Tag Archives: microsoft
TLS 1.0 and 1.1 support will be removed for new & existing Azure storage accounts starting Nov 2024
To meet evolving technology and regulatory needs and align with security best practices, we are removing support for Transport Layer Security (TLS) 1.0 and 1.1 for both existing and new storage accounts in all clouds. TLS 1.2 will be the minimum supported TLS version for Azure Storage starting Nov 1, 2024.
Azure Storage currently supports TLS 1.0 and 1.1 (for backward compatibility) and TLS 1.2 on public HTTPS endpoints. TLS 1.2 is more secure and faster than older TLS versions. TLS 1.0 and 1.1 do not support modern cryptographic algorithms and cipher suites. Many of the Azure storage customers are already using TLS 1.2 and we are sharing this guidance to expedite the transition for customers currently on TLS 1.0 and 1.1. Customers must secure their infrastructure by using TLS 1.2 with Azure Storage by Oct 31, 2024. The older TLS versions (1.0 and 1.1) are being deprecated and removed to meet evolving standards (FedRamp, NIST), and provide improved security for our customers.
This change will impact both existing and new storage accounts using TLS 1.0 and 1.1. To avoid disruptions to your applications connecting to Azure Storage, you must migrate to TLS 1.2 and remove dependencies on TLS version 1.0 and 1.1, by Oct 31, 2024.
Learn more about how to migrate to TLS1.2.
As best practice, we also recommend using Azure policy to enforce a minimum TLS version. Learn more here about how to enforce a minimum TLS version for all incoming requests. If you already use Azure Policy to enforce TLS version, minimum supported version after this change rolls out will be TLS 1.2.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Enhancing Genomic Analysis with Hybrid Cloud: A Microsoft Azure Perspective
In the rapidly advancing field of genomics, managing and analyzing vast amounts of genomic data has become a critical challenge. The article titled “Enhancing Genomic Analysis with Hybrid Cloud” explores how a hybrid cloud approach, particularly leveraging Microsoft Azure services, can significantly accelerate secondary genomic analysis.
Introduction
The article delves into the complexities of secondary genomic analysis and introduces the hybrid cloud model, which seamlessly integrates on-premises infrastructure with the powerful capabilities of Microsoft Azure. Microsoft Azure , Pure Storage, and Illumina conducted testing in Equinix’s Dallas data center utilizing Equinix Metal to determine the benefits and challenges of a hybrid cloud infrastructure.
Solution and Architecture
Illumina DRAGEN (dynamic read analysis for genomics) provides accurate, comprehensive, and efficient secondary analysis of NGS data.
Azure CycleCloud orchestrates a traditional HPC cluster (ie. Slurm for this testing) and enables autoscaling the Azure NP series virtual machines (VMs) with the AMD/Xilinx Field Programmable Gate Array (FPGA) acceleration card that enables Illumina DRAGEN processing.
Pure Storage FlashBlade is an all-flash, consolidated data storage solution for both file and object workloads. FlashBlade is designed to support data-heavy, unstructured workloads efficiently, providing unequaled density, capacity, and performance.
Equinix is the world’s digital infrastructure company, enabling digital leaders to fast-track competitive advantage across clouds, networking, storage, compute, and software.
Pure Storage on Equinix Metal with FlashBlade embedded provides a high-performance, full-stack, hosted bare-metal infrastructure platform. Enterprises can take advantage of the platform to build best-of-breed, cost-optimized, hybrid-cloud solutions. The platform is fully interconnected with every major public-cloud provider. It features more than 356,000 global interconnects to nearly every telecom and ISP provider, creating a true hybrid/multi cloud environment with unparalleled performance.
The Equinix Metal platform embeds the full portfolio of Pure Storage products, including FlashArray™, FlashBlade®, and Portworx®. The solution enables native block, file, object, and container storage on dedicated, bare-metal hardware, physically managed by Equinix Metal. Simplify data storage and infrastructure management into a single fully integrated, on-demand platform. Reimagine the cloud journey and accelerate business and digital transformation. Gain the flexible infrastructure to quickly respond to changing business needs and to help unlock critical business insights.
Architecture – Hybrid cloud
Azure highlights
The article highlights Microsoft Azure’s role in enabling an efficient hybrid cloud approach for genomics:
Azure Virtual Machines: Researchers can deploy and manage virtual machines (VMs) on Azure to handle compute-intensive tasks.
Azure CylceCloud: IT can orchestrate a traditional HPC job scheduler and cluster (ie. Slurm, PBS, GridEngine, etc) and incorporate compute node autoscaling to control costs. Researchers can utilize known job submission scripts to minimize changes to workflow.
Other Azure Compute infrastructure
Azure Kubernetes Service (AKS): Azure AKS assists in orchestrating containerized applications, enhancing scalability and ease of deployment.
Azure Batch: A cloud native HPC job scheduler that can be incorporated with external workflow engines (ie. Cromwell and Nextflow) or integrated into existing code for job submissions.
Advantages of Azure for hybrid cloud for Genomic Analysis
Seamless Scalability: Azure’s elasticity enables researchers to scale resources up or down based on analysis demands.
Flexibility: New technology (ie. latest GPU) or capabilities (ie. new compute queue) can be added almost instantly.
Cost Efficiency: Pay-as-you-go pricing minimizes infrastructure costs while maximizing performance during peak periods.
Security and Compliance: Azure’s robust security measures ensure data protection, compliance with regulations, and privacy.
Challenges and Considerations
Potential challenges include data privacy, data transfer (using Express Routes), integration complexities, and management of hybrid environments.
Conclusion
The article concludes by highlighting how leveraging Microsoft Azure’s hybrid cloud capabilities can revolutionize secondary genomic analysis. By integrating on-premises infrastructure with Azure’s powerful services, researchers can unlock new insights, expedite research, and drive innovation in the field of genomics.
Microsoft Tech Community – Latest Blogs –Read More
Developing a Curriculum for Microsoft Fabric: Cloud-Powered App Development
Welcome, Educators! The ever-evolving landscape of technology demands that our educational strategies keep pace, enabling our students to thrive in the digital sphere. Today, we delve into a comprehensive curriculum centered around Microsoft Fabric, aimed at empowering your students in cloud-powered app development.
Course Overview
Description
This course is designed to immerse educators and students in the expansive realm of Microsoft Fabric, emphasizing cloud services with a primary focus on the Microsoft Azure Platform. Throughout the sessions, we’ll navigate through scalable services covering Data Analytics, Data Warehousing, Data Science, Machine Learning, and Real-Time Event Processing.
