Category: Microsoft
Category Archives: Microsoft
How to Remove a Single Service Plan from Entra ID User Account Licenses with PowerShell
Some years ago, I wrote a script to demonstrate how to remove service plans from user account licenses with PowerShell. This article describes some upgrades to make the script even better by improving the code and leveraging complex Microsoft Graph queries against the license information stored for Entra ID user accounts. It’s PowerShell, so feel free to change the script!
https://office365itpros.com/2024/04/23/remove-service-plan-powershell-2/
Some years ago, I wrote a script to demonstrate how to remove service plans from user account licenses with PowerShell. This article describes some upgrades to make the script even better by improving the code and leveraging complex Microsoft Graph queries against the license information stored for Entra ID user accounts. It’s PowerShell, so feel free to change the script!
https://office365itpros.com/2024/04/23/remove-service-plan-powershell-2/
Read More
Install parameters for teams bot/message extension app on installation
Hello,
I would like the admin to be able to store the API key when installing the teams bot/message extension app. This API key should be unique for each organization. Is there a way to configure this on the installation popup?
Thank you.
Hello, I would like the admin to be able to store the API key when installing the teams bot/message extension app. This API key should be unique for each organization. Is there a way to configure this on the installation popup? Thank you. Read More
realtek network controller
hi
so tonight my comptuer woke from sleep mode and I had no internet. I checked my ethernet connection and the light was a solid orange. I tried ipconfig /all but the controller isn’t showing up. I then went to device manager and checked for it, it wasnt showing up there either. I then tried showing hidden devices and it showed up. When i checked the properties it says
“Currently, this hardware device is not connected to the computer. (Code 45) To fix this problem, reconnect this hardware device to the computer.”
I’ve tried everything i could think of. ran multiple windows troubleshooters, found the latest driver for “Realtek Gaming 2.5GbE Family Controller”, updated it, didnt work. I reset winsock, tried it in safe mode with networking and other stuff like flushing the dns and turning off fast boot.
I finally uninstalled the device completely and restarted, but upon restarting, it just disappeared completely from my device manager list instead of reinstalling. so I restored my pc back a couple days and now its back when i show hidden devices. i can still ping 127.0.0.1 with my wifi disabled but i can’t connect to the internet with a wired connection.
hiso tonight my comptuer woke from sleep mode and I had no internet. I checked my ethernet connection and the light was a solid orange. I tried ipconfig /all but the controller isn’t showing up. I then went to device manager and checked for it, it wasnt showing up there either. I then tried showing hidden devices and it showed up. When i checked the properties it says”Currently, this hardware device is not connected to the computer. (Code 45) To fix this problem, reconnect this hardware device to the computer.”I’ve tried everything i could think of. ran multiple windows troubleshooters, found the latest driver for “Realtek Gaming 2.5GbE Family Controller”, updated it, didnt work. I reset winsock, tried it in safe mode with networking and other stuff like flushing the dns and turning off fast boot. I finally uninstalled the device completely and restarted, but upon restarting, it just disappeared completely from my device manager list instead of reinstalling. so I restored my pc back a couple days and now its back when i show hidden devices. i can still ping 127.0.0.1 with my wifi disabled but i can’t connect to the internet with a wired connection. Read More
Community Efforts for Women in Tech in China
A special event that focused on AI technology and digitalization from a women’s point of view took place in China on March 8, International Women’s Day. This online event, held in partnership with the local Power Platform community and Microsoft Reactor, attracted more than 2,000 attendees.
Christina Liang, a Microsoft Community Program Manager, was instrumental in organizing the event from choosing the theme and speaker recruitment to being a panelist on the day. She shares her experience in the event, “On International Women’s Day, our dedicated event greatly contributed to women empowerment in our region by offering a skill enhancement opportunity in contemporary topics. This year’s focus topic was AI and digitalization from a woman’s perspective, and I joined a panel discussion with a panelist of women, Hui Zou (M365 MVP), Dan Zhang (CFO of an energy company), and the MVP moderator Liu Yu to energize the festivities. The panelists, who are CFO and HR experts, shared insights on how to use AI knowledge for real-world applications in the dialogue.”
Liu Yu, a Business Applications MVP in the Power Platform community who organized the event to support women empowerment, describes the key takeaway from the event as “the growing interest and efforts of women in HR and finance sectors towards AI and digitalization.” He states, ”I was inspired by seeing many women who actively engage in these fields and make strides towards leveraging technology. Looking ahead, we need to continue to support and invest resources in these areas and provide them with technical knowledge and practical experience to empower their further development. By sharing expertise and experiences, we can help their growth towards a more inclusive and successful future in the tech industry.”
This virtual event provided participants with an engaging platform to explore how technology can enhance various professional roles and foster career development. Christina remarks, “The engagement level was remarkably high, and the event successfully raised awareness of our program. It attracted a large number of attendees who are eager to learn about Microsoft technology, and we were able to deliver our message on this important day.”
The event garnered remarkable interest and acclaim. Liu summarized the overall feedback, stating, “The feedback was overwhelmingly positive, and we learned that attendees felt comfortable and are eager to join such sharing opportunities more. They expressed a desire for access to the latest cutting-edge knowledge from diverse communities and leaders in the future. Two industry expert guest speakers also got substantial benefits from this interaction, gaining fresh inspiration and knowledge that they plan to share within their respective fields and careers.”
This initiative also inspired Microsoft MVP attendees. “Many MVPs resonated with the insights shared by the guests. In particular, women MVPs showed their commitment to increased participation and contribution in the future,” says Liu.
Liu has been diligently engaging with women of the tech community. He elaborates on their participation within the community, stating, “Our community empowers many women speakers who are excellent knowledge producers. Not only are they technically proficient, but they are also enthusiastic about sharing knowledge and community building. Additionally, we have numerous volunteers, primarily university students. These young women actively participate in community events to stay abreast of technological advancements, engage with tech experts, acquire knowledge, and engage in extensive practice to master their skills. Among the community audience, we also have women from various societal backgrounds who actively participate in community sessions to gain knowledge and wisdom. They utilize these insights to enhance their abilities and broaden their perspectives.”
In terms of fostering diversity and inclusion in the community, this event was not just a one-off initiative but one of the ongoing community’s efforts. As a community leader dedicated to empowering women, Liu articulated his ongoing commitment to furthering women’s empowerment in future initiatives. “As a low-code community, we aim to share technical information benefiting more women in the future, especially professional women in various fields. They should be one of the most significant groups to benefit from Microsoft technologies. In the future, when we organize events, we would like to collaborate with Microsoft to increase resource allocation, enhance the impact of these initiatives, and ensure that the voices of women in tech are uplifted and heard.”
Microsoft Tech Community – Latest Blogs –Read More
Is there a way to give suggestions when user is typing in message box
When user is typing some characters in message box in teams bot, If we can give suggestions of all the objects which contain these characters. So It will be easier to type. The objects will be changed dynamic and more than 10, so “commands menu” can not meet our expectation.
“message extension search commands” is very similar with my expectation, but it can not be invoked from message box.
Could anyone please help give some suggestions?
