Tag Archives: microsoft
Disabled web push notifications on Android of a deployed Web link
Hi,
We are using Microsoft Intune to manage our company devices. We have enabled web push notifications on one of our websites, and it works correctly on Windows desktops as well as on Android and iOS devices.
However, once we deploy the website as a web app link through Intune on Android, the web push feature no longer works (even though we enabled push notifications on the App deployed by Intune on the device for the web link). Additionally, even when connecting to the website directly through Chrome web push notifications do not work.
It seems that the browser might not allow enabling the web push service for our website when it’s installed through Intune. We know it’s not a device or browser issue because web push notifications work correctly if we connect to another test website that’s not deployed through Intune.
Is there any configuration or setting we need to do on Intune to enable web push notifications on our Android devices?
Thank you in advance for any help,
Charles
Hi, We are using Microsoft Intune to manage our company devices. We have enabled web push notifications on one of our websites, and it works correctly on Windows desktops as well as on Android and iOS devices.However, once we deploy the website as a web app link through Intune on Android, the web push feature no longer works (even though we enabled push notifications on the App deployed by Intune on the device for the web link). Additionally, even when connecting to the website directly through Chrome web push notifications do not work.It seems that the browser might not allow enabling the web push service for our website when it’s installed through Intune. We know it’s not a device or browser issue because web push notifications work correctly if we connect to another test website that’s not deployed through Intune.Is there any configuration or setting we need to do on Intune to enable web push notifications on our Android devices?Thank you in advance for any help,Charles Read More
You must install or update .NET to run this application
Trying to get Cloud Scripting working. I have an Azure subscription and the ID is set in the publishing panel. When I run my project in the editor I get the error:
0:00.000 Error [CloudScriptingCloudHosting]: . [2024-04-19T16:53:25.259725Z: Error]: CloudScriptingAppProcess.. You must install or update .NET to run this application.
I have the latest version of the .NET SDK installed (.NET 8)
Trying to get Cloud Scripting working. I have an Azure subscription and the ID is set in the publishing panel. When I run my project in the editor I get the error: 0:00.000 Error [CloudScriptingCloudHosting]: . [2024-04-19T16:53:25.259725Z: Error]: CloudScriptingAppProcess.. You must install or update .NET to run this application.I have the latest version of the .NET SDK installed (.NET 8) Read More
How to enroll training services designation
We are enrolled as Cloud AI partner program, please guide how to enroll to Training services designation
We are enrolled as Cloud AI partner program, please guide how to enroll to Training services designation Read More
Debugging MS Store – Appxsym removed?
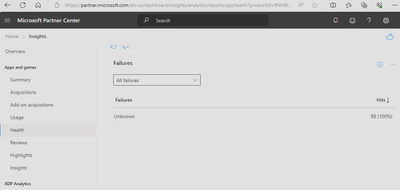
The Insights health report for my Win32 app only reports Unknown failure:
So to resolve, I first generated debug symbols as a .pdb file using /DEBUG and /Zi
Then configured the MSIX generator to include symbols:
However symbols did not seem to be included yet.
Symbols were successfully included after following instructions in this Stackoverflow discussion to edit Microsoft.AppxPackage.Targets, setting AppxPackageIncludePrivateSymbols to true.
I confirmed the newly generated .msixbundle does indeed include a .appxsym file, which contains the .pdb debug symbols.
After submitting to the Partner Dashboard for distribution, I install the new version from the MS Store and cannot locate the .pdb file. And the failure reports for the new version still only report “Unknown”
How can I receive detailed crash reports for the app?
