Tag Archives: microsoft
Custom WIM Image – “Windows cannot find the Microsoft Software License Terms”
Hello, I made a custom WIM image to install Windows 10 and put it in a Windows 10 ISO image in the sources folder. The WIM file is completely valid (I can see it in 7-zip) but the installator of the ISO image gives an error: “Windows cannot find the Microsoft Software License Terms. Make sure the installation sources are valid and restart the installation.”.
I have searched solutions on the internet and found out that my VM might be the problem. I’m using VirtualBox and people on internet says that removing any floppy disk attachment to the VM makes it works again, but I have nothing other than a virtual 20 Go disk and my ISO file as a virtual CD/DVD disk.
Any solutions to this ? Thanks in advance.
Hello, I made a custom WIM image to install Windows 10 and put it in a Windows 10 ISO image in the sources folder. The WIM file is completely valid (I can see it in 7-zip) but the installator of the ISO image gives an error: “Windows cannot find the Microsoft Software License Terms. Make sure the installation sources are valid and restart the installation.”.I have searched solutions on the internet and found out that my VM might be the problem. I’m using VirtualBox and people on internet says that removing any floppy disk attachment to the VM makes it works again, but I have nothing other than a virtual 20 Go disk and my ISO file as a virtual CD/DVD disk.Any solutions to this ? Thanks in advance. Read More
Portfolio & Budget management
My company plans to carry out several projects from 2024 until 2030. Each project lasts about 2-4 years. Is it possible to represent all these projects on the same platform? Like a Gantt chart, each project is a bar on the chart?
Also, is there a way to include a per-project budget for management purposes? The budget will be allocated over time. For example: Project A lasts 3 years from January 1, 2024 to January 1, 2027, with an estimated budget of 1 million USD. Of which, 70% will be allocated in the first 6 months, the remaining 30% will be divided equally every month until the end of the project.
When the duration of the project changes, for example 5 years instead of 3 years, this allocated cost part will also automatically update accordingly.
Thank you so much
My company plans to carry out several projects from 2024 until 2030. Each project lasts about 2-4 years. Is it possible to represent all these projects on the same platform? Like a Gantt chart, each project is a bar on the chart?Also, is there a way to include a per-project budget for management purposes? The budget will be allocated over time. For example: Project A lasts 3 years from January 1, 2024 to January 1, 2027, with an estimated budget of 1 million USD. Of which, 70% will be allocated in the first 6 months, the remaining 30% will be divided equally every month until the end of the project.When the duration of the project changes, for example 5 years instead of 3 years, this allocated cost part will also automatically update accordingly.Thank you so much Read More
How to set desktop background from spotlight to picture option using powershell script
How to set desktop background from spotlight to picture option by setting registry key using powershell script
How to set desktop background from spotlight to picture option by setting registry key using powershell script Read More
To Do app can’t open right click menu
Hi,
After my laptop upgrade to Windows 11 , the To Do app can’t right click to move the task.
It doesn’t show on the menu.
My colleague have same problem with me.
Do you have any solution about this problem?
Thank you.
Regards,
Hao.
Hi, After my laptop upgrade to Windows 11 , the To Do app can’t right click to move the task.It doesn’t show on the menu.My colleague have same problem with me.Do you have any solution about this problem?Thank you.Is there have any setting or update should I need to do? Regards,Hao. Read More
Hello I am unable to renewal my Microsoft Certificate
Yesterday was the last day for me to renew my microsoft certificate and i was presuming that i have multiple attempts to clear the renewal test but unfortunately after two attempts it has given a message that i have to wait for 24 hours to give more attempt and i couldn’t make it…..I request Microsoft to allow me one day time so i can renew my certificate.
Yesterday was the last day for me to renew my microsoft certificate and i was presuming that i have multiple attempts to clear the renewal test but unfortunately after two attempts it has given a message that i have to wait for 24 hours to give more attempt and i couldn’t make it…..I request Microsoft to allow me one day time so i can renew my certificate. Read More
Graph formating
Hello,
Please see the attached screen shot, my question is easy. I am working on a 100% stacked column graph and the highest % is shown is the smaller block, why and how can I change that please?
Thank you for your help
Hello,Please see the attached screen shot, my question is easy. I am working on a 100% stacked column graph and the highest % is shown is the smaller block, why and how can I change that please? Thank you for your help Read More
asking for help to solve my problem with optimization
At first, an optimization option appeared in “Review -> Workbook Performance”. After optimizing, it removed all the empty rows below. I also can’t insert rows using “Home -> Insert Sheet Rows”.
Fingers crossed that you can lend me a hand. Thank you beforehand !
At first, an optimization option appeared in “Review -> Workbook Performance”. After optimizing, it removed all the empty rows below. I also can’t insert rows using “Home -> Insert Sheet Rows”. Fingers crossed that you can lend me a hand. Thank you beforehand ! Read More
Copy Tab in worksheet to new worksheet
I have copied a tab from one worksheet to another and when I update the Tab from the first worksheet it doesn’t automatically update in the second worksheet in which I’ve copied that tab to. What am I doing wrong? We are making sure that the tabs are updated through the Excel Desktop app and not through the website link
I have copied a tab from one worksheet to another and when I update the Tab from the first worksheet it doesn’t automatically update in the second worksheet in which I’ve copied that tab to. What am I doing wrong? We are making sure that the tabs are updated through the Excel Desktop app and not through the website link Read More
LEARN PYTHON PROGRAMMING WITH VS CODE!
LEARN PYTHON PROGRAMMING USING VS CODE MICROSOFT LEARN STUDENT AMBASSADORS ONLINE EVENT!:graduation_cap::laptop_computer::globe_showing_americas:
My name is MAH E UROOJ and I’m Muslim Pakistani. I’m newly selected Microsoft Learn Student Ambassador milestone – Alpha. I cordially invite you all to attend a live MS Teams session scheduled this coming Friday. Your all presence will make this event a success. You will learn Fundamental Python concepts with Practical hands-on practice on Microsoft VS Code IDE. You can also get a chance to win LinkedIn Premium vouchers if event gets approved. Your all participation is needed in this regard. I hope to see you on the session day. The event joining link is given in this email.
Learn, Read, Write & Grow!
:open_book::globe_showing_americas::smiling_face_with_smiling_eyes:
Thank You!
_________
Tap on the link or paste it in a browser to join.
https://teams.microsoft.com/l/meetup-join/19%3ameeting_ODYyNzhiOTktMWZkMi00MzQ2LWI4M2YtZDMwNDMyNmQxNjg0%40thread.v2/0?context=%7b%22Tid%22%3a%2284c31ca0-ac3b-4eae-ad11-519d80233e6f%22%2c%22Oid%22%3a%22c8df4290-b528-46d5-b127-03e4618d60d3%22%7d
Join an exclusive
Live Python Fundamental Programming Session on VS Code.