When user is typing some characters in message box in teams bot, If we can give suggestions of all the objects which contain these characters. So It will be easier to type. The objects will be changed dynamic and more than 10, so “commands menu” can not meet our expectation. “message extension search commands” is very similar with my expectation, but it can not be invoked from message box. Could anyone please help give some suggestions? Read More
Failed Migration from Exchange Online
Error: EndpointNotFoundTransientException: The call to ‘https://mail.Test.com/EWS/mrsproxy.svc‘ failed because no service was listening on the specified endpoint. Error details: There was no endpoint listening at https://mail.Test.com/EWS/mrsproxy.svc that could accept the message. This is often caused by an incorrect address or SOAP action. See InnerException, if present, for more details. –> There was no endpoint listening at https://mail.Test.com/EWS/mrsproxy.svc that could accept the message. This is often caused by an incorrect address or SOAP action. See InnerException, if present, for more details.
Error: EndpointNotFoundTransientException: The call to ‘https://mail.Test.com/EWS/mrsproxy.svc’ failed because no service was listening on the specified endpoint. Error details: There was no endpoint listening at https://mail.Test.com/EWS/mrsproxy.svc that could accept the message. This is often caused by an incorrect address or SOAP action. See InnerException, if present, for more details. –> There was no endpoint listening at https://mail.Test.com/EWS/mrsproxy.svc that could accept the message. This is often caused by an incorrect address or SOAP action. See InnerException, if present, for more details. Read More
Powershell to get all licences
Hello
I am looking for a script that gives me all licences of a userlist.
The output should consist in:
DisplaynameUPNService PlanSkuPartNumberAccountSkuIdProductname
Do you have such a script?
Regards
JFM_12
HelloI am looking for a script that gives me all licences of a userlist. The output should consist in:DisplaynameUPNService PlanSkuPartNumberAccountSkuIdProductnameDo you have such a script?Regards JFM_12 Read More
AVD – prevent saving user credentials
I’m using Azure Virtual Desktop with the Remote Desktop client on my Windows machine.
I want to prevent the password from being saved when I’m logging in to Azure Virtual Desktop.
I found this group policy do not allow passwords to be saved in Remote Desktop Connection Client.
But this seems not to apply to the new Remote Desktop Client.
Is there something similar for the version im using ?
The only thing I can think of for now is that I could unsubscribe from the workspaces at the end of the day or reset. But that’s not suitable at all and very inconvenient.
I’m using Azure Virtual Desktop with the Remote Desktop client on my Windows machine.I want to prevent the password from being saved when I’m logging in to Azure Virtual Desktop. I found this group policy do not allow passwords to be saved in Remote Desktop Connection Client.But this seems not to apply to the new Remote Desktop Client.Is there something similar for the version im using ?The only thing I can think of for now is that I could unsubscribe from the workspaces at the end of the day or reset. But that’s not suitable at all and very inconvenient. Read More
Join tech enthusiasts at MS Build ’24: Exploring AI, Machine Learning, Azure, and More!
Hello and welcome to my first blog post! I’m Suniti, an enthusiastic Microsoft Learn Student Ambassador, pursing graduation in the field of Data Science. Today, I’m super excited to discuss the upcoming MS Build’24 event with all of you!
Join us in celebrating the 14th edition of MS Build, as Microsoft draws closer to celebrating its 50 Years of establishment next year, filled with innovation and challenges. So, let’s have a look at what’s in for you in this exciting event!
What’s the buzz About MS Build?
Ready to immerse yourself in all things AI, machine learning, Azure, Generative AI, and beyond? I am!
MS Build is an annual 3 day-long, conference organised by Microsoft. This year’s is all about “ How AI Will Shape Your Future?”. Microsoft Build promises you get an exclusive peek into the latest AI innovations. This year the schedule for the event is May 21 -24, 2024 for in-person and May 21 – 23, 2024 for online attendees.
What to Expect:
Brief of the most recent changes in Azure AI Services, Microsoft Fabric, .Net, and the Azure OpenAI Service.
Keynotes, live demos, and breakout sessions that will boost your minds from the experts of Microsoft.
Exclusive insights into emerging technologies from Microsoft.
Event swag and digital swag.
Microsoft Cloud Skills Challenge to enhance your learning journey.
Get a chance to connect with Industry experts and get answers to your questions.
Meet the Keynote Speakers:
Satya Nadella, CEO of Microsoft
Rajesh Jha, EVP
Scott Guthrie, EVP Cloud + AI
And many more!
Recapping MS Build 2023
Were you there in MS Build’23? If No, here is a recap of what new was introduced last year.
Window’s Copilot – Learn more
Bringing Bing to ChagGPT
Copilot and Plugins – Learn more
Helping Solve Humanity’s Greatest Challenges with AI Tools
Jugalbandi Chat Bot
Get Started with AI on Microsoft Azure – Learn more
These were the most liked and popular among developers. If you want to explore more, what was there for you. in MS Build’23. Click Here
The History of MS Build
Since its inception in 2011, Microsoft Build has been a beacon of innovation and collaboration. From Anaheim to Seattle, this annual gathering has evolved into a platform, uniting developers and technologists from every corner of the world.
How It Starts:
The conference is organized in a hybrid mode.
In-person: Microsoft Build will be held at the Seattle, corporate headquarters of Microsoft Corporation. It will cost you $1,825 to attend the session offline.
Online: Everyone around the world can attend the session, once you register you will receive a digital attendee pass and an email for confirmation.
The Keynote on the first day was led by the Microsoft CEO Satya Nadella addressing the press and developers. Then, there are breakout sessions led by Microsoft’s Minds, where you can learn new technologies. Thousands of developers from all over the world will attend, so it’s a great chance to network and make some connections too.
| Register now at Microsoft Build 2024
Building a Brighter Future
Microsoft always fosters a welcoming environment for all. Building AI solutions following Responsible AI principles and the opportunity to learn from and connect with diverse students and professionals from various countries, religions, genders, and races. Having been part of the community since April ’23, I’ve had as an MLSA. This experience has been enriching, allowing me to engage in a wide range of activities, from learning and teaching to sharing ideas and collaborating on projects.
So, are you ready to embark on your journey fuelled with AI? Join, along with me in the conversation at Microsoft Build 2024. See you there!
Resources
MS Build | Scaling Future
Wikipedia | History of MS Build
MS Developers | YouTube
Thanks for diving into the excitement with me! Let’s keep the conversation going as we look forward to Microsoft Build 2024. See you there!
Microsoft Tech Community – Latest Blogs –Read More
How to send a message to a specific user
I want to send a message to a specific user from external service using the user ID.
In the sample code, I can use “getPagedInstallations” to loop through all users.
—————————————–
—————————————–
I think this is bad performance.
Is there any other better way?