Expectations and Goals
This curriculum serves as an introductory guide to cloud services, concentrating on data-centric services related to storage and analytics processing. The lecture-based approach, supplemented by Microsoft Learn online modules, will equip participants with a comprehensive understanding of these concepts, delivered via online video format.
Daily Requirements
To maximize learning outcomes, participants are expected to review presentation content and complete assigned MS Learn Modules for each class day. While flexible, it’s advised not to skip assignments to prevent issues from accumulating over the short duration of this course.
Course Schedule
Lesson 1
Introduction: 30 mins
Setup:
Enable Microsoft Fabric Trial: 10 mins
Create Microsoft Learn Accounts: 10 mins
Register for 30 days to Learn IT Micrsofoft Fabric: 10 mins
Presentation:
Intro to Azure: 15 mins
Azure Fundamentals: 45 mins
Video Presentations: 3.5 hours
• Webinar – Introducing Unified Analytics
• Webinar – Data Warehousing in Microsoft Fabric
• Learn Live – Get started with end-to-end analytics and lakehouses in
Microsoft Fabric
• Learn Live – Get started with data warehouses in Microsoft Fabric
MS Learn Modules 2 hours
• Introduction to end-to-end analytics using Microsoft Fabric
• Get started with lakehouses in Microsoft Fabric
• Get started with data warehouses in Microsoft Fabric
Lesson 2
Video Presentations 3.5 hours
• Webinar – Data Engineering with Microsoft Synapse
• Learn Live – Use Apache Spark in Microsoft Fabric
• Learn Live – Work with Delta Lake tables in Microsoft Fabric
MS Learn Modules: 2.5 hours
Use Apache Spark in Microsoft Fabric
Work with Delta Lake tables in Microsoft Fabric
Lesson 3
Video Presentations 3.5 hours
Webinar – Data Factory in Microsoft Fabric
Learn Live – Use Data Factory pipelines in Microsoft Fabric
Learn Live – Ingest Data with Dataflows Gen2 in Microsoft Fabric
MS Learn Modules: 2.5 hours
• Use Data Factory pipelines in Microsoft Fabric
• Ingest Data with Dataflows Gen2 in Microsoft Fabric
Lesson 4
Video Presentations: 4 hours
Webinar – Real-Time Analytics in Microsoft Fabric
Webinar – Data Science in Microsoft Fabric
Learn Live – Get started with Real-Time Analytics in Microsoft Fabric
Learn Live – Get started with data science in Microsoft Fabric
MS Learn Modules: 2 hours
Get started with Real-Time Analytics in Microsoft Fabric
Get started with data science in Microsoft Fabric-time analytics
Lesson 5
Video Presentations: 2 hours
Webinar – Power BI in Microsoft Fabric
Learn Live – Administer Microsoft Fabric Azure Synapse
MS Learn Modules: 1 hour
Final Project
Product Experience Report: 1 hour
Create and submit a word document. The report should be ~ ½ to 1 full page
describing what you found most important regarding the material
covered in the course.
Conclusion
This curriculum aims not just to educate but also to inspire educators and students alike to explore the vast potential of Microsoft Fabric. As you embark on this journey, remember, it’s not just about acquiring knowledge, but also about contributing your insights and feedback to shape the future of these technologies.
Feel free to share your thoughts, engage with the material, and nurture a vibrant community of learning. Together, let’s empower the next generation of tech enthusiasts and innovators!
Microsoft Tech Community – Latest Blogs –Read More
Chat with your Azure DevOps data
Introduction
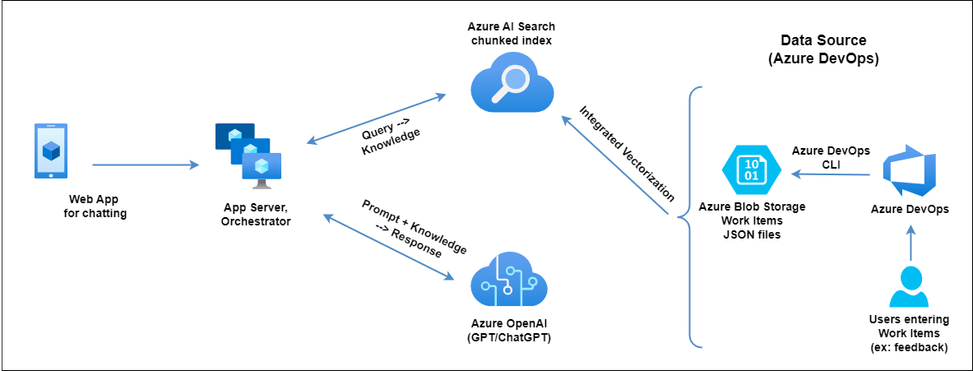
In the world of software development, the ability to quickly access and interpret Azure DevOps (ADO) Work Items is crucial. This is where our innovative solution comes into play, offering a ChatGPT-like experience directly with your ADO. Utilizing the Retrieval Augmented Generation (RAG) pattern, Azure AI Search & Azure Open AI’s cutting-edge capabilities, we’ve created a seamless integration that elevates the efficiency of querying ADO work items.
Solution Overview
This solution builds on top of Azure Search OpenAI Demo.
The solution leverages Azure DevOps CLI to periodically export ADO Work Items as JSON and store them in Azure Blob storage. Next Azure AI Search indexer runs on a scheduled basis to chunk and create a vectorized embeddings of the JSON data to create index, leveraging Azure AI Search’s Integrated Vectorization feature. In the final step, when users query about their work items through the Chat App, the orchestrator queries Azure AI Search index using Hybrid Search + Semantic ranker to retrieves relevant knowledge (work items). Then the orchestrator sends the knowledge along with vectorized embeddings of the user query to Azure OpenAI. Finally Azure OpenAI builds the response based on the knowledge provided and that gets served to the user.
Part 1: Exporting Work Items to Azure Blob Storage
The journey begins with Azure DevOps CLI, where work items such as User Stories, Product Backload Items (or custom work item such as Product Feedback) are exported to JSON files. An Azure Function operates periodically, transforming any new or modified work items into JSON files and securely storing them in Azure Blob storage. This ensures that data remains current and accurate.
Setting Up the Azure DevOps CLI and Exporting Work Items
The first step in our solution involves setting up the Azure DevOps CLI and exporting work items. This process is streamlined with a Bash script, which automates the retrieval of work items as JSON files. These JSON files are then stored securely in Azure Blob storage.