:spiral_calendar:️ Day: April 26th, 2024.
:eight_o_clock: Time: 06:00 p.m. – 06:45 p.m.
:round_pushpin: Microsoft Teams Virtual Event.
Microsoft Teams Need help?
Meeting ID: 216 758 209 212
Passcode: cTkzCR
You’re invited to Learn Python Programming! :laptop_computer::graduation_cap::globe_with_meridians:
LEARN PYTHON PROGRAMMING USING VS CODE MICROSOFT LEARN STUDENT AMBASSADORS ONLINE EVENT!:graduation_cap::laptop_computer::globe_showing_americas: My name is MAH E UROOJ and I’m Muslim Pakistani. I’m newly selected Microsoft Learn Student Ambassador milestone – Alpha. I cordially invite you all to attend a live MS Teams session scheduled this coming Friday. Your all presence will make this event a success. You will learn Fundamental Python concepts with Practical hands-on practice on Microsoft VS Code IDE. You can also get a chance to win LinkedIn Premium vouchers if event gets approved. Your all participation is needed in this regard. I hope to see you on the session day. The event joining link is given in this email. Learn, Read, Write & Grow! :open_book::globe_showing_americas::smiling_face_with_smiling_eyes: Thank You!_________Tap on the link or paste it in a browser to join.https://teams.microsoft.com/l/meetup-join/19%3ameeting_ODYyNzhiOTktMWZkMi00MzQ2LWI4M2YtZDMwNDMyNmQxNjg0%40thread.v2/0?context=%7b%22Tid%22%3a%2284c31ca0-ac3b-4eae-ad11-519d80233e6f%22%2c%22Oid%22%3a%22c8df4290-b528-46d5-b127-03e4618d60d3%22%7dJoin an exclusive Live Python Fundamental Programming Session on VS Code. :spiral_calendar:️ Day: April 26th, 2024.:eight_o_clock: Time: 06:00 p.m. – 06:45 p.m. :round_pushpin: Microsoft Teams Virtual Event. Microsoft Teams Need help? Meeting ID: 216 758 209 212 Passcode: cTkzCRYou’re invited to Learn Python Programming! :laptop_computer::graduation_cap::globe_with_meridians: Read More
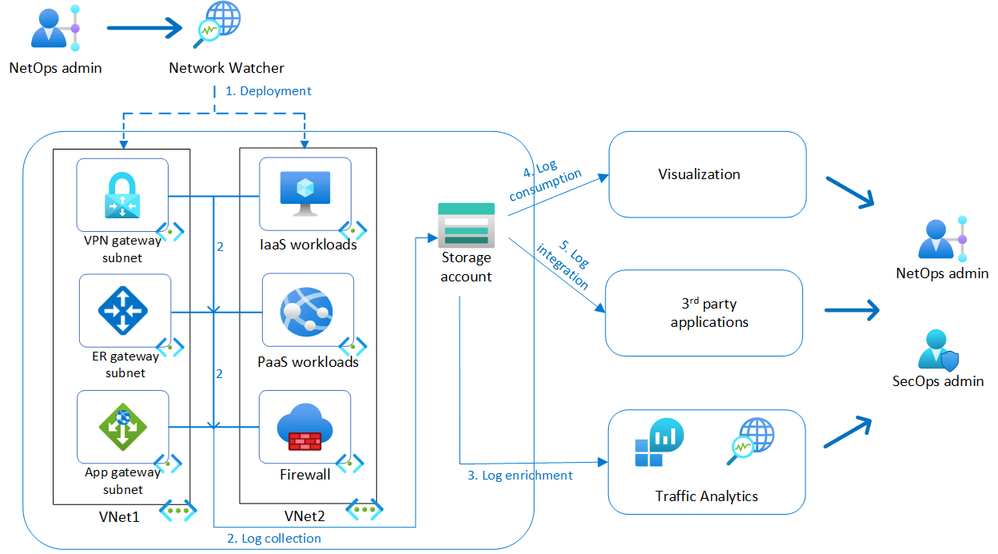
Network traffic observability with virtual network flow logs
Azure Network Watcher provides network monitoring and troubleshooting capabilities to increase observability and actionable insights with out-of-box health metrics & topology visualization, connectivity monitoring, traffic monitoring and diagnostics suite. For on-premises workloads, network administrators rely on NetFlow or IPFIX to address these use cases. Virtual network flow logs are a capability of Network Watcher service to address these scenarios for Azure and hybrid networks and we are excited to announce that virtual network flow logs are now transitioning from public preview to general availability.
Overview
Virtual network flow logs record layer-4 IP traffic flowing through a virtual network capturing the 5-tuple (source IP, destination IP, source port, destination port, protocol) and traffic volume information with no impact to application performance.
Deployment: virtual network flow logs can be enabled by NetOps admin for desired scope of virtual networks, subnets, or network interfaces.
Log collection: Inbound and outbound traffic is recorded at each network interface of the supported workloads and ingested to a storage account in JSON format for analysis and cost-effective retention.
Log enrichment: Traffic Analytics can be enabled as an add-on functionality to process the raw flow logs, aggregate them at longer intervals, and enrich them with environmental metadata for advanced insights into user and application activity and malicious communication patterns.
Log consumption: Virtual network flow logs can be accessed directly from storage accounts or integrated with out-of-box visualization such as Power BI.
Log integration: Virtual network flow logs can be integrated with 3rd party applications for network and security analysis.
Use cases of virtual network flow logs
Network security group flow logs and virtual network flow logs address the following use cases:
Network troubleshooting
Troubleshoot network connectivity between source and destination endpoints.
Identify overly restrictive or permissive access control rules.
Identify network security group (NSG) or Azure Virtual Network Manager rules blocking traffic.
Usage monitoring and optimization
Identify top talking hosts and top communicating applications across or within networks.
Monitor and visualize traffic levels and bandwidth consumption for cross-region traffic.
Identify unknown or undesired traffic.
Compliance
Record all network activity with configurable retention intervals to meet audit requirements.
Use flow data to verify network isolation and compliance with enterprise access rules.
Network forensics and security analysis
Analyze network flows from compromised IPs and network interfaces.
Identify ports and hosts communicating with public IPs or internet.
Integrate with 3rd party Intrusion Detection System (IDS) or Security Information and Event Management (SIEM) tool of choice for advanced detections and threat hunting.