I want to send a message to a specific user from external service using the user ID. In the sample code, I can use “getPagedInstallations” to loop through all users.—————————————–const pagedData = await notificationApp.notification.getPagedInstallations( pageSize, continuationToken); const installations = pagedData.data;for (const target of installations) { …}—————————————– I think this is bad performance.Is there any other better way? Read More
Unveiling Generative AI Bulk Processing and Ingestion Pattern
Generative and embeddings models have taken the world by storm in recent years, producing high-quality natural language responses for various tasks and domains. Organizations, start-ups, and innovators across the world have been exploring the applications of this capability through prototyping, small-scale proof of concepts, and influencing text outputs through prompt engineering. As they gain more understanding of generative AI concepts such as context length, tokens, embeddings, and attention, as well as methods to avoid hallucinations, they discover new use cases and opportunities for leveraging this technology. One of the most popular and widely applicable use cases is search-based answer generation, which can enhance the user experience and satisfaction for any industry that relies on information retrieval and query answering.
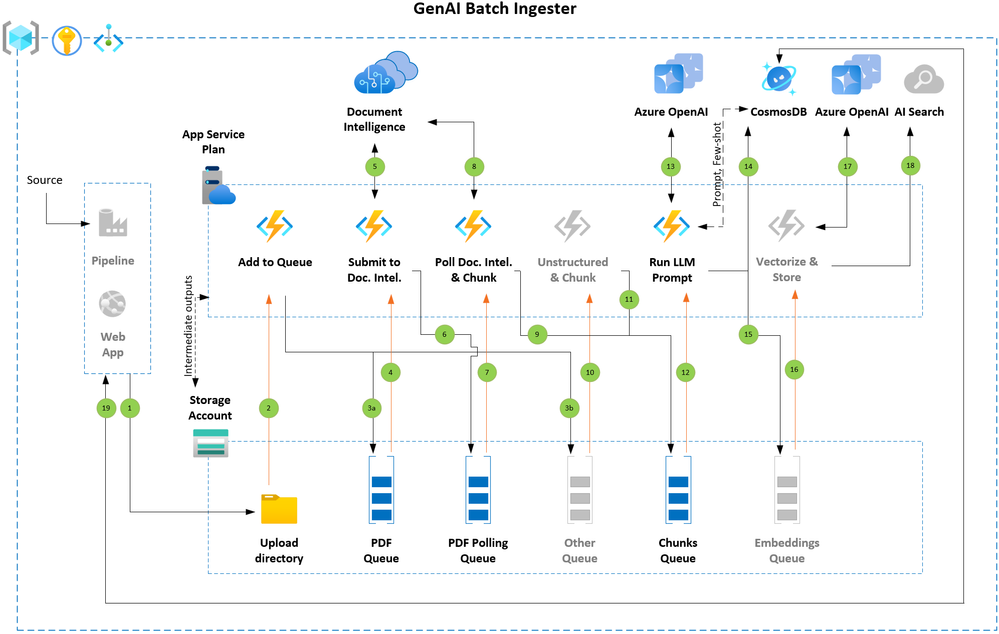
This technical blog describes a pattern for bulk processing and ingestion with generative AI, which can help organizations grow their generative AI solutions from prototype and proof of concept phases to pilot and production workloads. The described bulk processing and ingestion pattern leverages the parallel and distributed computing capabilities of Azure platform to generate and store large volumes of natural language responses based on a given set of PDF documents. The blog also provides a walkthrough of the sample code made available on the Github repository, which implements this pattern using Azure OpenAI, Azure Functions, Azure Queue Storage, Azure Document Intelligence, Azure CosmosDB and potentially Azure AI Search. The code can be easily customized and adapted to different generative AI models and use cases, such as knowledgebase population for search-based answer generation.
Architecture Overview
Figure 1: Key components and execution flow
The solution takes advantage of the event-driven processing paradigm. As soon as the input documents are uploaded to a designated Azure Storage location, they trigger an event that invokes Azure Functions written in Python to extract text from the documents. The extracted text is then split into smaller segments of text (based on a configurable token count value) and concatenated into larger segments (also configurable). This approach allows for flexibility in generating text at different levels of granularity, depending on the context length supported by the large language models (LLMs).
The concatenated segments are then processed in parallel, making API calls to one or more Azure OpenAI endpoints to apply a default prompt predefined in the Azure CosmosDB database. The prompt to be applied can be customized at the document level by adding its id to the blob metadata. If the document blob has a prompt_id metadata tag that points to a user-defined prompt value available in the Azure CosmosDB, then that prompt will be used. Otherwise, the default prompt (also configurable) will be applied. All intermediate outputs are stored in Azure Storage for traceability back to the source document. The text can also be vectorized and indexed by an AI Search service by cloning and modifying the Run LLM Prompt function. The vectorization step is not implemented in sample code.
Code components from different publicly available accelerators made by internal teams are reused in this solution. We thank them for their work.
Flow Details
Incremental offload (Step 1)
When processing large sets of documents, it is a best practice to split the work in small batches of documents and have them processed one set of documents at a time. You can build a simple pipeline that fetches and offloads the documents batch by batch into designated storage account container. Next batch can be added upon successful completion of previous. Alternatively, there could be use cases where you can offer upload functionality directly to users through a web application.
Queued for processing (Steps 2 and 3a)
Each arriving document triggers the Azure Function that queues the document to be submitted to Document Intelligence endpoint. The code implementation of this pattern currently supports processing of PDF files and can be easily extended to handle other file types.
Submitted to Document Intelligence (Steps 4, 5 and 6)
As the next step, the BLOB URL of the document is appended with a SAS token and submitted to Document Intelligence endpoint. The Document Intelligence API returns a unique identifier upon accepting the document for extracting the text. This unique identifier is passed to the next queue to keep polling the Document Intelligence endpoint until it has processed the document.
Verify that Document Intelligence processing is completed and chunk the text (Steps 7, 8 and 9)
The time to analyze a document depends on the size (for example, number of pages) and associated content on each page. This step keeps polling Document Intelligence until the status code 200 is received. Otherwise requeue the message to trigger a new instance of the check without looping inside the code. This is a powerful feature that queues offer. Once the status code 200 is received, the text response is chunked and details of the merged chunks are passed to the next que to apply prompt (or vectorize and ingest into AI Search) or any other task that you would like to accomplish as part of the flow.
Figure 2: Chunks queue message structure
Apply LLM prompt (Steps 12, 13, 14)
Each merged chunk is prefixed with system message (configurable) and default (or user defined) prompt retrieved from the Azure CosmosDB which acts as a metadata and information logging database. The updated prompt is passed to Azure OpenAI chat completion endpoint. The response from Azure OpenAI endpoint is saved into both Azure Storage and Azure CosmosDB. In case your use case requires few shot examples to be passed per prompt, you may store these few shot examples in the Azure CosmosDB and fetch them dynamically along with the prompt to be given to a large language model.
(Alternatively) Vectorize and ingest into AI Search (Steps 15, 16, 17, 18)
You could easily clone the Apply LLM prompt function to achieve embedding generation for the merged chunk and store each chunk as an AI Search document along with reference to the source document.
Intermediate outputs
Saving the outputs produced by each flow step is a best practice when a flow is broken into multiple steps. These outputs can be handy to re-run part of the flow by rehydrating the storage queue with messages. The provided sample code that implements this pattern stores all intermediate outputs in the Azure Storage.
Figure 3: After text is extracted by Document Intelligence API
Figure 4: Chunks are created
Figure 5: Prompt output
Addressing request throttling
The sample code in Github demonstrates use of multiple (you may also use a single) endpoints to distributes the request across Azure Document Intelligence and Azure OpenAI endpoints. Please see below additional considerations for mitigating the request throttling.