Learn about Azure DevOps command line interface extension – Azure DevOps | Microsoft Learn
Embedding and Utilizing Queries in the Script
To automate the export of items, we’re going to use Queries. Queries in Azure DevOps are used to fetch specific sets of work items based on criteria like type, status, or custom fields. These Azure Boards Queries can exist in either Azure DevOps Boards, or in embedded in the script as a Work Item Query Language (WIQL) query. We will then use the Azure DevOps CLI to run the query and export the data to JSON files.
Use managed queries to list work items – Azure Boards | Microsoft Learn
View or run a query in Azure Boards and Azure DevOps – Azure Boards | Microsoft Learn
There is a limitation of the CLI only returning 1000 rows from queries, so if you have a lot of data you can leverage REST calls directly or have multiple queries that return smaller amounts of data, like per year or per quarter.
Selecting Different Fields in Queries
Finally, we’ll select and export only the fields we care about. Queries can return limited data but also data that is more verbose than needed and can come across as noise for the purposes of exploring your data.
Given this returned data from a query, there is a lot of extra data that we can clean up, like CreatedBy and Id.
{
“fields”: {
“System.CreatedBy”: {
“_links”: {
“avatar”: {
“href”: “[Anonymized Avatar URL]”
}
},
“descriptor”: “[Anonymized Descriptor]”,
“displayName”: “[Anonymized Name]”,
“id”: “[Anonymized ID]”,
“imageUrl”: “[Anonymized Image URL]”,
“uniqueName”: “[Anonymized Email]”,
“url”: “[Anonymized URL]”
},
“System.Id”: 12484,
},
“id”: 12484,
}
The Azure CLI has the capability to filter, rename, and manipulate JavaScript results. The Azure CLI supports JMESPath, a query language for JSON.
JMESPath query command results with Azure CLI | Microsoft Learn
JMESPath — JMESPath
By leveraging a JMESPath query, we can simplify the result objects to make indexing and the intent clearer.
$ recordFormat='[].{Id:fields.”System.Id”, CreatedBy:fields.”System.CreatedBy”.displayName}’
$ az boards query –org=$org –id ${queryId} –query $recordFormat
{
“CreatedBy”: “[Anonymized Person]”,
“Id”: 12484,
}
This gives us more concise, targeted results that reduce a lot of duplication and noise.
The Script: Automated Script for Exporting Work Items
The automation script plays a crucial role in the export process. Below is sample version of the script. This can be run manually, or put in a pipeline and run on a schedule. The result is a folder full of json files, one per workitem. From here you can manually upload the files to Azure Blob Storage, use the script to automate it, or put those instructions into a pipeline. In the future we can show how to make this a continuous process instead of a snapshot export.
Here a complete script for use as an example: azure-devops-scripts/scripts/export-query-to-json.sh at main · codebytes/azure-devops-scripts (github.com)
Part 2: Indexing with Azure AI Search
Next, we harness Azure AI Search’s indexer to organize the ADO work item data from Blob storage, capitalizing on the Integrated Vectorization feature. This process, which can be scheduled according to your needs, involves chunking the data with the Text Split skill followed by the pivotal step of converting text into vectors using the AzureOpenAIEmbedding skill. Get started with integrated vectorization using the Import and vectorize data wizard in the Azure portal.
Once Azure AI Search service provisioned with Standard pricing tier, click on the “Import and vectorize data” button as shown below and follow the wizard to create Index and Indexer (to periodically index the data).
Part 3: Chatting with Azure OpenAI Models using your own data
Finally, the crux of our solution lies in the Chat with Azure OpenAI models feature. Within Azure OpenAI Studio, we integrate our Azure AI Search index and employ vector search, utilizing the Azure OpenAI’s text-embedding-ada-002 model. By selecting the Hybrid + Semantic ranker search configuration, we ensure the highest quality of results, combining vector and keyword searches with a semantic ranker. Follow this Quickstart to Chat with Azure OpenAI models using your own data.
Querying and Deployment
After integrating our data sources, the Chat playground within Azure OpenAI Studio becomes the testing ground. Here, queries about work items come to life, providing insights and answers through conversational AI. With satisfaction in the studio experience, deploying the model as a standalone web application is merely a click away.
From your Azure OpenAI’s “Model deployments” under Azure Portal, open Azure OpenAI Studio/Azure AI Studio. Here you can use Chat option under playground to “Add your data“. Then make sure to select “Azure AI Search” as data source and select the right AI search service and Index provisioned in the step 2. Check “Add vector search to this search resource” box. Select Ada embedding model from drop down, if it’s not provisioned, go back and provision it first. Under “Data management” screen, select search type as “Hybrid + semantic“.
Now you can start chatting with your work items as shown below. Once satisfied with the results, click on “Deploy to” button to deploy as “A new web app“.
Authentication
By default, user authentication is mandatory via App Service Easy Auth, with the option to limit access to specific users or Entra ID groups, ensuring both security and flexibility.
Conclusion
Our solution not only streamlines access to work items within Azure DevOps but also enhances the user experience with intelligent and intuitive AI-driven interactions. By marrying Azure’s powerful AI Search with conversational models, we’ve unlocked a new realm of productivity for developers and project managers alike.
Microsoft Tech Community – Latest Blogs –Read More
TLS 1.0 and 1.1 support will be removed for new & existing Azure storage accounts starting Nov 2024
To meet evolving technology and regulatory needs and align with security best practices, we are removing support for Transport Layer Security (TLS) 1.0 and 1.1 for both existing and new storage accounts in all clouds. TLS 1.2 will be the minimum supported TLS version for Azure Storage starting Nov 1, 2024.
Azure Storage currently supports TLS 1.0 and 1.1 (for backward compatibility) and TLS 1.2 on public HTTPS endpoints. TLS 1.2 is more secure and faster than older TLS versions. TLS 1.0 and 1.1 do not support modern cryptographic algorithms and cipher suites. Many of the Azure storage customers are already using TLS 1.2 and we are sharing this guidance to expedite the transition for customers currently on TLS 1.0 and 1.1. Customers must secure their infrastructure by using TLS 1.2 with Azure Storage by Oct 31, 2024. The older TLS versions (1.0 and 1.1) are being deprecated and removed to meet evolving standards (FedRamp, NIST), and provide improved security for our customers.
This change will impact both existing and new storage accounts using TLS 1.0 and 1.1. To avoid disruptions to your applications connecting to Azure Storage, you must migrate to TLS 1.2 and remove dependencies on TLS version 1.0 and 1.1, by Oct 31, 2024.
