Tag Archives: microsoft
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Prepare for upcoming TLS 1.3 support for Azure Storage
Azure Storage has started to enable TLS 1.3 support on public HTTPS endpoints across its platform globally to align with security best practices. Azure Storage currently supports TLS 1.0, 1.1 (scheduled for deprecation by November 2024), and TLS 1.2 on public HTTPS endpoints. This blog provides additional guidance on how to prepare for upcoming support for TLS 1.3 for Azure Storage.
TLS 1.3 introduces substantial enhancements compared to its predecessors. TLS 1.3 improvements focus on both performance and security, featuring faster handshakes and a streamlined set of more secure cipher suites, namely TLS_AES_256_GCM_SHA384 and TLS_AES_128_GCM_SHA256. Notably, TLS 1.3 prioritizes Perfect Forward Secrecy (PFS) by eliminating key exchange algorithms that don’t support it.
Clients that utilize the latest available TLS version will automatically pick TLS 1.3 when it is available. If you need more time to upgrade to TLS 1.3, you can choose to continue to use TLS 1.2 by controlling the TLS negotiations through client configuration (see recommendations section below). Azure storage will continue to support TLS 1.2 in addition to TLS 1.3.
We have outlined below some of the known issues with TLS 1.3 enablement, potential impact and mitigation.
Known Issues, impact and mitigation
Certain Java clients can experience high latencies, timeouts, and connections that hang for extended periods due to a bug in the Java Http stack. The issue manifests primarily for applications with high request concurrency. The bugs are [JDK-8293562] and [JDK-8208526] .
The major JDK versions with the bug fixes are:
JDK 11 (> 11.0.17)
JDK 17 (> 17.0.6)
JDK 21
The following categories of clients could be affected while using TLS 1.3:
Clients that run on JDK versions other than JDK versions mentioned above.
Client tools like WASB and Azure Storage SDK for Java < v12 running the JDK version without the fix. (Note: ABFS, Azure Storage Java SDK > V12 are not impacted).
Recommendations for mitigation:
Option 1: (Recommended) Upgrade your application to the latest supported JDK versions mentioned above or latest Azure Storage SDK for Java. You can refer to the following link to get the latest recommended SDK versions.
Option 2: (Short-term workaround) We understand it might not always be possible to upgrade to the latest SDK version. While you move your application to the latest SDK version, this can be mitigated by setting the maximum TLS version for client versions to TLS 1.2. There are two ways to accomplish this:
Setting system properties when invoking the Java application:
java -Djdk.tls.client.protocols=TLSv1.2 -Dhttps.protocols=TLSv1.2 -jar …
Setting system properties in code:
System.setProperty(“Djdk.tls.client.protocols”, “TLSv1.2”);
System.setProperty(“Dhttps.protocols”, “TLSv1.2”);
When your applications are ready to work with TLS 1.3, remember to reset these settings.
Help and Support
If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and you need technical help, create a support request:
For Issue type, select Technical.
For Subscription, select your subscription.
For Service, select My services.
For Service type, select Blob Storage.
For Resource, select the Azure resource you are creating a support request for.
For Summary, type a description of your issue.
For Problem type, select Connectivity.
For Problem subtype, select Issues using TLS.
Microsoft Tech Community – Latest Blogs –Read More
Known issue: Voice calling on Apple devices running iOS/iPadOS 17.2
We’ve recently received a few cases where some users are experiencing issues with voice calls after updating their iOS/iPadOS devices to 17.2.
Apple’s aware of the issue and are actively working on a resolution. We’ll keep this post updated as we learn more, and a fix becomes available.
Microsoft Tech Community – Latest Blogs –Read More
Known issue: Voice calling on Apple devices running iOS/iPadOS 17.2
We’ve recently received a few cases where some users are experiencing issues with voice calls after updating their iOS/iPadOS devices to 17.2.