Azure Document Intelligence
Implement retry logic in your application.
If you find that you’re being throttled on the number of POST requests, consider adding a delay between the requests.
Increase the workload gradually. Avoid sharp changes.
Create a support request to increase transactions per second (TPS) limit.
Azure OpenAI
Implement client-side retry logic to wait the retry-after-ms time and retry.
Consider redirecting the traffic to other models, deployments.
Move quota from another deployment, if necessary.
Please review references section of this article for additional information links to product documentation.
Monitoring the progress
A detailed process log is maintained in the Azure CosmosDB at the granularity of each merged chunk. You can review the process logs and stay on top of the processing status by using NoSQL API for Azure CosmosDB. Sample queries are show below, you may write additional queries. For instance chunks that may have encountered error or were skipped and the supporting error message to perform further investigations.
Figure 6: View chunk progress log
Figure 7: LLM output saved in the Azure CosmosDB
Execution Times
Please see below the execution time for the test dataset and setup combinations in our sandbox environment. With each test we added more files and increased the infrastructure configuration to confirm the scaling aspect of this pattern. These numbers may vary based on your workload and implementation details – whether you are applying an LLM prompt to chunks or generating embeddings or doing both, chunk size, the output token size you have selected, the LLM model, etc.
References
GitHub Code sample – GenAI-Batch-Ingester
Azure OpenAI Service REST API reference
Azure OpenAI – Staying within rate limits
Azure OpenAI – PTU
Document Intelligence API
Document Intelligence – Mitigating throttling
Azure Queue storage trigger and bindings for Azure Functions
Microsoft Tech Community – Latest Blogs –Read More
Azure IoT hub & edge gateways
Hi,
We are evaluating azure IoT for implementing IoT pipeline for one of our customer.
We are looking for latest case study and implementation references, also we have few queries. Please help us with references and documentation.
1. Do we have any recent case study & Business cases references using the Azure IoT hub/edge?
2. Any sample case studies for implementing the IoT edge as gateways for protocol translation?
3. Do we have any recent reference for SDKs for Java/Python to build the Custom modules for translational gateways handling multiple protocol translations? GitHub we came across were atleast 2-4 years old.
4. Where can we find the details on defining the device and connect them to the IoT Edge gateway?
5. Do we have latest documentation on the IoT Edge Windows deployment?
Thanks,
Hi,We are evaluating azure IoT for implementing IoT pipeline for one of our customer. We are looking for latest case study and implementation references, also we have few queries. Please help us with references and documentation.1. Do we have any recent case study & Business cases references using the Azure IoT hub/edge?2. Any sample case studies for implementing the IoT edge as gateways for protocol translation?3. Do we have any recent reference for SDKs for Java/Python to build the Custom modules for translational gateways handling multiple protocol translations? GitHub we came across were atleast 2-4 years old.4. Where can we find the details on defining the device and connect them to the IoT Edge gateway?5. Do we have latest documentation on the IoT Edge Windows deployment? Thanks, Read More
Looking value in another sheet and returns the ID
Hi All,
I have excel file in that i have 2 sheets S1 (orange) & S2 (blue). I have CID column in S2 and I want to check D column value of S2 in C column of S1 and then i want to return the ID in CID column
for example, I have 5 entries in S2 sheet
BadakhshanAfghanistanBadakhshanAfghanistanBadakhshanAfghanistanBadakhshanAfghanistanBadakhshanAfghanistanBadakhshanAfghanistan
and in S1 i have this
CONCAT2ID
BadakhshanAfghanistan1
So I want the result in S2 to be
CONCAT1 CID
BadakhshanAfghanistan1BadakhshanAfghanistan1BadakhshanAfghanistan1BadakhshanAfghanistan1BadakhshanAfghanistan1BadakhshanAfghanistan1
i have added excel sheet as well for your reference. Thanks 🙂
Hi All, I have excel file in that i have 2 sheets S1 (orange) & S2 (blue). I have CID column in S2 and I want to check D column value of S2 in C column of S1 and then i want to return the ID in CID column for example, I have 5 entries in S2 sheetBadakhshanAfghanistanBadakhshanAfghanistanBadakhshanAfghanistanBadakhshanAfghanistanBadakhshanAfghanistanBadakhshanAfghanistan and in S1 i have this CONCAT2IDBadakhshanAfghanistan1 So I want the result in S2 to beCONCAT1 CIDBadakhshanAfghanistan1BadakhshanAfghanistan1BadakhshanAfghanistan1BadakhshanAfghanistan1BadakhshanAfghanistan1BadakhshanAfghanistan1 i have added excel sheet as well for your reference. Thanks 🙂 Read More
Start and Wait for approval
I want to utilize the functionality provided by the Microsoft Graph API to initiate and await approval for timesheets stored in SharePoint. Could someone please assist me in understanding the process for implementing this?
I want to utilize the functionality provided by the Microsoft Graph API to initiate and await approval for timesheets stored in SharePoint. Could someone please assist me in understanding the process for implementing this? Read More
Update 2403 for Microsoft Configuration Manager current branch is now available.
Update 2403 for Configuration Manager current branch is available as an in-console update. Apply this update on sites that run version 2211 or later. When installing a new site, it will also be available as a baseline version soon after general availability. This article summarizes the changes and new features in Configuration Manager, version 2403.
Site infrastructure
Starting Configuration Manager version 2403, Microsoft Azure Active Directory is renamed to Microsoft Entra ID within Configuration Manager.
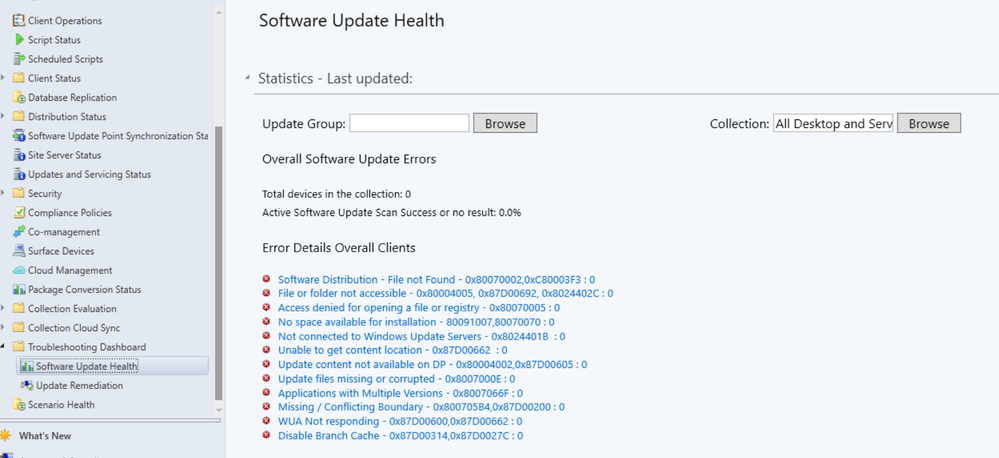
Automated diagnostic Dashboard for Software Update Issues
A new dashboard is added to the console under monitoring workspace, which shows the diagnosis of the software update issues in your environment this feature can easily identify any issues related to software updates. You can fix software update issues based on troubleshooting documentations.