Thanks
The Insights health report for my Win32 app only reports Unknown failure: So to resolve, I first generated debug symbols as a .pdb file using /DEBUG and /ZiThen configured the MSIX generator to include symbols:However symbols did not seem to be included yet.Symbols were successfully included after following instructions in this Stackoverflow discussion to edit Microsoft.AppxPackage.Targets, setting AppxPackageIncludePrivateSymbols to true. I confirmed the newly generated .msixbundle does indeed include a .appxsym file, which contains the .pdb debug symbols. After submitting to the Partner Dashboard for distribution, I install the new version from the MS Store and cannot locate the .pdb file. And the failure reports for the new version still only report “Unknown” How can I receive detailed crash reports for the app? Thanks Read More
Outlook crashed in Chrome
I have outlook ctrashes in Chrome windows 10 desktop despite having cache cleared, restarting computer and deleting and reinstalling outlook. I can’t get thru my email without it fgreezing or crashing.
I have outlook ctrashes in Chrome windows 10 desktop despite having cache cleared, restarting computer and deleting and reinstalling outlook. I can’t get thru my email without it fgreezing or crashing. Read More
Print via Send document to API
I am trying to test some unattended print scenarios. I know there are some limitations currently, but is there a reason the following would not work:
Use the graph API to send a pdf document to a UP connected printer that is able to print a PDF document. Create print job create upload session and upload document tell the print job to start
Other info
– Printer is connected to UP and can be printed to from client devices
Print job is in the UP queue, but printer does not process the job.
I am trying to test some unattended print scenarios. I know there are some limitations currently, but is there a reason the following would not work:Use the graph API to send a pdf document to a UP connected printer that is able to print a PDF document. Create print job create upload session and upload document tell the print job to start Other info- Printer is connected to UP and can be printed to from client devices Print job is in the UP queue, but printer does not process the job. Read More
MozzGuard Consumer Reports-(Mozz Guard Canada)-Step-by-step guide to setting up the Mozz Guard Mosqu
Furthermore, the Mozz Guard Mosquito Zapper is also a cost-effective solution. In the long run, investing in this device can save you money compared to continuously purchasing expensive mosquito repellents or hiring professional exterminators. With the Mozz Guard Mosquito Zapper, you have a one-time investment that provides long-lasting protection season after season. It’s a smart choice for your wallet and your peace of mind.
Click Here To Purchase Mozz Guard Directly From The Official Website At A Discount Price
Enjoy a mosquito-free summer with Mozz Guard. Place your orders now!
Furthermore, the Mozz Guard Mosquito Zapper is also a cost-effective solution. In the long run, investing in this device can save you money compared to continuously purchasing expensive mosquito repellents or hiring professional exterminators. With the Mozz Guard Mosquito Zapper, you have a one-time investment that provides long-lasting protection season after season. It’s a smart choice for your wallet and your peace of mind. Click Here To Purchase Mozz Guard Directly From The Official Website At A Discount PriceEnjoy a mosquito-free summer with Mozz Guard. Place your orders now! Read More
Duck Game Crashes
I am hoping that someone here might be able to steer me in the right direction. I have posted in the game’s forum, but I am not receiving any support there. I have a new laptop running Windows 11. We are getting frequent game crashes while playing Duck Game. I am wondering if it is a compatibility issue as the game is older. Any help would be GREATLY appreciated. Here is our most recent crash report:
System.InvalidOperationException: An unexpected error has occurred.
