Tag Archives: microsoft
Why does a query fail when there is no error? | SQL Server 2022 Hidden Gems | Data Exposed
Join us in this episode of Data Exposed: SQL Server 2022 Hidden Gems to learn about the first hidden gem engineers put into the product that you may find helpful.
Resources:
What’s new in SQL Server 2022 (16.x)
Microsoft Tech Community – Latest Blogs –Read More
Why does a query fail when there is no error? | SQL Server 2022 Hidden Gems | Data Exposed
Join us in this episode of Data Exposed: SQL Server 2022 Hidden Gems to learn about the first hidden gem engineers put into the product that you may find helpful.
Resources:
What’s new in SQL Server 2022 (16.x)
Microsoft Tech Community – Latest Blogs –Read More
Why does a query fail when there is no error? | SQL Server 2022 Hidden Gems | Data Exposed
Join us in this episode of Data Exposed: SQL Server 2022 Hidden Gems to learn about the first hidden gem engineers put into the product that you may find helpful.
Resources:
What’s new in SQL Server 2022 (16.x)
Microsoft Tech Community – Latest Blogs –Read More
Why does a query fail when there is no error? | SQL Server 2022 Hidden Gems | Data Exposed
Join us in this episode of Data Exposed: SQL Server 2022 Hidden Gems to learn about the first hidden gem engineers put into the product that you may find helpful.
Resources:
What’s new in SQL Server 2022 (16.x)
Microsoft Tech Community – Latest Blogs –Read More
Why does a query fail when there is no error? | SQL Server 2022 Hidden Gems | Data Exposed
Join us in this episode of Data Exposed: SQL Server 2022 Hidden Gems to learn about the first hidden gem engineers put into the product that you may find helpful.
Resources:
What’s new in SQL Server 2022 (16.x)
Microsoft Tech Community – Latest Blogs –Read More
Why does a query fail when there is no error? | SQL Server 2022 Hidden Gems | Data Exposed
Join us in this episode of Data Exposed: SQL Server 2022 Hidden Gems to learn about the first hidden gem engineers put into the product that you may find helpful.
Resources:
What’s new in SQL Server 2022 (16.x)
Microsoft Tech Community – Latest Blogs –Read More
Why does a query fail when there is no error? | SQL Server 2022 Hidden Gems | Data Exposed
Join us in this episode of Data Exposed: SQL Server 2022 Hidden Gems to learn about the first hidden gem engineers put into the product that you may find helpful.
Resources:
What’s new in SQL Server 2022 (16.x)
Microsoft Tech Community – Latest Blogs –Read More
Why does a query fail when there is no error? | SQL Server 2022 Hidden Gems | Data Exposed
Join us in this episode of Data Exposed: SQL Server 2022 Hidden Gems to learn about the first hidden gem engineers put into the product that you may find helpful.
Resources:
What’s new in SQL Server 2022 (16.x)
Microsoft Tech Community – Latest Blogs –Read More
Why does a query fail when there is no error? | SQL Server 2022 Hidden Gems | Data Exposed
Join us in this episode of Data Exposed: SQL Server 2022 Hidden Gems to learn about the first hidden gem engineers put into the product that you may find helpful.
Resources:
What’s new in SQL Server 2022 (16.x)
Microsoft Tech Community – Latest Blogs –Read More
Why does a query fail when there is no error? | SQL Server 2022 Hidden Gems | Data Exposed
Join us in this episode of Data Exposed: SQL Server 2022 Hidden Gems to learn about the first hidden gem engineers put into the product that you may find helpful.
Resources:
What’s new in SQL Server 2022 (16.x)
Microsoft Tech Community – Latest Blogs –Read More
Why does a query fail when there is no error? | SQL Server 2022 Hidden Gems | Data Exposed
Join us in this episode of Data Exposed: SQL Server 2022 Hidden Gems to learn about the first hidden gem engineers put into the product that you may find helpful.
Resources:
What’s new in SQL Server 2022 (16.x)
Microsoft Tech Community – Latest Blogs –Read More
Why does a query fail when there is no error? | SQL Server 2022 Hidden Gems | Data Exposed
Join us in this episode of Data Exposed: SQL Server 2022 Hidden Gems to learn about the first hidden gem engineers put into the product that you may find helpful.