Special credit to Shankar Subramanian and Smita Jadhav for their details and troubleshooting notes.
For more information, see Software update health dashboard.
Users can now use the global search box in CM console, which streamlines the search experience and centralizes access to information. This feature enhances the overall usability, productivity and effectiveness of CM. Users no longer need to navigate through multiple nodes or sections/ folders to find information they require, saving valuable time and effort.
For more information, see Improvements to console search.
You can now organize scripts by using folders. This change allows for better categorization and management of scripts. Full Administrator and Operations Administrator roles can manage the folders.
For more information, see Folder support for scripts.
HTTPS or Enhanced HTTP should be enabled for client communication from this version of Configuration Manager
HTTP-only communication is deprecated, and support is removed from this version of Configuration Manager. Enable HTTPS or Enhanced HTTP for client communication.
For more information, see Enable site system roles for HTTPS or Enhanced HTTP. and Deprecated features
Windows Server 2012/2012 R2 operating system site system roles are not supported from this version of Configuration Manager
Starting 2403, Windows Server 2012/2012 R2 operating system site system roles aren’t supported in any CB releases. Clients with extended support (ESU) will continue to support.
For more information, see Supported-operating-systems-for-site-system-servers.
Any configured Resource access profiles and deployments block Configuration manager upgrade. Consider deleting them and moving the co-management workload for Resource Access (if co-managed) to Intune.
For more information, see FAQ and Resource access policies are no longer supported.
A new parameter SoftwareUpdateO365Language is now added to PowerShell Save-CMSoftwareUpdate cmdlet. Customers now don’t have to check a specific language in the SUP Properties (causing a metadata download for that language for all updates).
PowerShell Commandlet: Save-CMSoftwareUpdate – SoftwareUpdateO365Language <language name> (<region name>)”
Note
Languages need to be in O365 format to be consistent with Admin Console UI. E.g. “Hungarian (Hungary)”.
Configuration Manager operating system deployment support is now added on Windows 11 ARM 64 devices. Currently Importing and customizing Arm 64 boot images, Wipe and load TS, Media creation TS, WDS PXE for Arm 64 and CMPivot is supported.
Administrators while deploying the “Install Software Package” via Dynamic variable with “Continue on error” unchecked to clients, will not be notified with task sequence failures even if package versions on the distribution point are updated.
For more information, see Options for Install Application.
The option to upgrade Configuration Manager 2403 is blocked if you’re running cloud management gateway V1 (CMG) as a cloud service (classic). All CMG deployments should use a virtual machine scale set.
For more information, see Check for a cloud management gateway (CMG) as a cloud service (classic).
Learn about support changes before they’re implemented in removed and deprecated items.
System Center Update Publisher (SCUP) and integration with ConfigMgr planned end of support Jan 2024.
For more information, see Removed and deprecated features for Configuration Manager.
This release includes the following improvements to BitLocker:
Starting in this release, this feature ensures proper verification of key escrow and prevents message drops. We now validate whether the key is successfully escrowed to the database, and only on successful escrow we add the key protector.
This feature now prevents a potential data loss scenario where BitLocker is protecting the volumes with keys that are never backed up to the database, in any failures to escrow happens.
For more information on BitLocker management, see Deploy BitLocker management. and Plan for BitLocker management..
From this version of Configuration Manager, the Windows 11 readiness dashboard shows charts for Windows 23H2.
Defender Exploit Guards policy for controlled folder now accepts regex in the file path for apps. For example, [C:FolderSubfolderapp?.exe] [C:Folder1Sub*Name]
At this time, version 2403 is released for the early update ring. To install this update, you need to opt in. For more information, see Early update ring.
Thank you,
The Configuration Manager team
Additional resources:
What’s New in Configuration Manager
Documentation for Configuration Manager
Microsoft Configuration Manager announcement
Microsoft Configuration Manager vision statement
Evaluate Configuration Manager in a lab
Upgrade to Configuration Manager
Configuration Manager Forums
Configuration Manager Support
Report an issue
Provide suggestions
Microsoft Tech Community – Latest Blogs –Read More
Wired for Hybrid – What’s New in Azure Networking – April 2024 edition
Hello Folks,
Azure Networking is the foundation of your infrastructure in Azure. Each month we bring you an update on What’s new in Azure Networking.
In this blog post, we’ll cover what’s new with Azure Networking in April 2024. In this blog post, we will cover the following announcements and how they can help you.
Listener TLS certificates management in the Azure portal
Application Gateway for Containers
Application Gateway (v2) IPv6 support
Microsoft open sources Retina: A cloud-native container networking observability platform
Azure Virtual Network encryption now in additional regions
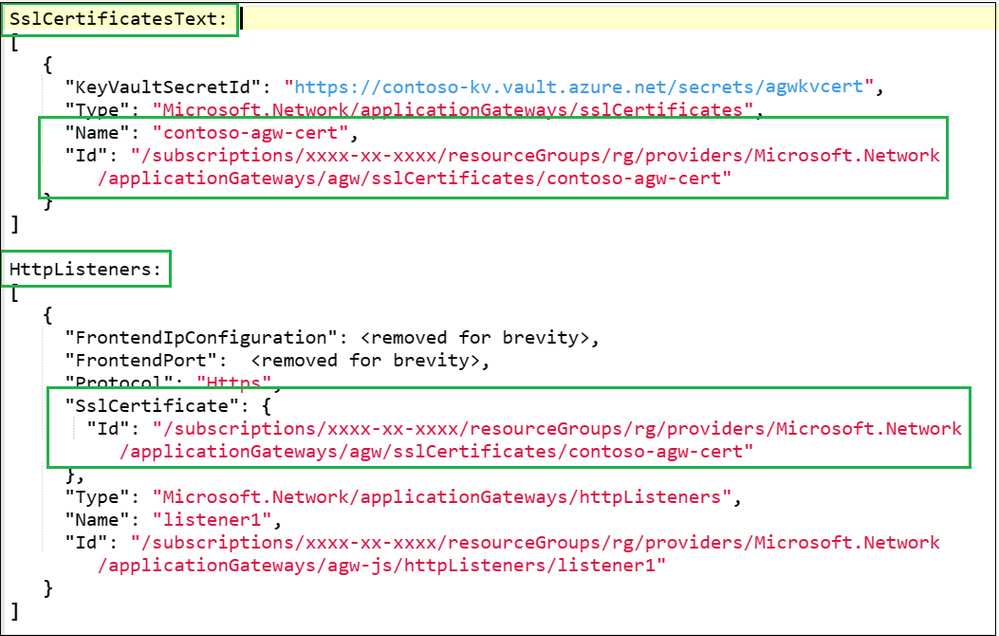
Listener TLS certificates management in the Azure portal
With this GA release, you can more easily manage TLS certificates for your Application Gateway workloads in the Azure Portal.
