Category: Microsoft
Category Archives: Microsoft
What’s New in Excel (January 2024)
Happy 2024!! Welcome to our first update of the year, the January update.
This month, we are excited to share that users can now sync form data to Excel for the web. Insert pictures into cells is available to users of Excel on Windows and Mac, and PivotTables has expanded functionality in Excel for iPad.
Many of these features are the result of your feedback. THANK YOU! Your continued Feedback in Action (#FIA) helps improve Excel for everyone.
Excel for Web:
Sync Forms Data to Excel
Date Picker #FIA
Excel for Windows:
Insert Pictures in Cells #FIA
Check Performance
Excel for Mac:
Insert Pictures in Cells #FIA
Excel for iPad:
PivotTables on iPad
Excel for Web
1. Sync Forms Data to Excel
With just one click, you can now easily access all your form responses in Excel for the web and take advantage of Excel’s rich functions to analyze and visualize your data. With automatic syncing of new responses in real-time, you can keep working on your existing spreadsheet without missing a beat. Read more here >
Data Sync to Microsoft Forms
#FIA
2. Date Picker
The Date Picker feature in Excel allows you to quickly insert a date from a calendar within a cell. This tool also enables you to display preset dates within your Excel worksheets. You can activate the Date Picker pop-up by either double-clicking in a cell or entering a date manually.
Excel for Windows
#FIA
1. Insert Pictures in Cells
We’ve enabled the ability for a picture to become the actual cell value. It remains attached to the data even when the sheet’s layout is modified. You can use it in tables, sort, filter, include it in formulas, and much more! Read more here > or watch this YouTube instructional video from one of our Excel MVP’s Leila Gharani.
Insert Pictures in Cells
2. Check Performance
When you open your workbook, Excel can detect whether your workbook contains unwanted formatted cells that can slow down your workbook. If so, Excel suggests launching “Check Performance”. You can also manually launch the feature from Review > Check Performance. Read more and try it yourself >. This capability is already available for all web users.
Excel for Mac
#FIA
1. Insert Pictures in Cells
We’ve enabled the ability for a picture to become the actual cell value. It remains attached to the data even when the sheet’s layout is modified. You can use it in tables, sort, filter, include it in formulas, and much more! Read more here > or watch this YouTube instructional video from one of our Excel MVP’s Leila Gharani.
Insert Pictures in Cells
Excel for iPad
1. PivotTables for iPad
PivotTables allow you to calculate, summarize, and analyze data. This powerful tool has now been tailored for the iPad’s smaller screen and touch interface. Read more here >
PivotTables on iPad
Check if a specific feature is in your version of Excel
Click here to open in a new browser tab
Your feedback helps shape the future of Excel. Please let us know how you like a particular feature and what we can improve upon—“Give a compliment” or “Make a suggestion”.. You can also submit new ideas or vote for other ideas via Microsoft Feedback.
Subscribe to our Excel Blog and the Insiders Blog to get the latest updates. Stay connected with us and other Excel fans around the world – join our Excel Community and follow us on X, formerly Twitter.
Special thanks to our Excel MVPs David Benaim and Bill Jelen for their contribution to this month’s What’s New in Excel article. David publishes weekly YouTube videos and regular LinkedIn posts about the latest innovations in Excel and more. Bill is the founder and host of MrExcel.com and the author of several books bout Excel.
Microsoft Tech Community – Latest Blogs –Read More
Common Deployment Challenges and Workarounds for HCI 23H2
Introduction
Azure Stack HCI 23H2 introduces a new method for deploying the cluster from the Azure portal. You use the Azure portal to join on-premises servers to the domain, build a cluster, and set up an AKS on top of that to act as the resource bridge created by an AKS Cluster. These involve numerous steps and tasks that need completion, spanning from the cloud to your on-premises servers. In this blog, I will share the most common steps to help you avoid any issues that could lead to your cluster failing in the middle of the deployment.
OS Installation
If you are using existing hardware with a previous version of HCI, the wizard will prompt you to choose between a new installation or an upgrade. Opt for a new installation, but ensure to clean all the disks. This involves deleting all volumes on the OS disk, and if you had Storage Spaces Direct (S2D) configured on other disks, take the opportunity to delete the data disks as well.
Post OS Installation
Local Administrator Credentials
Once the OS is installed, you will be prompted to enter a new password for the default Administrator. I suggest you create a password following Azure recommendations. The reason is, during the deployment, you will be asked to enter a username and password for the local administrator, just in case If you decide to use the default administrator credentials, of course you can change the password later on using PowerShell.