Learn more about how to migrate to TLS1.2.
As best practice, we also recommend using Azure policy to enforce a minimum TLS version. Learn more here about how to enforce a minimum TLS version for all incoming requests. If you already use Azure Policy to enforce TLS version, minimum supported version after this change rolls out will be TLS 1.2.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Experience Defender Experts above the fold
Since we announced our latest enhancements to Defender Experts for XDR in November 2023, we have received positive feedback from our customers, and continue to take in their suggestions as we work to continuously enhance our service to help elevate their security posture and overall experience throughout our partnership. This blog highlights our newest updates that enable you to experience Defender Experts above the fold, giving you more visibility into what our experts are doing on your behalf.
New and improved homepage experience
As an extended managed detection and response customer, it’s vital to be able to quickly determine what your service provider needs you to do. We’re making that experience more prominent with our new Defender Experts overview banner. This banner, located at the very top of the Microsoft Defender XDR homepage, will be your one-stop shop for your primary Defender Experts needs. For example, if you’re just getting started with our service, the Defender Experts overview banner will prompt you to complete our onboarding wizard, so you can easily get up and running with our service.
Figure 1. Screenshot of Microsoft Defender XDR homepage featuring the new Defender Experts banner.
Furthermore, once you’re onboarded to the Defender Experts for XDR service, the banner will show relevant operational data. This will help you quickly understand any incidents that require your immediate action and provide a summary of how many incidents Defender Experts has handled recently.
Figure 2. Screenshot of Microsoft Defender Experts banner that shows the number of incidents that require action from a customer.
Enhanced Reporting
Our Defender Experts for XDR report has shown fundamental data that highlights the efficacy of our service. This includes our incident coverage, efficiency, and incident volumes stratified by their severities and threat categories. We’re excited to add two new widgets to our report, giving customers even more visibility into the work we’re doing to help keep their organizations secure.
Figure 3. Screenshot of a Microsoft Defender Experts report that shows the percentage of incidents resolved and incidents by severity and category.
First, our report now includes actionable insights that show customers their most impacted users and devices. You can see how many incidents their most impacted assets were involved in, and drill down to see the corresponding incidents, their classification, and any managed response actions published or carried out by Defender Experts.
Figure 4. Screenshot of Defender Experts report portion that shows the most impacted assets.
The enhanced report also breaks down incidents based on service sources, giving customers real-time visibility into the volume of incidents detected by individual Microsoft Defender products, and resolved by Defender Experts. This enables your SOC team to tangibly observe how Defender Experts effectively protects your attack surfaces daily.
Figure 5. Screenshot of Defender Experts report portion that shows incidents by service source.
To learn more about our service, visit the Microsoft Defender Experts for XDR web page, read the Defender Experts for XDR docs page, or watch our explainer video. You can also visit our Tech Community Discussion Space to ask questions, engage in conversations, and share your expertise and feedback.
Microsoft Tech Community – Latest Blogs –Read More
Hack Together: The Microsoft Fabric Global AI Hack
Are you ready to unleash your creativity and build amazing solutions with Microsoft Microsoft Fabric and AI?
If so, join us for Hack Together: The Microsoft Fabric Global AI Hack, a virtual event where you can learn, experiment, and hack together with the new Copilot and AI features in Microsoft Fabric!
Hack Together is a global online hackathon that runs from February 15th to March 4th, 2024.
It’s open to anyone who wants to explore the possibilities of using Microsoft Fabric to develop AI applications, whether you are a beginner, advanced maker, admin or a professional developer – all are welcome! You can join solo or hack together as a team of up to 3 people.
Are you ready to unleash your creativity and build amazing solutions with Microsoft Microsoft Fabric and AI?
Register NOW https://aka.ms/hacktogether-fabric-AI
What is Hack Together?
Hack Together is a global online hackathon that runs from February 15th to March 4th, 2024.
It’s open to anyone who wants to explore the possibilities of using Microsoft Fabric to develop AI applications, whether you are a beginner, advanced maker, admin or a professional developer – all are welcome! You can join solo or hack together as a team of up to 3 people.
The goal of Hack Together is to build solutions in Microsoft Fabric that address one or more AI-themed Hackathon categories. You can use any combination of workload features available in Microsoft Fabric (including Data Factory, Synapse Data Engineering, Synapse Data Warehousing, Synapse Data Science, Synapse Real-Time Analytics, Data Activator, Power BI) to align your solution to the categories defined below:
Best Real-World AI application built with Microsoft Fabric: A solution that solves a real world problem with Microsoft Fabric by implementing any concept or collection of concepts related to Artificial Intelligence. This could include utilization of RAG to fine-tune an LLM, training an object detection model, anomaly detection, predictive forecasting, or any other modern application of AI within Microsoft Fabric.
Best use of Microsoft Fabric + Azure OpenAI: A solution that specifically uses Azure OpenAI service(s) alongside Microsoft Fabric to solve a real-world problem. This could include a document analysis service that uses Azure OpenAI to semantically tag content or utilize vector search to implement a retrieval augmented generation architecture. It could even make use of DALL·E 2 to genearte images based on semantic processing of text data. Simply put, if it uses Azure OpenAI inside of Microsoft Fabric, it most definitely fits into this category!
Best use of Copilot for Microsoft Fabric: A solution that makes use of one or more Copilots for Microsoft Fabric. This could include any combination of Copilot for Power BI,Copilot for Data Science and Data Engineering, and / or Copilot for Data Factory.
How to participate
To participate in Hack Together, you need to register for the event at https://aka.ms/hacktogether/fabric-ai/register.
You will need to have access to a Microsoft Fabric capacity. If you don’t have one, you can obtain a Microsoft Fabric trial license by following these instructions.
Once you have registered and have access to Microsoft Fabric, you can start building your solution!
We’ll have livestreams every week for you to learn more about AI solutions built with Microsoft Fabric. These will include a lineup of Microsoft executives like Kim Manis, VP of Microsoft Fabric as well as our Data Advocacy team and MVP’s that are ready to help you get up to speed so you can start hacking!
