-check, apply for nonprofit grants and discounts.
Wait for the confirmation email from Microsoft and follow up with any additional information or clarification that may be requested.
Microsoft is not only a grant provider, but also a partner and ally in your social impact journey. Don’t hesitate to reach out to the Nonprofit Community for any questions, feedback, or support that you may need along the way.
Microsoft Tech Community – Latest Blogs –Read More
Windows Server “Ask Microsoft Anything” January 25
This Thursday, January 25 at 9 a.m. Pacific time we’ll be having an Ask Microsoft Anything (AMA) session on Windows Server “v.Next.” Yes, we are hard at work on the next version of Windows Server and our Microsoft program managers, including @Ned Pyle and @Jeff Woolsey among others, will be on the chat to get your feedback and answer your questions.
We’d love to hear from you about:
Your thoughts on the Windows Server features previewed at Ignite
Your feedback on innovations and improvements you’d like to see in future versions of Windows Server
Here is the link to the session, where you can sign up to add it to your calendar. The team is looking forward to chatting with you!
Microsoft Tech Community – Latest Blogs –Read More
Windows Server “Ask Microsoft Anything” January 25
This Thursday, January 25 at 9 a.m. Pacific time we’ll be having an Ask Microsoft Anything (AMA) session on Windows Server “v.Next.” Yes, we are hard at work on the next version of Windows Server and our Microsoft program managers, including @Ned Pyle and @Jeff Woolsey among others, will be on the chat to get your feedback and answer your questions.
We’d love to hear from you about:
Your thoughts on the Windows Server features previewed at Ignite
Your feedback on innovations and improvements you’d like to see in future versions of Windows Server
Here is the link to the session, where you can sign up to add it to your calendar. The team is looking forward to chatting with you!
Microsoft Tech Community – Latest Blogs –Read More
Windows Server “Ask Microsoft Anything” January 25
This Thursday, January 25 at 9 a.m. Pacific time we’ll be having an Ask Microsoft Anything (AMA) session on Windows Server “v.Next.” Yes, we are hard at work on the next version of Windows Server and our Microsoft program managers, including @Ned Pyle and @Jeff Woolsey among others, will be on the chat to get your feedback and answer your questions.
We’d love to hear from you about:
Your thoughts on the Windows Server features previewed at Ignite
Your feedback on innovations and improvements you’d like to see in future versions of Windows Server
Here is the link to the session, where you can sign up to add it to your calendar. The team is looking forward to chatting with you!
Microsoft Tech Community – Latest Blogs –Read More
Windows Server “Ask Microsoft Anything” January 25
This Thursday, January 25 at 9 a.m. Pacific time we’ll be having an Ask Microsoft Anything (AMA) session on Windows Server “v.Next.” Yes, we are hard at work on the next version of Windows Server and our Microsoft program managers, including @Ned Pyle and @Jeff Woolsey among others, will be on the chat to get your feedback and answer your questions.
We’d love to hear from you about:
Your thoughts on the Windows Server features previewed at Ignite
Your feedback on innovations and improvements you’d like to see in future versions of Windows Server
Here is the link to the session, where you can sign up to add it to your calendar. The team is looking forward to chatting with you!
Microsoft Tech Community – Latest Blogs –Read More
Windows Server “Ask Microsoft Anything” January 25
This Thursday, January 25 at 9 a.m. Pacific time we’ll be having an Ask Microsoft Anything (AMA) session on Windows Server “v.Next.” Yes, we are hard at work on the next version of Windows Server and our Microsoft program managers, including @Ned Pyle and @Jeff Woolsey among others, will be on the chat to get your feedback and answer your questions.
We’d love to hear from you about:
Your thoughts on the Windows Server features previewed at Ignite
Your feedback on innovations and improvements you’d like to see in future versions of Windows Server
Here is the link to the session, where you can sign up to add it to your calendar. The team is looking forward to chatting with you!
Microsoft Tech Community – Latest Blogs –Read More
Partner Blog | Grow with Microsoft: unlock new benefits packages and program updates
By Julie Sanford, Vice President, Partner GTM, Programs & Experiences
We are committed to providing the resources and support our partners need to deliver incredible solutions to organizations and communities globally. Today, I’m excited to announce the release of new partner benefits packages, each equipped with in-demand product, support, and advisory benefits and designed to drive partner success.
There are three new distinct benefits packages: Partner Launch Benefits, Partner Success Core Benefits, and Partner Success Expanded Benefits. These packages are purpose-built to meet the varied needs of our partners at different stages of growth and designed to help take your business to the next level. They complement Solutions Partner and ISV Success core and expanded benefits already available for partners.