$NewPassword = Read-Host -AsSecureString
Set-ADAccountPassword Administrator –NewPassword $NewPassword -Reset
However I suggest you create a new local user and adding to local Administrators
$NewLocalAdmin = Read-Host
$Password = Read-Host -AsSecureString
New-LocalUser “$NewLocalAdmin” -Password $Password -FullName “$NewLocalAdmin” -Description “Local User for HCI Deployment” | Add-LocalGroupMember -Group “Administrators”
Networking
There are some steps you should consider performing at the beginning the deployment , some of them are required and other you need to make it easier for yourself while you are preparing the nodes
Windows Firewall
Enable file and print share on each node after the deployment you need to disable it
netsh advfirewall firewall set rule group=”File and Printer Sharing” new enable=Yes
Enable Internet Control Message Protocol (ICMP). This command is required for the other nodes to access the first node. (Required for the deployment )
netsh advfirewall firewall add rule name=”ICMP Allow incoming V4 echo request” protocol=icmpv4:8,any dir=in action=allow
NetworkAdapter
Rename the adapter based on the usage , probably in each node you have 6 ports 2 for Management, 2 for Management , 2 for Compute and 2 for storage , obviously I would make the RDMA capable Network Interface for the storage the following are cmdlet that needed to manage the network adapter
List all Network Adapters
Get-NetAdapter
Rename Network Adapter
Rename-NetAdapter -Name “CURRENT NETWORK ADAPTER NAME” -NewName “NEW Network NAME”
** I suggest renaming the adapter based on the intended use (e.g., Storage01 for storage, MGMT-COMPUTE01 for combined Management and Compute on the same NIC, etc.). Ensure that the names are consistent across all nodes for the same purpose or usage.
Assign a VLAN to the network interface
Set-Netadapter -VlanID “VLAN NUMBER” – Name “NETWORK ADAPTER NAME”
Identify RDMA capable network adapters that have RDMA enabled
Get-NetAdapterRdma -Name “*” | Where-Object -FilterScript { $_.Enabled }
Assign IP to the Management interface
New-NetIPAddress -InterfaceAlias “NETWORK ADAPTER NAME” -IPAddress “IP Address for Management” -PrefixLength 24 -DefaultGateway “Default Gateway” -AddressFamily IPv4
Assign DNS to the management interface
Set-DnsClientServerAddress -InterfaceAlias “NETWORK ADAPTER NAME” -ServerAddresses (“IP FOR DNS SERVER1″,”IP FOR DNS SERVER1”)
**Ensure that only one network adapter has a configured gateway; the deployment prerequisites will fail if multiple gateways are detected on the server. Verify that the Component IDs are consistent for network cards with the same intent
Get-NetAdapter | Select name , ComponentID
Disable IPV6 on all adapters
Disable-NetAdapterBinding -Name * -ComponentID ms_tcpip6
Disable DHCP on all adapters
Set-NetIPInterface -InterfaceAliace * -Dhcp Disabled
Proxy Setup
If the node are behind a proxy the following configuration are required
Install and configure WinInetProxy module
$proxyurl = ‘http://PROXYURL:PORTNUMBER‘
$proxy= ‘PROXYURL:PORTNUMBER’
[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
[system.net.webrequest]::defaultwebproxy = new-object system.net.webproxy($proxyurl)
[system.net.webrequest]::defaultwebproxy.credentials = [System.Net.CredentialCache]::DefaultNetworkCredentials
[system.net.webrequest]::defaultwebproxy.BypassProxyOnLocal = $true
$WebClient = New-Object System.Net.WebClient
$WebClient.DownloadFile(“https://psg-prod-eastus.azureedge.net/packages/wininetproxy.0.1.0.nupkg“,”C:wininetproxy.0.1.0.zip”)
New-Item -Path $env:ProgramFilesWindowsPowerShellModulesWinInetProxy -ItemType Directory
cd $env:ProgramFilesWindowsPowerShellModulesWinInetProxy
Expand-Archive -Path C:wininetproxy.0.1.0.zip
Move-Item -Path .wininetproxy.0.1.0 -Destination ..1.0
Set-ExecutionPolicy -ExecutionPolicy Bypass
Import-Module WinInetProxy
Set-WinInetProxy -ProxySettingsPerUser 0 -ProxyServer proxy -ProxyBypass “<local>”
Set up netsh winhttp proxy
netsh winhttp set proxy proxy-server=’http://PROXYURL:PORTNUMBER‘ bypass-list=”localhost;<local>;*.Internaldomain;Node1;Node2;clustername;first three octets of the IP address.*”
Example
netsh winhttp set proxy proxy-server=”http://globalproxy.Contoso.com:9400” bypass-list=”localhost;<local>;*.corp.contoso.com;HCIN1;HCIN2;HCIN3;HCIN4;Cluster01;192.90.8.*”
Set up environment variables
[Environment]::SetEnvironmentVariable(“HTTPS_PROXY”, “http://globalproxy.Contoso.com:9400“, “Machine”)
$env:HTTPS_PROXY = [System.Environment]::GetEnvironmentVariable(“HTTPS_PROXY”, “Machine”)
[Environment]::SetEnvironmentVariable(“HTTP_PROXY”, “http://globalproxy.Contoso.com:9400“, “Machine”)
$env:HTTP_PROXY = [System.Environment]::GetEnvironmentVariable(“HTTP_PROXY”, “Machine”)
$no_proxy = “localhost,127.0.0.1,.svc,192.90.8.192/22,.corp.Contoso.com”
[Environment]::SetEnvironmentVariable(“NO_PROXY”, $no_proxy, “Machine”)
$env:NO_PROXY = [System.Environment]::GetEnvironmentVariable(“NO_PROXY”, “Machine”)
Set up PowerShell and install Az.StackHCI module
$proxy = ‘http://globalproxy.Contoso.com:9400‘
[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
[system.net.webrequest]::defaultwebproxy = new-object system.net.webproxy($proxy)
[system.net.webrequest]::defaultwebproxy.credentials = [System.Net.CredentialCache]::DefaultNetworkCredentials
[system.net.webrequest]::defaultwebproxy.BypassProxyOnLocal = $true
Install-PackageProvider -Name nuget -Scope AllUsers -Confirm:$false -Force -MinimumVersion 2.8.5.201
Set-PSRepository PSGallery -InstallationPolicy Trusted
install-module az.stackhci
Network Driver Update
HCI doesn’t support home driver, you need to download the driver from the hardware vendor, the following cmdlet will help you
Start-BitsTransfer -Source “http://VENDORURL/NetworkDrive.exe” -Destination “c:tempNetworkDrive.exe”
After you install the vendor driver , make sure to check the driver provider name, as well as the ComponentID
Get-NetAdapter | Select name , ComponentID, DriverProvider | FT
After the upgrade, I’ve observed that the ComponentID for the same card can change, even though it may remain the same but in a different letter format. For example, in a dual-card setup, Port 1 might have the ComponentID in small letters, while Port 2 has it in capital letters. To address this, consider uninstalling the drivers, installing a lower version of the driver, and then upgrading to the latest driver update.