Apple’s aware of the issue and are actively working on a resolution. We’ll keep this post updated as we learn more, and a fix becomes available.
Microsoft Tech Community – Latest Blogs –Read More
Best practices for designing Word, Excel, and PowerPoint add-ins
Designing an add-in in Word, Excel, or PowerPoint can be a challenging task, but with the right approach you can inspire users and help them solve problems with a positive experience. In this blog post, we’ll explore some considerations and strategies to design an effective add-in. Whether you’re a seasoned developer or starting out, these tips will help you create an add-in that is intuitive, user-friendly, and valuable to your users. Let’s dive in and discover the best practices for designing an add-in that stands out from the crowd!
Name your add-in effectively
The average attention span for a user to a product or design is 8 seconds. Choosing the right name for your add-in is crucial to its success. Two key tips to keep in mind when selecting a name are:
1) Reflect the add-in’s core functionality
2) Be direct and memorable
If you already have a well-known branding name, don’t hesitate to include your brand first. Also, the name should give users a clear idea of what the add-in does and how it can benefit them. For example, if your add-in is a writing assistant, consider a name like ‘GrammarGuard’ or ‘ LanguageLift ‘ that clearly communicates its purpose. Additionally, the name should be easy to remember and stand out from other add-ins in the same category. Avoid using overly complex or generic names that get lost in the crowd. Don’t forget to check Microsoft Trademark and Brand guidelines.
Provide a detailed description
Your description provides a second chance to make a good impression. A well-crafted description succinctly conveys the key benefits and features of your add-in in a way that is easy to understand and memorable. Ideally, keep your description under two lines (less than 60 characters). It allows users to quickly understand what your add-in does and how it helps them in under ten seconds.
To create an effective two-line description, it’s important to include your add-in’s value proposition and the specific tasks it can help users accomplish. If your add-in is an artificial intelligent writing assistant, your description might read ‘Improve grammar, spelling, punctuation, and style in written content with our service.’
Design your UI to integrate with Office
Follow the Office design principles to create a positive add-in experience.
Design explicitly for Office. Your add-in UI design must integrate seamlessly with Office to provide efficient, natural interaction for your users. The functionality, as well as the look and feel, of an add-in must harmoniously complement the Office experience. Consider using Fluent UI for the web as your design language and tool set. The Fluent UI for the web has two versions.
For React UIs: use Fluent UI React, a React front-end framework designed to build experiences that fit seamlessly into a broad range of Microsoft products. It provides robust, up-to-date, accessible React-based components which are highly customizable using CSS-in-JS. To get started, see Fluent UI React Components. (More resources, see Fluent UI React in Office Add-ins).
For non-React UIs: Use Fabric Core, an open-source collection of CSS classes and Sass mixings that give you access to colors, animations, fonts, icons, and grids. To get started, see Fabric Core in Office Add-ins.
Favor content over chrome. Allow customers’ page, slide, or spreadsheet to remain the focus of the experience.
Make it enjoyable and keep users in control.
Design for all platforms and input methods.
Onboard inside the app
A first-run experience (FRE) is presented when a user opens an add-in for the first time. It provides them with insight into the functions, features, and benefits of the add-in. This experience helps shape the user’s impression of an add-in and strongly influences their likelihood to come back to and continue using your add-in.
Please remember, don’t make users register or sign up first. This can be a blocker for users to try the real functionality. A smooth and easy register experience gives users the opportunity to complete an action that positively affects their perception of the add-in. For more information, see First-run experience patterns for Office Add-ins – Office Add-ins | Microsoft Learn.
Choose the freemium business model
Lastly, consider monetizing your add-in after gaining sufficient traffic. The freemium business model is a great way to attract customers, build a user base, and generate revenue. Freemium is a pricing strategy where you offer a basic version of the product or service for free, while charging for advanced features or premium versions.