The Azure Application Gateway is a proxy load balancer that operates at Layer-7, the application layer of the OSI model. Now it supports Layer-4 proxy with TCP and TLS protocols as well. This provides scalable, highly available, and secure application delivery. One of its key features is the ability to secure client traffic through TLS termination, which requires TLS server certificates for listeners. For large gateways with multiple HTTPS or TLS listeners, this means managing multiple .PFX certificates.
For certificate management in the portal, you can list and manage your certificates.
Expiry
Common Name
Thumbprint
Issuer Name
Each certificate includes the following details for quick identification:
Managing certificates in any organization can be a challenge. This is a great addition for reducing friction for admins responsible for secure workloads utilizing certificates.
References:
Application Gateway TCP/TLS proxy overview (Preview)
Listener TLS certificate management in Application Gateway
Quickstart: Direct web traffic using the portal – Azure Application Gateway
TLS termination with Azure Key Vault certificates
General availability: Application Gateway for Containers
Application Gateway for Containers is GA. With this release, you get application (layer 7) load balancing and dynamic traffic management capabilities for workloads running in a Kubernetes cluster.
Application Gateway for Containers is the evolution of the Application Gateway Ingress Controller (AGIC), a Kubernetes application that enables Azure Kubernetes Service (AKS) customers to use Azure’s native Application Gateway application load-balancer. In its current form, AGIC monitors a subset of Kubernetes Resources for changes and applies them to the Application Gateway, utilizing Azure Resource Manager (ARM).
Features – Public preview and GA has added support for Custom Health Probes, URL Redirect, URL / Header Rewrite.
Controller High Availability – Have peace of mind if a node goes down, changes within your cluster will continue to be propagated to the network.
Gateway API v1 – Bring the familiarity and role based access control provided by Gateway API to your network configuration.
Additional Region Availability – Take advantage of Application Gateway for Containers in a region closest to you.
SLA for Production Workloads – Feel confident in running your production workloads with Application Gateway for Containers.
References:
What is Application Gateway for Containers?
Application Gateway for Containers components
Quickstart: Deploy Application Gateway for Containers ALB Controller
What is Azure Application Gateway Ingress Controller?
Application Gateway (v2) IPv6 support
We are announcing that IPv6 support for Azure Application Gateway (v2) is now generally available.
With the addition of IPv6 support, you can take advantage of the increased address space and improved routing efficiency that IPv6 provides. This is especially important for customers who are running out of IPv4 addresses or who need to support IPv6 clients.
To get started with IPv6 support for Azure Application Gateway (v2), simply create a new Application Gateway and select both IPv4 and IPv6 frontends during the creation process. You can also find more information about IPv6 support in our documentation.
References:
Configure Application Gateway with a frontend public IPv6 address using the Azure portal
What is Azure Application Gateway v2?
Microsoft open sources Retina: A cloud-native container networking observability platform
Retina is an open-source Kubernetes Network Observability platform designed to assist with DevOps, SecOps, and compliance use cases. It acts as a centralized hub for monitoring the health, security, and performance of applications and networks within Kubernetes clusters. The platform caters to Cluster Network Administrators, Cluster Security Administrators, and DevOps Engineers.
Provides actionable network insights for cloud-native applications: Retina offers users a way to see how their containerized microservices interact on the network, helping them troubleshoot issues like latency, packet drops and many more.
Non-intrusive and easy to use: Retina works with existing applications without requiring any code changes and provides users with simple ways to observe and troubleshoot network issues.
Supports diverse environments: Designed to be adaptable, Retina works seamlessly with any CNI’s (container network interface), OS, or cloud provider, making it a valuable tool across different environments.
Resources:
Introduction to Retina
Microsoft open sources Retina: Announcement
Azure Virtual Network encryption now in additional regions
Whenever Azure customer traffic moves between datacenters, Microsoft applies a data-link layer encryption method using the IEEE 802.1AE MAC Security Standards (MACsec). This encryption is implemented to secure the traffic outside physical boundaries not controlled by Microsoft or on behalf of Microsoft. This method is applied from point-to-point across the underlying network hardware. Virtual network encryption enables you to encrypt traffic between Virtual Machines and Virtual Machines Scale Sets within the same virtual network. It also encrypts traffic between regionally and globally peered virtual networks. Virtual network encryption enhances existing encryption in transit capabilities in Azure.
With Virtual Network encryption, customers can enable encryption of traffic between Virtual Machines and Virtual Machines Scale Sets within the same virtual network and between regionally and globally peered virtual networks. This new feature enhances the existing encryption in transit capabilities in Azure.
Azure Virtual Network encryption is available in the following additional regions:
West Us
West US 2
East US 2
US East
Europe North
Europe West
France Central
India Central
UAE North
East Asia
Japan West
Japan East
Resources:
What is Azure Virtual Network?
What is Azure Virtual Network encryption?
That’s it for this month.
Cheers
Pierre
Microsoft Tech Community – Latest Blogs –Read More
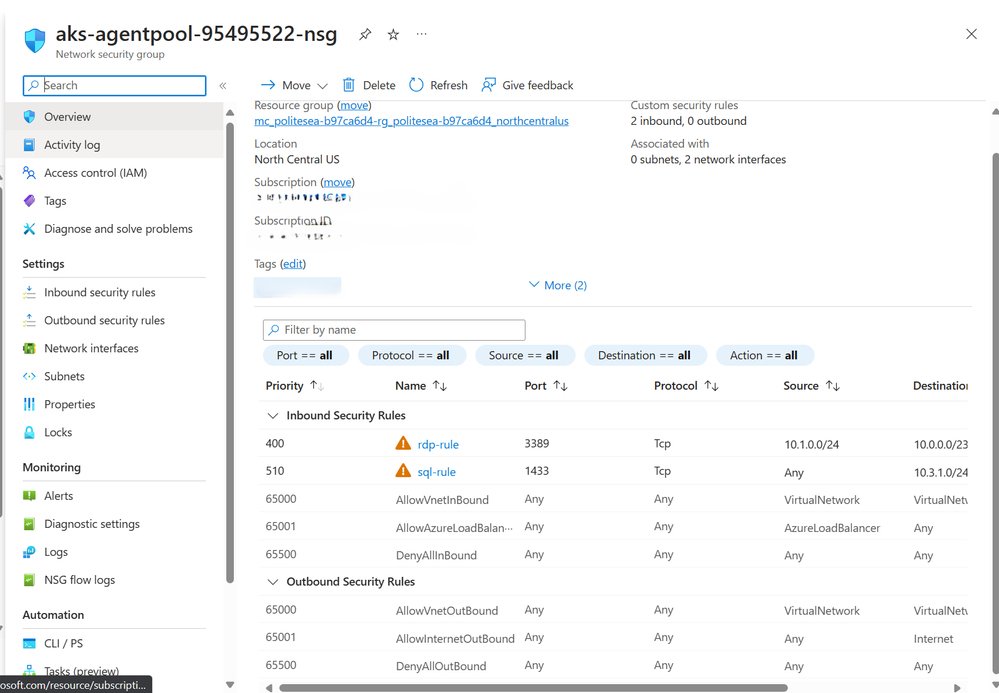
Perform bulk NSG rule rollout across multiple target NSGs
Network Security Groups (NSGs) are a fundamental aspect of Azure networking, providing a layer of security to control traffic flow within virtual networks. However, managing NSG rules across multiple NSGs can be a daunting task, especially when done manually. This article introduces a powerful PowerShell script that allows you to perform bulk NSG rule rollouts across multiple target NSGs, saving you time and ensuring consistency across your network.