Register HCI Node with ARC
On all the nodes, make sure you have the required Modules
Register PSGallery as a trusted repo
Register-PSRepository -Default -InstallationPolicy Trusted
Install Arc registration script from PSGallery
Install-Module AzsHCI.ARCinstaller
Install required PowerShell modules in your node for registration
Install-Module Az.Accounts -Force
Install-Module Az.ConnectedMachine -Force
Install-Module Az.Resources -Force
Create the following variable and assign the appropriate value
Define the subscription where you want to register your server as Arc device
$Subscription = “YourSubscriptionID” #Define the resource group where you want to register your server as Arc device
$RG = “YourResourceGroupName” #Define the tenant you will use to register your server as Arc device
$Tenant = “YourTenantID”
Connect to Azure using the Devise Code switch
Connect-AzAccount -SubscriptionId $Subscription -TenantId $Tenant -DeviceCode
Get the Access Token for the registration
$ARMtoken = (Get-AzAccessToken).Token
Get the Account ID for the registration
$id = (Get-AzContext).Account.Id
Invoke the registration script. For this release, eastus and westeurope regions are supported.
Invoke-AzStackHciArcInitialization -SubscriptionID$Subscription -ResourceGroup$RG -TenantID$Tenant -Regioneastus -Cloud”AzureCloud” -ArmAccessToken$ARMtoken -AccountID$id
In case you have a proxy use the following command
Invoke-AzStackHciArcInitialization -SubscriptionID$Subscription -ResourceGroup$RG -TenantID$Tenant -Regioneastus -Cloud”AzureCloud” -ArmAccessToken$ARMtoken -AccountID$id – proxy http://PROXYURL:PORTNUMBER
After the node appears in Azure as an hybrid machine, verify that you have all the extension have been successfully installed
I often see the TelemetryAndDiagnostics and AzureEdgeLifeCyclemanager extension in failed state after registering the nodes to ARC
How to Fix
TelemetryAndDiagnostics
From any of the HCI node run the following
Remove-AzConnectedMachineExtension -MachineName <NodeName> -Name “TelemetryAndDiagnostics ” -ResourceGroupName <Resource Group name> -SubscriptionId <SubscriptionID> -NoWait
After the extension get removed from the portal reinstall the extension
New-AzConnectedMachineExtension -MachineName <NodeName> -Name “TelemetryAndDiagnostics” -ResourceGroupName <Resource Group name> -SubscriptionId <SubscriptionID> -Location <region>-Publisher “Microsoft.AzureStack.Observability.TelemetryAndDiagnostics” -ExtensionType “TelemetryAndDiagnostics” -NoWait
What happen if the extension get stuck in deleting status
Try to use the ARM client to delete the extension , then reboot the node
.ARMClient.exe delete “<ResourceID>?api-version=2023-10-03-preview
You can get the resource ID from by checking the checkbox to show hidden resources
AzureEdgeLifecycleManager
On the affected node go to Go to `C:MASLogsLCMECELiteLogs`
run $filename = Get-ChildItem *.xml -recurse | Select-String -pattern “InitializeDeploymentService” | select Path -last 1
Copy the XML to the C:EceStore
copy $filename.path C:EceStoreefb61d70-47ed-8f44-5d63-bed6adc0fb0f`
remane the XML file you just copied to “dcd7bf4e-5148-83f1-1fdb-dbfca46c6840”
Rename-Item $filename -NewName dcd7bf4e-5148-83f1-1fdb-dbfca46c6840
** keep the above GUIDs as they are
Reboot the node and wait for 5 minutes and check the portal.
Microsoft Tech Community – Latest Blogs –Read More
Data MVPs and Microsoft Fabric Super Users in the Era of AI | Data Exposed: MVP Edition
Taking a step back in this episode of Data Exposed: MVP Edition to dive into the Microsoft MVP program and learn what Fabric Super Users are.
Resources:
Microsoft Fabric Learn Together
Become a Fabric Analytics Engineer
View/share our latest episodes on Microsoft Learn and YouTube!
Microsoft Tech Community – Latest Blogs –Read More
Data MVPs and Microsoft Fabric Super Users in the Era of AI | Data Exposed: MVP Edition
Taking a step back in this episode of Data Exposed: MVP Edition to dive into the Microsoft MVP program and learn what Fabric Super Users are.
Resources:
Microsoft Fabric Learn Together
Become a Fabric Analytics Engineer
View/share our latest episodes on Microsoft Learn and YouTube!