at Microsoft.Xna.Framework.Graphics.GraphicsDevice.DrawUserIndexedPrimitives[T](PrimitiveType primitiveType, T[] vertexData, Int32 vertexOffset, Int32 numVertices, Array indexData, Int32 indexOffset, Int32 primitiveCount, VertexDeclaration vertexDeclaration, _D3DFORMAT indexFormat)
at DuckGame.MTSpriteBatcher.FlushVertexArray(Int32 start, Int32 end) in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeRenderSpriteBatcher.cs:line 709
at DuckGame.MTSpriteBatcher.DrawBatch(SpriteSortMode sortMode) in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeRenderSpriteBatcher.cs:line 485
at DuckGame.MTSpriteBatch.End() in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeRenderMTSpriteBatch.cs:line 151
at DuckGame.Layer.End(Boolean transparent, Boolean isTargetDraw) in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeLayer.cs:line 897
at DuckGame.Layer.Draw(Boolean transparent, Boolean isTargetDraw) in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeLayer.cs:line 1154
at DuckGame.LayerCore.DrawLayers() in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeLayer.cs:line 381
at DuckGame.Level.DoDraw() in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeLevel.cs:line 1081
at DuckGame.Level.DrawCurrentLevel() in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeLevel.cs:line 198
at DuckGame.MonoMain.RunDraw(GameTime gameTime) in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeMonoMain.cs:line 2524
at DuckGame.MonoMain.Draw(GameTime gameTime) in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeMonoMain.cs:line 2246
Last 8 Lines of Console Output:
Creating ghost (1442)
@received Activating NMItemSpawned (2044->2045)((0)(H)LawMac,76561198093753884)(16)
@received Activating NMFireGun (2045->2046)((0)(H)LawMac,76561198093753884)(16)
@sent Sent NMKillDuck (421)((0)(H)LawMac,76561198093753884)(16)
Creating ghost (1443)
@received Activating NMItemSpawned (2046->2047)((0)(H)LawMac,76561198093753884)(16)
Creating ghost (8879)
Creating ghost (8880)
Date: 04/19/2024 03:58:56
Version: 1.1.7717.16376
Platform: Windows 10 (Steam Build 8782838)(SFX)
Online: 1 (C,0.01582697)
Mods: nomods
Time Played: 00:39:02 (140607)
Special Code: men20
Resolution: (A)1920×1080 (G)1920×1080 (Fullscreen(W))(RF 140420)
Level: Content/levels/deathmatch/office01_8.lev
Command Line:
I am hoping that someone here might be able to steer me in the right direction. I have posted in the game’s forum, but I am not receiving any support there. I have a new laptop running Windows 11. We are getting frequent game crashes while playing Duck Game. I am wondering if it is a compatibility issue as the game is older. Any help would be GREATLY appreciated. Here is our most recent crash report: System.InvalidOperationException: An unexpected error has occurred.at Microsoft.Xna.Framework.Graphics.GraphicsDevice.DrawUserIndexedPrimitives[T](PrimitiveType primitiveType, T[] vertexData, Int32 vertexOffset, Int32 numVertices, Array indexData, Int32 indexOffset, Int32 primitiveCount, VertexDeclaration vertexDeclaration, _D3DFORMAT indexFormat)at DuckGame.MTSpriteBatcher.FlushVertexArray(Int32 start, Int32 end) in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeRenderSpriteBatcher.cs:line 709at DuckGame.MTSpriteBatcher.DrawBatch(SpriteSortMode sortMode) in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeRenderSpriteBatcher.cs:line 485at DuckGame.MTSpriteBatch.End() in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeRenderMTSpriteBatch.cs:line 151at DuckGame.Layer.End(Boolean transparent, Boolean isTargetDraw) in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeLayer.cs:line 897at DuckGame.Layer.Draw(Boolean transparent, Boolean isTargetDraw) in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeLayer.cs:line 1154at DuckGame.LayerCore.DrawLayers() in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeLayer.cs:line 381at DuckGame.Level.DoDraw() in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeLevel.cs:line 1081at DuckGame.Level.DrawCurrentLevel() in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeLevel.cs:line 198at DuckGame.MonoMain.RunDraw(GameTime gameTime) in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeMonoMain.cs:line 2524at DuckGame.MonoMain.Draw(GameTime gameTime) in C:gamedevduckgame_current_steamduckgameDuckGamesrcMonoTimeMonoMain.cs:line 2246Last 8 Lines of Console Output:Creating ghost (1442)@received Activating NMItemSpawned (2044->2045)((0)(H)LawMac,76561198093753884)(16)@received Activating NMFireGun (2045->2046)((0)(H)LawMac,76561198093753884)(16)@sent Sent NMKillDuck (421)((0)(H)LawMac,76561198093753884)(16)Creating ghost (1443)@received Activating NMItemSpawned (2046->2047)((0)(H)LawMac,76561198093753884)(16)Creating ghost (8879)Creating ghost (8880)Date: 04/19/2024 03:58:56Version: 1.1.7717.16376Platform: Windows 10 (Steam Build 8782838)(SFX)Online: 1 (C,0.01582697)Mods: nomodsTime Played: 00:39:02 (140607)Special Code: men20Resolution: (A)1920×1080 (G)1920×1080 (Fullscreen(W))(RF 140420)Level: Content/levels/deathmatch/office01_8.levCommand Line: Read More
Feed does not exists
Post ContentRead More
MFA alerts for when a alternative phone number is added
Hi, i need to be able to find a way when someones adds a alternative phone number to MFA it sends an alert via email that would go into a shared mailbox but haven’t been able to find a way to get the MFA alerts for alternative phone numbers. can someone help please?