The Challenge
In a large-scale Azure environment, you may have hundreds or even thousands of NSGs, each with its own set of rules. Updating these rules manually is not only time-consuming but also prone to errors. Furthermore, it’s difficult to ensure consistency across all NSGs, which is crucial for maintaining a secure and reliable network.
Scenario
The requirements were to empower the customers using an automation that could perform the mass assignment, updating, or deletion of the NSG rules across a set of NSGs. The NSG rules would have a common definition across all the NSGs except the source address prefix range and the destination address prefix range that would change based on the NSGs subnet address range, and if the rule’s direction is outbound or inbound.
The Solution
The solution consists of three PowerShell scripts that perform add, update, and delete operations on Network Security Group (NSG) rules in Azure.
Add Operation
Our PowerShell script, nsg_rule_add_csv.ps1, simplifies the process of adding NSG rules in bulk. The script reads from a CSV file, nsg_rule_definitions.csv, which contains the definitions of the rules to be added. It then applies these additions to the target NSGs specified in another CSV file, target_nsgs.csv. If the rule already exists in the NSG, the script skips the addition. Otherwise, it adds the rule to the NSG. Find the code for nsg_rule_add_csv.ps1.
function Add-NsgRule ($SubscriptionId, $ResourceGroup, $NsgName, $ruleDefinition, $SubnetAddressPrefix) {
if ($ruleDefinition.Direction -ieq ‘Inbound’) {
$rule = New-AzNetworkSecurityRuleConfig -Name $ruleDefinition.Name -Description $ruleDefinition.Description -Priority $ruleDefinition.Priority -Direction $ruleDefinition.Direction -Access $ruleDefinition.Access -SourceAddressPrefix $ruleDefinition.SourceAddressPrefix -SourcePortRange $ruleDefinition.SourcePortRange -DestinationAddressPrefix $subnetAddressPrefix -DestinationPortRange $ruleDefinition.DestinationPortRange -Protocol $ruleDefinition.Protocol
} elseif ($ruleDefinition.Direction -ieq ‘Outbound’) {
$rule = New-AzNetworkSecurityRuleConfig -Name $ruleDefinition.Name -Description $ruleDefinition.Description -Priority $ruleDefinition.Priority -Direction $ruleDefinition.Direction -Access $ruleDefinition.Access -SourceAddressPrefix $subnetAddressPrefix -SourcePortRange $ruleDefinition.SourcePortRange -DestinationAddressPrefix $ruleDefinition.DestinationAddressPrefix -DestinationPortRange $ruleDefinition.DestinationPortRange -Protocol $ruleDefinition.Protocol
}
Try {
# Switch the context to the appropriate subscription
Set-AzContext -SubscriptionId $SubscriptionId -ErrorAction Stop
$nsg = Get-AzNetworkSecurityGroup -Name $NsgName -ResourceGroupName $ResourceGroup -ErrorAction Stop
$nsg.SecurityRules.Add($rule)
Set-AzNetworkSecurityGroup -NetworkSecurityGroup $nsg -ErrorAction Stop
Write-Host “Rule added to NSG: $NsgName ($ResourceGroup)”
$timestamp = Get-Date -Format “yyyy-MM-dd_HH-mm-ss”
$logEntry = “$timestamp, $($ruleDefinition.Name), $nsgName, $ResourceGroup, Added Successfully”
$logFileName = “$($run_time)_$($ruleDefinition.Name)_add_success.log”
Add-Content -Path “.$logFileName” -Value $logEntry
} Catch {
$timestamp = Get-Date -Format “yyyy-MM-dd_HH-mm-ss”
$logEntry = “$timestamp, $($NsgName), $($_.Exception.Message)”
$logFileName = “$($run_time)_$($ruleDefinition.Name)_add_fail.log”
Add-Content -Path “.$logFileName” -Value $logEntry
Write-Error “Failed to add rule to NSG: $NsgName ($ResourceGroup) – $($_.Exception.Message)”
}
}
Update Operation
Our PowerShell script, nsg_rule_update_csv.ps1, simplifies the process of updating NSG rules in bulk. The script reads from a CSV file, nsg_rule_definitions_update.csv, which contains the rule definitions to be updated. It then applies these updates to the target NSGs specified in another CSV file, target_nsgs.csv. If the rule exists in the NSG, and the rule name (immutable) and old rule priority (additional input in the nsg_rule_definitions_update.csv for validating the rule before update operation) matches, the script updates the rule to the new rule definition. If the rule doesn’t exist, it logs an error message. Find the code for nsg_rule_update_csv.ps1.
function Update-NsgRule ($SubscriptionId, $ResourceGroup, $NsgName, $ruleDefinition, $subnetaddrprefix) {
Try {
# Switch the context to the appropriate subscription
Set-AzContext -SubscriptionId $SubscriptionId
# Get the Network Security Group
$nsg = Get-AzNetworkSecurityGroup -Name $NsgName -ResourceGroupName $ResourceGroup -ErrorAction Stop
$existingRule = Get-AzNetworkSecurityRuleConfig -Name $ruleDefinition.Name -NetworkSecurityGroup $nsg -ErrorAction Stop
if ($existingRule) {
# if existing PN= OLd PN-> Update
# existing PN != OLd PN -> throw error
if ($existingRule.Priority -eq $ruleDefinition.OldPriority) {
$existingRule.Priority = $ruleDefinition.Priority
$existingRule.Direction = $ruleDefinition.Direction
$existingRule.SourceAddressPrefix = [System.Collections.Generic.List[string]]@($ruleDefinition.SourceAddressPrefix)
$existingRule.DestinationAddressPrefix = [System.Collections.Generic.List[string]]@($ruleDefinition.DestinationAddressPrefix)
$existingRule.SourcePortRange = [System.Collections.Generic.List[string]]@($ruleDefinition.SourcePortRange)
$existingRule.DestinationPortRange = [System.Collections.Generic.List[string]]@($ruleDefinition.DestinationPortRange)
$existingRule.Description = $ruleDefinition.Description
$existingRule.Protocol = $ruleDefinition.Protocol
$existingRule.Access = $ruleDefinition.Access
if ($ruleDefinition.Direction -ieq ‘Inbound’ ) {
$existingRule.DestinationAddressPrefix = [System.Collections.Generic.List[string]]@($subnetaddrprefix)
} elseif ($ruleDefinition.Direction -ieq ‘Outbound’) {
$existingRule.SourceAddressPrefix = [System.Collections.Generic.List[string]]@($subnetaddrprefix)
}
# Update the existing rule
$nsg | Set-AzNetworkSecurityRuleConfig -Name $existingRule.Name -Description $existingRule.Description -Access $existingRule.Access -Protocol $existingRule.Protocol -Direction $existingRule.Direction -Priority $existingRule.Priority -SourceAddressPrefix $existingRule.SourceAddressPrefix -SourcePortRange $existingRule.SourcePortRange -DestinationAddressPrefix $existingRule.DestinationAddressPrefix -DestinationPortRange $existingRule.DestinationPortRange -ErrorAction Stop
# Save the changes to the Network Security Group
$nsg | Set-AzNetworkSecurityGroup -ErrorAction Stop
$timestamp = Get-Date -Format “yyyy-MM-dd_HH-mm-ss”
$logEntry = “$timestamp, $($ruleDefinition.Name), $nsgName, $ResourceGroup, Updated Successfully”
$logFileName = “$($run_time)_$($ruleDefinition.Name)_update_success.log”
Add-Content -Path “.$logFileName” -Value $logEntry
Write-Host “Rule updated in NSG: $NsgName ($ResourceGroup)”
}
else{
$errorMessage = “Cannot update the rule in NSG: $NsgName ($ResourceGroup) – Priority does not match for rule in NSG.”