Benefits packages that meet you where you are
Partner benefits packages represent a holistic approach to partner development. Whether you’re building your first solution or aiming to expand your capabilities, there is a package for you. Partners who want to kickstart their growth can explore the Partner Launch Benefits, which empower you to discover, use, and test Microsoft products. As you expand, the Partner Success Core Benefits offer a more robust set of tools and support. For those who are ready to scale at a larger level, the Partner Success Expanded Benefits provide the most comprehensive range of product benefits and support.
The new partner benefits packages can be purchased individually and in addition to existing benefits, including ISV Success. Beyond these packages, partners are encouraged to differentiate their organizations with a solution area Solutions Partner* designation or specialization. In addition to helping you stand out to your customers in the market, these offerings unlock significantly more Microsoft Azure credits, seats, and technical support.
Click here to continue reading about partner benefits packages
**Be sure to also join our partner benefits discussion board found here**
Microsoft Tech Community – Latest Blogs –Read More
Microsoft and Trevor Noah: A Partnership for Asking Questions
Trevor Noah
How comedian Trevor Noah is helping Microsoft for Nonprofits spark curiosity and innovation in the era of AI
Microsoft believes in the power of questions. Questions can inspire creativity, challenge assumptions, and lead to breakthroughs—that’s why Microsoft named Trevor Noah Chief Questions Officer. Trevor is a keynote speaker at the Global Nonprofit Leaders Summit and brings his curiosity to exploring the future of nonprofits making an impact with AI.
As Microsoft Chief Questions Officer, Trevor uses humor, insight, and curiosity to engage with the future of AI for powering change. With his series “The Prompt,” he explores how technology like AI, cloud computing, gaming, and edtech are driving social impact.
Trevor Noah is a perfect fit for this role because he is a master of asking questions. His passion for learning and innovation combined with a global perspective and sharp wit inspires people to approach AI with curiosity and unleash their potential.
At the Global Nonprofit Leaders Summit, Trevor will join Kate Behncken, CVP of Microsoft Philanthropies, for “Q&AI”, a conversation on the power of curiosity as we meet the challenges and opportunities of AI together. Be sure to register for the event with code VIRTUAL to watch and learn.
For a look at how Trevor brings curiosity to conversations about AI for impact, watch the latest episode of The Prompt, exploring how the Fred Hutchinson Cancer Center is using AI to combat addition with emotional support.
Trevor Noah at the Global Nonprofit Leaders Summit, January 31
Microsoft Tech Community – Latest Blogs –Read More
Partner Blog | Grow with Microsoft: unlock new benefits packages and program updates
By Julie Sanford, Vice President, Partner GTM, Programs & Experiences
We are committed to providing the resources and support our partners need to deliver incredible solutions to organizations and communities globally. Today, I’m excited to announce the release of new partner benefits packages, each equipped with in-demand product, support, and advisory benefits and designed to drive partner success.
There are three new distinct benefits packages: Partner Launch Benefits, Partner Success Core Benefits, and Partner Success Expanded Benefits. These packages are purpose-built to meet the varied needs of our partners at different stages of growth and designed to help take your business to the next level. They complement Solutions Partner and ISV Success core and expanded benefits already available for partners.
Benefits packages that meet you where you are
Partner benefits packages represent a holistic approach to partner development. Whether you’re building your first solution or aiming to expand your capabilities, there is a package for you. Partners who want to kickstart their growth can explore the Partner Launch Benefits, which empower you to discover, use, and test Microsoft products. As you expand, the Partner Success Core Benefits offer a more robust set of tools and support. For those who are ready to scale at a larger level, the Partner Success Expanded Benefits provide the most comprehensive range of product benefits and support.
The new partner benefits packages can be purchased individually and in addition to existing benefits, including ISV Success. Beyond these packages, partners are encouraged to differentiate their organizations with a solution area Solutions Partner* designation or specialization. In addition to helping you stand out to your customers in the market, these offerings unlock significantly more Microsoft Azure credits, seats, and technical support.
Click here to continue reading about partner benefits packages
**Be sure to also join our partner benefits discussion board found here**
Microsoft Tech Community – Latest Blogs –Read More
Partner Blog | Grow with Microsoft: unlock new benefits packages and program updates
By Julie Sanford, Vice President, Partner GTM, Programs & Experiences
We are committed to providing the resources and support our partners need to deliver incredible solutions to organizations and communities globally. Today, I’m excited to announce the release of new partner benefits packages, each equipped with in-demand product, support, and advisory benefits and designed to drive partner success.