Resources:
What’s new in SQL Server 2022 (16.x)
Microsoft Tech Community – Latest Blogs –Read More
Why does a query fail when there is no error? | SQL Server 2022 Hidden Gems | Data Exposed
Join us in this episode of Data Exposed: SQL Server 2022 Hidden Gems to learn about the first hidden gem engineers put into the product that you may find helpful.
Resources:
What’s new in SQL Server 2022 (16.x)
View/share our latest episodes on Microsoft Learn and YouTube!
Microsoft Tech Community – Latest Blogs –Read More
Why does a query fail when there is no error? | SQL Server 2022 Hidden Gems | Data Exposed
Join us in this episode of Data Exposed: SQL Server 2022 Hidden Gems to learn about the first hidden gem engineers put into the product that you may find helpful.
Resources:
What’s new in SQL Server 2022 (16.x)
View/share our latest episodes on Microsoft Learn and YouTube!
Microsoft Tech Community – Latest Blogs –Read More
🚀 Big News: NTA Techies Blog Joins Nonprofit Techies for Global Impact! 🌐
Dear NTA Techies Community,
Hold onto your seats because the NTA Techies Blog is about to redefine its reach, impact, and excitement! We’re thrilled to announce a game-changing move – the NTA Techies Blog is now making its home within the Nonprofit Techies blog, reaching an even broader audience!
In a move that promises to redefine the tech narrative, we’re joining forces with Nonprofit Techies to amplify our collective impact. This isn’t just a move; it’s a leap into a space where our insights will resonate with an even broader audience!
Hold onto the thrill – the best is yet to come!
Microsoft Tech Community – Latest Blogs –Read More
Tell Us What You Think!
Microsoft Tech Community – Latest Blogs –Read More
Copilot in PowerPoint – Copilot Snack Show Me How Video
Copilot for Microsoft 365 can help you save time and effort by automating and simplifying the presentation creation process. Here are some of the benefits of using Copilot:
You can generate relevant and engaging content for your slides with just a few clicks. Copilot can analyze your topic and keywords and suggest bullet points, images, charts, and other elements that match your message and audience.
You can design your slides with ease and confidence. Copilot can recommend the best templates and layouts for your presentation, based on your content and purpose. You can also customize your slides with Copilot’s editing tools and apply themes, colors, fonts, and animations.
In this Copilot Snack Show Me How video I walk through several ways to create, and enrich, your creation of presentation decks in PowerPoint using Copilot for Microsoft 365.
**Please note the long form Word doc used in one of the creation demos was rendered by downloading a large PDF, opening it in Microsoft Word, then saving the resultant Word document to my OneDrive. The entire process, from download to resulting slides done in under 4 minutes!
Resources:
Copilot in PowerPoint help & learning (microsoft.com)
Create a new presentation – Microsoft Support
Summarize your presentation with Copilot in PowerPoint – Microsoft Support
Organize this presentation with Copilot in PowerPoint – Microsoft Support
Use your organization’s branding with Copilot in PowerPoint – Microsoft Support
Help with Copilot prompts
Thanks for visiting – Michael Gannotti LinkedIn | Twitter
Microsoft Tech Community – Latest Blogs –Read More
Microsoft Entra’s Top 50 Features of 2023
To kick off 2024, we’re revisiting the top features delivered in Microsoft Entra over the last calendar year. We served thousands of customers to verify all types of identities and secure, manage, and govern their access to any resource with multicloud identity and network access products. We introduced the latest wave of advancements from Microsoft Entra, expanding into Security Service Edge (SSE), Artificial Intelligence (AI), and accelerating innovations in other key areas like Decentralized Identities, multicloud, and non-human identities, delivering more than a hundred features. Below, you’ll find the top fifty features influenced by customer feedback and market needs. For a comprehensive list, please refer to the release notes. By adopting these latest identity innovations, you can better protect your digital estate and get more out of your security investments.