By offering a free version of a product, companies can attract a larger audience and build a user base that can later be converted into paying customers. Once users are familiar with the product, they are more likely to upgrade to the premium version to access additional features. Additionally, offering a free version of a product can reduce the cost of acquiring new customers, as users can try the product before they purchase. Finally, the freemium model makes it easier to increase brand awareness and generate buzz around a product.
Get started
Make your first add-in in minutes:
Develop Office Add-ins
Sample add-ins:
Add AI-generated content to your Word document
Get data from an Excel spreadsheet for a mail merge
Create PowerPoint presentations with unique designs
Microsoft Tech Community – Latest Blogs –Read More
Dive into the World of AI with the Semantic Kernel Cookbook
If you’re interested in AI and looking for a hands-on way to dive deeper, the Semantic Kernel Cookbook on GitHub is a resource you won’t want to miss.
Since the release of Semantic Kernel in March of 2023, we’ve managed to see a community of AI engineers emerge from around the globe. And Kinfey Lo’s “Semantic Kernel Cookbook” is certain to enable even more “AI chefs” to find their path to combining native code with semantic code. How? By learning how to cook with AI in SK by discovering the joys of Plugins, Planners, and Personas.
We’re all learning together — in the open. And we know that the best way to build a community is through sharing recipes so we can all learn together. Faster. Open source has a wonderful capability to enable greater learning by just being a member of one of the open-source communities. Showing up counts! Since you’ve chosen to show up, definitely try out some of Kinfey’s cooking. And if you’re in the mood for it, make your own recipe for AI with SK and share it back.
With respect and love,
—The Semantic Kernel Team @ Microsoft
What is the Semantic Kernel Cookbook?
The Semantic Kernel Cookbook is a repository hosted by Microsoft on GitHub. It’s designed to help developers integrate cutting-edge Large Language Models (LLMs) like OpenAI, Azure OpenAI, and Hugging Face with conventional programming languages like C#, Python, and Java.
Session
Intro
.NET
Python
Getting started with LLM
Begin to know LLM, including OpenAI, Azure OpenAI Service and LLM on Hugging face
Using Azure OpenAI Service With SDK
Learn how to use Azure OpenAI Service with SDK
Click
Click
Foundations of Semantic Kernel
What is Semantic Kernel? What are its advantages and disadvantages? Semantic Kernel related concepts, etc.
Click
Click
The skills of LLM – Plugins
We know that communicating with LLM requires the use of prompt engineering?
For enterprise applications, there are many business-oriented prompt engineering.
In Semantic Kernel we call it Plugins. In this session we will introduce how to use Semantic
Kernel Plugins and how to define your own Plugins
Click
Click
Planner – Let LLM have planning work
Human beings need to complete a job step by step, and the same goes for LLMs.
Semantic Kernel has a very powerful task planning capability – Planner, in this session we will explain in detail how to define and use Planner to make your application more intelligent
Click
Click
Embedding Skills
Building RAG applications is the most commonly used LLM solution at this stage. It is very convenient to build RAG applications through Semantic Kernel.
This session will tell you how to use Semantic Kernel Embeddings
Click
Click
HandsOnLab
Through three hands on labs projects, let everyone truly understand the application
of Semantic Kernel
Click
Click
Why Use the Semantic Kernel Cookbook?
Using the Semantic Kernel Cookbook, you can define plugins that can be chained together in just a few lines of code. What makes Semantic Kernel special, however, is its ability to automatically orchestrate plugins with AI. With Semantic Kernel planners, you can ask an LLM to generate a plan that achieves a user’s unique goal. Afterwards, Semantic Kernel will execute the plan for the user.
Getting Started with Semantic Kernel Cookbook
Getting started with the Semantic Kernel Cookbook is simple. The Semantic Kernel SDK is available in C#, Python . To get started, choose your preferred language and follow the instructions provided in the repository.
