Tag Archives: microsoft
Access Releases 9 Issue Fixes in Version 2312 (Released January 4th, 2024)
Our newest round of Access bug fixes was released on January 4th, 2024. In this blog post, we highlight some of the fixed issues that our Access engineers released in the current monthly channel.
If you see a bug that impacts you, and if you are on the current monthly channel Version 2312, you should have these fixes. Make sure you are on Access Build # 16.0.17126.20126 or greater.
Bug Name
Issue Fixed
No list of font sizes when Aptos font is selected
Aptos is the default font for controls in a new database using the recently updated ‘Office Theme,’ but the font size drop down was not displaying a list of font sizes (although you could manually type in a font size).
When a query was open in datasheet or design view, the context menu command to open in SQL View in the navigation pane would not switch the open query to SQL View
This command on the context menu was recently added to allow opening a query directly into SQL view. However, to be consistent with other commands, it now switches the mode of a query that is already open to SQL view.
#Error when using DateDiff with one Date/Time column and one Date/Time Extended column
The DateDiff function was working correctly if both arguments were of type Date/Time, or both arguments were of type Date/Time Extended but would fail to evaluate with one argument of each type.
The updated linked table manager no longer shows the name of the DSN used for a linked table
The old, linked table manager displayed this information. The new linked table manager now also displays it.
Access may terminate unexpectedly when running a macro after editing it
In some cases, after adding/removing/moving macro actions in the macro designer, then attempting to run the macro, Access would terminate unexpectedly. This no longer occurs.
F1 does not display the correct help page when used on some properties/methods of the Field2 object in the VBA IDE
F1 now directs to the appropriate help page for the following properties/methods:
CreateProperty, Expression, IsComplex, Name, Required, SourceTable, Type, ValidationRule, ValidationText, and Value.
Some valid values for the DBEngine.SetOption method have no defined constant
The following constants were added:
dbPagesLockedToTableLock, dbPasswordEncryptionProvider, dbPasswordEncryptionAlgorithm, dbPasswordEncryptionKeyLength
Subform control does not support LabelName property
The LabelName property was shown in the property sheet for every other control that supported child labels and is now present for subform controls as well.
Auto expand in combo boxes doesn’t work for list items >100 index
In some cases, autocomplete did not work for items in a dropdown list when there were more than 100 items in the list. This issue has been resolved.
Please continue to let us know if this is helpful and share any feedback you have.
Microsoft Tech Community – Latest Blogs –Read More
Logic Apps Mission Critical Series: “We Speak: IBM i: COBOL and RPG Applications”
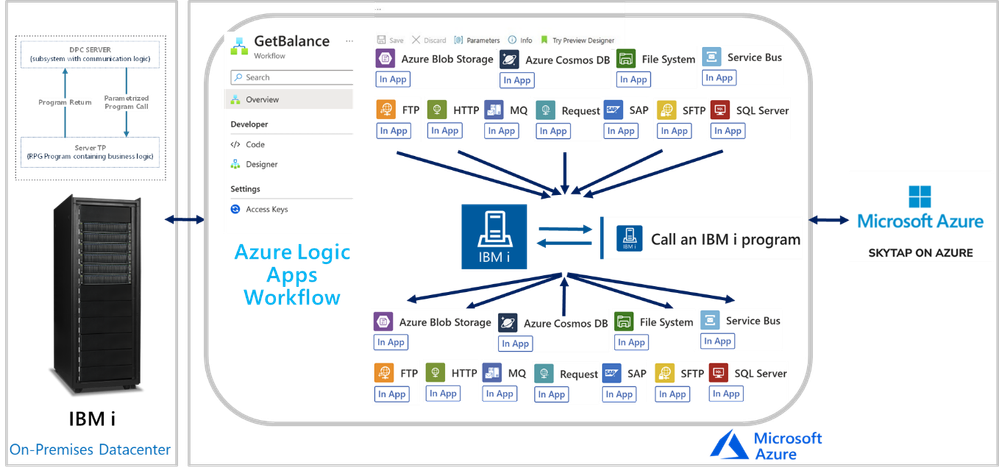
In this session, we continue with the “We Speak”, Mission Critical Series with an episode on how Azure Logic Apps can unlock scenarios where is required to integrate with IBM i (i Series or former AS/400) Applications.
The IBM i In-App Connector
The IBM i In-App connector enables connections between Logic App workflows to IBM i Applications running on IBM Power Systems.
Background:
More than 50 years ago, IBM released the first midrange systems. IBM advertised them as “Small in size, small in price and Big in performance. It is a system for now and for the future”. Over the years, the midranges evolved and became pervasive in medium size businesses or in large enterprises to extend Mainframe environments. Midranges running IBM i (typically Power systems), support TCP/IP and SNA. Host Integration Server supports connecting with midranges using both.
IBM i includes the Distributed Program Calls (DPC) server feature that allows most IBM System i applications to interact with clients such as Azure Logic Apps in request-reply fashion (client-initiated only) with minimum modifications. DPC is a documented protocol that supports program to program integration on an IBM System i, which can be accessed easily from client applications using the TCP/IP networking protocol.
IBM i Applications were typically built using the Report Program Generator (RPG) or the COBOL languages. The Azure Logic Apps connector for IBM i supports integrating with both types of programs. The following is a simple RPG program called CDRBANKRPG.
As with many of our other IBM Mainframe connectors, it is required to prepare an artifact with the metadata of the IBM i programs to call by using the HIS Designer for Logic Apps tool. The HIS Designer will help you creating a Host Integration Design XML file (HIDX) for use with the IBM i connector. The following is a view of the outcome of the HIDX file for the program above.
For instructions on how to create this metadata artifacts, you can watch this video:
Once you have the HIDX file ready for deployment, you will need to upload it in the Maps artifacts of your Azure Logic App and then create a workflow and add the IBM 3270 i Connector.
To set up the IBM i Connector, you will require inputs from the midrange Specialist. You will require at least the midrange IP and Port.
In the Parameters section, enter the name of the HIDX file. If the HIDX was uploaded to Maps, then it should appear dynamically:
And then select the method name:
The following video include a complete demonstration of the use of the IBM i In-App connector for Azure Logic Apps:
Microsoft Tech Community – Latest Blogs –Read More
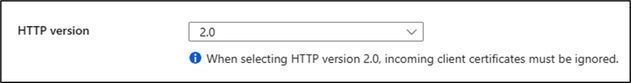
Send HTTP 2.0 Request to App Service using C#
Azure App Service supports HTTP 2.0. The major advance of HTTP/1.1 was the use of persistent connections to service multiple requests in a row. In HTTP/2, a persistent connection can be used to service multiple simultaneous requests.
This blog will demonstrate how you can send HTTP 2.0 Request to app service for testing using C#:
Step 1:
Go to > App Service > Configuration > Enable HTTP 2.0
Step 2:
Create a .Net Core Console Application / Web Application as per requirement . In this example I have taken a .Net Core Console Application:
var client = new HttpClient() { BaseAddress = new Uri(“https://<>.azurewebsites.net”) };
Console.WriteLine(“Sending HTTP 2.0 Request.”);
// HTTP/2 request
using (var request = new HttpRequestMessage(HttpMethod.Get, “/”) { Version = new Version(2, 0) })
using (var response = await client.SendAsync(request))
Console.WriteLine(response);
The HTTPClient class has DefaultRequestVersion property with which you can set the default version of the requests as below:
var SecondRequest = new HttpClient()
{
BaseAddress = new Uri(“https://<>.azurewebsites.net”),
DefaultRequestVersion = new Version(2, 0)
};
// HTTP/2 is default
using (var response = await SecondRequest.GetAsync(“/”))
Console.WriteLine(response);
You should be able to see a successful HTTP Response once the code executes:
For more information you can refer the below documents:
HttpClient Class (System.Net.Http) | Microsoft Learn
HttpClient.DefaultRequestVersion Property (System.Net.Http) | Microsoft Learn
Microsoft Tech Community – Latest Blogs –Read More
Empowering Healthcare with Innovative Solutions: A Microsoft Power Apps Project (UCL x NHS)
Introduction:
Greetings, fellow enthusiasts of technology and innovation! Today, I’m excited to share an incredible journey undertaken by our team of four UCL MSc Computer Science students. Over the past three months, we’ve had the privilege of working on three transformative projects aimed at optimizing healthcare operations using Microsoft Power Platform. Allow me to take you through the remarkable venture that is Bed Management Power Apps, TasCare, and E-Rostering Power Apps.