There are three new distinct benefits packages: Partner Launch Benefits, Partner Success Core Benefits, and Partner Success Expanded Benefits. These packages are purpose-built to meet the varied needs of our partners at different stages of growth and designed to help take your business to the next level. They complement Solutions Partner and ISV Success core and expanded benefits already available for partners.
Benefits packages that meet you where you are
Partner benefits packages represent a holistic approach to partner development. Whether you’re building your first solution or aiming to expand your capabilities, there is a package for you. Partners who want to kickstart their growth can explore the Partner Launch Benefits, which empower you to discover, use, and test Microsoft products. As you expand, the Partner Success Core Benefits offer a more robust set of tools and support. For those who are ready to scale at a larger level, the Partner Success Expanded Benefits provide the most comprehensive range of product benefits and support.
The new partner benefits packages can be purchased individually and in addition to existing benefits, including ISV Success. Beyond these packages, partners are encouraged to differentiate their organizations with a solution area Solutions Partner* designation or specialization. In addition to helping you stand out to your customers in the market, these offerings unlock significantly more Microsoft Azure credits, seats, and technical support.
Click here to continue reading about partner benefits packages
**Be sure to also join our partner benefits discussion board found here**
Microsoft Tech Community – Latest Blogs –Read More
MFA App ID deprecation in Exchange Online
We wanted to inform you of an important update regarding MFA App ID (Microsoft Exchange Online Remote PowerShell App ID) used in Exchange Online. The MFA App ID (a0c73c16-a7e3-4564-9a95-2bdf47383716) will be deprecated by the end of March 2024. After that date, the App ID will no longer be operational.
What is the MFA app Id?
The MFA App ID is an Azure-based identifier used for authentication purposes to access Exchange Online resources. This App ID was specifically designed for the now-deprecated Exchange Online PowerShell v1 module also called as MFA v1 module, which has been replaced by the more robust Exchange Online v3 module. As the MFA module is no longer supported, and other use of this App ID was never officially documented and recommended by Microsoft, we have decided to proceed with its deprecation. We already made this deprecation announcement in Partner Center during February and August 2023.
Who is impacted by this change?
There are three ways in which you could possibly be impacted by this deprecation:
When you connect to Exchange Online using the Exchange Online PowerShell V3 module’s Connect-ExchangeOnline cmdlet, and you are using the -AccessToken parameter and passing the MFA App ID mentioned above.
You have written an in-house (home grown) app that still uses this App ID. Please check your source code for the presence of this App ID.
If you use a 3rd party app that uses this App ID, your tenant might get a Message Center post about this change. Please check with your 3rd party vendors if they used this App ID.
What you should do.
Although Microsoft never officially recommended the use of MFA App Id, we understand that over the years, some of our partners and customers may have taken dependency on this App ID. If you are currently using the MFA App ID, we urge you to transition away from it as soon as possible to avoid any service disruptions.
To replace the MFA App ID in case you use it, we recommend you start using the v3 PowerShell module without using MFA app id as an access token or create a new Application through the Azure portal, ensuring it has the necessary permissions for your required operations and make use of this newly created app ID to login to Exchange Online. For detailed information about Application Id creation and consumption you can refer to: App-only authentication in Exchange Online PowerShell and Security & Compliance PowerShell | Microsoft Learn.
Have additional concerns?
In case you have any concerns regarding the MFA app ID deprecation, you can reach out to us at MFAAppIDDeprecation(AT)service.microsoft.com.
Exchange Online Manageability Team
Microsoft Tech Community – Latest Blogs –Read More
Vulnerable Components Inventory now in public preview
In recent years, software supply chain vulnerabilities and related supply chain attacks have become a major concern for security teams across industries. As software systems become increasingly complex and software developers rely more on open-source software packages and commercial third-party software components, it has become difficult for security teams to keep track of and mitigate new vulnerabilities found within software being used in their organizations.
To address this challenge, Microsoft Defender Vulnerability Management is introducing a dedicated inventory that lists known vulnerable software components found in the organization. This inventory, along with a new security recommendation, improves visibility of vulnerabilities found within software components, such as open-source libraries. These components are widely used, but often not clearly visible, due to inner dependencies within software products.
By increasing awareness among security teams of vulnerabilities found in software components that are being used by multiple software products within an organization, security administrators can identify affected devices, prioritize, and mitigate risk proactively. Therefore, improving their security posture and reducing the risk of potential cyber-attacks.