Comparison to NSG flow logs
NSG flow logs also enable traffic recording but had limitations that virtual network flow logs overcome.
Capability
NSG flow logs
Virtual network flow logs
Scope of enablement
NSG
Virtual network, subnet, network interface
Identification of allowed/denied traffic in NSG rules
Yes
Yes
Identification of allowed/denied traffic by Virtual Network Manager security admin rules
No
Yes
Support of Virtual Network encryption
No
Yes
Traffic volume (bytes and packets) for stateless flows
No
Yes
Extensive resource coverage
No
Yes
Price
Billed per gigabyte of Network flow logs collected
Billed per gigabyte of Network flow logs collected
NSG flow logs can be migrated to virtual network flow logs for simplified transition to new capabilities.
Using virtual network flow logs
Virtual network flow logs can be enabled on one or more virtual networks using Azure Portal, PowerShell, AzCLI or Policy, with no requirement to attach NSGs to those virtual networks. The example below is a snippet of the flow log retrieved from storage account. Traffic flows are recorded as comma separated values with IP, port and volume information recorded under ‘flowTuples’. Traffic flows are unencrypted, as Azure virtual network encryption has not been enabled, indicated by ‘NX’.
With Traffic Analytics enabled, advanced insights on environment, traffic distribution, usage patterns, malicious flows across regions can be visualized with additional capabilities to slice and dice the data as per requirement in a Log analytics workspace with Kusto queries.
Scenarios addressed with virtual network flow logs
Demo environment
To demonstrate some of the scenarios described above, Azure environment comprising a hub and spoke topology is used, with the hub containing a Firewall, Bastion, DNS Private Resolver, and connectivity to on-premises via ExpressRoute gateway. Spoke1 has a sample application deployed on virtual machines with load balancers fronting each tier, and a private endpoint connected to an SQL Database for the DB tier. Spoke2 has sample workloads to test spoke-to-spoke traffic. Network Watcher virtual network flow logs and Traffic Analytics have been enabled on Hub and Spoke virtual networks.
Scenario 1: Troubleshooting virtual network manager security admin rules
Organizations typically have the requirement to log when network traffic is allowed or denied, to satisfy regulatory requirements and assist with troubleshooting in day-to-day operations. Network administrators can allow or deny traffic in a virtual network either using NSGs or Azure Virtual Network Manager security admin rules. Both mechanisms are logged using virtual network flow logs enabling visibility into traffic being allowed or denied.
In this case, there are both NSGs and Azure Virtual Network Manager security admin rules applied to the environment. An NSG named ‘yada-nsg’ has the second highest flow volume and an Azure Virtual Network Manager security admin rule called “nossh” is dropping SSH traffic to all virtual machines in the virtual network. Traffic Analytics dashboards shows the Access Control Lists (ACLs) hitting most traffic. Additional insights can be derived by navigating to Log Analytics workspace and modifying pre-built Kusto queries. To address scenarios such as troubleshooting failed SSH connections, an audit trail of SSH connection attempts from both internal and external IP addresses can be listed.
Scenario 2: Simplifying traffic visibility by enabling virtual network flow logs on hub virtual network
Virtual network flow logs allow optimization of log volume and simplification of management by enabling them at hub virtual network. All traffic flowing through the hub, including spoke-to-spoke traffic is recorded on the hub virtual network. In the topology of demo environment, traffic between the spokes is routed via hub firewall. The example query below aggregates throughput between internal IP addresses for specified ranges. An endpoint on Spoke2 (10.1.2.20) can be seen accessing another API endpoint on Spoke1(10.1.1.21) on port 8080, connecting to Web endpoint on Spoke1(10.1.1.4) via SSH and establishing DNS connectivity with Hub(10.1.0.8) on port 53. Traffic patterns between spoke virtual networks can be aggregated over time to distinguish hub-to-spoke vs spoke-to-spoke volume.
Scenario 3: Hybrid traffic visibility with ExpressRoute gateway
Typical enterprise deployments include a combination of Azure and on-premises workloads with significant traffic traversing ExpressRoute or VPN gateways. Estimating the overall traffic volume on ExpressRoute circuits and identifying the workloads that are consuming significant bandwidth on these circuits enables capacity planning, cross-charging internal teams, or re-architecting application communication to optimize costs. Further investigation to identify the top consumer of bandwidth (26%) in this ExpressRoute circuit (10.4.2.2) can be achieved to list top communicating endpoints, as well as timeline view of bandwidth patterns to eliminate anomalous patterns.
Conclusion
Virtual network flow logs enable centralized visibility of traffic patterns across virtual machines and scale sets, application gateways, load balancers, ExpressRoute gateways, VPN gateways and firewalls. Network and security administrators can leverage these flow logs to ensure organizational needs around network observability and compliance are met in a light-weight scalable manner. In addition, virtual network flow logs enable detection of security vulnerabilities and aid in threat hunting investigations with a complete trail of user and application activity.
Virtual network flow logs currently support the following 3rd party applications with seamless integration for additional scenarios:
Cisco XDR
Darktrace
IBM QRadar
Splunk
Virtual network flow logs will eventually be billed per gigabyte of logs generated. For more information, see Network Watcher pricing (Network flow logs collected).
Learn more
Network Watcher overview
Virtual network flow logs overview
Enable virtual network flow logs
Traffic Analytics overview
Traffic Analytics usage scenarios
Microsoft Tech Community – Latest Blogs –Read More
How fix QuickBooks Error 30159 after update Payroll?
Troubleshooting Solutions: QuickBooks Payroll Update Error 30159
Check Payroll Subscription: QuickBooks Error 30159 often occurs due to issues with the payroll subscription. Ensure your payroll subscription is active and up-to-date by logging into your Intuit account and verifying your subscription status.Update QuickBooks: Make sure you’re using the latest version of QuickBooks. Outdated software can trigger errors like 30159. Go to the “Help” menu and select “Update QuickBooks” to install any available updates.Run QuickBooks Payroll Update: QuickBooks often releases payroll updates to fix errors and enhance functionality. Run the latest payroll update by selecting “Employees” > “Get Payroll Updates” > “Download Entire Update.”Check Payroll Service Key: Verify that the payroll service key is correct in QuickBooks. Navigate to “Employees” > “My Payroll Service” > “Manage Service Keys.” If the key is incorrect, click “Edit” and enter the correct service key.Repair QuickBooks Installation: A corrupted QuickBooks installation can lead to error 30159. Use the QuickBooks Install Diagnostic Tool to repair the installation. Download and run the tool from the Intuit website to fix any installation-related issues.Update Windows and .NET Framework: Ensure that your Windows operating system and .NET Framework are updated. QuickBooks relies on these components, and outdated versions can cause compatibility issues. Check for updates in the Windows Update settings.Scan for Malware/Viruses: Malware or viruses on your system can interfere with QuickBooks processes, leading to error 30159. Run a thorough scan using reputable antivirus software to detect and remove any malicious programs.Check Firewall and Security Software: Your firewall or security software may be blocking QuickBooks from accessing necessary resources. Temporarily disable your firewall and security software, then try running QuickBooks again. If the error disappears, adjust your firewall settings to allow QuickBooks access.Contact QuickBooks Support: If none of the above solutions resolve the error, contact QuickBooks support for further assistance. They can provide advanced troubleshooting steps or address any underlying technical issues causing error 30159.