Meet the Team:
Before we dive into the projects, let me introduce our talented team:
1. Judy Chin
– LinkedIn: https://www.linkedin.com/in/judy-giaying-chin/
– Project team lead; Developer of TasCare
2. Lee-Yu Yeh
– LinkedIn: https://www.linkedin.com/in/leeyu-yeh-67378b20a/
– Developer of E-Rostering Manager App
3. Tania Turdean
– LinkedIn: https://www.linkedin.com/in/tania-turdean-8530aa160/
– Developer of E-Rostering Power Apps User App
4. Wenjin Yang
– LinkedIn: https://www.linkedin.com/in/wenjin-yang-28a481256/
– Developer of Bed Management Power Apps
Project Overview:
Our journey began with a mission to address critical issues in healthcare and social care management. The three projects – Bed Management Power Apps, TasCare, and E-Rostering Power Apps – were crafted to streamline processes, enhance efficiency, and provide impactful solutions to real-world problems.
Project Journey:
Navigating the intricate world of healthcare, our team encountered challenges and triumphs alike. We meticulously developed low-code, hybrid applications using Microsoft Power Apps to adapt seamlessly to mobile or web platforms. Challenges such as complex bed management systems and time-consuming shift scheduling were tackled head-on, with innovative solutions emerging at every turn. Through weekly Teams calls with our external supervisor Stephanie Stasey, we quickly understood the current hot issues in healthcare and dived into solving the problems via Microsoft technologies.
Technical Details:
In the realm of technology, specifics matter. The Microsoft Power Platform became our ally, empowering us to create solutions that are both dynamic and user-friendly. Bed Management Power Apps, TasCare, and E-Rostering Power Apps were carefully designed, leveraging the capabilities of Power Apps to bring efficiency to healthcare operations.
Using Power Apps as our main developing environment, which not only boasts the advantage of low-code but also, can easily seamlessly be combined with other Microsoft Power Platform technologies.
Dataverse, SharePoint – Seamless connection to Bed Management App live data
Power Automate – Regeneration of repeat tasks daily, weekly, and monthly in TasCare
High-complexity, low-code application – E-Rostering Power Apps
App Details & Demos:
See our project website for more details: UCL Power Apps For NHS
Bed Management Power Apps
Bed Management Power Apps address the challenge within hospitals where intricate bed management systems impede the efficiency of tasks such as patient admissions and discharges.
Github Solution: Bed Management Power Apps Solution
Demo Video:
TasCare
TasCare strives to assist workers in organizing their daily responsibilities through a mobile app, offering various features like documenting refusals and reporting incidents.
See Details and App Solution: TasCare – A Social Care Task Management Power Apps
Demo:
E-Rostering Power Apps
E-Rostering Power Apps addresses the challenge faced by hospital ward managers who spend extensive hours managing and scheduling shifts, presenting a streamlined and dependable system as the solution.
Solution: Please see our project website for details
Demo: (Admin App & User App)
Results and Outcomes:
The culmination of our efforts has led to tangible results. Whether it’s the expedited bed management processes, the streamlined social care task management through TasCare, or the simplified shift scheduling with E-Rostering Power Apps.
These application solutions are open to download and import to your own environment as solutions. See more in the individual project pages above.
Reflections
Reflecting on this journey, we’ve grown not only as developers but as problem solvers. The challenges we faced taught us resilience, adaptability, and the importance of collaboration. Each hurdle was an opportunity for personal and professional growth.
A heartfelt appreciation extends to Microsoft, Stephanie Stasey, and the NHS for their pivotal roles in our healthcare innovation journey. Microsoft’s cutting-edge Power Platform empowered us to develop transformative solutions, while Stephanie Stasey’s guidance on the healthcare sector served as a guiding light, shaping our project’s success. The NHS’s commitment to embracing technology and improving healthcare services provided us with a meaningful platform to make a positive impact. Together, this collaboration symbolizes the fusion of technology and compassion, driving us towards a future where healthcare is not just efficient but profoundly human. Our sincere thanks to these partners for their unwavering support, commitment to innovation, and the opportunity to contribute to the advancement of healthcare.
Future Development:
As we look to the future, our commitment to innovation remains unwavering. We envision enhancements, additional features, and further research to continually refine and expand the impact of Bed Management Power Apps, TasCare, and E-Rostering Power Apps. The journey doesn’t end here; it’s a stepping stone to greater possibilities.
Conclusion:
In conclusion, this journey has been nothing short of transformative. We’ve witnessed the power of technology to revolutionize healthcare and social care, making a positive impact on the lives of professionals and, ultimately, the patients they serve. Our journey has only just begun, and the potential for further innovation is boundless.
Are you intrigued by the intersection of technology and healthcare? Explore the Microsoft Learn Modules/Docs related to Power Platform to delve deeper into the tools that fueled our journey. Engage with us, ask questions, and let’s continue this dialogue for a brighter, more efficient future in healthcare.
Thank you for joining us on this adventure – together, we can shape a healthier, technologically empowered world.
Microsoft Tech Community – Latest Blogs –Read More
Contextual Risk Estimation for Effective Prioritization
Handling Cloud Posture Tasks Overload
Cybersecurity risks pose a significant threat to organizations of all sizes. As a result, security teams must be diligent in their efforts to protect their networks and data from potential breaches. However, with the increasing complexity of the digital environment and the expanding attack surface, security teams are faced with more and more tasks to improve the organization’s posture as well as investigating potential incidents. This can lead to critical security risks being overlooked or delayed, leaving organizations vulnerable to cyber-attacks. It becomes increasingly more important to estimate the risk created by the security issues in the environment’s configuration and to prioritize their mitigation correctly.
Prioritized cyber risks allow security teams to focus their efforts and resources on the most critical threats, ensuring that they are addressed promptly and effectively, which ultimately helps to reduce the organization’s overall risk profile.
Basic prioritization systems assign a static severity rating to each issue, a rating that is determined at the issue’s definition stage. This rating is based on an assumed or estimated potential impact of the threat. Devices vulnerable to the same vulnerability are evaluated to be of the same severity whether the vulnerable resource is of high business criticality and exposed, or it is an isolated insignificant resource vulnerability which cannot be exploited. That is to say, the specific details of an issue’s instance are not considered which is a significant shortcoming.
A well-established concept in risk assessment involves the dependence of risk on two critical components: the likelihood of a successful attack and the impact that such an attack can have. The relationship is frequently represented by the formula Risk = Likelihood × Impact.
More sophisticated and informed prioritization systems look further than the issue type but also the contextual information of each manifestation. It includes considering the impacted resource criticality, likelihood of exploitation, and other factors to estimate the risk posed by an issue correctly. In this blog post, we introduce a new framework for methodic estimation and scoring of risk.
The framework is based on contextual information, and we demonstrate how this risk estimation is used to prioritize the mitigation of security issues found in the environment. The risk calculation process, we consider both likelihood and impact, recognizing their significance in evaluating and managing risks effectively. By thoroughly assessing these factors, we aim to make informed decisions and develop strategies to mitigate potential threats and vulnerabilities.
Microsoft Defender for Cloud has recently introduced a new feature for Defender CSPM helping customers to rank the security issues in their environment configuration and fix them accordingly. This feature is based on the presented framework and enhances the risk prioritization capabilities of Defender CSPM.
From Concept to Reality: Prioritization Concepts
Overview
The framework enhances the basic severity score of an issue by factoring in the likelihood of a successful attack and its potential impact, empowering security teams with precise task prioritization for improved accuracy and effectiveness. The high customizability and extensibility make it suitable for any product to create prioritized task lists, whether security-related or not. It allows the incorporation of scenarios and contextual information specific to each product’s area of expertise. By empowering end-users to define the value of assets and behaviors, they have the freedom to adjust the prioritization according to their preferences. This approach enables organizations to enhance their overall cybersecurity posture and effectively secure their resources.
Prioritization is accomplished in several steps:
Security issues are enriched with contextual information.
The security issue is scored using a new method, described below.
Issues of the same risk type and security score form a group.
Groups are prioritized in descending score order.
Within each group items are sorted more precisely. This process is discussed later in this post.
In the following sections, we will explain in detail the core concepts of the new framework: security issues, contextual information, contextual security issue (CSI) and the contextual security matrix (CSM).
Security issue (SI)
The term “security issue” refers to the type of fault that requires attention, and may be indicative of increased likelihood of a successful attack, increased impact, or both. In Microsoft Defender for Cloud issues are surfaced as recommendations, which are actions that should be taken to resolve the fault and improve the overall posture and security of the environment. An issue may be realized in multiple ways and aspects. As a result, several recommendations can be an indication for the same issue. For example, both “Machines should have vulnerability findings resolved” and “SQL databases should have vulnerability findings resolved” point to the same security issue: a resource is vulnerable (and therefore, should be patched). Issues are not limited to the cloud: a vulnerability on an on-premises computer is also afflicted by the same issue. Some of the key issues in cloud environment are “Unnecessary internet reachability”, “excessive permissions”, and “vulnerability”.