The new Vulnerable Components Inventory includes a list of software components that are known to have critical vulnerabilities in the past.
The following is a list of components that are currently supported. A few of these components were previously shown under the ‘Software inventory’ but are now available via the ‘Vulnerable components’ inventory.
Apache Commons Text
Apache Log4j
Apache Struts [newly supported]
LiteDB
OpenSSL
Spring Framework
WebP (libwebp) [newly supported]
Defender Vulnerability Management coverage of software components will continue to expand based on the ever-evolving threat landscape and customer demand. For example, in light of critical vulnerabilities recently found in WebP (CVE-2023-4863)
and Apache Struts 2 (CVE-2023-50164), Defender Vulnerability Management was updated to support both components.
For each vulnerable component you will see basic information including the component name and vendor, the number of weaknesses related to that component and the impact to the overall exposure score, whether an exploit is available, and if there are active threats or alerts associated with it.
The Component page’s tabs provide detailed information and insights:
Data visualizations show the number of, and severity of, vulnerabilities and graphs with the number of installed and exposed devices.
Named CVEs of discovered vulnerabilities.
Devices that have the component installed along with device name, domain, OS, and more).
List of components’ versions, including number of devices the version is installed on, the number of discovered vulnerabilities, and the names of the installed devices.
In addition, a list of vulnerable files found is provided with file paths, version, and associated vulnerabilities, which can be exported for further investigation and handling.
Defender Vulnerability Management provides actionable Security Recommendations to assist security administrators reduce their organization’s exposure to vulnerabilities through the process of keeping their software up to date. Given the inherited complexity of updating a software component within an enterprise environment, the Attention required recommendation is designed to raise awareness of security teams to an emerging threat and explore their next steps, rather than a call for action to update a version, which may not be applicable for a specific software component.
Administrators can also drill down to a specific device and view a list of vulnerable components with the relevant file level evidence details.
Learn more.
If you’re interested in learning more about Microsoft Defender Vulnerability Management visit our website to take advantage of our free 90-day trial, check out our interactive guide, and read more information in our product documentation.
Providing feedback.
As always, we’d love to know what you think. Looking forward to your feedback. share your feedback directly at: mdvmfeedback@microsoft.com
Microsoft Tech Community – Latest Blogs –Read More
New Year, new meeting enhancements in Microsoft Teams
As we head into 2024, the air is filled with resolutions, aspirations, and goals for the new year. As individuals, we strive to better ourselves in the coming year. The Teams product team also strives to make your meetings better. We’re excited to share how Teams is getting better with updates that will help you customize every meeting, present content seamlessly, and enhance meeting efficiency with simplified processes.
Below we’ll take a closer look at how we’re evolving meetings in Teams to deliver new engaging and flexible controls that help you level up your meetings in 2024.
Meet comfortably and confidently with customizable meeting views
The meeting stage, or gallery, is at the core of the virtual meeting experience and can either hinder or enhance meeting efficiency depending on your needs. We’re excited to share how we’re evolving the default gallery experience in Teams meetings to give you a simpler, more predictable meeting presence—while enabling more controls that let you personalize the view to suit your preferences.
First, let’s look at the new default gallery experience that will be applicable to all. The new gallery will place everyone in tiles of equal size (16:9 ratio) whether their video is turned on or off. Additionally, the new default gallery layout will be more consistent and predictable for all meetings, regardless of size and content shared.
There are still a few default configurations that AI will optimize for to improve engagement and efficiency. For virtual participants, these are prioritizing those that have a raised hand and prioritizing the active speaker, enhancing their visibility so comments are not missed.
And when a Teams Room joins the meeting, the video of the room automatically enlarges, bridging the gap between remote and in-room participants. Remote attendees enjoy a clearer view and better connection, easily spotting who is speaking. Want a custom view? Simply tweak the tile size to your preference from the more options (…) menu by hovering on the room name. It’s seamless, inclusive, and ensures everyone can be seen, no matter where they are.
Next, let’s look at the controls that help you customize every meeting view to suit your needs.
While the default gallery size for meetings will be 16 participants, you can customize the number of participants visible on your screen to best fit your preference. You can choose from 4, 9, 16, and 49 participants visible on the screen for gallery size.
For some, having their own video visible to them on screen is a distraction. Now, you can opt to hide your own tile from your gallery view. This will not hide your tile from other participants, only your own gallery view.
When you don’t want to completely hide your video tile but want to change its position, you can also choose to remove it from the main gallery and position it either to the side or above the main gallery.