By following these troubleshooting steps, you should be able to resolve QuickBooks Error 30159 and resume your workflow without interruption.
Troubleshooting Solutions: QuickBooks Payroll Update Error 30159 Check Payroll Subscription: QuickBooks Error 30159 often occurs due to issues with the payroll subscription. Ensure your payroll subscription is active and up-to-date by logging into your Intuit account and verifying your subscription status.Update QuickBooks: Make sure you’re using the latest version of QuickBooks. Outdated software can trigger errors like 30159. Go to the “Help” menu and select “Update QuickBooks” to install any available updates.Run QuickBooks Payroll Update: QuickBooks often releases payroll updates to fix errors and enhance functionality. Run the latest payroll update by selecting “Employees” > “Get Payroll Updates” > “Download Entire Update.”Check Payroll Service Key: Verify that the payroll service key is correct in QuickBooks. Navigate to “Employees” > “My Payroll Service” > “Manage Service Keys.” If the key is incorrect, click “Edit” and enter the correct service key.Repair QuickBooks Installation: A corrupted QuickBooks installation can lead to error 30159. Use the QuickBooks Install Diagnostic Tool to repair the installation. Download and run the tool from the Intuit website to fix any installation-related issues.Update Windows and .NET Framework: Ensure that your Windows operating system and .NET Framework are updated. QuickBooks relies on these components, and outdated versions can cause compatibility issues. Check for updates in the Windows Update settings.Scan for Malware/Viruses: Malware or viruses on your system can interfere with QuickBooks processes, leading to error 30159. Run a thorough scan using reputable antivirus software to detect and remove any malicious programs.Check Firewall and Security Software: Your firewall or security software may be blocking QuickBooks from accessing necessary resources. Temporarily disable your firewall and security software, then try running QuickBooks again. If the error disappears, adjust your firewall settings to allow QuickBooks access.Contact QuickBooks Support: If none of the above solutions resolve the error, contact QuickBooks support for further assistance. They can provide advanced troubleshooting steps or address any underlying technical issues causing error 30159.By following these troubleshooting steps, you should be able to resolve QuickBooks Error 30159 and resume your workflow without interruption. Read More
Henvisningskode B I T G E T: qp29 (B I T G E T 1000 USDT registreringsbonus) | Ny kampagnekode
Henvisningskode B I T G E T: qp29 (B I T G E T 1000 USDT registreringsbonus) | Ny kampagnekode B I T G E T 2024
Leder du efter henvisningskode B I T G E T? Den sidste for 2024 er qp29. Med denne kode får du 30% rabat. Derudover kan nye BIT G E T-brugere, der tilmelder sig med kampagnekoden “qp29”, modtage en eksklusiv kampagnebelønning til en værdi af op til $1.000.
Hvad er henvisningskoden B I T G E T?
Koden “qp29” i BIT G E T-programmet fungerer som en henvisningskode. Ved at indtaste denne kode vil du modtage en permanent reduktion i handelsgebyrer samt 30% rabat på dine handler. Plus, hvis du deler din henvisningskode med dine venner, har du en chance for at vinde en generøs 50% bonus. Brug af denne kode giver en værdifuld mulighed for at reducere gebyrer og potentielt øge din indtjening ved at tiltrække andre til platformen.
Hvad er den bedste B I T G E T 2024 henvisningskode?
Den stærkt anbefalede B I T G E T-henvisningskode er qp29. Hvis du bruger denne kode, når du tilmelder dig, vil du modtage en generøs $100 bonus. Hvis du deler din kode med dine venner, har du mulighed for at tjene en kæmpe kommission på 50%. Dette giver dig i bund og grund muligheden for at modtage en maksimal tilmeldingsbonus på op til $1.000 som en velkomstbelønning. Dette er en fantastisk måde at udvide din handelsoplevelse med yderligere fordele, mens du opmuntrer andre til at deltage og tjene deres egne belønninger.
Sådan bruger du henvisningskoden B I T G E T
Henvisningskoden B I T G E T er tilgængelig for nye brugere, som endnu ikke er registreret på børsen. Hvis du allerede har en konto, vil du desværre ikke kunne bruge henvisningskoden.
B I T G E T tilbyder dog flere andre måder at deltage i kampagner og optjene belønninger på. Lad os se på disse alternativer.
For B I T G E T nybegyndere er her trin-for-trin instruktioner om, hvordan man ansøger om en henvisningskode:
For at komme i gang skal du besøge B I T G E T og klikke på den blå “Log ind”-knap.
Angiv nøjagtige brugeroplysninger, da de vil blive kontrolleret for overholdelse af KYC- og AML-procedurer.
Når du bliver bedt om din henvisningskode, skal du indtaste qp29.
Fuldfør registreringsprocessen og fuldfør alle nødvendige bekræftelser.
Når alle betingelser er opfyldt, kan du straks modtage velkomstbonussen.
Denne tilgang sikrer, at nye brugere nemt kan gennemføre registreringsprocessen selv uden en henvisningskode og modtage en velkomstbonus efter at have opfyldt de fastsatte krav.
Hvad er den anbefalede henvisningskode for B I T G E T?
Henvisningskode B I T G E T – qp29. For at få 30 % rabat på din B I T G E T-kommission skal du blot følge disse trin:
Registrer en ny konto hos B I T G E T.
Sørg for at bruge referencekoden B I T G E T qp29.
Hvor meget er henvisningsbonussen for B I T G E T?
Inviter dine venner til at deltage i B I T G E T og vind en del af henvisningspræmiepuljen sammen! Hver ven, du henviser, kan tjene $50, op til et maksimum på $1.000 pr. bruger. Brugere kan invitere venner til at registrere sig hos B I T G E T. Hvis de opfylder alle kravene, vil du og dine venner modtage handelsbonusser på $50 op til maksimumgrænsen.
Hvordan får jeg B I T G E T bonussen?