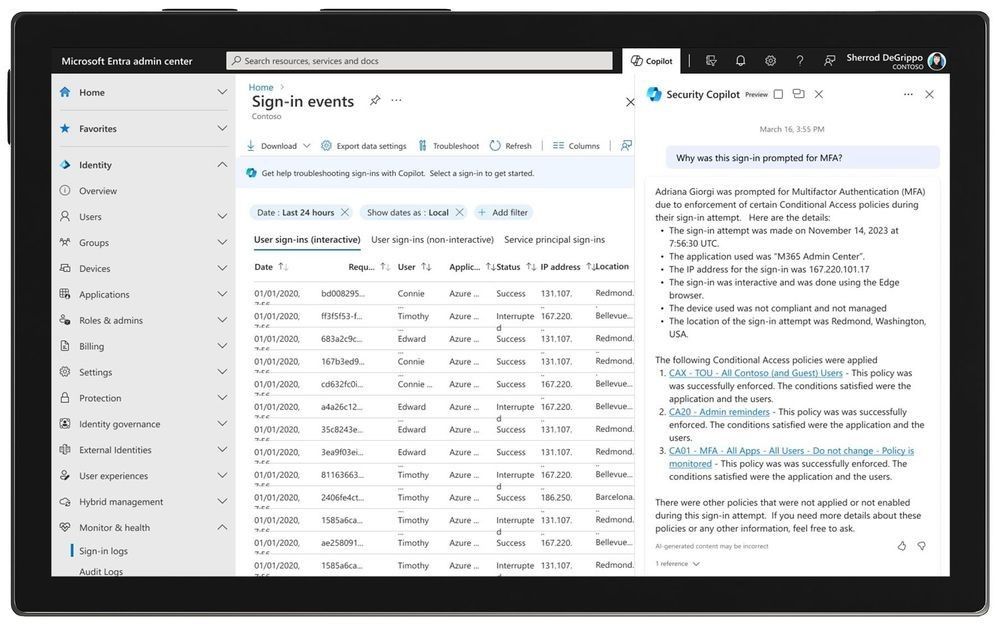
Secure Access in the Era of AI – at Microsoft Ignite 2023, we announced that Microsoft Security Copilot is coming to Microsoft Entra (in Private Preview) to help you automate common tasks, troubleshoot faster, interpret complex policies, and design workflows. This monumental inclusion is only one component of maintaining strong and consistent identity security. Microsoft Entra’s breadth of solutions protect employees, frontline workers, customers, and partners—as well as apps, devices, and workloads across multicloud and hybrid environments.
In the Microsoft Entra admin center, Microsoft Security Copilot explains in simple, conversational language what a Conditional Access policy does or why multi-factor authentication (MFA) was triggered.
Upcoming support for passkeys offering phishing-resistant alternative to physical FIDO2 security keys supporting our enterprises and government customers.
Secure by default, through the auto-rollout of Microsoft Entra Conditional Access policies protecting tenants based on risk signals, licensing, and usage.
Conditional Access enforcement of token protection for sign-in sessions (Public Preview) to combat token theft and replay attacks.
Conditional Access for protected actions enabling organizations to safeguard critical administrative operations, such as altering Conditional Access policies, adding credentials to an application, or changing federation trust settings etc.
Conditional Access overview dashboard offering a comprehensive view of Conditional Access posture and templates providing a convenient method to deploy new policies aligned with Microsoft recommendations.
Conditional Access authentication strength to enable organizations to tailor authentication method requirements based on the user’s sign-in risk level or the sensitivity of the accessed resource, empowering those in highly regulated industries or with strict compliance requirements.
Implement Zero Trust access control by invalidating tokens that violate your IP-based location policies and prevent token replay attacks in near real-time through the strict enforcement of location policies (Public Preview).
The new Entra ID Protection dashboard (Public Preview) is a central hub aiding identity admins and IT practitioners in understanding security posture and implementing effective protections against identity compromises.
New Entra ID Protection signals: verified threat actor ID and attacker in the middle, to help protect organizations from malicious actors and activities.
Entra ID Protection now offers real-time threat intelligence detections to apply risk-based Conditional Access policies to protect identities.
Manage the permissions of identities across a multicloud infrastructure – Improve the security posture of your identities for multicloud infrastructure by managing their permissions and ensuring the principle of least privilege. Manage identity permissions across your multicloud infrastructure.
Leverage Entra ID Protection – Allow on-premises password change to reset user risk (Public Preview) to effectively manage user risk in hybrid environments.
Integration of Entra ID Protection with Microsoft 365 Defender to investigate incidents efficiently and effectively, gaining a comprehensive understanding of end-to-end attacks and facilitating a quicker response to identity compromises.
System-preferred authentication for MFA to sign in users with the most secure method they’ve registered and the method that’s enabled by admin policy.
Configure phishing-resistant MFA on mobile without having to provision certificates on the user’s mobile device using certificate-based authentication (CBA) on mobile.