Hi, i need to be able to find a way when someones adds a alternative phone number to MFA it sends an alert via email that would go into a shared mailbox but haven’t been able to find a way to get the MFA alerts for alternative phone numbers. can someone help please? Read More
Issues carrying table/data over to different sheet with matching.
Hi,
I’m having trouble figuring out how to go about transferring information into another sheet based on matching criteria.
In one sheet I have columns of sets, reps, load, with the corresponding #s below (sometimes 2 or 3 rows depending on the week). My goal is to have these set/rep schemes named. That way, when I build a program on another sheet, I can simply click the name of the set scheme via a list (from data validation) and have the schemes auto-filled into the corresponding cells.
I’m unsure how to proceed with naming the data set of sets/reps/load (since there are multiple weeks to account for) or what formula to use to essentially copy and paste the data set to my preferred cells based on the matching name I choose.
For example, in Sheet 1, C3-H3 is Sets1, Reps1, Load1…Load2, C4:H6 are the prescribed numbers. How would I name this set? Then, in another sheet if I have a data-validated list cell (for the scheme), what formula would carry the information over into the new sheet?
Appreciate the help.
Hi, I’m having trouble figuring out how to go about transferring information into another sheet based on matching criteria. In one sheet I have columns of sets, reps, load, with the corresponding #s below (sometimes 2 or 3 rows depending on the week). My goal is to have these set/rep schemes named. That way, when I build a program on another sheet, I can simply click the name of the set scheme via a list (from data validation) and have the schemes auto-filled into the corresponding cells. I’m unsure how to proceed with naming the data set of sets/reps/load (since there are multiple weeks to account for) or what formula to use to essentially copy and paste the data set to my preferred cells based on the matching name I choose. For example, in Sheet 1, C3-H3 is Sets1, Reps1, Load1…Load2, C4:H6 are the prescribed numbers. How would I name this set? Then, in another sheet if I have a data-validated list cell (for the scheme), what formula would carry the information over into the new sheet? Appreciate the help. Read More
Create new lists from an array in Excel
Hi,
I would like help building a formula that creates a new list of values from an array containing a reference value in example below find all “a”, “b” & “c” and populate the list with the corresponding Col 2 value
e.g.
Col1 Col2 new list “a” new list “b” new list “c”
a 1 1 5 3
a 2 2 4 2
b 5 2 3
c 3 5
b 4
c 2
c 3
a 2
a 5
Thanks All
Hi,I would like help building a formula that creates a new list of values from an array containing a reference value in example below find all “a”, “b” & “c” and populate the list with the corresponding Col 2 valuee.g. Col1 Col2 new list “a” new list “b” new list “c”a 1 1 5 3a 2 2 4 2b 5 2 3c 3 5 b 4c 2c 3a 2a 5 Thanks All Read More
Windows 11 file explorer top toolbar freezing
Hello everyone,
I have a client set up in a new azure virtual desktop environment with fslogix. Everything is running smoothly, but there are certain times when the top toolbar in file explorer just freezes. Most of the time it only affects the ability to use the back arrow, but sometimes it affects the entire toolbar.