Optjen point dagligt og veksle dem til USDT. Gennemfør udfordringen inden for syv dage for at låse op for alle belønninger. Tilmeld dig for at modtage en velkomstpakke til en værdi af $1.000. Indbetal mindst $50 for at optjene 200 point. Lav din første handel til en værdi af mindst $50 og optjen 500 point.
Anvendes handelskommissionsrabatter automatisk?
Absolut. Når du registrerer dig med vores eksklusive henvisningskode B I T G E T qp29, vil 30% rabatten blive anvendt automatisk. Der kræves ingen yderligere handling. Du skal bare dykke ned i handel og nyde godt af en permanent 30 % rabat på alle kommissioner.
Henvisningskode B I T G E T: qp29 (B I T G E T 1000 USDT registreringsbonus) | Ny kampagnekode B I T G E T 2024Leder du efter henvisningskode B I T G E T? Den sidste for 2024 er qp29. Med denne kode får du 30% rabat. Derudover kan nye BIT G E T-brugere, der tilmelder sig med kampagnekoden “qp29”, modtage en eksklusiv kampagnebelønning til en værdi af op til $1.000.Hvad er henvisningskoden B I T G E T?Koden “qp29” i BIT G E T-programmet fungerer som en henvisningskode. Ved at indtaste denne kode vil du modtage en permanent reduktion i handelsgebyrer samt 30% rabat på dine handler. Plus, hvis du deler din henvisningskode med dine venner, har du en chance for at vinde en generøs 50% bonus. Brug af denne kode giver en værdifuld mulighed for at reducere gebyrer og potentielt øge din indtjening ved at tiltrække andre til platformen.Hvad er den bedste B I T G E T 2024 henvisningskode?Den stærkt anbefalede B I T G E T-henvisningskode er qp29. Hvis du bruger denne kode, når du tilmelder dig, vil du modtage en generøs $100 bonus. Hvis du deler din kode med dine venner, har du mulighed for at tjene en kæmpe kommission på 50%. Dette giver dig i bund og grund muligheden for at modtage en maksimal tilmeldingsbonus på op til $1.000 som en velkomstbelønning. Dette er en fantastisk måde at udvide din handelsoplevelse med yderligere fordele, mens du opmuntrer andre til at deltage og tjene deres egne belønninger.Sådan bruger du henvisningskoden B I T G E THenvisningskoden B I T G E T er tilgængelig for nye brugere, som endnu ikke er registreret på børsen. Hvis du allerede har en konto, vil du desværre ikke kunne bruge henvisningskoden.B I T G E T tilbyder dog flere andre måder at deltage i kampagner og optjene belønninger på. Lad os se på disse alternativer.For B I T G E T nybegyndere er her trin-for-trin instruktioner om, hvordan man ansøger om en henvisningskode:For at komme i gang skal du besøge B I T G E T og klikke på den blå “Log ind”-knap.Angiv nøjagtige brugeroplysninger, da de vil blive kontrolleret for overholdelse af KYC- og AML-procedurer.Når du bliver bedt om din henvisningskode, skal du indtaste qp29.Fuldfør registreringsprocessen og fuldfør alle nødvendige bekræftelser.Når alle betingelser er opfyldt, kan du straks modtage velkomstbonussen.Denne tilgang sikrer, at nye brugere nemt kan gennemføre registreringsprocessen selv uden en henvisningskode og modtage en velkomstbonus efter at have opfyldt de fastsatte krav.Hvad er den anbefalede henvisningskode for B I T G E T?Henvisningskode B I T G E T – qp29. For at få 30 % rabat på din B I T G E T-kommission skal du blot følge disse trin:Registrer en ny konto hos B I T G E T.Sørg for at bruge referencekoden B I T G E T qp29.Hvor meget er henvisningsbonussen for B I T G E T?Inviter dine venner til at deltage i B I T G E T og vind en del af henvisningspræmiepuljen sammen! Hver ven, du henviser, kan tjene $50, op til et maksimum på $1.000 pr. bruger. Brugere kan invitere venner til at registrere sig hos B I T G E T. Hvis de opfylder alle kravene, vil du og dine venner modtage handelsbonusser på $50 op til maksimumgrænsen.Hvordan får jeg B I T G E T bonussen?Optjen point dagligt og veksle dem til USDT. Gennemfør udfordringen inden for syv dage for at låse op for alle belønninger. Tilmeld dig for at modtage en velkomstpakke til en værdi af $1.000. Indbetal mindst $50 for at optjene 200 point. Lav din første handel til en værdi af mindst $50 og optjen 500 point.Anvendes handelskommissionsrabatter automatisk?Absolut. Når du registrerer dig med vores eksklusive henvisningskode B I T G E T qp29, vil 30% rabatten blive anvendt automatisk. Der kræves ingen yderligere handling. Du skal bare dykke ned i handel og nyde godt af en permanent 30 % rabat på alle kommissioner. Read More
Link up mailbox to exchange online from on-premise exchange
We got customer using the below.
1 x on-premise exchange server
Active M365 admin portal with users account synced online via AD sync from on-premise AD but without mailbox.
Mailbox are on-premise exchange.
Now we need to assign M365 mailbox to active user account on exchange online.
Because we tried assign in exchange online but it prompt on-premise exchange server detected and can’t proceed.
What is the best method to do so?
Thanks.
We got customer using the below.1 x on-premise exchange server Active M365 admin portal with users account synced online via AD sync from on-premise AD but without mailbox. Mailbox are on-premise exchange. Now we need to assign M365 mailbox to active user account on exchange online.Because we tried assign in exchange online but it prompt on-premise exchange server detected and can’t proceed. What is the best method to do so? Thanks. Read More
Shared calendars not syncing for others
I have created three calendars which have been shared by email with the organisation I work at. Some people do not receive updates when calendar events are amended (i.e., updates do not sync). Is this a regular glitch?
I have created three calendars which have been shared by email with the organisation I work at. Some people do not receive updates when calendar events are amended (i.e., updates do not sync). Is this a regular glitch? Read More
Removing Tags
Hi All,
I am just wondering whether it is at all possible to entirely remove a work item tag from Azure DevOps so that it doesn’t appear within the tag dropdown and cause confusion?
No resources online actually touch on this so I thought I’d ask here. The goal essentially being to remove certain work item tags from the project/organization.