Microsoft Tech Community – Latest Blogs –Read More
Data MVPs and Microsoft Fabric Super Users in the Era of AI | Data Exposed: MVP Edition
Taking a step back in this episode of Data Exposed: MVP Edition to dive into the Microsoft MVP program and learn what Fabric Super Users are.
Resources:
Microsoft Fabric Learn Together
Become a Fabric Analytics Engineer
View/share our latest episodes on Microsoft Learn and YouTube!
Microsoft Tech Community – Latest Blogs –Read More
Data MVPs and Microsoft Fabric Super Users in the Era of AI | Data Exposed: MVP Edition
Taking a step back in this episode of Data Exposed: MVP Edition to dive into the Microsoft MVP program and learn what Fabric Super Users are.
Resources:
Microsoft Fabric Learn Together
Become a Fabric Analytics Engineer
View/share our latest episodes on Microsoft Learn and YouTube!
Microsoft Tech Community – Latest Blogs –Read More
Data MVPs and Microsoft Fabric Super Users in the Era of AI | Data Exposed: MVP Edition
Taking a step back in this episode of Data Exposed: MVP Edition to dive into the Microsoft MVP program and learn what Fabric Super Users are.
Resources:
Microsoft Fabric Learn Together
Become a Fabric Analytics Engineer
View/share our latest episodes on Microsoft Learn and YouTube!
Microsoft Tech Community – Latest Blogs –Read More
Data MVPs and Microsoft Fabric Super Users in the Era of AI | Data Exposed: MVP Edition
Taking a step back in this episode of Data Exposed: MVP Edition to dive into the Microsoft MVP program and learn what Fabric Super Users are.
Resources:
Microsoft Fabric Learn Together
Become a Fabric Analytics Engineer
View/share our latest episodes on Microsoft Learn and YouTube!
Microsoft Tech Community – Latest Blogs –Read More
Data MVPs and Microsoft Fabric Super Users in the Era of AI | Data Exposed: MVP Edition
Taking a step back in this episode of Data Exposed: MVP Edition to dive into the Microsoft MVP program and learn what Fabric Super Users are.
Resources:
Microsoft Fabric Learn Together
Become a Fabric Analytics Engineer
View/share our latest episodes on Microsoft Learn and YouTube!
Microsoft Tech Community – Latest Blogs –Read More
Data MVPs and Microsoft Fabric Super Users in the Era of AI | Data Exposed: MVP Edition
Taking a step back in this episode of Data Exposed: MVP Edition to dive into the Microsoft MVP program and learn what Fabric Super Users are.
Resources:
Microsoft Fabric Learn Together
Become a Fabric Analytics Engineer
View/share our latest episodes on Microsoft Learn and YouTube!
Microsoft Tech Community – Latest Blogs –Read More
Data MVPs and Microsoft Fabric Super Users in the Era of AI | Data Exposed: MVP Edition
Taking a step back in this episode of Data Exposed: MVP Edition to dive into the Microsoft MVP program and learn what Fabric Super Users are.
Resources:
Microsoft Fabric Learn Together
Become a Fabric Analytics Engineer
View/share our latest episodes on Microsoft Learn and YouTube!
Microsoft Tech Community – Latest Blogs –Read More
Data MVPs and Microsoft Fabric Super Users in the Era of AI | Data Exposed: MVP Edition
Taking a step back in this episode of Data Exposed: MVP Edition to dive into the Microsoft MVP program and learn what Fabric Super Users are.
Resources:
Microsoft Fabric Learn Together
Become a Fabric Analytics Engineer
View/share our latest episodes on Microsoft Learn and YouTube!
Microsoft Tech Community – Latest Blogs –Read More
Data MVPs and Microsoft Fabric Super Users in the Era of AI | Data Exposed: MVP Edition
Taking a step back in this episode of Data Exposed: MVP Edition to dive into the Microsoft MVP program and learn what Fabric Super Users are.
Resources:
Microsoft Fabric Learn Together
Become a Fabric Analytics Engineer
View/share our latest episodes on Microsoft Learn and YouTube!
Microsoft Tech Community – Latest Blogs –Read More
Data MVPs and Fabric Super Users | Data Exposed: MVP Edition
Taking a step back in this episode of Data Exposed: MVP Edition to dive into the Microsoft MVP program and learn what Fabric Super Users are.
Resources:
Microsoft Fabric Learn Together
Become a Fabric Analytics Engineer
View/share our latest episodes on Microsoft Learn and YouTube!
Microsoft Tech Community – Latest Blogs –Read More
Partner Blog | Unlock productivity with Jira Cloud plugin for Microsoft Copilot for Microsoft 365
By Srini Raghavan,VP, Microsoft Teams Ecosystem
There’s little doubt that AI is transforming the way we work across entire enterprise processes and the day-to-day digital experiences of employees. But what about the business value it represents?
According to a recent global study from IDC, organizations are quickly realizing rapid return on investment and significant increases to customer satisfaction, productivity, and market share that results from AI integration—especially when coupled with 40 percent of organizations reporting implementation times of less than six months and 92 percent of AI deployments taking 12 months or less.*
Continue reading here
Microsoft Tech Community – Latest Blogs –Read More
What’s new in Microsoft Teams (free) | January 2024
Read more about the latest feature updates and improvements in Microsoft Teams (free) in the recent blog post on the Teams Insider Blog:
https://insider.teams.com/blog/whats-new-in-microsoft-teams-free-jan-2024/
Microsoft Tech Community – Latest Blogs –Read More
Get started with Azure partner-led offerings: Azure Migrate and Modernize, and Azure Innovate.