Contextual Information
Contextual information is any information that affects the estimation of the hazard caused by a security issue. Contextual information could be about the methods and feasibility of exploitation of that issue, about the level and type of risk to the organization if a resource is compromised or information that may indicate an immediate intent, previous or current attempts to exploit the issue.
Like SI, contextual information could be related to increased likelihood or impact. For example, the use of a common username for authentication creates a risk as it could be a target for a password brute force guessing attack. The impact of such an issue is much greater when the asset the user has access to is the intellectual property of the organization than if the user can only access an isolated virtual machine. A resource’s exposure to the internet enhances the risk that a vulnerability on a resource would be exploited, and therefore it is crucial information to evaluate the urgency of patching the vulnerability. It might be more urgent to handle a configuration issue of a running VM than an issue concerning a shutdown VM or prioritize a resource that is known to be a target for past attacks.
Contextual Security Issue
A Contextual Security Issue (CSI) is a security issue enriched with contextual information.
Consider, for example, a vulnerable VM. The vulnerable VM poses a “Security Issue” that requires remediation. If the VM is exposed to the internet, it increases the risk of exploitation by an external attacker and therefore the internet exposure is considered “a contextual information”. Similarly, if the VM stores credentials to a critical asset, the stored credentials are also considered contextual information as they can be used to move laterally and compromise the critical asset. When the issue (vulnerability) is enriched with contextual information it forms the CSI: “Internet exposed vulnerable VM containing sensitive data“.
In certain scenarios the internet exposure itself may be a security issue, certainly the stored credentials are a security issue. Indeed, an issue could serve as a context for the evaluation of another issue’s risk. To summarize, a CSI expresses how the affected resource can be reached, the risk in compromising the resource itself, how the issue can be exploited and used to proceed to further compromise resources and the damage that may be caused.
The Contextual Security Matrix and CSI Score
So far, we have explained the significance of the context in which the issue exists. Let us examine how contextual information influences our risk estimation. Consider a resource vulnerable to remote code execution. We want to estimate the risk to the resource and environment and prioritize it compared to other issues in the queue. The contextual information that the resource is currently running, indicates that the vulnerability is in increased risk of exploitation. Consequently, this leads to an elevated risk evaluation. Let us also consider a resource that is not encrypted at rest. The risk created by the lack of encryption does not vary much whether the resource is running or not. We see that the same context may be insignificant to some issues, and incredibly significant to another. The CSM is a framework for quantifying the CSI security risk based on that understanding. The matrix reflects the degree a security issue risk increases or decreases when it occurs within a specific context.
Fig. 1: Contextual Score Matrix structure
The CSM consists of columns representing the different security issues, each assigned a “base score.” The rows correspond to potential contexts. The matrix’s cells indicate the differential score for a specific issue (column) considering the given context(s) (rows). To calculate the CSI score, the base score of the issue is summed with the applicable contextual differential scores.
The following example demonstrates the calculation of a CSI score for a vulnerability on an exposed VM that has permission to a critical asset. To calculate a CSI’s security score, we refer to the issue’s column in the matrix. We sum the base score and the values of the contexts included in the CSI. The score for the issue (i.e., the vulnerability) in the context of the applicable contexts (exposure and access) is calculated to be 13=5+(3+5).
Fig. 2: Vulnerable Exposed VM with permissions to a critical asset
The framework is extensible and adjustable. Organizations can add columns to the matrix to account for issues that are not currently considered or replace an issue with multiple more specific issues. Contexts can also be added to account for additional information if such is available. MDC prioritization is criticality biased, that is, it prioritizes protection of a critical asset over multiple non-critical assets. By adjusting the matrix weights, organizations can create a preference or a bias that better fits their needs. Contexts in the matrix may be added to support the highlighting and suppression of certain resources. This can be achieved by adding a flag context to increase the score or a flag context that reduces it for uninteresting resources. For example, a honeypot or a dev device that is deliberately left weakened.
Primary Group
The previous section explained how a CSI score is calculated. A security issue that is a part of multiple CSIs will be scored for each CSI, i.e., a list of CSI scores is calculated for it. The security issue is finally scored with the maximal CSI score on its list. This score is the issue’s Primary Score. This scoring method is where the emphasis of business criticality over the number of resources is introduced. Issues of the same primary score and issue type are grouped into a Primary Group. The primary groups are prioritized from the highest score to lowest.
Secondary Prioritization
The primary prioritization described above is criticality biased in the sense that it prioritizes security issues that expose sensitive and important resources over those risking multiple less significant resources. We prioritize one crown jewel over a stack of rocks. The complexity of exploitation of resources is considered: when a misconfigured resource is identified the primary prioritization looks to find other resources that could be “easily compromised” and may allow up to one “complicated step”.
The secondary prioritization prioritizes within the primary group, and prioritizes issues exposing more resources over those who expose fewer, and prioritizes simple exploitation routes over complex ones. This prioritization cannot result in an issue “escaping” the primary group.
Several parameters are used to determine the secondary prioritization.
The list of compromised resources: an issue that creates a risk to a greater number of resources will have a higher risk estimation score. Since we value criticality, we promote first based on the number of high-importance resources, if these match we prefer the one that has greater number of less-important resources
If several path exist that lead to similarly critical resource the simple CSIs are promoted over more complicated ones. This is achieved by assigning a decay factor, a value between 0 and 1, to each step that propagates the foreseen attack from one resourceidentity to another. The easier it is to transition to the next resource- the higher the factor. For example: using clear text credentials on a machine to log to a resource is easy, therefore the factor is high, say, 0.9.
Using a vulnerability to stealthily take hold of a resource requires a more skilled attacker and the factor would be lower, 0.4. From this factor rises the definition for “easily compromised” and “complicated step” – steps with decay factor higher then 0.5 are considered easy, lower are considered difficult.
The score of the CSI is multiplied by its’ steps decay factors, reducing the score of more complex and longer path over shorter and simpler ones.
Figures 3,4: Step for posture management task prioritization
Summary
The introduced framework is a new method that was developed to evaluate risk and prioritize the tasks needed for the strengthening of the environment configuration and posture. Using this framework, issues can be addressed in a manner that best serves the security needs of the organization, allowing for better management and quicker improvement and reduction of attack surface. The method emphasizes critical assets and prevents multitude of less significant issues from overshadowing the crucial and immediate threats. The framework is flexible and can easily be adjusted and extended to include specific or new scenarios.
Appendix 1: Issues
Software vulnerability
Description
A resource may be at increased risk of being compromised, attacked, or exploited due to a software flaw.
Examples
A server is vulnerable to Log4Shell vulnerability (CVE-2021-44228), increasing the risk of exploitation by a remote malicious code execution.
Anonymous access
Description
A resource can be accessed without being required to provide identifying information, allowing untrusted actors to access data or compute resources and potentially do harm.
Example
Storage resources open to public may lead to unauthorized access to sensitive data, as well as data breaches and corruption. Additionally, public storage resources may be used to spread malware.
Excessive permissions
Description
An identity is allowed to access more resources than is necessary for its intended function, providing opportunities for malicious actors to gain access to sensitive data or systems.
Example
Simple user that has subscription permission,
A service account that only needs “read” permission to a database but is also granted “delete” permission may be used to corrupt the database, if compromised.
No MFA
Description
Multi-Factor Authentication (MFA) is not enabled for users of certain type. A user without MFA enabled is at a higher risk of having their account accessed by unauthorized individuals, such as through phishing attacks or password guessing.
Example
A company that only requires employees to use a username and password to access their email accounts.
The Target data breach of November 2013 started when attackers managed to steal a third-party contractor’s password through a phishing attack. Since no MFA was required, the attackers were able to use the stolen credentials to access Target systems.
Default account
Description
The use of a preconfigured user account in a system or application that has a default username and password. Actors may be able to use guessed or known default usernames and passwords to gain unauthorized access to sensitive data or system.
Example
Devices are often provided with default usernames such as “root” and “admin”. The Mirai botnet was able to spread by brute-forcing default usernames and passwords on Internet of Things (IoT) devices, disrupting major websites such as Netflix, PayPal, and others.
Usage of local Identity services
Description
Authentication and authorization should be managed by the central identity provider since it allows for more granular control over which resources and systems each user can access.
Example
Use Azure Active Directory authentication for Azure Kubernetes Service clusters.