Has anyone seen a problem like this? Any possible solution to try?
thanks
Hello everyone,I have a client set up in a new azure virtual desktop environment with fslogix. Everything is running smoothly, but there are certain times when the top toolbar in file explorer just freezes. Most of the time it only affects the ability to use the back arrow, but sometimes it affects the entire toolbar.Has anyone seen a problem like this? Any possible solution to try?thanks Read More
How to eliminate automatic page breaks
A certain portion of my worksheet has a ‘zillion’ automatic page breaks that I don’t know how to eliminate. Help!!!
A certain portion of my worksheet has a ‘zillion’ automatic page breaks that I don’t know how to eliminate. Help!!! Read More
Blurry text in Microsoft word 365, Win 11
May I know how to solve this blurry issues? getting my nerve now. Keep happening to me when I scrolling and stay blurry for quite awhile and even permanent until I close and reopen my word.
blurry texts
May I know how to solve this blurry issues? getting my nerve now. Keep happening to me when I scrolling and stay blurry for quite awhile and even permanent until I close and reopen my word. blurry texts Read More
Right function
Hi,
Is there a way for the right function to omit zeros from the start of the findings?
My example is: we use the last digits of our item codes to generate a batch number; the format always starts with the letter I and then has 5 numeric following the letter. I only want to capture the numbers greater than zero from the item code!
So if I had our item I01141 it would return 1141, but if I had item I00141 it would return 141 and omit the zeros. Anybody got an idea on how to do this please?
Hi, Is there a way for the right function to omit zeros from the start of the findings?My example is: we use the last digits of our item codes to generate a batch number; the format always starts with the letter I and then has 5 numeric following the letter. I only want to capture the numbers greater than zero from the item code!So if I had our item I01141 it would return 1141, but if I had item I00141 it would return 141 and omit the zeros. Anybody got an idea on how to do this please? Read More
come levare la crittografia su un file excel
sto avendo un problema con excel, poco fa ho unserito la protezione di un file excel ma adesso non riesco più a toglierla.
sto avendo un problema con excel, poco fa ho unserito la protezione di un file excel ma adesso non riesco più a toglierla. Read More
Autofill feature
Hi,
I am trying to fill a column on a spreadsheet with over 2,000 rows. Is there a way to auto fill the column efficiently? I just need to fill the column on this specific table, not the entire worksheet.
Hi, I am trying to fill a column on a spreadsheet with over 2,000 rows. Is there a way to auto fill the column efficiently? I just need to fill the column on this specific table, not the entire worksheet. Read More
Pictionary on Microsoft Teams
We want to play Pictionary on Microsoft Teams. I want to know, is there a built-in feature for this game in the Teams desktop version?
Thank you.
We want to play Pictionary on Microsoft Teams. I want to know, is there a built-in feature for this game in the Teams desktop version?Thank you. Read More
Setting up Sentinel for Kubernetes Monitoring
A guide to using Microsoft Sentinel for monitoring the security of your containerized applications and orchestration platforms.
Part 3 of 3 part series about security monitoring of your Kubernetes Clusters and CI/CD pipelines by @singhabhi and @Umesh_Nagdev , Security GBB
Link to Part 1
Link to Part 2
Introduction
In part 1 and part 2 of this series, we discussed the type of log sources you should consider for monitoring the security of your Kubernetes environment, most pertinent risks (and corresponding use cases) in your AKS environment, and log sources to ingest data. This blog will demonstrate how to configure Azure Sentinel to derive identify the risks.
More specifically we will show:
Mapping of container security risks with Microsoft Defender for Cloud
Data connectors to ingest AKS data
Container Security Workbooks in Sentinel
Search queries to mine specific log tables for more pressing risks
How Microsoft Defender for Cloud addresses container risks
Microsoft Defender for Containers is a security solution designed specifically for containerized environments. Microsoft Defender for Containers provides several key capabilities to enhance container security:
Real-time protection: Defender for Containers offers real-time protection by continuously monitoring container activities, network traffic, and system events. It uses machine learning algorithms and heuristics to detect and respond to potential threats promptly.