With Microsoft Azure, you have access to a portfolio of products, resources, and offerings to help you meet evolving customer opportunities and join a community of partners committed to leading the way in the era of AI. With Azure, you can meet faster application delivery times, achieve significant cost savings, and access funding through Azure Migrate and Modernize and Azure Innovate. Formerly the Azure Migration and Modernization Program, Azure Migrate and Modernize is an expanded offering for customer migration and modernization scenarios across apps, data, and infrastructure that includes more workloads support, streamlined access to specialized partners, incentives to offset migration costs, and security guidance built into every engagement. Azure Innovate is our newest offering to build new solutions and modernize existing ones on Azure to meet the demand for AI transformation and begin the next wave of growth for your business.
Azure specialized partners and qualified ISVs have access to assessments, pilot POCs, tooling, funding, and Microsoft expert guidance when you need it – all designed to help you accelerate the cloud journey and drive growth and impact. At Microsoft, we recognize that what you need to succeed is unique to your business model, size, and stage of growth. That’s why we’re investing in these two comprehensive offerings that are built for all.
We are setting the pace in 2024 with the latest announcements effective January 1:
Extra small engagement sizes are now available for all scenarios
ISV partners can now nominate strategics in Azure Migrate and Modernize
Top Tier partners can access Azure Migrate and Modernize partner-led for ISVs if they satisfy the IP co-sell top tier criteria
And multiple nominations for the same customer will be available for the same engagement type
Learn more and nominate today!
Microsoft Tech Community – Latest Blogs –Read More
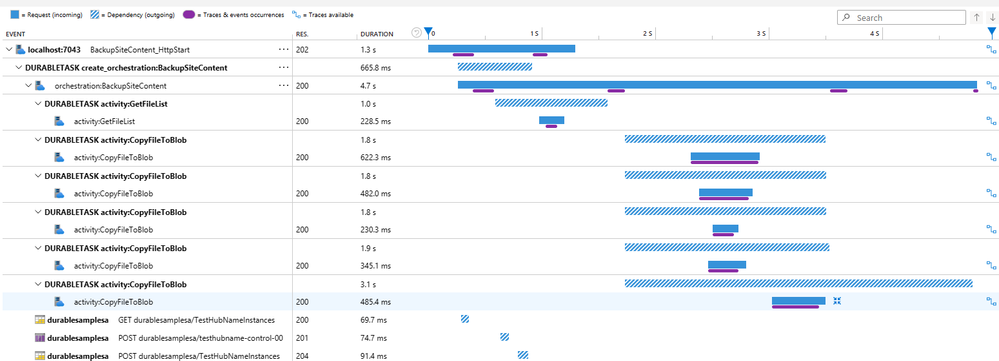
Preview of Distributed Tracing V2 for Durable Functions
We released Distributed Tracing V2 for Durable Functions to help improve observability!
Durable Functions enables you to write long-running, reliable, event-driven, and stateful logic on the Azure Functions platform using everyday imperative code.
Distributed Tracing allows you to correlate operations together and track requests between services. This is especially useful for Durable Functions apps as they coordinate work across multiple services and VMs.
Distributed Tracing V2 Improvements
The first implementation of Distributed Tracing supported only the .NET in-process model and the Azure Storage backend. The V1 implementation is still in an experimental state. Distributed Tracing V2, on the other hand, is not an experimental feature and supports all Durable Functions language SDKs, including .NET Isolated, and all Durable Functions backends: Azure Storage, MSSQL, and Netherite. It also provides more information about the spans.
This image above shows a trace where site content is backed up. The orchestration first calls an activity to get the files to backup and then all of those files are copied.
Limitations
Currently, Distributed Tracing V2 does not give traces for Durable Entities operations.
Try it out!
Step 1: Check the Durable Functions version
You’ll need Durable Functions Extension 2.12.0 or above. If you are using extension bundles, please follow these instructions to get the required Durable Functions version.
Step 2: Set up host.json
To set up Distributed Tracing V2, add the following settings to the application’s host.json:
“durableTask”: {
“tracing”: {
“DistributedTracingEnabled”: true,
“Version”: “V2”
}
}
If you are using Distributed Tracing V1, you will have to update your host.json to explicitly use V2.
Step 3: Create an Application Insights resource
If there’s no existing Application Insights resource configured with your Function app, then you will also need to create an Application Insights resource and configure it to connect to the Function app.
Other than the aforementioned configuration changes, no other code changes are required.
A getting started sample can be found here.
For more information, refer to Diagnostics in Durable Functions – Azure | Microsoft Learn.
Compatibility with Durable Task Framework
Distributed Tracing is also compatible with apps using the Durable Task Framework, the underlying C# OSS framework that powers Durable Functions.
You’ll need DurableTask.Core version >=2.16.0. More information can be found here.
Give us feedback!
Try it out and let us know how you like it! If you have any feedback regarding Distributed Tracing v2 for Durable Functions, please open an issue in the durable extension repo; for feedback regarding Durable Task Framework, use the durabletask repo.