Conclusion
The Semantic Kernel Cookbook is a unique opportunity to dive into the world of AI and programming languages. Whether you’re a beginner or an experienced developer, this resource offers valuable learning experiences and the chance to connect with a global community of tech enthusiasts. So why wait?
Visit the following resources and start your AI journey:
Semantic Kernel Cookbook
Semantic Kernel is at the center of the agent stack
Why use an SDK like Semantic Kernel?
Get started using the Semantic Kernel SDK
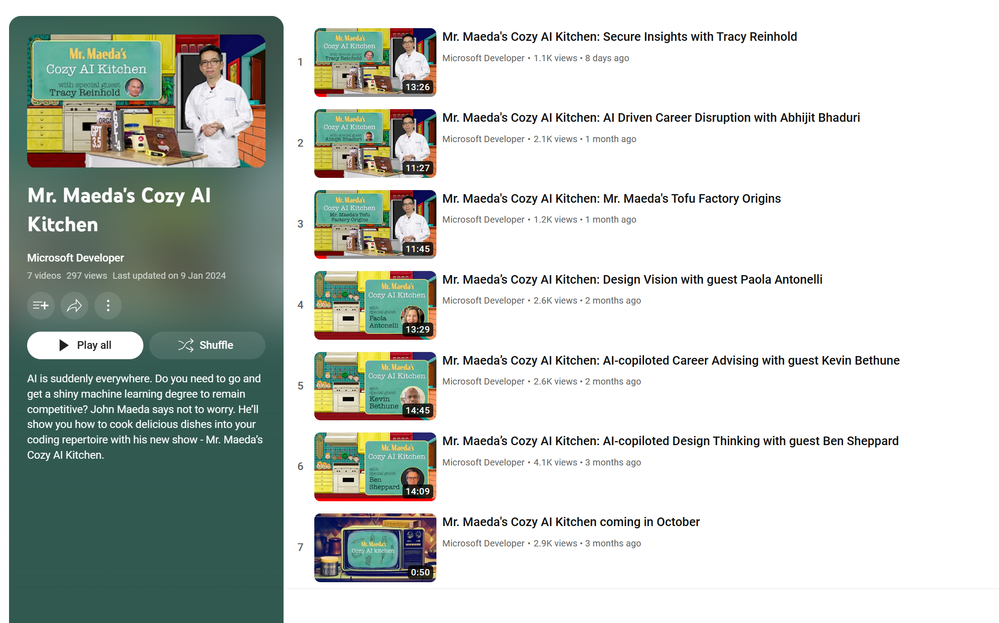
AI is suddenly everywhere. Do you need to go and get a shiny machine learning degree to remain competitive? John Maeda says not to worry. He’ll show you how to cook delicious dishes into your coding repertoire with his new show – Mr. Maeda’s Cozy AI Kitchen.
Mr. Maeda’s Cozy AI Kitchen (youtube.com)
Microsoft Tech Community – Latest Blogs –Read More
Best practices for designing Word, Excel, and PowerPoint add-ins
Designing an add-in in Word, Excel, or PowerPoint can be a challenging task, but with the right approach you can inspire users and help them solve problems with a positive experience. In this blog post, we’ll explore some considerations and strategies to design an effective add-in. Whether you’re a seasoned developer or starting out, these tips will help you create an add-in that is intuitive, user-friendly, and valuable to your users. Let’s dive in and discover the best practices for designing an add-in that stands out from the crowd!
Name your add-in effectively
The average attention span for a user to a product or design is 8 seconds. Choosing the right name for your add-in is crucial to its success. Two key tips to keep in mind when selecting a name are:
1) Reflect the add-in’s core functionality
2) Be direct and memorable
If you already have a well-known branding name, don’t hesitate to include your brand first. Also, the name should give users a clear idea of what the add-in does and how it can benefit them. For example, if your add-in is a writing assistant, consider a name like ‘GrammarGuard’ or ‘ LanguageLift ‘ that clearly communicates its purpose. Additionally, the name should be easy to remember and stand out from other add-ins in the same category. Avoid using overly complex or generic names that get lost in the crowd. Don’t forget to check Microsoft Trademark and Brand guidelines.