New features and enhancements in certificate-based authentication (CBA) enabling government organizations to comply with Executive Order 14028 requirements and helping customers migrate from Active Directory Federation Services.
Verify your workplace on LinkedIn with Microsoft Entra Verified ID – Start your decentralized identity journey through managed verifiable credentials service based on open standards.
Converged Authentication Methods – Manage multi-factor authentication (MFA) and self-service password reset (SSPR) in one policy alongside passwordless methods like FIDO2 security keys and certificate-based authentication (CBA).
Secure non-human identities using Microsoft Entra Workload Identities App Health Recommendations.
AD FS Application Migration – Modernize identity estate through cloud-based identity services, enhanced security, and improved user experience.
Use FIDO2 security keys to sign in to Microsoft Entra ID federated applications on iOS and macOS web browsers.
Configure single sign-on (SSO) for Microsoft Entra ID accounts on macOS, iOS, and iPadOS across all applications using Microsoft Enterprise SSO for Apple Devices.
Configure either the phishing-resistant credential or a traditional password as the authentication method using platform SSO for macOS (Public Preview).
Protect and secure local administrator accounts using Windows Local Administrator Password Solution with Microsoft Entra ID.
Customize your authentication flows with custom claims provider to source claims from external systems.
Microsoft Entra External ID (Public Preview) – Establish more secure digital relationships for external identities, create people-centric experiences, and accelerate development of secure applications.
Personalize and help secure access to any application for customers and partners.
With Microsoft Graph Activity Logs, you can now investigate the complete picture of activity in your tenant – from token request in Sign–In logs, to API request activity (reads, writes, and deletes) in Microsoft Graph Activity Logs, to ultimate resource changes in Audit logs.
Restricted management administrative units: Designate specific users, security groups, or devices in your Microsoft Entra ID tenant that you want to protect from modification by tenant-level administrators.
IPv6 support to Microsoft Entra ID allowing customers to reach the Entra services over IPv4, IPv6 or dual stack endpoints.
Microsoft Entra Permissions Management – Microsoft Defender for Cloud (MDC) integration (Public preview): Consolidate identity and access permission insights with other cloud security information in a single interface.
Microsoft Entra Permissions Management – ServiceNow integration: Allow ServiceNow customers to request time-bound, on-demand permissions for multicloud environments (Azure, AWS, Google Cloud) via the ServiceNow portal.
Gain a centralized view of all identities and their permissions (Public Preview), regardless of the identity provider solutions they’re using.
Safeguard Network Access with Microsoft Entra – in July 2023 we announced two new products: Microsoft Entra Internet Access (Public Preview) and Microsoft Entra Private Access (Public Preview). With Identity and Network Access solutions working together, organizations don’t need to spend time deciding which tool would work better for each app, or how to bridge the policies your identity team created with the policies your networking team created. You can enforce unified adaptive access controls, simplify network access security, and deliver a great user experience anywhere with identity-centric Security Service Edge (SSE) solutions. Secure access to all internet, SaaS, and Microsoft 365 apps and resources with an identity-centric Secure Web Gateway (SWG).
Identity Platform Developer Center: One-stop shop for everything developers need to understand about identity concepts, learn the features of Microsoft Entra External ID, and how best to use the new platform to build awesome consumer–facing applications.
Enhanced company branding – Create a custom look and feel for the default sign–in pages, as well as pages targeting specific browser languages.
Cross-tenant access settings improvements – secure your cross-tenant collaboration scenarios and improve end-user experiences for partners.
Prevent data exfiltration using Tenant Restrictions v2 to secure cross-tenant access.
Lifecycle workflows land within LID Governance – On June 7, 2023, Microsoft Entra ID Governance became generally available, and included one of our newest capabilities: Lifecycle Workflows (LCW). With the new Lifecycle Workflows, updates and improvements can be made with more granular workflow execution auditing, and at any time, allowing for navigation to Lifecycle Workflows Audit Logs or Entra Identity Governance Audit Logs. All this access provides extensive workflow execution info and other workflow management activities.Design workflows to ensure new employees are productive immediately—and that access is removed when employees leave.
Machine Learning-based recommendations for reviewers.
A new Microsoft Entra ID Governance dashboard that pulls information, giving you an at-a-glance view of your current state of Identity Governance, a launch-pad for IGA features, and quick access to compliance reports.
Implement require independently verified credentials before approving access to confidential resources.