Vulnerability management: The solution helps identify vulnerabilities in container images and runtime environments. It can scan container images for known vulnerabilities, misconfigurations, and insecure dependencies, allowing organizations to address these issues before deploying containers into production.
Malware detection: Defender for Containers can detect and block malicious code, malware, and suspicious activities within containers. It leverages signature-based detection, behavioral analysis, and sandboxing techniques to identify and mitigate threats.
File integrity monitoring: The solution includes file integrity monitoring capabilities to detect unauthorized changes or tampering within containerized environments. It monitors critical system files, configuration files, and application binaries for any suspicious modifications.
Network security: Defender for Containers helps secure container network traffic by enforcing access controls, segmenting network traffic, and detecting anomalies or suspicious network behavior. It can detect and block malicious network activities, such as port scanning, denial-of-service attacks, and lateral movement attempts.
Integration with Azure Security Center: Defender for Containers integrates seamlessly with Azure Security Center, providing centralized visibility, monitoring, and management of container security across hybrid and multi-cloud environments. It leverages Azure’s cloud-native security capabilities and threat intelligence to enhance container security posture.
Incident response and remediation: In case of security incidents or suspicious activities, Defender for Containers provides tools for incident investigation, threat hunting, and automated remediation actions. It helps security teams quickly respond to security incidents and mitigate potential risks.
There are several alerts https://learn.microsoft.com/en-us/azure/defender-for-cloud/alerts-reference#alerts-for-containers—kubernetes-clusters that you get out of the box.
Additionally, you can secure the Kubernetes Control Plane using Azure Policy (https://learn.microsoft.com/en-us/azure/aks/use-azure-policy).
This resource https://techcommunity.microsoft.com/t5/microsoft-defender-for-cloud/leveraging-defender-for-containers-to-simplify-policy-management/ba-p/3755757 provides additional background on how Azure Policies work to protect your Kubernetes Control Plane.
There are several out of the box policies that can quickly get you started https://learn.microsoft.com/en-us/azure/aks/policy-reference
The table below shows a mapping of container risks to MDC alerts and Azure Policies. You will see that with the help of Defender for Containers you will get a great coverage across several risks that we discussed in blog part 2
#
Kubernetes Risk
Risk Area
MDC Alert(s)
Azure Policy(s)
1
Detect unauthorized or suspicious pods running in the cluster.
Pod Security Monitoring
Attempt to create a new Linux namespace from a container detected
Anomalous pod deployment (Preview)
Anomalous secret access (Preview)
Behavior similar to common Linux bots detected (Preview)
Command within a container running with high privileges
Container running in privileged mode
Container with a sensitive volume mount detected
Kubernetes cluster containers should only pull images when image pull secrets are present
Kubernetes cluster containers CPU and memory resource limits should not exceed the specified limits
Kubernetes cluster containers should only use allowed capabilities
Kubernetes cluster containers should only use allowed images
Kubernetes cluster containers should only use allowed pull policy
Kubernetes cluster containers should run with a read only root file system
Kubernetes cluster pod hostPath volumes should only use allowed host paths
Kubernetes cluster pods and containers should only run with approved user and group IDs
2
Monitor for privilege escalation attempts within pods.
Pod Security Monitoring
Attempt to create a new Linux namespace from a container detected
Anomalous secret access (Preview)
Command within a container running with high privileges
Container running in privileged mode
Container with a sensitive volume mount detected
Detected file download from a known malicious source
Excessive role permissions assigned in Kubernetes cluster (Preview)
Privileged container detected
Kubernetes cluster containers should only pull images when image pull secrets are present
Kubernetes cluster containers CPU and memory resource limits should not exceed the specified limits
Kubernetes cluster containers should only use allowed capabilities
Kubernetes cluster containers should only use allowed images
Kubernetes cluster containers should only use allowed pull policy
Kubernetes cluster containers should run with a read only root file system
Kubernetes cluster pod hostPath volumes should only use allowed host paths
Kubernetes cluster pods and containers should only run with approved user and group IDs
3
Track and alert on changes to pod security policies.