Thanks
Hi All, I am just wondering whether it is at all possible to entirely remove a work item tag from Azure DevOps so that it doesn’t appear within the tag dropdown and cause confusion? No resources online actually touch on this so I thought I’d ask here. The goal essentially being to remove certain work item tags from the project/organization. Thanks Read More
Sending Urgent Teams Chats with PowerShell
A reader asked if it is possible to script sending chat messages. In this article, we explore how to compose and send Teams urgent messages to a set of recipients using Microsoft Graph PowerShell SDK cmdlets. The conversation with each recipient is a one-to-one chat that Teams either creates from scratch or reuses (if a suitable one-on-one chat exists).
https://office365itpros.com/2024/04/24/teams-urgent-message-ps/
A reader asked if it is possible to script sending chat messages. In this article, we explore how to compose and send Teams urgent messages to a set of recipients using Microsoft Graph PowerShell SDK cmdlets. The conversation with each recipient is a one-to-one chat that Teams either creates from scratch or reuses (if a suitable one-on-one chat exists).
https://office365itpros.com/2024/04/24/teams-urgent-message-ps/
Read More
What’s the best HEIC to JPG converter for my Windows 11?
I’m currently searching for an efficient solution to convert HEIC files to JPG format. Since I often need to handle numerous photos from my iPhone, which saves images in HEIC format by default, I find it necessary to convert these files into a more universally accepted format like JPG. The main challenge I’m facing is finding a best HEIC to JPG converter that maintains high-quality outputs without substantial loss in image detail, especially when dealing with a large volume of photos. Could anyone recommend a reliable HEIC to JPG converter that meets these criteria? Any suggestions on software or online tools that have worked well for you would be greatly appreciated.
I’m currently searching for an efficient solution to convert HEIC files to JPG format. Since I often need to handle numerous photos from my iPhone, which saves images in HEIC format by default, I find it necessary to convert these files into a more universally accepted format like JPG. The main challenge I’m facing is finding a best HEIC to JPG converter that maintains high-quality outputs without substantial loss in image detail, especially when dealing with a large volume of photos. Could anyone recommend a reliable HEIC to JPG converter that meets these criteria? Any suggestions on software or online tools that have worked well for you would be greatly appreciated. Read More
Windows Server 2022: Capi2 error on backup
Hello, i get some error message when i backup exchange with veritas backup exec or Veeam.
Log Name: Application
Source: Microsoft-Windows-CAPI2
Date: 24/04/2024 09:39:30
Event ID: 513
Task Category: None
Level: Error
Type of error:
Description:
Cryptographic Services failed while processing the OnIdentity() call in the System Writer Object.
Details:
AddWin32ServiceFiles: Unable to back up image of service McpManagementService since QueryServiceConfig API failed
System Error:
The resource loader failed to find MUI file.
Other:
Details:
AddLegacyDriverFiles: Unable to back up image of binary MsQuic.
System Error:
The specified resource name cannot be found in the image file.
Cryptographic Services failed while processing the OnIdentity() call in the System Writer Object.
Details:
AddWin32ServiceFiles: Unable to back up image of service dcsvc since QueryServiceConfig API failed
System Error:
The system cannot find the file specified.
Hello, i get some error message when i backup exchange with veritas backup exec or Veeam. Log Name: ApplicationSource: Microsoft-Windows-CAPI2Date: 24/04/2024 09:39:30Event ID: 513Task Category: NoneLevel: Error Type of error:Description:Cryptographic Services failed while processing the OnIdentity() call in the System Writer Object.Details:AddWin32ServiceFiles: Unable to back up image of service McpManagementService since QueryServiceConfig API failedSystem Error:The resource loader failed to find MUI file. Other:Details:AddLegacyDriverFiles: Unable to back up image of binary MsQuic.System Error:The specified resource name cannot be found in the image file. Cryptographic Services failed while processing the OnIdentity() call in the System Writer Object.Details:AddWin32ServiceFiles: Unable to back up image of service dcsvc since QueryServiceConfig API failedSystem Error:The system cannot find the file specified. Read More
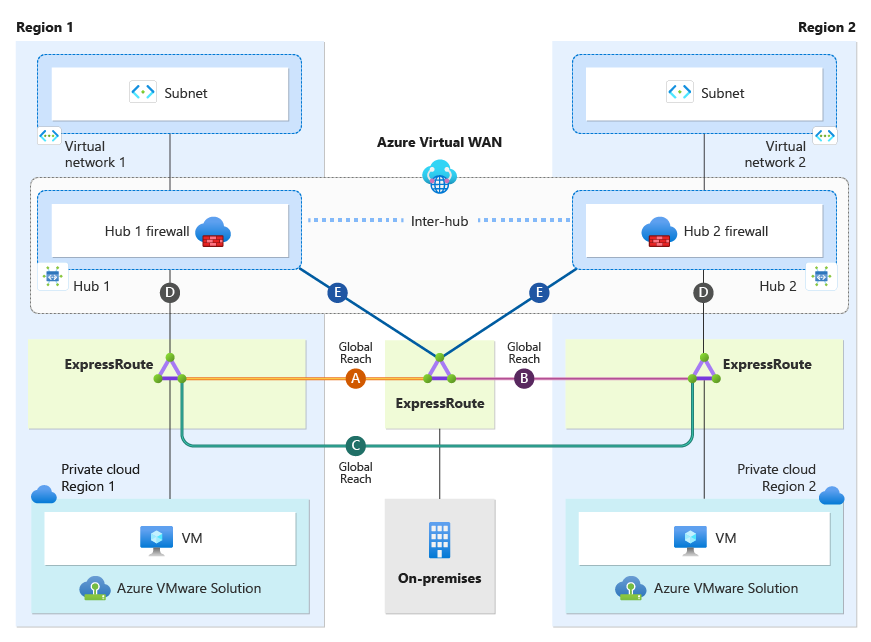
Dual-Region Azure VMware Solution design with Global Reach, using Secure Virtual WAN
This article describes the best practices for connectivity, traffic flows, and high availability of dual-region Azure VMware Solution when using Azure Secure Virtual WAN with Routing Intent and Global Reach. This article breaks down Virtual WAN with Routing Intent topology from the perspective of Azure VMware Solution private clouds, on-premises sites, and Azure native. The implementation and configuration of Secure Virtual WAN with Routing Intent are beyond the scope and are not discussed in this document.
The document assumes readers have a basic understanding of Virtual WAN and Secure Virtual WAN with Routing Intent.
Virtual WAN
Virtual WAN Routing Intent
How to configure Virtual WAN Hub routing intent and routing policies
Secure Virtual WAN with Routing Intent is only supported with Virtual WAN Standard SKU. Secure Virtual WAN with Routing Intent provides the capability to send all Internet traffic and Private network traffic to a security solution like Azure Firewall, a third-party Network Virtual Appliance (NVA), or SaaS solution. In the scenario, we have a network topology that spans two regions. There is one Virtual WAN with two Hubs, Hub1 and Hub2. Hub1 is in Region 1, and Hub2 is in Region 2. Each Hub has its own instance of Azure Firewall deployed(Hub 1 Firewall, Hub 2 Firewall), essentially making them each Secure Virtual WAN Hubs. Having Secure Virtual WAN hubs is a technical prerequisite to Routing Intent. Secure Virtual WAN Hub1 and Hub2 have Routing Intent enabled.