February 15th @ 9 AM Pacific: Fabric AI Hack Together Kickoff: Ready, Set Hack: Do more with AI in Microsoft Fabric
February 20th @ 9 AM Pacific: Fabric AI Hack Together Workshop – Building a Custom Object Detection Model on Microsoft Fabric with Snapshot Serengeti Dataset
February 22nd @ 9 AM Pacific: Fabric AI Hack Together Workshop – Building RAG Application on Microsoft Fabric & Azure Open AI
February 27th @ 9 AM Pacific: Fabric AI Hack Together Workshop – Building a Credit Card Fraud Detection System on Microsoft Fabric
February 29th @ 9 AM Pacific: Fabric AI Hack Together Wrap Up – How to submit and get ready for Fabric Community Conf
You can also join the Hack Together discussion board in the Microsoft Fabric Community to ask questions, share ideas, and get feedback from Microsoft experts and other participants. Drop a comment in the forum and introduce yourself so you can get to know your fellow hackers!
You can submit your solution any time before March 4th, 2024 at 11:59 PM PST. You will need to provide a brief description of the project, the solution overview, short video demo of your solution, and link to a project repository URL on GitHub. You can submit your solution here.
Looking for more info about the event? Check out our site for all the details: https://aka.ms/fabricaihack
What are the prizes?
Projects will be evaluated by a panel of judges, including Microsoft executives, product managers, and developer advocates. Judging criteria will include alignment with corresponding hackathon category, documentation / reusability, and innovation / impact (defined in more detail below).
The winning teams will receive the following exciting prizes (up to 3 individuals if submitting as a team, prizes distributed per team). Winning solutions and/or product feedback may also be considered for integration into the Microsoft Fabric product roadmap.
Hack Together winners will be selected as per the following judging criteria:
25% - Alignment with hackathon category - Does the solution fit into one or more of the three Hackathon Categories (Best Real-World AI application built with Microsoft Fabric, Best use of Microsoft Fabric + Azure OpenAI, Best use of Copilot for Microsoft Fabric)
25% - Innovation / Impact - Does the solution have real-world relevance? Does the solution solve a clearly defined problem that could be beneficial to others?
25% - Documentation / Reproducibility – Is the solution clearly documented in a GitHub repo that makes it easy for others to follow along and reproduce your solution? Is a video demonstration included in the submission?
25% - Video Demonstration – Does the project submission include a link to a video demonstration of the solution in action? Does the video clearly depict the solution’s use of Microsoft Fabric features and capabilities and demonstrate how the solution makes use of artificial intelligence?
Grand Prize winner: The best of the best! This category rewards the solution that meets all judging criteria, wows judges, has potential real-world value, and demonstrates innovative use of Artificial Intelligence in Microsoft Fabric.
Up to three (3) passes to attend the Microsoft Fabric Community Conference*. Approximate Retail Value (ARV) $1,849.00 USD each.
Up to $500 USD per team member to be awarded in accordance with Section 10 (Participation Gratuity Options of official contest rules). Approximate Retail Value (ARV) $500 each.
Up to three (3) Microsoft Fabric SWAG packages – hoodie and blanket. Approximate Retail Value (ARV) $80.00 USD each.
Note: Conference passes include admission only. Airfare, hotel, or any other related travel costs are the sole responsibility of the winner.
Best Real-World AI application built with Microsoft Fabric: A solution that solves a real world problem with Microsoft Fabric by implementing any concept or collection of concepts related to Artificial Intelligence. This could include utilization of RAG to fine-tune an LLM, training an object detection model, anomaly detection, predictive forecasting, or any other modern application of AI within Microsoft Fabric.
Up to $500 USD per team member, to be awarded in accordance with Section 10 (Participation Gratuity Options of official contest rules). Approximate Retail Value (ARV) $500 each.
Up to three (3) Microsoft Fabric SWAG packages – hoodie and blanket. Approximate Retail Value (ARV) $80.00 USD each.
Best use of Microsoft Fabric + Azure OpenAI: A solution that specifically uses Azure OpenAI service(s) alongside Microsoft Fabric to solve a real-world problem. This could include a document analysis service that uses Azure OpenAI to semantically tag content or utilize vector search to implement a retrieval augmented generation architecture. It could even make use of DALL·E 2 to genearte images based on semantic processing of text data. Simply put, if it uses Azure OpenAI inside of Microsoft Fabric, it most definitely fits into this category!
Up to $500 USD per team member, to be awarded in accordance with Section 10 (Participation Gratuity Options of official contest rules). Approximate Retail Value (ARV) $500 each.
Up to three (3) Microsoft Fabric SWAG packages – hoodie and blanket. Approximate Retail Value (ARV) $80.00 USD each.
Best use of Copilot for Microsoft Fabric: A solution that makes use of one or more Copilots for Microsoft Fabric. This could include any combination of Copilot for Power BI,Copilot for Data Science and Data Engineering, and / or Copilot for Data Factory.
Up to $500 USD per team member, to be awarded in accordance with Section 10 (Participation Gratuity Options of official contest rules). Approximate Retail Value (ARV) $500 each.
Up to three (3) Microsoft Fabric SWAG packages – hoodie and blanket. Approximate Retail Value (ARV) $80.00 USD each.
All hackathon participants who submit an app will receive a digital badge.
Join the fun!
Are you ready to hack? You will learn new skills, meet new people, and have fun along the way. Plus, you might win some awesome prizes!
So, what are you waiting for? Register NOW https://aka.ms/hacktogether-fabric-AI and start hacking! We can’t wait to see what you create!
Microsoft Tech Community – Latest Blogs –Read More
TLS 1.0 and 1.1 support will be removed for new & existing Azure storage accounts starting Nov 2024
To meet evolving technology and regulatory needs and align with security best practices, we are removing support for Transport Layer Security (TLS) 1.0 and 1.1 for both existing and new storage accounts in all clouds. TLS 1.2 will be the minimum supported TLS version for Azure Storage starting Nov 1, 2024.
Azure Storage currently supports TLS 1.0 and 1.1 (for backward compatibility) and TLS 1.2 on public HTTPS endpoints. TLS 1.2 is more secure and faster than older TLS versions. TLS 1.0 and 1.1 do not support modern cryptographic algorithms and cipher suites. Many of the Azure storage customers are already using TLS 1.2 and we are sharing this guidance to expedite the transition for customers currently on TLS 1.0 and 1.1. Customers must secure their infrastructure by using TLS 1.2 with Azure Storage by Oct 31, 2024. The older TLS versions (1.0 and 1.1) are being deprecated and removed to meet evolving standards (FedRamp, NIST), and provide improved security for our customers.
This change will impact both existing and new storage accounts using TLS 1.0 and 1.1. To avoid disruptions to your applications connecting to Azure Storage, you must migrate to TLS 1.2 and remove dependencies on TLS version 1.0 and 1.1, by Oct 31, 2024.