For meetings that have a mix of video on and video off, you can choose to prioritize tiles with video on in the main gallery to better connect with your teams.
The new gallery view updates are available in Public Preview starting this month. Learn more about gallery view on the support page.
In addition to meeting gallery updates, we are also introducing more customizable options for the color scheme of your Teams interface. When you get tired of dark screens for your Teams meetings and calls, you can now brighten things up with the Light Theme option. Light Theme enables you to customize the appearance of your Teams client. You can change the color theme of your Teams client from the default Dark Mode to Light Theme from your Teams settings. You can join meetings with Light Theme too. Light Theme is available now for the new Teams app.
Save time with simplified meeting join
As our calendars become increasingly packed with virtual and hybrid meetings, the need for efficiency is more important than ever. To help address this, we’re rolling out new updates to enhance the meeting join process. These improvements will enable you to join meetings quickly and effortlessly, so you can dive into important discussions without delay.
Let’s start with the invite, since the meeting invite is the first thing that a participant sees before joining. To ensure the most important information is visible and all the join options are clear, we are updating the invite design to better group related information as well as clean it up visually.
The simplified meeting invite will be available in February.
As part of the revamped invite design, we’re also improving the meeting join link by making it shorter. Sharing and joining meetings just got easier with a meeting URL that is shorter and clearer than before.
Shortened meeting link will be available in the second quarter of this year.
We’re also simplifying the experience of joining meetings across your different Microsoft accounts, with the ability to seamlessly join Teams (free) meetings from Teams for work and vice versa. This enables Microsoft Teams (free) users, those using a personal Microsoft Account, to directly join Teams for work meetings from within the client and stay connected even after the meeting has ended. This capability similarly enables Microsoft Teams (work or school) users to join the Microsoft Teams (free) meetings directly from within the client. With this simplified experience, you are no longer prompted to join via a browser and treated as a meeting guest (anonymous). This capability will be available in February.
Enhance efficiency with streamlined audio and video controls
The efficiency gains extend beyond just joining meetings. We’re streamlining in-meeting processes as well, including audio and video controls. This enables you to focus on important conversations rather than navigating through the settings to make audio and video adjustments. Starting this month, we are rolling out audio and video flyouts in meetings, which are designed to make it easier and more efficient for users to manage their audio and video settings during Teams meetings.
Now, when you want to select your camera or mic device, you can choose the right device directly from the flyouts. You can also adjust the volume, spatial audio, and noise suppression controls from the audio flyout.
If you didn’t select your background during the pre-join page, you can easily change your background directly from the camera flyout. We’ve also made avatars accessible from the camera flyout so you can use avatars in meetings, and meeting reactions will be reflected by your avatar. You can also adjust brightness and soft focus from the camera flyout.
Collaborate without compromise, no matter where you are
In 2020 we launched Together Mode to make virtual meetings feel more personal by bringing everyone together in a shared background. Together Mode offers unique benefits by placing everyone in a consistent position in the shared virtual space, so the group has a common spatial perception of where everyone is. This improved spatial awareness helps you connect more naturally and reduce virtual meeting fatigue by more closely imitating the cognitive processing that happens when people are in the same room.
Now, Together Mode is getting better with a new layout for content sharing. Visually, this new layout moves the Together Mode video participants to the bottom of the screen so you can see remote colleagues with a shared background on a horizontal plane – similarly to the front row experience in Teams Rooms.
This new layout will give people in the room a greater sense of connection to remote participants, and extend the natural benefits of Together Mode to the points of a meeting when content is shared or presented. The new Together Mode layout will be in Public Preview in early February.
Microsoft Tech Community – Latest Blogs –Read More
Create Tasks Repository in Microsoft Sentinel
Important note:
Before we start with the main topic, Tasks repository, we are happy to announce that starting today, Tasks feature in Microsoft Sentinel is also reaching GA (General Availability)!
One of the most important factors in running your security operations (SecOps) effectively and efficiently is the standardization of processes. SecOps analysts are expected to perform a list of steps, or tasks, in the process of triaging, investigating, or remediating an incident. Standardizing and formalizing the list of tasks can help keep your SOC running smoothly, ensuring the same requirements apply to all analysts. This way, regardless of who is on-shift, an incident will always get the same treatment and SLAs. Analysts don’t need to spend time thinking about what to do, or worry about missing a critical step. Those steps are defined by the SOC manager or senior analysts (tier 2/3) based on common security knowledge (such as NIST), their experience with past incidents, or recommendations provided by the security vendor that detected the incident.