Privilege escalation
Description
The resource is using a risky configuration that might allow privilege escalation. If compromised, an attacker may gain higher privileges and potentially get full control over the resource.
Example
A container that runs as a privileged container allows a container to access host resources including modifying the filesystem and gaining elevated privileges.
Unnecessary internet reachability
Description
The resource can be reached from the internet, either directly by having a public IP or due to insufficient network restrictions. This can be a security risk because it exposes the resource to potential attacks and unauthorized access attempts.
Example
A virtual machine listening on port 3389 (RDP) and is directly accessible to the internet may be targeted and exploited as an entry point to the network.
Unencrypted communication protocols
Description
Encrypted protocols should be used for traffic over the internet. Encryption ensures that only authorized parties can read your data if someone intercepts it as it travels over the network.
Example
Web applications should use require HTTPS using TLS 1.2 or higher than HTTP.
Poor integrity
Description
Software integrity refers to the trustworthiness of software and the confidence that it is genuine and will perform as expected without any malicious or unintended behavior.
Example
Linux virtual machines should use signed boot components. Unsigned boot components are exposed to tempered and backdoored software versions.
Data Loss and corruption
Description
Measures should be taken to reduce the risk of accidental data loss or corruption.
Example
Enabling deletion protection for resources reduces the risk of accidental deletion and loss of data.
Sanitation
Description
Refers to the process of deletion or removal of unnecessary resources and accounts to reduce attack surface and prevent unauthorized access.
Example
Blocked accounts with high privileged permissions should be deleted to reduce attack surface.
Appendix 2: Contexts
Issues, by definition, indicate a weakness in the environment, and therefore every issue may also add context to other issues found. Other than the issues contexts include:
Contains sensitive data
Description
The resource contains sensitive data, such as PII (personally identifiable information), network configuration information or credentials such as usernames, passwords, keys that if obtained by unauthorized individuals could be used to access other systems.
Example
A storage resource contains employee’s personal information such as social security number and credit card number.
Resource importance
Description
The resource is of high business criticality. This context may be based on end-user input, allowing them to adjust and promote assets and behavior of interest.
Example
A subscription owner of an Azure subscription, an individual or managed identity, has full administrative access and holds the highest level of authority over the resources and services within that subscription. If the Azure subscription owner account is compromised, it poses significant risks to the security and integrity of the Azure environment. The compromised resource can be used to gain unrestricted access to any resource within the subscription, leading to data breach, account takeover, resource abuse (crypto-mining), allow the attacker to achieve persistence and undermine compliance with regulatory requirements and industry standards.
Access to a resource
Description
The resource can authenticate and has permissions to another resource, either by its assigned identity and permissions, or by utilizing credentials found on it.
Example
A VM that can authenticate as a managed identity that has permission to the subscription.
Is running
Description
The resource is currently running, turned ON.
Example
Indicates that a resource, e.g., Kubernetes cluster, is in a running state.
Cross cloud
A resource maintained by a cloud service provider can be used to compromise a resources maintained by another cloud service provider.
Example
An shh-key found on an AWS EC2 instance that can be used to authenticate to an Azure VM
Highly likely to be under attack
Description
There is an indication on an ongoing attack on the resource.
Example
There are recent alerts for RDP BF activity on the VM.
Successfully compromised resource
Description
A resource that has been successfully compromised and is therefore untrusted.
Example
There are recent alerts for RDP BF activity on the VM resulting in a successful login.
Microsoft Tech Community – Latest Blogs –Read More
Consolidating CSV results files in Azure Load Testing
Azure Load Testing (ALT) provides a rich and consolidated dashboard to analyze your load test results. However, you can also download or export the test results, build your own dashboards and reporting, for example, using Microsoft Excel or Power BI. You can also use JMeter backend listeners to write the results to a data store of your choice and analyze the data.
When you use the download results option, the ALT service splits the results into one CSV file per engine. This ensures that the file size is not huge, and it is easy to open the files in tools like notepad, excel to analyze the data. In cases where your input data is split across test engines, you can pick the results file for a specific engine and analyze.
If you want to get one consolidated view of the test run results in a single file – to compute aggregate values of response time across all the requests, to calculate the number of errors of a specific type for a request etc., you will have to go through a few manual steps to extract the zip file, open each CSV and copy the data into a single file. In this blogpost, we will walk you through two ways in which you can leverage automation for this scenario.
Download the results and consolidate into a single CSV file. You can use this option if you wish to automate the results download step as well. We will demonstrate this using a Python script.
Extract the downloaded Zip file and consolidate into a single CSV file. This is suitable if you have already downloaded the results file and you do not want to use any ALT APIs/SDKs for this automation. We will demonstrate this using a PowerShell script.
Download the results and consolidate into a single CSV file
In this approach, you can provide the test run ID as the input and use the Azure Load Testing APIs/SDKs to download the results zip file and then extract it and consolidate the results.
For this blogpost, we used the ALT SDK for Python to create a Python script that does the following:
Download the results zip file using the test run ID.
Unzip the file to a local directory.
Open each CSV file and add the engine number as an additional column.
Copy the data from each CSV file into a single consolidated CSV file.
Save the consolidated file to the same directory.
To try this out for your test runs,
Download the script.
Update the config file to provide the inputs related to your subscription and your Azure Load Testing resource.
Run the script to perform the five steps described above.
The same can also be achieved by using the REST APIs or the SDKs for .NET, Java and JavaScript.
Extract the downloaded Zip file and consolidate into a single CSV file
If you have already downloaded the results zip file to your local directory, you can skip the step to download the results using ALT APIs/SDKs in your automation script and just perform steps 2 through 5. You can use this PowerShell script to achieve this in the following steps.
Download the script to the same directory where you have the results zip file. If you choose to run the script from another directory, update the script directory path.
Run the script to extract the zip file and create a consolidated CSV file in the same directory.
To summarize, we have seen two approaches to leverage automation to simplify the process of consolidating the results from an Azure Load Testing test run into a single CSV file.
If you haven’t tried Azure Load Testing yet, create an Azure Load Testing resource and get started with your first test run in a few minutes. Let us know your feedback through our feedback forum.
Happy load testing!
Additional resources:
Azure Load Testing resources: https://aka.ms/MALT-resources.
Previous blogposts on Azure Load Testing here.
Microsoft Tech Community – Latest Blogs –Read More
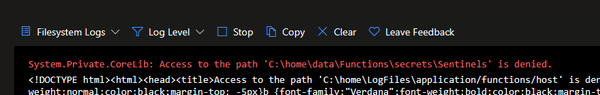
Key Vault policies affecting your Logic App Standard functioning
Sometimes we get cases that are not usual, so it’s always nice to document our findings, so that you may also investigate and solve your issues faster.
This article shows how Key Vault Policies may affect the functioning of a Logic App Standard, the troubleshooting steps and how to fix it.
Background
Logic App Standard works with many resources all together and as you know, it has a specific connection to the Storage Accounts and Fileshares, where it stores the main files and other supporting records (like in Tables and Queues).
If this connection is broken, the runtime will not be able to load as it cannot retrieve the needed files. So, when troubleshooting these types of errors, we usually check for the typical points of failure, like Private Endpoints and Vnet integrations.
Observed errors
While looking at a Logic App Standard (LA STD), we found a common error, that is the indicator of the connection severed to the Storage Account.
Our internal tools also showed that the Logic App was not able to connect to Storage Account (SA).
We knew that Vnet integration was enabled and that the Storage Account was behind Firewall (FW) and with Private Endpoints (PE).
As part of the troubleshooting, the first steps were to check the Storage Account Firewall and Private Endpoints:
Storage Account Private Endpoint associated to Logic App Subnet
Same region
All 4 endpoints created (File, Blob, Table, Queue)
All correctly configured
Still the Logic App runtime was not loading
Network tests showed that Private Endpoint name resolution was occurring without issues, so DNS was not at fault.
TCPPing tests were also successful, from an external VM to the Storage Account.
So, when in doubt, attempt to revert to vanilla state, disable FW and PE from Storage Account and disable Vnet from Logic App. After this, the Logic App was still not loading.
Again, hostname resolution and TCPPing was OK, for the Storage endpoints.
Runtime internal Logs showed the following:
Details
Microsoft.Azure.WebJobs.Script.WebHost.HttpException : Function host is not running.
System.IO.IOException : The user name or password is incorrect. : ‘C:homedataFunctionssecretsSentinels’
Log Stream showed the following:
This error is common and not very explicit. If we just cut off the Public Access, this message will also show. In fact, this image was obtained from one POC that I built, in which I had only cut off the Public Access.