Learn more about how to migrate to TLS1.2.
As best practice, we also recommend using Azure policy to enforce a minimum TLS version. Learn more here about how to enforce a minimum TLS version for all incoming requests. If you already use Azure Policy to enforce TLS version, minimum supported version after this change rolls out will be TLS 1.2.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
TLS 1.0 and 1.1 support will be removed for new & existing Azure storage accounts starting Nov 2024
To meet evolving technology and regulatory needs and align with security best practices, we are removing support for Transport Layer Security (TLS) 1.0 and 1.1 for both existing and new storage accounts in all clouds. TLS 1.2 will be the minimum supported TLS version for Azure Storage starting Nov 1, 2024.
Azure Storage currently supports TLS 1.0 and 1.1 (for backward compatibility) and TLS 1.2 on public HTTPS endpoints. TLS 1.2 is more secure and faster than older TLS versions. TLS 1.0 and 1.1 do not support modern cryptographic algorithms and cipher suites. Many of the Azure storage customers are already using TLS 1.2 and we are sharing this guidance to expedite the transition for customers currently on TLS 1.0 and 1.1. Customers must secure their infrastructure by using TLS 1.2 with Azure Storage by Oct 31, 2024. The older TLS versions (1.0 and 1.1) are being deprecated and removed to meet evolving standards (FedRamp, NIST), and provide improved security for our customers.
This change will impact both existing and new storage accounts using TLS 1.0 and 1.1. To avoid disruptions to your applications connecting to Azure Storage, you must migrate to TLS 1.2 and remove dependencies on TLS version 1.0 and 1.1, by Oct 31, 2024.
Learn more about how to migrate to TLS1.2.
As best practice, we also recommend using Azure policy to enforce a minimum TLS version. Learn more here about how to enforce a minimum TLS version for all incoming requests. If you already use Azure Policy to enforce TLS version, minimum supported version after this change rolls out will be TLS 1.2.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
TLS 1.0 and 1.1 support will be removed for new & existing Azure storage accounts starting Nov 2024
To meet evolving technology and regulatory needs and align with security best practices, we are removing support for Transport Layer Security (TLS) 1.0 and 1.1 for both existing and new storage accounts in all clouds. TLS 1.2 will be the minimum supported TLS version for Azure Storage starting Nov 1, 2024.
Azure Storage currently supports TLS 1.0 and 1.1 (for backward compatibility) and TLS 1.2 on public HTTPS endpoints. TLS 1.2 is more secure and faster than older TLS versions. TLS 1.0 and 1.1 do not support modern cryptographic algorithms and cipher suites. Many of the Azure storage customers are already using TLS 1.2 and we are sharing this guidance to expedite the transition for customers currently on TLS 1.0 and 1.1. Customers must secure their infrastructure by using TLS 1.2 with Azure Storage by Oct 31, 2024. The older TLS versions (1.0 and 1.1) are being deprecated and removed to meet evolving standards (FedRamp, NIST), and provide improved security for our customers.
This change will impact both existing and new storage accounts using TLS 1.0 and 1.1. To avoid disruptions to your applications connecting to Azure Storage, you must migrate to TLS 1.2 and remove dependencies on TLS version 1.0 and 1.1, by Oct 31, 2024.
Learn more about how to migrate to TLS1.2.
As best practice, we also recommend using Azure policy to enforce a minimum TLS version. Learn more here about how to enforce a minimum TLS version for all incoming requests. If you already use Azure Policy to enforce TLS version, minimum supported version after this change rolls out will be TLS 1.2.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
TLS 1.0 and 1.1 support will be removed for new & existing Azure storage accounts starting Nov 2024
To meet evolving technology and regulatory needs and align with security best practices, we are removing support for Transport Layer Security (TLS) 1.0 and 1.1 for both existing and new storage accounts in all clouds. TLS 1.2 will be the minimum supported TLS version for Azure Storage starting Nov 1, 2024.
Azure Storage currently supports TLS 1.0 and 1.1 (for backward compatibility) and TLS 1.2 on public HTTPS endpoints. TLS 1.2 is more secure and faster than older TLS versions. TLS 1.0 and 1.1 do not support modern cryptographic algorithms and cipher suites. Many of the Azure storage customers are already using TLS 1.2 and we are sharing this guidance to expedite the transition for customers currently on TLS 1.0 and 1.1. Customers must secure their infrastructure by using TLS 1.2 with Azure Storage by Oct 31, 2024. The older TLS versions (1.0 and 1.1) are being deprecated and removed to meet evolving standards (FedRamp, NIST), and provide improved security for our customers.
This change will impact both existing and new storage accounts using TLS 1.0 and 1.1. To avoid disruptions to your applications connecting to Azure Storage, you must migrate to TLS 1.2 and remove dependencies on TLS version 1.0 and 1.1, by Oct 31, 2024.
Learn more about how to migrate to TLS1.2.
As best practice, we also recommend using Azure policy to enforce a minimum TLS version. Learn more here about how to enforce a minimum TLS version for all incoming requests. If you already use Azure Policy to enforce TLS version, minimum supported version after this change rolls out will be TLS 1.2.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
TLS 1.0 and 1.1 support will be removed for new & existing Azure storage accounts starting Nov 2024
To meet evolving technology and regulatory needs and align with security best practices, we are removing support for Transport Layer Security (TLS) 1.0 and 1.1 for both existing and new storage accounts in all clouds. TLS 1.2 will be the minimum supported TLS version for Azure Storage starting Nov 1, 2024.
Azure Storage currently supports TLS 1.0 and 1.1 (for backward compatibility) and TLS 1.2 on public HTTPS endpoints. TLS 1.2 is more secure and faster than older TLS versions. TLS 1.0 and 1.1 do not support modern cryptographic algorithms and cipher suites. Many of the Azure storage customers are already using TLS 1.2 and we are sharing this guidance to expedite the transition for customers currently on TLS 1.0 and 1.1. Customers must secure their infrastructure by using TLS 1.2 with Azure Storage by Oct 31, 2024. The older TLS versions (1.0 and 1.1) are being deprecated and removed to meet evolving standards (FedRamp, NIST), and provide improved security for our customers.
This change will impact both existing and new storage accounts using TLS 1.0 and 1.1. To avoid disruptions to your applications connecting to Azure Storage, you must migrate to TLS 1.2 and remove dependencies on TLS version 1.0 and 1.1, by Oct 31, 2024.
Learn more about how to migrate to TLS1.2.