In Microsoft Sentinel, you can utilize Tasks functionality for this purpose. Tasks can be added manually to the incident after the creation or using automation rules and/or playbooks automatically on incident creation.
But what if we have tasks for dozen incidents that are not the same? Or even few dozen? Creating and managing many automation rules for each incident or creating many conditions in playbooks can lead to complications and it would be really hard to manage.
In this blog, we will demonstrate how utilization of watchlists, automation rules, and playbooks can be used as tasks repository that will assign tasks based on incident title on incident creation. We should deploy it in this order:
Watchlist – Permission needed to deploy: Microsoft Sentinel Contributor
Playbook – Permission needed to deploy: Logic App Contributor; Permission needed to assign RBAC to managed identity: User Access Administrator or Owner on Resource Group where Microsoft Sentinel is
Automation rule – Permission needed to create: Microsoft Sentinel Responder
STEP 1
First step is to deploy the watchlist that will be used to store tasks. We can use sample watchlist and deploy it to our environment by clicking on Deploy to Azure.
Watchlist contains Incident title column that is also mapped to SearchKey, and additional 20 columns for tasks.
If there is a need for more then 20 tasks, please use CSV file to add additional columns, and create watchlist manually. Important note, when creating watchlist manually, use TasksRepository for alias, or this field will need to be updated in the playbook after deploying it. Also, map SearchKey to IncidentTitle column as playbook is using it as well.
IncidentTitle field doesn’t need to contain full incident title, as we are using contains to compare IncidentTitle field from watchlist with actual title when the incident is created. This is used so that you can utilize dynamic values feature when creating Analytic rules in Microsoft Sentinel.
Watchlist contain one row sample data, that can be deleted after adding tasks that will be used in production. Please note that if you delete sample value before adding any other rows in the watchlist, you will need to re-deploy the watchlist. Watchlist cannot be empty.
When adding additional tasks, there is a format that should be used so that playbook can map tasks title and description field. Each tasks filed should look like Tasks title, unique separator |^|, followed by Tasks description. Unique separator |^| is used in playbook to separate title and description of the tasks into its appropriate fields. In watchlist example, in column Task01 we can see example – Task 1|^|Task description.
Some additional recommendations around tasks:
Maximum number of tasks per incident is 100.
Task title length must not exceed 150 characters.
Task description length must not exceed 3000 characters.
You can use HTML elements like bold/italic/underlined, headings, hyperlinks, indenting.
When using hyperlinks, use target=’_blank’ to open in new tab as link cannot be opened in task itself – example
<a target=’_blank’ href=’https://www.microsoft.com/en-us/’>Microsoft Homepage</a>
STEP 2
Second step in the process is to deploy sample playbook that will extract task title and description based on the incident title and write it into the incident tasks.
After deploying the playbook, we will need to assign these permissions to Logic App managed identity:
Microsoft Sentinel Responder
Next, open Edit mode of the playbook, and add managed identity to Azure Monitor Logs action:
Select Create New to save our API connection, and then Save the playbook.
Also, important step is to make sure that For each loop in playbook has correct settings for parallelism so that tasks are added one by one, in order we define it in the watchlist.
In playbook, access Menu for action For each – task, and make sure that field Degree of Parallelism is set to 1.
STEP 3
Final step is to create an automation rule that will run on incident creation on all incidents, and as an action will run playbook. You can also add it to any existing automation rule you have that is being run on incident creation.
Title: Tasks repository
Trigger: When incident is created
Actions: Run playbook -> TasksRepository
After deploying watchlist, playbook, and automation rule, repository for tasks is ready. Add your tasks per incident to watchlist and make sure to update it regularly to remove any old information in the tasks! More information on how to manage watchlist can be found on Microsoft Sentinel docs.
Learn more about tasks:
Use tasks to manage incidents in Microsoft Sentinel | Microsoft Learn
Work with incident tasks in Microsoft Sentinel | Microsoft Learn
Audit and track changes to incident tasks in Microsoft Sentinel | Microsoft Learn
Tasks Workbook – Part of Sentinel SOAR Essentials solution
Please share feedback and what else you would like to see in Tasks Repository solution using Watchlists and Automation in Microsoft Sentinel!
Microsoft Tech Community – Latest Blogs –Read More
Troubleshooting Azure Stack HCI 23H2 Preview Deployments
Troubleshooting Azure Stack HCI 23H2 Preview Deployments
With Azure Stack HCI release 23H2 preview, there are significant changes to how clusters are deployed, enabling low touch deployments in edge sites. Running these deployments in customer sites or lab environments may require some troubleshooting as kinks in the process are ironed out. This post aims to give guidance on this troubleshooting.