Zero Trust access control – Just-in-time access to privileged roles with PIM for groups.
Enforce security requirements for activation using PIM integration with Conditional Access.
API-driven provisioning (Public Preview) – Enhance employees, partners productivity and help to meet compliance and regulatory requirements through robust identity governance.
Automate provisioning and governance of your on-premises applications.
Extending the access lifecycle with your organization-specific processes and business logic.
Assigning access automatically to access packages instead of requiring users to request access.
Configuring Verified ID checks in entitlement management.
Entitlement Management support in Conditional Access.
Identity security is a continuous journey
The identity security market is constantly developing, but so are the threats and risks from malicious actors and hackers and the advancements of AI. To keep up with these changes, organizations need to take an active and comprehensive approach to identity security, working with reliable vendors to offer them the best solutions. Even though 2023 is over, the demand for solutions remains high, and we are eager to reveal what we have planned for 2024.
Best regards,
Shobhit Sahay
Learn more about Microsoft identity:
Related Articles:
5 ways to secure identity and access for 2024
Microsoft named a Leader in 2023 Gartner® Magic Quadrant™ for Access Management for the 7th year
See recent Microsoft Entra blogs
Dive into Microsoft Entra technical documentation
Join the conversation on the Microsoft Entra discussion space and Twitter
Learn more about Microsoft Security
Microsoft Tech Community – Latest Blogs –Read More
Protect faster with Microsoft Defender XDR’s latest UX enhancements
Organizations are facing an unprecedented surge in cyberthreats and a global shortage of security experts, and Security Operations Center (SOC) teams are struggling with managing a rising influx of alerts, incidents, and raw telemetry produced by a variety of security tools to protect endpoints, email, identity, SaaS apps, data, and cloud infrastructure. Balancing the speed of response with the precision required for effective threat detection poses an ongoing challenge for SOC teams in optimizing their operational efficiency.
To help SOC teams protect faster, this week we are excited to share the general availability (GA) of our most recent user experience (UX) enhancements within Microsoft Defender XDR to make our industry-leading XDR platform easier to use than ever. These UX enhancements not only improve efficiency but also deliver an intuitive, smooth experience throughout the incident triage, investigation, and threat hunting processes for the SOC teams.
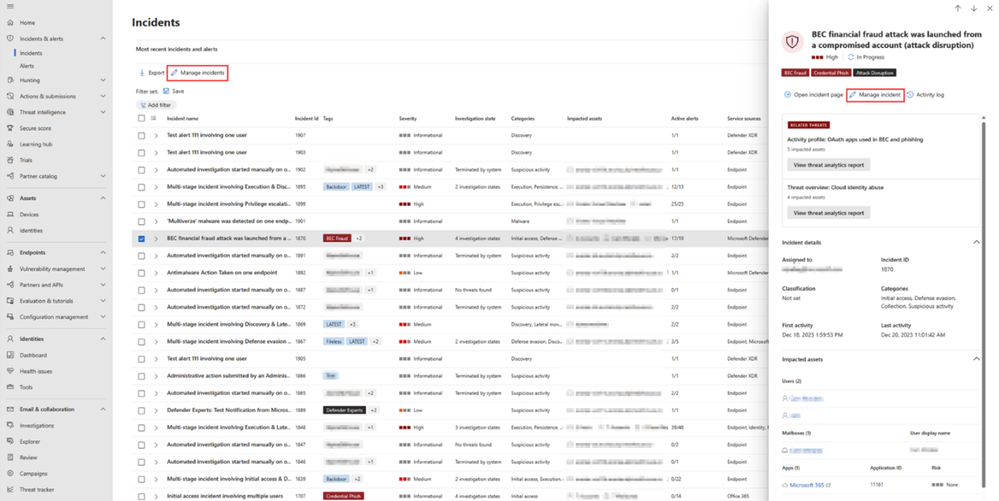
Incident customization
In Microsoft Defender portal, security analysts can choose which incidents should be prioritized based on several factors such as incident severity, incident status and more. To provide SOC analysts with a better and more customized incident management experience, we have added new capabilities to the “Manage incidents” action of the incident page so they can now assign incidents to security groups and change incident severity manually. Once you have the Incident side panel open, select the “Manage incident” action, and you will be able to assign the incident or change the incident severity manually.