As best practice, we also recommend using Azure policy to enforce a minimum TLS version. Learn more here about how to enforce a minimum TLS version for all incoming requests. If you already use Azure Policy to enforce TLS version, minimum supported version after this change rolls out will be TLS 1.2.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
TLS 1.0 and 1.1 support will be removed for new & existing Azure storage accounts starting Nov 2024
To meet evolving technology and regulatory needs and align with security best practices, we are removing support for Transport Layer Security (TLS) 1.0 and 1.1 for both existing and new storage accounts in all clouds. TLS 1.2 will be the minimum supported TLS version for Azure Storage starting Nov 1, 2024.
Azure Storage currently supports TLS 1.0 and 1.1 (for backward compatibility) and TLS 1.2 on public HTTPS endpoints. TLS 1.2 is more secure and faster than older TLS versions. TLS 1.0 and 1.1 do not support modern cryptographic algorithms and cipher suites. Many of the Azure storage customers are already using TLS 1.2 and we are sharing this guidance to expedite the transition for customers currently on TLS 1.0 and 1.1. Customers must secure their infrastructure by using TLS 1.2 with Azure Storage by Oct 31, 2024. The older TLS versions (1.0 and 1.1) are being deprecated and removed to meet evolving standards (FedRamp, NIST), and provide improved security for our customers.
This change will impact both existing and new storage accounts using TLS 1.0 and 1.1. To avoid disruptions to your applications connecting to Azure Storage, you must migrate to TLS 1.2 and remove dependencies on TLS version 1.0 and 1.1, by Oct 31, 2024.
Learn more about how to migrate to TLS1.2.
As best practice, we also recommend using Azure policy to enforce a minimum TLS version. Learn more here about how to enforce a minimum TLS version for all incoming requests. If you already use Azure Policy to enforce TLS version, minimum supported version after this change rolls out will be TLS 1.2.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
TLS 1.0 and 1.1 support will be removed for new & existing Azure storage accounts starting Nov 2024
To meet evolving technology and regulatory needs and align with security best practices, we are removing support for Transport Layer Security (TLS) 1.0 and 1.1 for both existing and new storage accounts in all clouds. TLS 1.2 will be the minimum supported TLS version for Azure Storage starting Nov 1, 2024.
Azure Storage currently supports TLS 1.0 and 1.1 (for backward compatibility) and TLS 1.2 on public HTTPS endpoints. TLS 1.2 is more secure and faster than older TLS versions. TLS 1.0 and 1.1 do not support modern cryptographic algorithms and cipher suites. Many of the Azure storage customers are already using TLS 1.2 and we are sharing this guidance to expedite the transition for customers currently on TLS 1.0 and 1.1. Customers must secure their infrastructure by using TLS 1.2 with Azure Storage by Oct 31, 2024. The older TLS versions (1.0 and 1.1) are being deprecated and removed to meet evolving standards (FedRamp, NIST), and provide improved security for our customers.
This change will impact both existing and new storage accounts using TLS 1.0 and 1.1. To avoid disruptions to your applications connecting to Azure Storage, you must migrate to TLS 1.2 and remove dependencies on TLS version 1.0 and 1.1, by Oct 31, 2024.
Learn more about how to migrate to TLS1.2.
As best practice, we also recommend using Azure policy to enforce a minimum TLS version. Learn more here about how to enforce a minimum TLS version for all incoming requests. If you already use Azure Policy to enforce TLS version, minimum supported version after this change rolls out will be TLS 1.2.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
TLS 1.0 and 1.1 support will be removed for new & existing Azure storage accounts starting Nov 2024
To meet evolving technology and regulatory needs and align with security best practices, we are removing support for Transport Layer Security (TLS) 1.0 and 1.1 for both existing and new storage accounts in all clouds. TLS 1.2 will be the minimum supported TLS version for Azure Storage starting Nov 1, 2024.
Azure Storage currently supports TLS 1.0 and 1.1 (for backward compatibility) and TLS 1.2 on public HTTPS endpoints. TLS 1.2 is more secure and faster than older TLS versions. TLS 1.0 and 1.1 do not support modern cryptographic algorithms and cipher suites. Many of the Azure storage customers are already using TLS 1.2 and we are sharing this guidance to expedite the transition for customers currently on TLS 1.0 and 1.1. Customers must secure their infrastructure by using TLS 1.2 with Azure Storage by Oct 31, 2024. The older TLS versions (1.0 and 1.1) are being deprecated and removed to meet evolving standards (FedRamp, NIST), and provide improved security for our customers.
This change will impact both existing and new storage accounts using TLS 1.0 and 1.1. To avoid disruptions to your applications connecting to Azure Storage, you must migrate to TLS 1.2 and remove dependencies on TLS version 1.0 and 1.1, by Oct 31, 2024.
Learn more about how to migrate to TLS1.2.
As best practice, we also recommend using Azure policy to enforce a minimum TLS version. Learn more here about how to enforce a minimum TLS version for all incoming requests. If you already use Azure Policy to enforce TLS version, minimum supported version after this change rolls out will be TLS 1.2.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
TLS 1.0 and 1.1 support will be removed for new & existing Azure storage accounts starting Nov 2024
To meet evolving technology and regulatory needs and align with security best practices, we are removing support for Transport Layer Security (TLS) 1.0 and 1.1 for both existing and new storage accounts in all clouds. TLS 1.2 will be the minimum supported TLS version for Azure Storage starting Nov 1, 2024.
Azure Storage currently supports TLS 1.0 and 1.1 (for backward compatibility) and TLS 1.2 on public HTTPS endpoints. TLS 1.2 is more secure and faster than older TLS versions. TLS 1.0 and 1.1 do not support modern cryptographic algorithms and cipher suites. Many of the Azure storage customers are already using TLS 1.2 and we are sharing this guidance to expedite the transition for customers currently on TLS 1.0 and 1.1. Customers must secure their infrastructure by using TLS 1.2 with Azure Storage by Oct 31, 2024. The older TLS versions (1.0 and 1.1) are being deprecated and removed to meet evolving standards (FedRamp, NIST), and provide improved security for our customers.
This change will impact both existing and new storage accounts using TLS 1.0 and 1.1. To avoid disruptions to your applications connecting to Azure Storage, you must migrate to TLS 1.2 and remove dependencies on TLS version 1.0 and 1.1, by Oct 31, 2024.
Learn more about how to migrate to TLS1.2.