Microsoft Tech Community – Latest Blogs –Read More
What’s New in Microsoft EDU webinar – February 2024
Join us on Tuesday, February 6th, 2024 for our latest “What’s New in Microsoft EDU” webinar! This webinar will also be recapping the big announcements we made at the Bett conference in London in late January. These 30 minute webinars are put on by the Microsoft Education Product Management group and happen once per month, this month both 8:00am Pacific Time and 4:00pm Pacific time to cover as many global time zones as possible around the world. And don’t worry – we’ll be recording these and posting on our Microsoft Education YouTube channel in the new “What’s New in Microsoft EDU” playlist, so you’ll always to able to watch later or share with others!
Here is our February 2024 webinar agenda:
What’s New in AI
What’s new in Microsoft Teams for EDU
What’s new in Microsoft 365 EDU
AMA – Ask Microsoft EDU Anything (Q&A)
How to sign up
OPTION 1: February 6th, Tuesday @ 8:00am Pacific Tim Register here
OPTION 2: February 6th, Tuesday @ 4:00pm Pacific Time: Register here
Send us your questions ahead of time by adding yours into this form: WNIEDUWebinarFeb24QnA
This is what the webinar portal will look like when you register:
Microsoft Tech Community – Latest Blogs –Read More
CAST – Modernizing your .NET apps to Windows containers on Azure Kubernetes Services
This blog post has been co-authored by Microsoft and Damien Santé and Emmanuelle Castaings at CAST.
Windows Containers have reached a great level of maturity, allowing customers to run production grade workloads with limited code refactoring. Though, specific compatibility checks are highly recommended for .NET applications, for example, to avoid discovering blockers hidden in source code during the migration, triggering unplanned fixes in urgency, additional time and costs.
To ensure an effective migration, a rapid portfolio analysis using CAST Highlight can be performed. It will automatically provide insights from custom source code, including the list of containerization blockers and indicative effort estimates to remediate. CAST Highlight will also automatically show a path to modernization post containerization leveraging Azure PaaS services. CAST Highlight is an automated solution where hundreds of custom applications can be analyzed within a few days, with no source code disclosed and no intrusion on production systems.
Since 2019, CAST has been working alongside Microsoft to automate the migration and modernization of custom applications for hundreds of clients worldwide, addressing a large variety of old and new languages such as C#, C++, VB.NET, Java, JavaScript, Python, Cobol and more, and various application types among Windows, mainframes, monoliths, databases and others.
This blog will cover the following sections:
CAST Highlight overview
How to use CAST for Windows container apps on AKS
Common containerization blockers, and CAST recommendations
Optimize further and prepare the modernization, using CAST
Illustrative case study on eShop applications & Customer Case Studies
CAST Highlight Overview
CAST Highlight provides a rapid analysis of the entire portfolio of custom applications, bringing data and facts to your modernization journey. CAST Highlight analysis is a rapid 3-steps process scanning hundreds of applications in a week.
CAST Highlight acts as a Control Tower for the tens or hundreds of applications in your portfolio helping you make informed decisions on governance, open-source risk control, greener software, and cloud modernization:
Cloud Maturity: 5Rs segmentation, roadmap to PaaS, containerization and cloud blockers, removal effort estimates
Software Health: resiliency, agility, complexity, technical debt
Open-source risks: security vulnerabilities, obsolescence, legal IP risks
Green Software: code deficiencies, recommendations with respect to industry good practices
CAST + Windows on Azure Kubernetes Service
Get actionable recommendations on containerization blockers
CAST Highlight shines a light on specific Cloud patterns that are blockers for containerization of applications, a subset of our 400+ existing patterns. Those patterns are agnostic to the target container, for instance, if an application is using DLLs, as part of the containerization tasks, the container definition (.dockerfile) should copy these required libraries and execute their registration if needed.
Nota Bene: CAST Highlight will not generate the Dockerfile but recommend the best options to be utilized. See here more details on how to optimize the Dockerfile configuration.
CAST Highlight lists in a dedicated tab all the containerization blockers and related details:
Documentation pop-up for each blocker with rationale, level of criticality, impact on containerization tasks
Technology/language triggering the blocker and number of occurrences in the code (roadblocks)
Estimated remediation effort based on customizable abacus.
At the portfolio level: list of applications where the blocker was found and at application level: list of files where the blocker occurred.
Common containerization blockers, and CAST recommendations
CAST Highlight provides the rationale for each containerization blocker categorized in three types of impact:
Blockers impacting the container only.
Blockers impacting the application code.
Blockers impacting the application architecture.
Blockers impacting the container only.
Registry Settings – Using Windows registry to store Application Settings
The problem: Legacy applications often use Windows registry to store application settings. The good practice consists of avoiding OS-specific storage such as Windows Registry, as in the container the operating system is not guaranteed to be the same.
The solution: CAST Highlight lists all your code files declaring registry dependencies so you can create a .reg file containing all the entries required by the application then edit the Dockerfile to copy it inside the container on creation and add the registry entries.
CAST Highlight detects other blockers that impact the container configuration such as usage of a temporary local file or directory, applications using other configuration files than web configuration, applications using system DLLs or COM Components, etc.
The figure below illustrates the description of the blocker in CAST Highlight with criticality, impact, rationale and references.
Blockers impacting the application code.
Temporary Files – Access to environment variable
The problem: applications accessing environment variables. This blocker impacts the application code, architecture, and the target container.