Figure 1: Manage incident action in incident details paneFigure 2: Manage incident panel
In page-filters for the incident queue
Every second counts in cybersecurity. In SOC team’s daily work, customization saves time as it helps security analysts swiftly retrieve their preferred filter configurations. Today we are introducing a set of powerful in-page filters that improve the way you customize your incidents queue within Microsoft Defender XDR. Now, you can easily search for specific filters and save your frequently used filter sets to tailor your incident response experience. The new in-page filters provide a user-friendly interface that allows security analysts to efficiently locate and apply the filters they need. This time-saving capability enables security analysts to manage the incident queue more efficiently in a seamless and productive incident management process.Figure 3: In page filters
Incident activity log
Gaining context in an easier and more efficient way represents another time-saving opportunity in security operations. Now with the new incident activity log, security analysts can thoroughly document the steps taken when investigating an incident. This not only ensures accurate reporting to management but also fosters seamless collaboration amongst coworkers. An analyst can also access records of comments on the incident made by other analysts.
Moreover, instead of plain text comments, analysts now have rich text comments for incidents. They can apply various formatting options such as bold, italics, underline, bullet points, and more, as well as add links and images to make their comments more expressive and informative. Additionally, the bi-directional synchronization feature with Microsoft Sentinel’s activity log allows SOC teams to benefit from the seamless integration of logs and comments.
Figure 4: Incident activity log and rich comment interface
Go hunt within incident page
Go hunt feature is now available in the attack story of the incident page. This new feature allows security analysts to access the Advanced hunting function directly from the Incident Graph, providing a well-organized overview of incident-related data all within the same tab. With Go hunt, analysts can quickly gather more data on various entities such as devices, IPs, URLs, and files as shown in Figure 5. Additionally, they can link advanced hunting query results to a specific incident as shown in Figure 5, all from the same page.Figure 5: “Go hunt” action on URL from incident attack storyFigure 6: Advanced hunting query results within incident page
Hunt and investigate from Advanced hunting page
The new query history feature helps SOC analysts to seamlessly resume their work from where they left off. This functionality reduces the risk of losing any unsaved work by automatically retaining security analysts’ recent queries and allows analysts to effortlessly run and modify those queries at their convenience. Figure 7: Query history in Advanced hunting page
Another enhancement of the Advanced hunting page is the new inline results exploration functionality that facilitates a smoother results exploration experience and allows SOC analysts to conveniently navigate through all the parsed data within the results grid while eliminating the necessity for horizontal scrolling or side panels. SOC analysts now can expand the record of the results to explore its content within the results grid. In addition, they can expand specific cells of type JSON or array to easily explore their parsed content.Figure 8: Inline results exploration in Advance hunting page
Furthermore, SOC analysts can now right-click on any result value in a row to add it as a filter to the existing query or copy the value to clipboard. This functionality preserves valuable time for analysts, allowing them to modify their queries in seconds based on the results, all without navigating away from the results grid.Figure 9: Right click context menu for Advanced hunting results
Speed and efficiency are crucial in security operations. The new UX enhancements in Microsoft Defender XDR make our XDR platform more user-friendly than ever before and provide an even more seamless and streamlined experience in incident triage, investigation, and threat hunting for SOC teams. The cumulative impact of each one of these improvements contributes to a significant enhancement in SOC efficiency.
Learn more:
Read our documentation to get started:
Manage incidents
Incidents queue filters
Incident activity log
“Go hunt” from incident attack story
Advanced hunting query history
Advanced hunting results exploration
Visit our websites to learn more about Microsoft Defender XDR and unified security operations platform.
Microsoft Tech Community – Latest Blogs –Read More
MidDay Café Episode 47 – Rundown on the Latest Copilot Announcements and Implications
This week on MidDay Café Microsoft’s with Tyrelle Barnes and Michael Gannotti the two hosts discuss the latest Microsoft announcements about Copilot. They also talk about the implications and real-world examples of the impact/value they deliver.
Listen to the Audio podcast version:
Subscribe to the Audio Podcast on Spotify
Subscribe to the Audio Podcast on Apple Podcasts
Subscribe to the Audio Podcast on Google Podcasts
Resources:
Bringing the full power of Copilot to more people and businesses – The Official Microsoft Blog
Expanding Copilot for Microsoft 365 to businesses of all sizes | Microsoft 365 Blog
Thanks for visiting!
Tyrelle Barnes LinkedIn : Michael Gannotti LinkedIn | Twitter
Microsoft Tech Community – Latest Blogs –Read More