The following is written using a rapidly changing preview release, based on field and lab experience. We’re focused on how to start troubleshooting, rather than digging into specific issues you may encounter.
Understanding the deployment process
Deployment is completed in two steps: first, the target environment and configuration are validated, then the validated configuration is applied to the cluster nodes by a deployment. While ideally any issues with the configuration will be caught in validation, this is not always the case. Consequently, you may find yourself working through issues in validation only to also have more issues during deployment to troubleshoot. We’ll start with tips on working through validation issues then move to deployment issues.
When the validation step completes, a ‘deploymentSettings’ sub-resource is created on your HCI cluster Azure resource.
Logs Everywhere!
When you run into errors in validation or deployment the error passed through to the Portal may not have enough information or context to understand exactly what is going on. To get to the details, we frequently need to dig into the log files on the HCI nodes. The validation and deployment processes pull in components used in Azure Stack Hub, resulting in log files in various locations, but most logs are on the seed node (the first node sorted by name).
Viewing Logs on Nodes
When connected to your HCI nodes with Remote Desktop, Notepad is available for opening log files and checking contents. Another useful trick is to use the PowerShell Get-Content command with the -wait parameter to follow a log and -last parameter to show only recent lines. This is especially helpful to watch the CloudDeployment log progress. For example:
Get-Content C:CloudDeploymentLogsCloudDeployment.2024-01-20.14-29-13.0.log -wait -last 150
Log File Locations
The table below describes important log locations and when to look in each:
Path
Content
When to use…
C:CloudDeploymentLogsCloudDeployment*
Output of deployment operation
This is the primary log to monitor and troubleshoot deployment activity. Look here when a deployment fails or stalls
C:CloudDeploymentLogsEnvironmentValidatorFull*
Output of validation run
When your configuration fails a validation step
C:ECEStoreLCMECELiteLogsInitializeDeploymentService*
Logs related to the Life Cycle Manager (LCM) initial configuration
When you can’t start validation, the LCM service may not have been fully configured
C:ECEStoreMASLogs
PowerShell script transcript for ECE activity
Shows more detail on scripts executed by ECE—this is a good place to look if CloudDeployment shows an error but not enough detail
C:CloudDeploymentLogscluster*
C:WindowsTemp StorageClusterValidationReport*
Cluster validation report
Cluster validation runs when the cluster is created; when validation fails, these logs tell you why
Retrying Validations and Deployments
Retrying Validation
In the Portal, you can usually retry validation with the “Try Again…” button. If you are using an ARM template, you can redeploy the template.
In the Validation stage, your node is running a series of scripts and checks to ensure it is ready for deployment. Most of these scripts are part of the modules found here:
C:Program FilesWindowsPowerShellModulesAzStackHci.EnvironmentChecker
Sometimes it can be insightful to run the modules individually, with verbose or debug output enabled.
Retrying Deployment
The ‘deploymentSettings’ resource under your cluster contains the configuration to deploy and is used to track the status of your deployment. Sometimes it can be helpful to view this resource; an easy way to do this is to navigate to your Azure Stack HCI cluster in the Portal and append ‘deploymentsettings/default’ after your cluster name in the browser address bar.
Image 1 – the deploymentSettings Resource in the Portal
From the Portal
In the Portal, if your Deployment stage fails part-way through, you can usually restart the deployment by clicking the ‘Return Deployment’ button under Deployments at the cluster resource.
Image 2 – access the deployment in the Portal so you can retry
Alternatively, you can navigate to the cluster resource group deployments. Find the deployment matching the name of your cluster and initiate a redeploy using the Redeploy option.
Image 3 – the ‘Redploy’ button on the deployment view in the Portal
If Azure/the Portal show your deployment as still in progress, you won’t be able to start it again until you cancel it or it fails.
From an ARM Template
To retry a deployment when you used the ARM template approach, just resubmit the deployment. With the ARM template deployment, you submit the same template twice—once with deploymentMode: “Validate” and again with deploymentMode: “Deploy”. If you’re wanting to retry validation, use “Validate” and to retry deployment, use “Deploy”.
Image 4 – ARM template showing deploymentMode setting
Locally on the Seed Node
In most cases, you’ll want to initiate deployment, validation, and retries from Azure. This ensures that your deploymentSettings resource is at the same stage as the local deployment.