Note
When configuring Azure VMware Solution with Secure Virtual WAN Hubs, ensure optimal routing results on the hub by setting the Hub Routing Preference option to “AS Path.” – see Virtual hub routing preference
Each region has its own Azure VMware Solution Private Cloud and an Azure Virtual Network. Additionally, there is an on-premises site connecting to both regions. Furthermore, Global Reach connectivity exists within the environment. Global Reach establishes a direct logical link via the Microsoft backbone, connecting Azure VMware Solution to on-premises or regional Azure VMware Solution Private Clouds. As shown in the diagram below, Global Reach connections do not transit Hub Firewall 1 and Hub Firewall 2. Consequently, Global Reach traffic between sites is not inspected.
Note
When utilizing Global Reach, consider enhancing security between Global Reach sites by inspecting traffic within the Azure VMware Solution environment’s NSX-T or an on-premises firewall.
Connection
Description
Connections (D)
Azure VMware Solution private cloud connection to its local regional hub.
Connection (A)
Azure VMware Solution Region 1 Global Reach connection back to on-premises.
Connection (B)
Azure VMware Solution Region 2 Global Reach connection back to on-premises.
Connection (C)
Azure VMware Solution Global Reach connection between the two private clouds’ managed circuits.
Connections (E)
on-premises connectivity via ExpressRoute to both regional hubs.
Inter-Hub
Inter-Hub logical connection between two hubs that are deployed under the same Virtual WAN.
The following sections cover traffic flows and connectivity for Azure VMware Solution, on-premises, Azure Virtual Networks, and the Internet when using Global Reach.
This section focuses on only the Azure VMware Solution Cloud Region 1 and Azure VMware Solution Cloud Region 2. Each Azure VMware Solution private cloud has an ExpressRoute connection to its local regional hub (connections labeled as “D”).
Each Azure VMware Solution Cloud Region connects back to an on-premises via ExpressRoute Global Reach. Azure VMware Solution Cloud Region 1 Global Reach connection is shown as “Global Reach (A)”. The Azure VMware Solution Cloud Region 2 Global Reach connection is shown as “Global Reach (B)”. Both Azure VMware Solution private clouds are connected directly to each other via Global Reach shown as Global Reach (C). Keep in mind that Global Reach traffic will never transit any hub firewalls.
Ensure that you explicitly configure Global Reach (A), Global Reach (B), and Global Reach (C). It is imperative to do this to prevent connectivity issues between Global Reach sites. See traffic flow section for more information.
The diagram below illustrates traffic flows from the perspective of the Azure VMware Solution Private Clouds.
Traffic Flow Chart
Traffic Flow Number
Source
Direction
Destination
Traffic Inspected on Secure Virtual WAN hub firewall?
1
Azure VMware Solution Cloud Region 1
→
Virtual Network 1
Yes, traffic is inspected at Hub 1 firewall
2
Azure VMware Solution Cloud Region 1
→
on-premises
No, traffic bypasses firewall and transits Global Reach (A)
3
Azure VMware Solution Cloud Region 1
→
Virtual Network 2
Yes, traffic is inspected at Hub 2 firewall
4
Azure VMware Solution Cloud Region 1
→
Azure VMware Solution Cloud Region 2
No, traffic bypasses firewall and transits Global Reach (C)
5
Azure VMware Solution Cloud Region 2
→
Virtual Network 1
Yes, traffic is inspected at Hub 1 firewall
6
Azure VMware Solution Cloud Region 2
→
Virtual Network 2
Yes, traffic is inspected at Hub 2 firewall
7
Azure VMware Solution Cloud Region 2
→
on-premises
No, traffic bypasses firewall and transits Global Reach (B)
This section focuses only on the on-premises site. As shown in the diagram, the on-premises site has an ExpressRoute connection to both Region 1 and Region 2 hubs (connections labeled as “E”).
On-premises systems can communicate to Azure VMware Solution Cloud Region 1 via connection “Global Reach (A)”. On-premises systems are also able to communicate with Azure VMware Solution Cloud Region 2 via connection “Global Reach (B)”.
Ensure that you explicitly configure Global Reach (A), Global Reach (B), and Global Reach (C). It is imperative to do this to prevent connectivity issues between Global Reach sites. See traffic flow section for more information.
The diagram below illustrates traffic flows from an on-premises perspective.
Traffic Flow Chart
Traffic Flow Number
Source
Direction
Destination
Traffic Inspected on Secure Virtual WAN hub firewall?
2
on-premises
→
Azure VMware Solution Cloud Region 1
No, traffic bypasses firewall and transits Global Reach (A)
7
on-premises
→
Azure VMware Solution Cloud Region 2
No, traffic bypasses firewall and transits Global Reach (B)
8
on-premises
→
Virtual Network 1
Yes, traffic is inspected at Hub 1 firewall
9
on-premises
→
Virtual Network 2
Yes, traffic is inspected at Hub 2 firewall
This section focuses only on connectivity from an Azure Virtual Network perspective. As depicted in the diagram, both Virtual Network1 and Virtual Network2 have a Virtual Network peering directly to their local regional hub.
A Secure Hub with enabled Routing Intent always sends the default RFC 1918 addresses (10.0.0.0/8, 172.16.0.0/12, 192.168.0.0/16) to peered Virtual Networks, plus any other prefixes that have been added as “Private Traffic Prefixes” – see Routing Intent Private Address Prefixes. In our scenario, with Routing Intent enabled, all resources in Virtual Network 1 and Virtual Network 2 currently possess the default RFC 1918 addresses and use their local regional hub firewall as the next hop. All traffic ingressing and egressing the Virtual Networks will always transit the Hub Firewalls. See traffic flow section for more information.
Traffic Flow Chart
Traffic Flow Number
Source
Direction
Destination
Traffic Inspected on Secure Virtual WAN hub firewall?