As best practice, we also recommend using Azure policy to enforce a minimum TLS version. Learn more here about how to enforce a minimum TLS version for all incoming requests. If you already use Azure Policy to enforce TLS version, minimum supported version after this change rolls out will be TLS 1.2.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
TLS 1.0 and 1.1 support will be removed for new & existing Azure storage accounts starting Nov 2024
To meet evolving technology and regulatory needs and align with security best practices, we are removing support for Transport Layer Security (TLS) 1.0 and 1.1 for both existing and new storage accounts in all clouds. TLS 1.2 will be the minimum supported TLS version for Azure Storage starting Nov 1, 2024.
Azure Storage currently supports TLS 1.0 and 1.1 (for backward compatibility) and TLS 1.2 on public HTTPS endpoints. TLS 1.2 is more secure and faster than older TLS versions. TLS 1.0 and 1.1 do not support modern cryptographic algorithms and cipher suites. Many of the Azure storage customers are already using TLS 1.2 and we are sharing this guidance to expedite the transition for customers currently on TLS 1.0 and 1.1. Customers must secure their infrastructure by using TLS 1.2 with Azure Storage by Oct 31, 2024. The older TLS versions (1.0 and 1.1) are being deprecated and removed to meet evolving standards (FedRamp, NIST), and provide improved security for our customers.
This change will impact both existing and new storage accounts using TLS 1.0 and 1.1. To avoid disruptions to your applications connecting to Azure Storage, you must migrate to TLS 1.2 and remove dependencies on TLS version 1.0 and 1.1, by Oct 31, 2024.
Learn more about how to migrate to TLS1.2.
As best practice, we also recommend using Azure policy to enforce a minimum TLS version. Learn more here about how to enforce a minimum TLS version for all incoming requests. If you already use Azure Policy to enforce TLS version, minimum supported version after this change rolls out will be TLS 1.2.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
TLS 1.0 and 1.1 support will be removed for new & existing Azure storage accounts starting Nov 2024
To meet evolving technology and regulatory needs and align with security best practices, we are removing support for Transport Layer Security (TLS) 1.0 and 1.1 for both existing and new storage accounts in all clouds. TLS 1.2 will be the minimum supported TLS version for Azure Storage starting Nov 1, 2024.
Azure Storage currently supports TLS 1.0 and 1.1 (for backward compatibility) and TLS 1.2 on public HTTPS endpoints. TLS 1.2 is more secure and faster than older TLS versions. TLS 1.0 and 1.1 do not support modern cryptographic algorithms and cipher suites. Many of the Azure storage customers are already using TLS 1.2 and we are sharing this guidance to expedite the transition for customers currently on TLS 1.0 and 1.1. Customers must secure their infrastructure by using TLS 1.2 with Azure Storage by Oct 31, 2024. The older TLS versions (1.0 and 1.1) are being deprecated and removed to meet evolving standards (FedRamp, NIST), and provide improved security for our customers.
This change will impact both existing and new storage accounts using TLS 1.0 and 1.1. To avoid disruptions to your applications connecting to Azure Storage, you must migrate to TLS 1.2 and remove dependencies on TLS version 1.0 and 1.1, by Oct 31, 2024.
Learn more about how to migrate to TLS1.2.
As best practice, we also recommend using Azure policy to enforce a minimum TLS version. Learn more here about how to enforce a minimum TLS version for all incoming requests. If you already use Azure Policy to enforce TLS version, minimum supported version after this change rolls out will be TLS 1.2.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
TLS 1.0 and 1.1 support will be removed for new & existing Azure storage accounts starting Nov 2024
To meet evolving technology and regulatory needs and align with security best practices, we are removing support for Transport Layer Security (TLS) 1.0 and 1.1 for both existing and new storage accounts in all clouds. TLS 1.2 will be the minimum supported TLS version for Azure Storage starting Nov 1, 2024.
Azure Storage currently supports TLS 1.0 and 1.1 (for backward compatibility) and TLS 1.2 on public HTTPS endpoints. TLS 1.2 is more secure and faster than older TLS versions. TLS 1.0 and 1.1 do not support modern cryptographic algorithms and cipher suites. Many of the Azure storage customers are already using TLS 1.2 and we are sharing this guidance to expedite the transition for customers currently on TLS 1.0 and 1.1. Customers must secure their infrastructure by using TLS 1.2 with Azure Storage by Oct 31, 2024. The older TLS versions (1.0 and 1.1) are being deprecated and removed to meet evolving standards (FedRamp, NIST), and provide improved security for our customers.
This change will impact both existing and new storage accounts using TLS 1.0 and 1.1. To avoid disruptions to your applications connecting to Azure Storage, you must migrate to TLS 1.2 and remove dependencies on TLS version 1.0 and 1.1, by Oct 31, 2024.
Learn more about how to migrate to TLS1.2.
As best practice, we also recommend using Azure policy to enforce a minimum TLS version. Learn more here about how to enforce a minimum TLS version for all incoming requests. If you already use Azure Policy to enforce TLS version, minimum supported version after this change rolls out will be TLS 1.2.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
TLS 1.0 and 1.1 support will be removed for new & existing Azure storage accounts starting Nov 2024
To meet evolving technology and regulatory needs and align with security best practices, we are removing support for Transport Layer Security (TLS) 1.0 and 1.1 for both existing and new storage accounts in all clouds. TLS 1.2 will be the minimum supported TLS version for Azure Storage starting Nov 1, 2024.
Azure Storage currently supports TLS 1.0 and 1.1 (for backward compatibility) and TLS 1.2 on public HTTPS endpoints. TLS 1.2 is more secure and faster than older TLS versions. TLS 1.0 and 1.1 do not support modern cryptographic algorithms and cipher suites. Many of the Azure storage customers are already using TLS 1.2 and we are sharing this guidance to expedite the transition for customers currently on TLS 1.0 and 1.1. Customers must secure their infrastructure by using TLS 1.2 with Azure Storage by Oct 31, 2024. The older TLS versions (1.0 and 1.1) are being deprecated and removed to meet evolving standards (FedRamp, NIST), and provide improved security for our customers.
This change will impact both existing and new storage accounts using TLS 1.0 and 1.1. To avoid disruptions to your applications connecting to Azure Storage, you must migrate to TLS 1.2 and remove dependencies on TLS version 1.0 and 1.1, by Oct 31, 2024.
Learn more about how to migrate to TLS1.2.
As best practice, we also recommend using Azure policy to enforce a minimum TLS version. Learn more here about how to enforce a minimum TLS version for all incoming requests. If you already use Azure Policy to enforce TLS version, minimum supported version after this change rolls out will be TLS 1.2.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More