As we wanted to recover the workflow files, to create a new Logic App, the user tried to browse the Logic App Fileshare. While doing this, our user was lacking the permissions to browse the Fileshare with the Microsoft Entra authentication type, so this was not valid.
Also, when trying to Browse using Access Key, this error was shown, blade failed to load with Key vault “unwrap key” error.
This was strange, as it’s not usual to see this error.
Over at the backend logs side, Storage Operations Logs show similar issue.
Microsoft.WindowsAzure.Storage.StorageException: Unexpected HTTP status code ‘Forbidden’.
—> System.Net.WebException: The remote server returned an error: (403) The key vault key is not found to unwrap the encryption key..
Findings
Deeper investigation showed that while the Encryption to the Storage Account was active and set to Customer Managed Keys (CMK), the Cryptographic operations were not allowed, thus not allowing Storage Account access using Access Key, as the keys were being stored in Key Vault for comparison.
From the documentation, we see that the Managed Identity is required to have minimum permissions, else it will fail to access the CMK.
Customer-managed keys for account encryption – Azure Storage | Microsoft Learn
“You can either create your own keys and store them in the key vault or managed HSM, or you can use the Azure Key Vault APIs to generate keys. The storage account and the key vault or managed HSM can be in different Microsoft Entra tenants, regions, and subscriptions.
…
The managed identity that is associated with the storage account must have these permissions at a minimum to access a customer-managed key in Azure Key Vault:
wrapkey
unwrapkey
get
“
Conclusions and mitigation
Due to the Encryption of the Storage Keys and the restrictions on the Access Policies, Logic App Standard was not able to correctly connect to the Storage Account, resulting in a broken runtime.
As the Policies were enabled in the Key Vault, Storage Account access was reactivated from the Logic App side, and all succeeding tests were successful, including when enabling Vnet integration.
Microsoft Tech Community – Latest Blogs –Read More
Visualizing narrow Kusto tables with Azure Managed Grafana
A common table design pattern in Kusto is the use of narrow tables.
In a schema design, narrow tables are characterized by having a few data values colums, so for each row in a table, different types of information being stored. A narrow table can still have multiple columns that serve other purpose. For instance, columns could be present for various dimensions, such as a device or a sensor.
Let’s consider an example of a narrow table with a fixed schema. The metric column includes values like temperature, pressure, or vibration. The respective measurements for these metrics are stored in the sensor_reading_real column:
measurement_ts
device_id
metric
unit
sensor_reading_real
2024-02-27T09:17:19Z
device-1
temperature
°C
15
2024-02-27T09:20:00Z
device-2
temperature
°C
15.01
2024-02-27T09:20:00Z
device-2
pressure
kPa
10
2024-02-27T09:30:00Z
device-2
temperature
°C
16.01
The design pattern is very flexible. For new metrics no schema design change has to be made.
How to achieve having multiple metrics in one visualization, with the additional flexibility to let users select what metrics to be visualized? The envisioned outcome is a Grafana dashboard of a certain design:
Grafana dashboard – envisioned outcome
For this blog-post we are using Azure Managed Grafana for the visualization. As a pre-requisite we assume that you have Azure Managed Grafana and a Kusto database running.
In Kusto we use the following table definition to store the data:
measurement_ts : datetime,
device_id : string,
metric : string,
unit : string,
sensor_reading_real : real
) with (docstring =’narrow table with data values with datatype real’, folder =’narrow’)
The function definition looks as follows:
narrow_measurement_real
| where measurement_ts between (_from .. _to) and metric in (_metric) and device_id in (_device_id)
| summarize sensor_reading=max(sensor_reading_real) by metric, device_id, bin(measurement_ts, _bin)
| evaluate pivot(metric, max(sensor_reading))
| order by measurement_ts
}
With this we are done on the database side and can start with the setup in Azure Managed Grafana. First we will set up a connection to our KQL database (for the detailed steps, please see also the documentation Visualize data from Azure Data Explorer in Grafana ). As a connection type we choose Azure Data Explorer Datasource. For the connection setup to the Kusto database in Azure Managed Grafana you need the cluser URI (for Fabric this is the URI provided as a Query URI under the database details). We are using the current user authentication method here, passing through the current user in Azure Managed Grafana to the Kusto database. You have to make sure that the users have at least viewer-permissons on the database. As of writing this blog article current user authentication method is in experimental phase, so it is not recommended yet using this in production deployments.
The connection will look similar to:
Now we can start with the dashboard creation. In Grafana go to the dashboards menu, create a new dashboard and add a visualization, and select the data source you’ve defined in the previous step. In the query window, switch from the builder to direct KQL, as the query builder currently does not support functions.
The KQL in the query window should look like this:
let _to=$__timeTo;
let _bin=$__timeInterval; //The $__interval is calculated using the time range and the width of the graph (the number of pixels).
let _device_id=dynamic([$v_device_id]);
let _metric=dynamic([$v_metric]);
wide_measurement_real(_from, _to, _bin, _device_id, _metric)
Next, you’ll need to define the two variables referenced in the query for the drop-down selection:
for the selection of the devices (include the time filter so users can only select devices for the current time-filtering),
and for the selection of the metrics.
Apply the current dashboard configuration and switch to the dashboard settings to define these two variables as query types. Define the name, the label, select your data source, and choose Kusto Query as the query type. You can either use the builder or direct KQL entry with the query definition that looks as follows for both variables:
Devices: v_device_id
| where measurement_ts between ($__timeFrom .. $__timeTo)
| distinct device_id
| order by device_id asc
Metrics: v_metric
| distinct metric
| order by metric asc
Make sure to change the refresh to On time range change for devices if you do the time selection in the query for the variable v_device_id. Enable multi-value selection for both variables, as we want to plot multiple metrics in the chart and multiple devices on the dashboards. This is also important, as the variables are defined with the dynamic datatype, so an array of senor ids and device ids is expected.
Almost done! Here are a few more edits:
Add v_device_id under repeat options to get the timeseries per device.
Define overrides for fields with regular expressions (this requires metrics to follow certain naming conventions). This way, you can configure the metrics displayed with different units based on the name. For more information on overriding the units of the metrics, check out the Grafana documentation
Add the legend as a table with several calculations and include calculations like minima, maxima, mean values.
With this we are done, and have created a simple and very flexible dashboard! If new metrics are inserted ot the table, no change is required, you will be able to visualize them as they will appear in the dropdown list for the selection:
Grafana dashboard with the metric selection
Conclusion
In this blog article, you have learned how to use narrow tables in Kusto, how to create a function to get a wide view on a narrow table definition, and how to visualize multiple metrics in one visualization with the flexibility for users to select the metrics they want to see. You’ve also learned how to define variables in Grafana for a more interactive and customized visualization experience.
Microsoft Tech Community – Latest Blogs –Read More
Veritas offers MISA partner solutions in Azure Marketplace
The Microsoft Intelligent Security Association (MISA) is an ecosystem of independent software vendors and managed security service providers that have integrated their solutions to better defend against a world of increasing threats. Learn more about offers from MISA partner Veritas in Azure Marketplace:
Veritas Alta Data Protection (Americas): Available in the Americas, Veritas Alta provides autonomous cloud data protection powered by Microsoft Azure for workloads of any size in any environment. The solution delivers elastic infrastructure for data protection, fully managed retention services, and cost-effective automated backups for leading SaaS apps, including Microsoft 365, Salesforce, and others.
Veritas Alta Data Protection (EMEA): Available in Europe and the Middle East, Veritas Alta provides autonomous cloud data protection powered by Microsoft Azure for workloads of any size in any environment. The solution delivers elastic infrastructure for data protection, fully managed retention services, and cost-effective automated backups for leading SaaS apps, including Microsoft 365, Salesforce, and others.
Veritas Alta Application High Availability (Americas): Available in the Americas, Veritas Alta Enterprise Resiliency optimizes workload performance while delivering real-time monitoring and disaster recovery orchestration. Built on Microsoft Azure, Enterprise Resiliency uses software-defined storage to provide business continuity for your business-critical applications, enables data migration between regions, and delivers a holistic solution for high availability workloads.