The solution: CAST Highlight provides the list of files for which an environment variable needs to be set up, so you can ensure it will exist in your container. It also gives the effort estimate to remediate the issue in the code. There are two ways this information can be passed down to the container. You can use the –e option in the run command of your docker container. It is adequate when the number of variables is low. However, as soon as we have more than a handful of variables, it can quickly become cumbersome and error prone. Another option is preferred where you can specify the file where to read values from, called an env_file.
CAST Highlight detects other blockers requiring changes in the application code such as stateful sessions, hardcoded credentials, network IP address (IPV4, IPV6) or unsecure network protocols (HTTP, FTP).
Blockers impacting the application architecture
Security & User Authentication- Using Webform Authentication
The problem: Applications using Webform Authentication which requires that user accounts and passwords be created and managed in a storage such as a database. This mechanism does not offer the flexibility of claims-based authentication and should not be used in Cloud applications. This is blocker which impacts the application architecture and code.
The solution: Use the CAST Highlight output listing all your code files declaring Webform Authentication dependencies. Review the dependencies in each file. Refactor the app to be AD-integrated and leverage Active Directory domain identities to support your authentication scenario. To achieve this, you can configure a Windows container to run with a group Managed Service Account (gMSA), which is a special type of service account introduced in Windows Server 2012 designed to allow multiple computers to share an identity without needing to know its password.
CAST Highlight also detects code performing file or directory manipulation, which creates files or folders on the local file system (C: or D: drives), or applications using a middleware application such as asynchronous messaging middleware.
Illustrative case study on eShop applications
This section describes the analysis performed on eShop applications, focusing on a legacy version of the code base (eShopLegacy) and a version that has been modernized (eShopModernized). We then review the results of analysis as it relates to containerization and identify key findings and recommendations.
Repository overview
The eShopModernizing repository contains 6 applications with a total of 91 000 lines of code in mainly C#, ASP.Net and JavaScript languages:
The first group is composed of 3 applications called “eShopLegacy*” containing the code before the containerization.
eShopLegacyMVC is a traditional Web app ASP.NET WebForms and MVC in .NET Framework.
eShopLegacyNTier is an N-Tier app based on a WCF service.
eShopLegacyWebforms is a client WinForms desktop app.
The second group is composed of the modernized version of the above 3 applications after containerization to Windows Containers and Azure Cloud.
Containerization insights
In total, the 6 eShop applications show 5 containerization blockers.
Three blockers impact the container configuration:
Access to environment variable 6 occurrences found in Ruby files.
Using other configuration files than Web configuration 6 occurrences in C# code.
Using connection strings for database connection: 4 occurrences in C# code of eShopModernized* apps.
Two blockers impact the applications architecture found in C# code:
Using file system: 3 occurrences found
Perform File Manipulation: 15 occurrences found.
The figure below illustrates the containerization insights collected by CAST Highlight: in which application, with estimated effort to remediate them, number of occurrences found for each blocker (roadblocks), technology involved and impact (Container only, Architecture, Code).
Remediating those blockers would take roughly:
0.36 person-day effort on the eShopLegacy* applications
0.52 person-day effort on the eShopModernized* applications
The estimated remediation effort only concerns the changes in the code, it must be added to surrounding tasks such as regression testing, project management, etc.
Why addressing the blockers in the code prior to containerization
In summary, we would spend less effort to fix the blockers before migrating the eShopLegacy* applications, compared to the effort spent on remediating the same applications after containerization.
For the eShopCase, the analysis of both versions of the codebase indicates that the best approach would have been to first address the blockers found in the legacy version prior to containerization. This approach required less effort than addressing the blockers after containerization. In fact, additional files were created in the modernized version to accommodate the new platform which added new issues and blockers.
Sample blockers details: “Using direct Database Access through Connection Strings”
Database connection strings are very sensitive data in a Cloud application as they protect access to data storage or other application services. As a result, connection strings must be protected to prevent data theft. It is recommended to store this kind of sensitive data in a secured cloud-based storage such (e.g. Azure Key Vault). This blocker impacts the container configuration, a documentation and references with the patterns detected in the code are available for each of the blockers in CAST Highlight:
This blocker has been found in 2 eShopModernized* applications: eShopModernizedMVCSolution eShopModernizedWebFormsSolution. This blocker was not detected in any Legacy application.
CAST Highlight detects 15 other blockers for containerization, find them all here: doc.casthighlight.com/cloudreadypatterns/ (refer to the ‘Containerization’ column).
Third-Party compliance
Third-party frameworks may not all be supported since Microsoft doesn’t specifically certify or support the use of non-Microsoft frameworks on Windows Containers. For each framework, you need to check that the vendor or application supports the policy for Windows containers, a frequent example being dependencies to Crystal Reports.
CAST Highlight makes an inventory of all third-party and open-sources components used by the application, either from dependencies declared in configuration files or directly in the code, or through physical libraries (JARs, DLLs) allowing you in one click to visualize all components used in your application portfolio. CAST Highlight also detects Common Vulnerabilities and Exposures (CVEs), obsolescence and licenses embedded in the 3rd-Party and Open-Sources Software components and generates a Software Bill of Materials.
On eShop applications, a few 3rd-Party frameworks such as ANTLR, autofac, log4net, owin or Pipelines.Sockets may require to use a docker image, a pre-installed SDK or publish a self-contained app including all the dependencies. Additionally, 8 high level CVEs were detected which may require an update to ensure maximum security on the container.
The figure below illustrates the CAST Highlight Software Composition insights including the Bill of Materials.