Provide a detailed description
Your description provides a second chance to make a good impression. A well-crafted description succinctly conveys the key benefits and features of your add-in in a way that is easy to understand and memorable. Ideally, keep your description under two lines (less than 60 characters). It allows users to quickly understand what your add-in does and how it helps them in under ten seconds.
To create an effective two-line description, it’s important to include your add-in’s value proposition and the specific tasks it can help users accomplish. If your add-in is an artificial intelligent writing assistant, your description might read ‘Improve grammar, spelling, punctuation, and style in written content with our service.’
Design your UI to integrate with Office
Follow the Office design principles to create a positive add-in experience.
Design explicitly for Office. Your add-in UI design must integrate seamlessly with Office to provide efficient, natural interaction for your users. The functionality, as well as the look and feel, of an add-in must harmoniously complement the Office experience. Consider using Fluent UI for the web as your design language and tool set. The Fluent UI for the web has two versions.
For React UIs: use Fluent UI React, a React front-end framework designed to build experiences that fit seamlessly into a broad range of Microsoft products. It provides robust, up-to-date, accessible React-based components which are highly customizable using CSS-in-JS. To get started, see Fluent UI React Components. (More resources, see Fluent UI React in Office Add-ins).
For non-React UIs: Use Fabric Core, an open-source collection of CSS classes and Sass mixings that give you access to colors, animations, fonts, icons, and grids. To get started, see Fabric Core in Office Add-ins.
Favor content over chrome. Allow customers’ page, slide, or spreadsheet to remain the focus of the experience.
Make it enjoyable and keep users in control.
Design for all platforms and input methods.
Onboard inside the app
A first-run experience (FRE) is presented when a user opens an add-in for the first time. It provides them with insight into the functions, features, and benefits of the add-in. This experience helps shape the user’s impression of an add-in and strongly influences their likelihood to come back to and continue using your add-in.
Please remember, don’t make users register or sign up first. This can be a blocker for users to try the real functionality. A smooth and easy register experience gives users the opportunity to complete an action that positively affects their perception of the add-in. For more information, see First-run experience patterns for Office Add-ins – Office Add-ins | Microsoft Learn.
Choose the freemium business model
Lastly, consider monetizing your add-in after gaining sufficient traffic. The freemium business model is a great way to attract customers, build a user base, and generate revenue. Freemium is a pricing strategy where you offer a basic version of the product or service for free, while charging for advanced features or premium versions.
By offering a free version of a product, companies can attract a larger audience and build a user base that can later be converted into paying customers. Once users are familiar with the product, they are more likely to upgrade to the premium version to access additional features. Additionally, offering a free version of a product can reduce the cost of acquiring new customers, as users can try the product before they purchase. Finally, the freemium model makes it easier to increase brand awareness and generate buzz around a product.
Get started
Make your first add-in in minutes:
Develop Office Add-ins
Sample add-ins:
Add AI-generated content to your Word document
Get data from an Excel spreadsheet for a mail merge
Create PowerPoint presentations with unique designs
Microsoft Tech Community – Latest Blogs –Read More
Embedding a Microsoft 365 Chat (Copilot) Window on a SharePoint Site
We are looking to embed Microsoft 365 Chat on a SharePoint site as a web part or have it appear as a modal/dialog window when this site is launched or a button is clicked. I have seen instructions to do this for custom Copilot chatbot experiences created with Copilot Studio. Has anyone done this with Microsoft 365 Chat?
We are looking to embed Microsoft 365 Chat on a SharePoint site as a web part or have it appear as a modal/dialog window when this site is launched or a button is clicked. I have seen instructions to do this for custom Copilot chatbot experiences created with Copilot Studio. Has anyone done this with Microsoft 365 Chat? Read More