Microsoft Tech Community – Latest Blogs –Read More
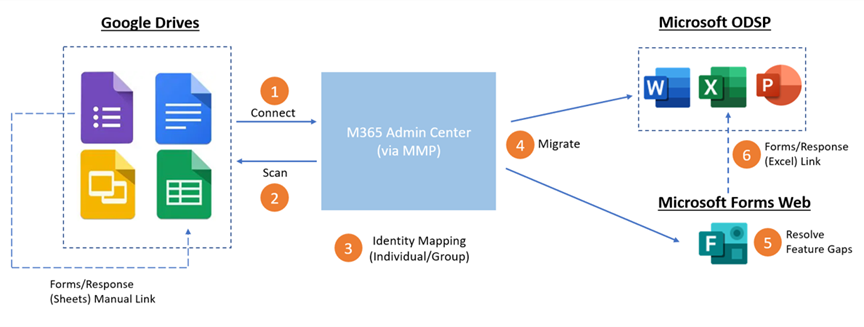
Migrate Your Google Forms to Microsoft Forms in Microsoft 365 Admin Center
Now you can migrate your Google forms to Microsoft Forms for the full Microsoft 365 experience. This feature is currently available in the Microsoft 365 admin center and is designed as an admin and tenant-level feature, enabling admins to bulk migrate their Google forms to Microsoft forms through the Microsoft 365 admin center. Individual users can then access the migrated forms on the Forms website after the migration. In the initial phrase, we’re -leveraging the existing document migration process in the Microsoft 365 admin center to support forms migration under personal Google drives. Now, let’s delve into the end-to-end process.
Google form migration E2E flow
Prepare for the migration
Users should review their Google forms and responses prior to the migration and then verify all information is intact once the process is complete.
Review Google forms before migration
Forms migration in the Microsoft 365 admin center
The admin can initiate the migration from the Microsoft 365 admin center. To get started, the admin should firstly add, select and copy the targeted drives for migration, then designate the destination storage within OneDrive. Note: it’s mandatory to specify forms destinations, either specifying individual forms destination via UX (below) or uploading CSV file for bulk. Next, they can start migrating the forms under the selected drives. Once the migration is complete, the admin can access the summarized report or download the full report to see more details in Excel.
Specify individual forms destination via UXSpecify forms destination in bulk via CSV file
Retrieve migrated forms on the Forms website
After the migration, users can go to the Forms website and find all the migrated forms in one collection (Migrated Forms from Google). The migrated forms are almost the same as before the migration, and only require minor edits before re-use. Users can view the migrated responses in Excel.
Check migrated forms on the Forms website
Microsoft Tech Community – Latest Blogs –Read More
Access Releases 9 Issue Fixes in Version 2312 (Released January 4th, 2024)
Our newest round of Access bug fixes was released on January 4th, 2024. In this blog post, we highlight some of the fixed issues that our Access engineers released in the current monthly channel.
If you see a bug that impacts you, and if you are on the current monthly channel Version 2312, you should have these fixes. Make sure you are on Access Build # 16.0.17126.20126 or greater.
Bug Name
Issue Fixed
No list of font sizes when Aptos font is selected
Aptos is the default font for controls in a new database using the recently updated ‘Office Theme,’ but the font size drop down was not displaying a list of font sizes (although you could manually type in a font size).
When a query was open in datasheet or design view, the context menu command to open in SQL View in the navigation pane would not switch the open query to SQL View
This command on the context menu was recently added to allow opening a query directly into SQL view. However, to be consistent with other commands, it now switches the mode of a query that is already open to SQL view.
#Error when using DateDiff with one Date/Time column and one Date/Time Extended column
The DateDiff function was working correctly if both arguments were of type Date/Time, or both arguments were of type Date/Time Extended but would fail to evaluate with one argument of each type.
The updated linked table manager no longer shows the name of the DSN used for a linked table
The old, linked table manager displayed this information. The new linked table manager now also displays it.
Access may terminate unexpectedly when running a macro after editing it
In some cases, after adding/removing/moving macro actions in the macro designer, then attempting to run the macro, Access would terminate unexpectedly. This no longer occurs.
F1 does not display the correct help page when used on some properties/methods of the Field2 object in the VBA IDE
F1 now directs to the appropriate help page for the following properties/methods:
CreateProperty, Expression, IsComplex, Name, Required, SourceTable, Type, ValidationRule, ValidationText, and Value.
Some valid values for the DBEngine.SetOption method have no defined constant
The following constants were added:
dbPagesLockedToTableLock, dbPasswordEncryptionProvider, dbPasswordEncryptionAlgorithm, dbPasswordEncryptionKeyLength
Subform control does not support LabelName property
The LabelName property was shown in the property sheet for every other control that supported child labels and is now present for subform controls as well.
Auto expand in combo boxes doesn’t work for list items >100 index
In some cases, autocomplete did not work for items in a dropdown list when there were more than 100 items in the list. This issue has been resolved.
Please continue to let us know if this is helpful and share any feedback you have.
Microsoft Tech Community – Latest Blogs –Read More
Access Releases 9 Issue Fixes in Version 2312 (Released January 4th, 2024)
Our newest round of Access bug fixes was released on January 4th, 2024. In this blog post, we highlight some of the fixed issues that our Access engineers released in the current monthly channel.
If you see a bug that impacts you, and if you are on the current monthly channel Version 2312, you should have these fixes. Make sure you are on Access Build # 16.0.17126.20126 or greater.
Bug Name
Issue Fixed
No list of font sizes when Aptos font is selected
Aptos is the default font for controls in a new database using the recently updated ‘Office Theme,’ but the font size drop down was not displaying a list of font sizes (although you could manually type in a font size).
When a query was open in datasheet or design view, the context menu command to open in SQL View in the navigation pane would not switch the open query to SQL View
This command on the context menu was recently added to allow opening a query directly into SQL view. However, to be consistent with other commands, it now switches the mode of a query that is already open to SQL view.
#Error when using DateDiff with one Date/Time column and one Date/Time Extended column
The DateDiff function was working correctly if both arguments were of type Date/Time, or both arguments were of type Date/Time Extended but would fail to evaluate with one argument of each type.
The updated linked table manager no longer shows the name of the DSN used for a linked table
The old, linked table manager displayed this information. The new linked table manager now also displays it.
Access may terminate unexpectedly when running a macro after editing it
In some cases, after adding/removing/moving macro actions in the macro designer, then attempting to run the macro, Access would terminate unexpectedly. This no longer occurs.
F1 does not display the correct help page when used on some properties/methods of the Field2 object in the VBA IDE
F1 now directs to the appropriate help page for the following properties/methods:
CreateProperty, Expression, IsComplex, Name, Required, SourceTable, Type, ValidationRule, ValidationText, and Value.
Some valid values for the DBEngine.SetOption method have no defined constant
The following constants were added:
dbPagesLockedToTableLock, dbPasswordEncryptionProvider, dbPasswordEncryptionAlgorithm, dbPasswordEncryptionKeyLength
Subform control does not support LabelName property
The LabelName property was shown in the property sheet for every other control that supported child labels and is now present for subform controls as well.
Auto expand in combo boxes doesn’t work for list items >100 index
In some cases, autocomplete did not work for items in a dropdown list when there were more than 100 items in the list. This issue has been resolved.
Please continue to let us know if this is helpful and share any feedback you have.
Microsoft Tech Community – Latest Blogs –Read More
Access Releases 9 Issue Fixes in Version 2312 (Released January 4th, 2024)
Our newest round of Access bug fixes was released on January 4th, 2024. In this blog post, we highlight some of the fixed issues that our Access engineers released in the current monthly channel.
If you see a bug that impacts you, and if you are on the current monthly channel Version 2312, you should have these fixes. Make sure you are on Access Build # 16.0.17126.20126 or greater.
Bug Name
Issue Fixed
No list of font sizes when Aptos font is selected
Aptos is the default font for controls in a new database using the recently updated ‘Office Theme,’ but the font size drop down was not displaying a list of font sizes (although you could manually type in a font size).
When a query was open in datasheet or design view, the context menu command to open in SQL View in the navigation pane would not switch the open query to SQL View
This command on the context menu was recently added to allow opening a query directly into SQL view. However, to be consistent with other commands, it now switches the mode of a query that is already open to SQL view.
#Error when using DateDiff with one Date/Time column and one Date/Time Extended column
The DateDiff function was working correctly if both arguments were of type Date/Time, or both arguments were of type Date/Time Extended but would fail to evaluate with one argument of each type.
The updated linked table manager no longer shows the name of the DSN used for a linked table
The old, linked table manager displayed this information. The new linked table manager now also displays it.
Access may terminate unexpectedly when running a macro after editing it
In some cases, after adding/removing/moving macro actions in the macro designer, then attempting to run the macro, Access would terminate unexpectedly. This no longer occurs.
F1 does not display the correct help page when used on some properties/methods of the Field2 object in the VBA IDE
F1 now directs to the appropriate help page for the following properties/methods:
CreateProperty, Expression, IsComplex, Name, Required, SourceTable, Type, ValidationRule, ValidationText, and Value.