However, in some instances, the deployment status as Azure understands it becomes out of sync with what is going on at the node level, leaving you unable to retry a stuck deployment. For example, Azure has your deploymentSettings status as “Provisioning” but the logs in CloudDeployment show the activity has stopped and/or the ‘LCMAzureStackDeploy’ scheduled task on the seed node is stopped. In this case, you may be able to rerun the deployment by restarting the ‘LCMAzureStackDeploy’ scheduled task on the seed node:
Start-ScheduledTask -TaskName LCMAzureStackDeploy
If this does not work, you may need to delete the deploymentSettings resource and start again. See: The big hammer: full reset.
Advanced Troubleshooting
Invoking Deployment from PowerShell
Although deployment activity has lots of logging, sometimes either you can’t find the right log file or seem to be missing what is causing the failure. In this case, it is sometimes helpful to retry the deployment directly in PowerShell, executing the script which is normally called by the Scheduled Task mentioned above. For example:
C:CloudDeploymentSetupInvoke-CloudDeployment.ps1 -Rerun
Local Group Membership
In a few cases, we’ve found that the local Administrators group membership on the cluster nodes does not get populated with the necessary domain and virtual service account users. The issues this has caused have been difficult to track down through logs, and likely has a root cause which will soon be addressed.
Check group membership with: Get-LocalGroupMember Administrators
Add group membership with: Add-LocalGroupMember Administrators -Member <domainusername|local username|SID>[,…]
Here’s what we expect on a fully deployed cluster:
Type
Accounts
Comments
Domain Users
DOMAIN<LCMUser>
This is the domain account created during AD Prep and specified during deployment
Local Users
AzBuiltInAdmin (renamed from Administrator)
ECEAgentService
HCIOrchestrator
These accounts don’t exist initially but are created at various stages during deployment. Try adding them—if they are not provisioned, you’ll get a message that they don’t exist.
Virtual Service Accounts
S-1-5-80-1219988713-3914384637-3737594822-3995804564-465921127
S-1-5-80-949177806-3234840615-1909846931-1246049756-1561060998
S-1-5-80-2317009167-4205082801-2802610810-1010696306-420449937
S-1-5-80-3388941609-3075472797-4147901968-645516609-2569184705
S-1-5-80-463755303-3006593990-2503049856-378038131-1830149429
S-1-5-80-649204155-2641226149-2469442942-1383527670-4182027938
S-1-5-80-1010727596-2478584333-3586378539-2366980476-4222230103
S-1-5-80-3588018000-3537420344-1342950521-2910154123-3958137386
These are the SIDs of the various virtual service accounts used to run services related to deployment and continued lifecycle management. The SIDs seem to be hard coded, so these can be added any time. When these accounts are missing, there are issues as early as the JEA deployment step.
ECEStore
The files in the ECEStore directory show state and status information of the ECE service, which handles some lifecycle and configuration management. The JSON files in this directory may be helpful to troubleshoot stuck states, but most events also seem to be reported in standard logs. The MASLogs directory in the ECEStore directory shows PowerShell transcripts, which can be helpful as well.
NUGET Packages
During initialization, several NuGet packages are downloaded and extracted on the seed node. We’ve seen issues where these packages are incomplete or corrupted—usually noted in the MASLogs directory. In this case, the The big hammer: full reset option seems to be required.
The Big Hammer: Full Reset
If you’ve pulled the last of your hair out, the following steps usually perform a full reset of the environment, while avoiding needing to reinstall the OS and reconfigure networking, etc (the biggest hammer). This is not usually necessary and you don’t want to go through this only to run into the same problem, so spend some time with the other troubleshooting options first.
Uninstall the Arc agents on all nodes with the Remove-AzStackHciArcInitialization command
Delete the deploymentSettings resource in Azure
Delete the cluster resource in Azure
Reboot the seed node
Delete the following directories on the seed node:
C:CloudContent
C:CloudDeployment
C:Deployment
C:DeploymentPackage
C:EceStore
C:NugetStore
Remove the LCMAzureStackStampInformation registry key on the seed node:
Get-Item -path HKLM:SOFTWAREMicrosoftLCMAzureStackStampInformation | Remove-Item -whatif
Reinitialize Arc on each node with Invoke-AzStackHciArcInitialization and retry the complete deployment
Conclusion
Hopefully this guide has helped you troubleshoot issues with your deployment. Please feel free to comment with additional suggestions or questions and we’ll try to get those incorporated in this post.
If you’re still having issues, a Support Case is your next step!
Microsoft Tech Community – Latest Blogs –Read More