Write-Error $errorMessage
$logFileName = “$($run_time)_$($ruleDefinition.Name)_update_fail.log”
Add-Content -Path “.$logFileName” -Value $logEntry
}
}
else {
Write-Error “Rule ‘$($ruleDefinition.Name)’ not found in NSG: $NsgName ($ResourceGroup)”
$timestamp = Get-Date -Format “yyyy-MM-dd_HH-mm-ss”
$logEntry = “$timestamp, $($NsgName), Rule not found in NSG.”
$logFileName = “$($run_time)_$($ruleDefinition.Name)_update_fail.log”
Add-Content -Path “.$logFileName” -Value $logEntry
}
}
Catch {
$timestamp = Get-Date -Format “yyyy-MM-dd_HH-mm-ss”
$logEntry = “$timestamp, $($NsgName), $($_.Exception.Message)”
$logFileName = “$($run_time)_$($ruleDefinition.Name)_update_fail.log”
Add-Content -Path “.$logFileName” -Value $logEntry
Write-Error “Failed to update rule in NSG: $NsgName ($ResourceGroup) – $($_.Exception.Message)”
}
}
Delete Operation
Our PowerShell script, nsg_rule_delete_csv.ps1, simplifies the process of deleting NSG rules in bulk. The script reads from a CSV file, nsg_rule_definitions.csv, which contains the definitions of the rules to be deleted. It then applies these deletions to the target NSGs specified in another CSV file, target_nsgs.csv. The script verifies if the existing rule’s name and priority matches the priority specified in the rule definition. If they match, the script removes the rule. If they don’t match, it logs an error message. Find the code for nsg_rule_delete_csv.ps1.
function Remove-NsgRule ($SubscriptionId, $ResourceGroup, $NsgName, $ruleDefinition) {
Try {
# Switch the context to the appropriate subscription
Set-AzContext -SubscriptionId $SubscriptionId -ErrorAction Stop
# Get the Network Security Group
$nsg = Get-AzNetworkSecurityGroup -Name $NsgName -ResourceGroupName $ResourceGroup -ErrorAction Stop
# Get the rule
$rule = Get-AzNetworkSecurityRuleConfig -Name $ruleDefinition.Name -NetworkSecurityGroup $nsg -ErrorAction Stop
# Check if the priority matches the user-provided priority
if ($rule.Priority -eq $ruleDefinition.Priority) {
# Remove the rule
$nsg | Remove-AzNetworkSecurityRuleConfig -Name $ruleDefinition.Name -ErrorAction Stop
$nsg | Set-AzNetworkSecurityGroup -ErrorAction Stop
$timestamp = Get-Date -Format “yyyy-MM-dd_HH-mm-ss”
$dateOnly = $timestamp.Substring(0, 10)
$logEntry = “$timestamp, $($ruleDefinition.Name), $nsgName, $ResourceGroup, Updated Successfully”
$logFileName = “$($run_time)_$($ruleDefinition.Name)_delete_success.log”
$logFileName = $logFileName -replace ‘[/:*?”<>|]’, ‘_’ # replace invalid characters
Add-Content -Path “.$logFileName” -Value $logEntry
Write-Host “Rule removed from NSG: $NsgName ($ResourceGroup)”
} else {
Write-Error “Priority does not match for rule in NSG: $NsgName ($ResourceGroup)”
$timestamp = Get-Date -Format “yyyy-MM-dd_HH-mm-ss”
$logEntry = “$timestamp, $($NsgName), Priority does not match for rule in NSG.”
$logFileName = “$($run_time)_$($ruleDefinition.Name)_delete_fail.log”
Add-Content -Path “.$logFileName” -Value $logEntry
}
} Catch {
$timestamp = Get-Date -Format “yyyy-MM-dd_HH-mm-ss”
$logEntry = “$timestamp, $($NsgName), $($_.Exception.Message)”
$logFileName = “$($run_time)_$($ruleDefinition.Name)_delete_fail.log”
Add-Content -Path “.$logFileName” -Value $logEntry
Write-Error “Failed to remove rule from NSG: $NsgName ($ResourceGroup) – $($_.Exception.Message)”
}
}
In all three scripts, the operations are performed using the Azure PowerShell module. The scripts also handle errors and log them to a file. The scripts prompt the user for confirmation before performing the operations. This way, you can easily manage NSG rules across multiple target NSGs, saving time and ensuring consistency across your network.
How It Works
The script works on the principle that the rules to be added, updated or modified must be consistent across all the target NSGs. For this, the script validates the rules for mass rollout on two baseline rule definition parameters i.e. rule name and rule priority, only on successful validation of these baseline, the script performs the required operations. For instance, the general flow of the nsg_rule_delete_csv.ps1 begins by prompting the user for confirmation, as the operation is irreversible. Once the user confirms, the script loops through each target NSG. For each NSG, it checks if the required variables (subscription ID, resource group, and NSG name) are null or empty. If they are, it logs an error message to a log file and skips to the next NSG.
Next, the script prints a message indicating that it’s deleting the rule from the NSG. It then loops through each rule definition and calls the Remove-NsgRule function to delete the rule.
If the user chooses not to proceed with the deletion, the script prints a message indicating that the operation was cancelled by the user.
Finally, the script prints a message indicating that it has completed. (Source: code repository)
Conclusion
With our PowerShell script, you can easily perform bulk NSG rule rollouts across multiple target NSGs. This not only saves you time but also ensures consistency across your network, enhancing its security and reliability.
Azure Portal: Manage your NSG rules at bulk
Stay tuned for more articles on how to automate and simplify your Azure networking tasks!
Microsoft Tech Community – Latest Blogs –Read More
print only odd pages?
In Excel, how do I print only odd pages? I’m on a pc.
In Excel, how do I print only odd pages? I’m on a pc. Read More
Azure Migrate availability for Southeast Asia
Just to check whether any of you facing any issue on testing Azure Migrate in Southeast Asia region ?
I’m facing a issue where the Azure Migrate dashboard can’t identify the “source appliance” that configured and discovering the VMs on source location, which causing problem on setting up “Target appliance”.
Just to check whether any of you facing any issue on testing Azure Migrate in Southeast Asia region ? I’m facing a issue where the Azure Migrate dashboard can’t identify the “source appliance” that configured and discovering the VMs on source location, which causing problem on setting up “Target appliance”. Read More