Some valid values for the DBEngine.SetOption method have no defined constant
The following constants were added:
dbPagesLockedToTableLock, dbPasswordEncryptionProvider, dbPasswordEncryptionAlgorithm, dbPasswordEncryptionKeyLength
Subform control does not support LabelName property
The LabelName property was shown in the property sheet for every other control that supported child labels and is now present for subform controls as well.
Auto expand in combo boxes doesn’t work for list items >100 index
In some cases, autocomplete did not work for items in a dropdown list when there were more than 100 items in the list. This issue has been resolved.
Please continue to let us know if this is helpful and share any feedback you have.
Microsoft Tech Community – Latest Blogs –Read More
Access Releases 9 Issue Fixes in Version 2312 (Released January 4th, 2024)
Our newest round of Access bug fixes was released on January 4th, 2024. In this blog post, we highlight some of the fixed issues that our Access engineers released in the current monthly channel.
If you see a bug that impacts you, and if you are on the current monthly channel Version 2312, you should have these fixes. Make sure you are on Access Build # 16.0.17126.20126 or greater.
Bug Name
Issue Fixed
No list of font sizes when Aptos font is selected
Aptos is the default font for controls in a new database using the recently updated ‘Office Theme,’ but the font size drop down was not displaying a list of font sizes (although you could manually type in a font size).
When a query was open in datasheet or design view, the context menu command to open in SQL View in the navigation pane would not switch the open query to SQL View
This command on the context menu was recently added to allow opening a query directly into SQL view. However, to be consistent with other commands, it now switches the mode of a query that is already open to SQL view.
#Error when using DateDiff with one Date/Time column and one Date/Time Extended column
The DateDiff function was working correctly if both arguments were of type Date/Time, or both arguments were of type Date/Time Extended but would fail to evaluate with one argument of each type.
The updated linked table manager no longer shows the name of the DSN used for a linked table
The old, linked table manager displayed this information. The new linked table manager now also displays it.
Access may terminate unexpectedly when running a macro after editing it
In some cases, after adding/removing/moving macro actions in the macro designer, then attempting to run the macro, Access would terminate unexpectedly. This no longer occurs.
F1 does not display the correct help page when used on some properties/methods of the Field2 object in the VBA IDE
F1 now directs to the appropriate help page for the following properties/methods:
CreateProperty, Expression, IsComplex, Name, Required, SourceTable, Type, ValidationRule, ValidationText, and Value.
Some valid values for the DBEngine.SetOption method have no defined constant
The following constants were added:
dbPagesLockedToTableLock, dbPasswordEncryptionProvider, dbPasswordEncryptionAlgorithm, dbPasswordEncryptionKeyLength
Subform control does not support LabelName property
The LabelName property was shown in the property sheet for every other control that supported child labels and is now present for subform controls as well.
Auto expand in combo boxes doesn’t work for list items >100 index
In some cases, autocomplete did not work for items in a dropdown list when there were more than 100 items in the list. This issue has been resolved.
Please continue to let us know if this is helpful and share any feedback you have.
Microsoft Tech Community – Latest Blogs –Read More
Access Releases 9 Issue Fixes in Version 2312 (Released January 4th, 2024)
Our newest round of Access bug fixes was released on January 4th, 2024. In this blog post, we highlight some of the fixed issues that our Access engineers released in the current monthly channel.
If you see a bug that impacts you, and if you are on the current monthly channel Version 2312, you should have these fixes. Make sure you are on Access Build # 16.0.17126.20126 or greater.
Bug Name
Issue Fixed
No list of font sizes when Aptos font is selected
Aptos is the default font for controls in a new database using the recently updated ‘Office Theme,’ but the font size drop down was not displaying a list of font sizes (although you could manually type in a font size).
When a query was open in datasheet or design view, the context menu command to open in SQL View in the navigation pane would not switch the open query to SQL View
This command on the context menu was recently added to allow opening a query directly into SQL view. However, to be consistent with other commands, it now switches the mode of a query that is already open to SQL view.
#Error when using DateDiff with one Date/Time column and one Date/Time Extended column
The DateDiff function was working correctly if both arguments were of type Date/Time, or both arguments were of type Date/Time Extended but would fail to evaluate with one argument of each type.
The updated linked table manager no longer shows the name of the DSN used for a linked table
The old, linked table manager displayed this information. The new linked table manager now also displays it.
Access may terminate unexpectedly when running a macro after editing it
In some cases, after adding/removing/moving macro actions in the macro designer, then attempting to run the macro, Access would terminate unexpectedly. This no longer occurs.
F1 does not display the correct help page when used on some properties/methods of the Field2 object in the VBA IDE
F1 now directs to the appropriate help page for the following properties/methods:
CreateProperty, Expression, IsComplex, Name, Required, SourceTable, Type, ValidationRule, ValidationText, and Value.
Some valid values for the DBEngine.SetOption method have no defined constant
The following constants were added:
dbPagesLockedToTableLock, dbPasswordEncryptionProvider, dbPasswordEncryptionAlgorithm, dbPasswordEncryptionKeyLength
Subform control does not support LabelName property
The LabelName property was shown in the property sheet for every other control that supported child labels and is now present for subform controls as well.
Auto expand in combo boxes doesn’t work for list items >100 index
In some cases, autocomplete did not work for items in a dropdown list when there were more than 100 items in the list. This issue has been resolved.
Please continue to let us know if this is helpful and share any feedback you have.
Microsoft Tech Community – Latest Blogs –Read More
Access Releases 9 Issue Fixes in Version 2312 (Released January 4th, 2024)
Our newest round of Access bug fixes was released on January 4th, 2024. In this blog post, we highlight some of the fixed issues that our Access engineers released in the current monthly channel.
If you see a bug that impacts you, and if you are on the current monthly channel Version 2312, you should have these fixes. Make sure you are on Access Build # 16.0.17126.20126 or greater.
Bug Name
Issue Fixed
No list of font sizes when Aptos font is selected
Aptos is the default font for controls in a new database using the recently updated ‘Office Theme,’ but the font size drop down was not displaying a list of font sizes (although you could manually type in a font size).
When a query was open in datasheet or design view, the context menu command to open in SQL View in the navigation pane would not switch the open query to SQL View
This command on the context menu was recently added to allow opening a query directly into SQL view. However, to be consistent with other commands, it now switches the mode of a query that is already open to SQL view.
#Error when using DateDiff with one Date/Time column and one Date/Time Extended column
The DateDiff function was working correctly if both arguments were of type Date/Time, or both arguments were of type Date/Time Extended but would fail to evaluate with one argument of each type.
The updated linked table manager no longer shows the name of the DSN used for a linked table
The old, linked table manager displayed this information. The new linked table manager now also displays it.
Access may terminate unexpectedly when running a macro after editing it
In some cases, after adding/removing/moving macro actions in the macro designer, then attempting to run the macro, Access would terminate unexpectedly. This no longer occurs.
F1 does not display the correct help page when used on some properties/methods of the Field2 object in the VBA IDE
F1 now directs to the appropriate help page for the following properties/methods:
CreateProperty, Expression, IsComplex, Name, Required, SourceTable, Type, ValidationRule, ValidationText, and Value.
Some valid values for the DBEngine.SetOption method have no defined constant
The following constants were added:
dbPagesLockedToTableLock, dbPasswordEncryptionProvider, dbPasswordEncryptionAlgorithm, dbPasswordEncryptionKeyLength
Subform control does not support LabelName property
The LabelName property was shown in the property sheet for every other control that supported child labels and is now present for subform controls as well.
Auto expand in combo boxes doesn’t work for list items >100 index
In some cases, autocomplete did not work for items in a dropdown list when there were more than 100 items in the list. This issue has been resolved.
Please continue to let us know if this is helpful and share any feedback you have.
Microsoft Tech Community – Latest Blogs –Read More
Access Releases 9 Issue Fixes in Version 2312 (Released January 4th, 2024)
Our newest round of Access bug fixes was released on January 4th, 2024. In this blog post, we highlight some of the fixed issues that our Access engineers released in the current monthly channel.
If you see a bug that impacts you, and if you are on the current monthly channel Version 2312, you should have these fixes. Make sure you are on Access Build # 16.0.17126.20126 or greater.
Bug Name
Issue Fixed
No list of font sizes when Aptos font is selected
Aptos is the default font for controls in a new database using the recently updated ‘Office Theme,’ but the font size drop down was not displaying a list of font sizes (although you could manually type in a font size).
When a query was open in datasheet or design view, the context menu command to open in SQL View in the navigation pane would not switch the open query to SQL View
This command on the context menu was recently added to allow opening a query directly into SQL view. However, to be consistent with other commands, it now switches the mode of a query that is already open to SQL view.