1
Virtual Network 1
→
Azure VMware Solution Cloud Region 1
Yes, traffic is inspected at Hub 1 firewall
3
Virtual Network 2
→
Azure VMware Solution Cloud Region 1
Yes, traffic is inspected at Hub 2 firewall
5
Virtual Network 1
→
Azure VMware Solution Cloud Region 2
Yes, traffic is inspected at Hub 1 firewall
6
Virtual Network 2
→
Azure VMware Solution Cloud Region 2
Yes, traffic is inspected at Hub 2 firewall
8
Virtual Network 1
→
on-premises
Yes, traffic is inspected at Hub 1 firewall
9
Virtual Network 2
→
on-premises
Yes, traffic is inspected at Hub 2 firewall
10
Virtual Network 1
→
Virtual Network 2
Yes, traffic is inspected at the Hub 1 firewall, then flows over the inter-hub connection to be inspected by Hub 2 firewall
This section focuses only on how internet connectivity is provided for Azure native resources in Virtual Networks and Azure VMware Solution Private Clouds in both regions. There are several options to provide internet connectivity to Azure VMware Solution. – see Internet Access Concepts for Azure VMware Solution.
Option 1: Internet Service hosted in Azure
Option 2: VMware Solution Managed SNAT
Option 3: Azure Public IPv4 address to NSX-T Data Center Edge
Although you can use all three options with Dual Region Secure Virtual WAN with Routing Intent, “Option 1: Internet Service hosted in Azure” is the best option when using Secure Virtual WAN with Routing Intent and is the option that is used to provide internet connectivity in the scenario.
With Routing Intent you have the option to generate a default route from the hub firewall. This default route is advertised to your Virtual Networks and Azure VMware Solution private clouds. This section is broken into two sections, one that explains internet connectivity from an Azure VMware Solution perspective and another from the Virtual Network perspective.
From an Azure VMware Solution Private Cloud perspective, you have the availability to achieve internet connectivity redundancy because it will learn the default route from both its local regional hub and its cross-regional hub. However, the Azure VMware Solution private cloud will always prioritize the local regional hub for primary internet access connectivity. Its cross-regional hub will serve as an internet backup in the event the local regional hub is down. This setup provides internet access redundancy for outbound traffic only. For inbound internet traffic to Azure VMware Solution workloads, consider using Azure Front Door or Traffic Manager in case of a regional outage.
Going into more detail, the Azure VMware Solution private cloud’s preferred default route “∞ 0.0.0.0/0” is received via connection “D” from its local regional hub. Additionally, the Azure VMware Solution private cloud receives a backup default route “△ 0.0.0.0/0,” which originates on the cross-regional hub and advertised across the Global Reach (C) connection. Ensure that you explicitly configure Global Reach (A), Global Reach (B), and Global Reach (C). It is imperative to do this to prevent connectivity issues between Global Reach sites.
When Routing Intent is enabled for internet traffic, the default behavior of the Secure Virtual WAN Hub is to not advertise the default route across ExpressRoute circuits. To ensure the default route is propagated to the Azure VMware Solution from the Azure Virtual WAN, you must enable default route propagation on your Azure VMware Solution ExpressRoute circuits – see To advertise default route 0.0.0.0/0 to endpoints. It is important to note that this setting should not be enabled for on-premises ExpressRoute circuits. Even though connection “D” will advertise the default route “∞ 0.0.0.0/0” to the Azure VMware Solution private clouds, the default route will also be advertised to on-premises via Global Reach (A) and Global Reach (B). As a result, it is recommended to implement a BGP Filter on your on-premises equipment to exclude learning the default route. This ensures that on-premises internet connectivity is not impacted.
Each Virtual Network will egress to the internet using its local regional hub firewall. When Routing Intent for internet access is enabled, the default route generated from the Secure VWAN Hub is automatically advertised to the hub-peered Virtual Network connections. However, this default route is never advertised across regional hubs over the ‘inter-hub’ link. Therefore, Virtual Networks can only use their local regional hub for internet access and will have no backup internet connectivity to the cross-regional hub. For further details, refer to the traffic flow section.
Traffic Flow Chart
Traffic Flow Number
Source
Direction
Destination
Traffic Inspected on Secure Virtual WAN hub firewall?
Internet Breakout
11
Azure VMware Solution Cloud Region 1
→
Internet
Yes, traffic is inspected at Hub 1 firewall
Via Hub 1 firewall
12
Azure VMware Solution Cloud Region 2
→
Internet
Yes, traffic is inspected at Hub 2 firewall
Via Hub 2 firewall
15
Virtual Network 1
→
Internet
Yes, traffic is inspected at Hub 1 firewall
Via Hub 1 firewall
16
Virtual Network 2
→
Internet
Yes, traffic is inspected at Hub 2 firewall
Via Hub 2 firewall
The traffic flow described below is only valid if there is an outage affecting a local regional hub. For instance, if the local regional hub of Azure VMware Solution experiences an outage, internet traffic will be rerouted to the cross-regional hub for internet connectivity.
Traffic Flow Number
Source
Direction
Destination
Traffic Inspected on Secure Virtual WAN hub firewall?
Internet Breakout
13
Azure VMware Solution Cloud Region 1
→
Internet
Yes, traffic will transit Global Reach (C) and inspected at Hub 2 firewall
Via Hub 2 firewall
14
Azure VMware Solution Cloud Region 2
→
Internet
Yes, traffic will transit Global Reach (C) and inspected at Hub 1 firewall
Via Hub 1 firewall
For more information on Virtual WAN hub configuration, see About virtual hub settings.
For more information on how to configure Azure Firewall in a Virtual Hub, see Configure Azure Firewall in a Virtual WAN hub.
For more information on how to configure the Palo Alto Next Generation SAAS firewall on Virtual WAN, see Configure Palo Alto Networks Cloud NGFW in Virtual WAN .
For more information on Virtual WAN hub routing intent configuration, see Configure routing intent and policies through Virtual WAN portal.
Microsoft Tech Community – Latest Blogs –Read More
Need to know if fluentd can be setup to filter logs from azure kubernetes service before sending it
Hi,
I have a Kubernetes service setup in azure and have enabled insights for the same. I have created a log analytics workspace and a diagnostic setting to send all the logs to the log analytics workspace. In order for me to reduce the cost of data ingestion and implement log rotation i’m thinking of using fluentd.
So my approach would be to install the fluentd agent/docker image in the kubernetes service and filter it out before sending the logs to the log analytics workspace.
Is this approach even possible? If so please help me with few sources/reference links.
Hi,I have a Kubernetes service setup in azure and have enabled insights for the same. I have created a log analytics workspace and a diagnostic setting to send all the logs to the log analytics workspace. In order for me to reduce the cost of data ingestion and implement log rotation i’m thinking of using fluentd.So my approach would be to install the fluentd agent/docker image in the kubernetes service and filter it out before sending the logs to the log analytics workspace.Is this approach even possible? If so please help me with few sources/reference links. Read More