Modernizing further
Identify “noisy neighbors.”
An additional value of CAST Highlight are insights on the portfolio Health indicating how your applications comply with programming good practices that impact resiliency, agility, complexity or technical debt.
Insights from CAST Highlight can help act proactively to avoid potential “noisy neighbors” in a large application portfolio for which you may not have a precise knowledge of each application.
Applications showing a very low resiliency score in CAST Highlight would need special attention. For example, they may cause memory overflow, which, when containerized, will impact the computing resources consumption on the node. Neighboring containers will suffer unless resource management is enabled thanks to Azure Kubernetes Services through the Set Limits and Set Namespace Quotas directives. Eventually, the orchestrator would terminate the container or the pod, rather than firing another one, resulting into irrelevant additional costs and resources!
The figure below illustrates the application Resiliency by application in CAST Highlight, each application is represented by a bubble.
Modernize towards PaaS.
Once eShop applications are containerized on Windows AKS, it does not mean they are ready for PaaS.
CAST Highlight Portfolio Advisor for Cloud indicates that opportunities for modernization could be considered on eShop applications for an estimated effort of less than 2 person-days, allowing to benefit from Azure Cloud Services such as Azure Storage or Azure Batch. Parallelly, other services could be leveraged immediately such as Azure Monitor.
On eShop Applications, CAST Highlight detected 2 PaaS blockers. Firstly, hardcoded URLs using the HTTP protocol (HTTP/HTTPS) which would need to be replaced by the new resource’s URL during the refactoring. Secondly, use of Log4Net for application logs management which should be replaced by Azure Application Insights.
See live here in more details how CAST Highlight helps on the Migration to PaaS journey.
Transform the Architecture Design.
Going further in modernization, eShop applications could be ported to a more modern design on .NET 6 and the legacy UI components such as ASP.NET/MVC could be refactored to Blazor. CAST Imaging helps accelerate such modernization initiatives by providing architecture blueprints of applications and automatically creating a comprehensive knowledge repository.
Application teams are enabled to rapidly discover the as-is architecture design in detail and prepare the transformation project whether refactoring to PaaS, implementing technical improvements, or engaging in a deep re-architecture. See CAST Imaging live here.
Customer Case Studies
Below selected customer cases leveraging CAST for containerization:
Auto tech firm assesses cloud readiness of apps 5x faster with CAST Highlight : The client compared the time it took to manually assess a few well understood apps with CAST Highlight’s automated approach; the latter was five times faster with the same accuracy. CAST Highlight analyzed all 134 apps in under two days and produced insights including the cloud readiness of each app, specific blockers that needed to be remediated within the code par app, per move group, per business unit. CAST Highlight results were crucial for the many apps that did not have dedicated teams. Within five weeks, the client containerized 40 of their apps and developed a plan to complete the process for the rest of the portfolio with recommendations on cloud services that each app could adopt once migrated.
Head of Engineering at Major Asian e-commerce company engaged in containerizing ~300 applications (core and web/micro-services) declared that CAST helped reduce the dependencies identification in code to 3-4 weeks instead of 3-4 months and to 1.5-2 months to execute the migration instead of 3-4 months. CAST helped accelerate the onboarding i.e. shifting-left Annual Recurring Revenue.
Global media firm cuts cloud migration planning time in half with CAST Highlight : Thanks to well-understood apps, average app assessment time was cut in half when using the CAST Highlight’s automation versus manual code reviews. They progressed to less familiar apps and the time savings become even more significant: up to 5 times faster with CAST. It also identified nearly 50% of the applications that were good refactoring candidates for PaaS, enabling adoption of a cloud-native approach sooner than expected, even further reducing cloud consumption costs. Ultimately, the architect team was able to focus their efforts on high-value infrastructure and integration initiatives instead of manual code and framework reviews.
Conclusion
Migrating .NET applications on Windows Containers with Azure Kubernetes Service provides significant value but demands preliminary checks, especially for custom applications. CAST products help throughout the journey to Azure, from planning the containerization to the succeeding modernization once on Azure. CAST Highlight provides actionable insights at application and at portfolio level, 2 to 4 times faster than a manual approach, including blockers to be remediated. CAST Highlight acts as a control tower for the portfolio. CAST Imaging offers deep insights into application code, allowing you to confidently execute the modernization acting as a knowledge base of your software.
With CAST and Microsoft Azure as partners on the cloud journey, IT Leaders have the right solutions and expertise to retrieve knowledge of their custom applications, unblock the typical “discovery paralysis” in cloud migrations, then reach the full potential of their applications on Azure with less U-turns, higher responsiveness to business requests and better team efficiency while executing the transformation.
Next steps
For more details on CAST for cloud migration & modernization, please visit https://learn.castsoftware.com/faster-modernization-and-cloud-migration and https://www.castsoftware.com/highlight on CAST Highlight specifically.
If you wish to have your application(s) analyzed on CAST Highlight or CAST Imaging for migration to Azure, you may be eligible to Microsoft-funded CAST analysis through the Microsoft Solution Assessment program. Please contact your Microsoft representative or reach out to CAST on microsoft.contact-me@castsoftware.com.
Alternatively, you can purchase a CAST Highlight SaaS subscription on the Azure Marketplace to run the analysis by your own.
For any questions, please contact microsoft.contact-me@castsoftware.com.
Microsoft Tech Community – Latest Blogs –Read More