#Error when using DateDiff with one Date/Time column and one Date/Time Extended column
The DateDiff function was working correctly if both arguments were of type Date/Time, or both arguments were of type Date/Time Extended but would fail to evaluate with one argument of each type.
The updated linked table manager no longer shows the name of the DSN used for a linked table
The old, linked table manager displayed this information. The new linked table manager now also displays it.
Access may terminate unexpectedly when running a macro after editing it
In some cases, after adding/removing/moving macro actions in the macro designer, then attempting to run the macro, Access would terminate unexpectedly. This no longer occurs.
F1 does not display the correct help page when used on some properties/methods of the Field2 object in the VBA IDE
F1 now directs to the appropriate help page for the following properties/methods:
CreateProperty, Expression, IsComplex, Name, Required, SourceTable, Type, ValidationRule, ValidationText, and Value.
Some valid values for the DBEngine.SetOption method have no defined constant
The following constants were added:
dbPagesLockedToTableLock, dbPasswordEncryptionProvider, dbPasswordEncryptionAlgorithm, dbPasswordEncryptionKeyLength
Subform control does not support LabelName property
The LabelName property was shown in the property sheet for every other control that supported child labels and is now present for subform controls as well.
Auto expand in combo boxes doesn’t work for list items >100 index
In some cases, autocomplete did not work for items in a dropdown list when there were more than 100 items in the list. This issue has been resolved.
Please continue to let us know if this is helpful and share any feedback you have.
Microsoft Tech Community – Latest Blogs –Read More
Access Releases 9 Issue Fixes in Version 2312 (Released January 4th, 2024)
Our newest round of Access bug fixes was released on January 4th, 2024. In this blog post, we highlight some of the fixed issues that our Access engineers released in the current monthly channel.
If you see a bug that impacts you, and if you are on the current monthly channel Version 2312, you should have these fixes. Make sure you are on Access Build # 16.0.17126.20126 or greater.
Bug Name
Issue Fixed
No list of font sizes when Aptos font is selected
Aptos is the default font for controls in a new database using the recently updated ‘Office Theme,’ but the font size drop down was not displaying a list of font sizes (although you could manually type in a font size).
When a query was open in datasheet or design view, the context menu command to open in SQL View in the navigation pane would not switch the open query to SQL View
This command on the context menu was recently added to allow opening a query directly into SQL view. However, to be consistent with other commands, it now switches the mode of a query that is already open to SQL view.
#Error when using DateDiff with one Date/Time column and one Date/Time Extended column
The DateDiff function was working correctly if both arguments were of type Date/Time, or both arguments were of type Date/Time Extended but would fail to evaluate with one argument of each type.
The updated linked table manager no longer shows the name of the DSN used for a linked table
The old, linked table manager displayed this information. The new linked table manager now also displays it.
Access may terminate unexpectedly when running a macro after editing it
In some cases, after adding/removing/moving macro actions in the macro designer, then attempting to run the macro, Access would terminate unexpectedly. This no longer occurs.
F1 does not display the correct help page when used on some properties/methods of the Field2 object in the VBA IDE
F1 now directs to the appropriate help page for the following properties/methods:
CreateProperty, Expression, IsComplex, Name, Required, SourceTable, Type, ValidationRule, ValidationText, and Value.
Some valid values for the DBEngine.SetOption method have no defined constant
The following constants were added:
dbPagesLockedToTableLock, dbPasswordEncryptionProvider, dbPasswordEncryptionAlgorithm, dbPasswordEncryptionKeyLength
Subform control does not support LabelName property
The LabelName property was shown in the property sheet for every other control that supported child labels and is now present for subform controls as well.
Auto expand in combo boxes doesn’t work for list items >100 index
In some cases, autocomplete did not work for items in a dropdown list when there were more than 100 items in the list. This issue has been resolved.
Please continue to let us know if this is helpful and share any feedback you have.
Microsoft Tech Community – Latest Blogs –Read More
Access Releases 9 Issue Fixes in Version 2312 (Released January 4th, 2024)
Our newest round of Access bug fixes was released on January 4th, 2024. In this blog post, we highlight some of the fixed issues that our Access engineers released in the current monthly channel.
If you see a bug that impacts you, and if you are on the current monthly channel Version 2312, you should have these fixes. Make sure you are on Access Build # 16.0.17126.20126 or greater.
Bug Name
Issue Fixed
No list of font sizes when Aptos font is selected
Aptos is the default font for controls in a new database using the recently updated ‘Office Theme,’ but the font size drop down was not displaying a list of font sizes (although you could manually type in a font size).
When a query was open in datasheet or design view, the context menu command to open in SQL View in the navigation pane would not switch the open query to SQL View
This command on the context menu was recently added to allow opening a query directly into SQL view. However, to be consistent with other commands, it now switches the mode of a query that is already open to SQL view.
#Error when using DateDiff with one Date/Time column and one Date/Time Extended column
The DateDiff function was working correctly if both arguments were of type Date/Time, or both arguments were of type Date/Time Extended but would fail to evaluate with one argument of each type.
The updated linked table manager no longer shows the name of the DSN used for a linked table
The old, linked table manager displayed this information. The new linked table manager now also displays it.
Access may terminate unexpectedly when running a macro after editing it
In some cases, after adding/removing/moving macro actions in the macro designer, then attempting to run the macro, Access would terminate unexpectedly. This no longer occurs.
F1 does not display the correct help page when used on some properties/methods of the Field2 object in the VBA IDE
F1 now directs to the appropriate help page for the following properties/methods:
CreateProperty, Expression, IsComplex, Name, Required, SourceTable, Type, ValidationRule, ValidationText, and Value.
Some valid values for the DBEngine.SetOption method have no defined constant
The following constants were added:
dbPagesLockedToTableLock, dbPasswordEncryptionProvider, dbPasswordEncryptionAlgorithm, dbPasswordEncryptionKeyLength
Subform control does not support LabelName property
The LabelName property was shown in the property sheet for every other control that supported child labels and is now present for subform controls as well.
Auto expand in combo boxes doesn’t work for list items >100 index
In some cases, autocomplete did not work for items in a dropdown list when there were more than 100 items in the list. This issue has been resolved.
Please continue to let us know if this is helpful and share any feedback you have.
Microsoft Tech Community – Latest Blogs –Read More
Access Releases 9 Issue Fixes in Version 2312 (Released January 4th, 2024)
Our newest round of Access bug fixes was released on January 4th, 2024. In this blog post, we highlight some of the fixed issues that our Access engineers released in the current monthly channel.
If you see a bug that impacts you, and if you are on the current monthly channel Version 2312, you should have these fixes. Make sure you are on Access Build # 16.0.17126.20126 or greater.
Bug Name
Issue Fixed
No list of font sizes when Aptos font is selected
Aptos is the default font for controls in a new database using the recently updated ‘Office Theme,’ but the font size drop down was not displaying a list of font sizes (although you could manually type in a font size).
When a query was open in datasheet or design view, the context menu command to open in SQL View in the navigation pane would not switch the open query to SQL View
This command on the context menu was recently added to allow opening a query directly into SQL view. However, to be consistent with other commands, it now switches the mode of a query that is already open to SQL view.
#Error when using DateDiff with one Date/Time column and one Date/Time Extended column
The DateDiff function was working correctly if both arguments were of type Date/Time, or both arguments were of type Date/Time Extended but would fail to evaluate with one argument of each type.
The updated linked table manager no longer shows the name of the DSN used for a linked table
The old, linked table manager displayed this information. The new linked table manager now also displays it.
Access may terminate unexpectedly when running a macro after editing it
In some cases, after adding/removing/moving macro actions in the macro designer, then attempting to run the macro, Access would terminate unexpectedly. This no longer occurs.
F1 does not display the correct help page when used on some properties/methods of the Field2 object in the VBA IDE
F1 now directs to the appropriate help page for the following properties/methods:
CreateProperty, Expression, IsComplex, Name, Required, SourceTable, Type, ValidationRule, ValidationText, and Value.
Some valid values for the DBEngine.SetOption method have no defined constant
The following constants were added:
dbPagesLockedToTableLock, dbPasswordEncryptionProvider, dbPasswordEncryptionAlgorithm, dbPasswordEncryptionKeyLength
Subform control does not support LabelName property
The LabelName property was shown in the property sheet for every other control that supported child labels and is now present for subform controls as well.
Auto expand in combo boxes doesn’t work for list items >100 index
In some cases, autocomplete did not work for items in a dropdown list when there were more than 100 items in the list. This issue has been resolved.
Please continue to let us know if this is helpful and share any feedback you have.
Microsoft Tech Community – Latest Blogs –Read More