Pod Security Monitoring
None
None
4
Identify and alert on unexpected network traffic patterns.
Network Security Monitoring
An uncommon connection attempt detected
CoreDNS modification in Kubernetes detected
K8S API requests from proxy IP address detected
Potential reverse shell detected
Potential port forwarding to external IP address
Suspicious use of DNS over HTTPS
None
5
Monitor for unauthorized ingress and egress traffic.
Network Security Monitoring
An uncommon connection attempt detected
CoreDNS modification in Kubernetes detected
K8S API requests from proxy IP address detected
Potential reverse shell detected
Potential port forwarding to external IP address
Suspicious use of DNS over HTTPS
None
6
Detect and investigate potential denial-of-service (DoS) attacks.
Network Security Monitoring
Indicators associated with DDOS toolkit detected
None
7
Scan container images for vulnerabilities before deployment.
Container Image Security
None (Gating when released)
Scanning is automatically done as part of ACR
Running container images should have vulnerability findings resolved
Running container images should have vulnerability findings resolved (powered by Microsoft Defender Vulnerability Management)
8
Monitor for unauthorized or unsigned images.
Container Image Security
None
Kubernetes cluster containers should only use allowed images
Kubernetes clusters should only use images signed by notation
[Preview]: Deploy Image Integrity on Azure Kubernetes Service
9
Track changes to container image repositories.
Container Image Security
None
Configure container registries to disable anonymous authentication
Configure container registries to disable ARM audience token authentication.
Configure container registries to disable local admin account.
Container registries should be encrypted with a customer-managed key
Container registries should have anonymous authentication disabled.
10
Monitor kubelet logs for signs of compromise or unauthorized access.
Kubelet Activity Monitoring
Possible credential access tool detected
Abnormal Kubernetes service account operation detected
Anomalous secret access (Preview)
Creation of admission webhook configuration detected
None
11
Detect abnormal activities related to node management.
Kubelet Activity Monitoring
“K8S.NODE_” Alerts
[Preview]: Cannot Edit Individual Nodes
[Preview]: Kubernetes clusters should restrict creation of given resource type
Azure Kubernetes Clusters should enable Container Storage Interface(CSI)
Azure Kubernetes Clusters should enable Key Management Service (KMS)
Azure Kubernetes Clusters should use Azure CNI
Azure Kubernetes Service Clusters should enable node os auto-upgrade
Azure Role-Based Access Control (RBAC) should be used on Kubernetes Services
Both operating systems and data disks in Azure Kubernetes Service clusters should be encrypted by customer-managed keys
Configure Node OS Auto upgrade on Azure Kubernetes Cluster
Deploy Azure Policy Add-on to Azure Kubernetes Service clusters
Kubernetes cluster containers CPU and memory resource limits should not exceed the specified limits
Kubernetes clusters should not allow container privilege escalation
Kubernetes clusters should not allow endpoint edit permissions of ClusterRole/system:aggregate-to-edit
Kubernetes clusters should not grant CAP_SYS_ADMIN security capabilities
Kubernetes clusters should use internal load balancers
12
Monitor Kubernetes API server logs for suspicious activities.
API Server Security
“K8S_*” Alerts
None
13
Track and alert on failed authentication attempts.
API Server Security
AKS clusters should be set up to use Azure AD Authentication
https://techcommunity.microsoft.com/t5/fasttrack-for-azure/azure-kubernetes-service-rbac-options-in-practice/ba-p/3684275
Azure Kubernetes Service Clusters should enable Microsoft Entra ID integration
14
Detect unusual API server request patterns.
API Server Security
“K8S_*” Alerts
None
15
Monitor changes to RBAC policies and roles.
RBAC (Role-Based Access Control) Monitoring
Role binding to the cluster-admin role detected
AKS clusters should be set up to use Azure AD Authentication
https://techcommunity.microsoft.com/t5/fasttrack-for-azure/azure-kubernetes-service-rbac-options-in-practice/ba-p/3684275
Azure Kubernetes Service Clusters should enable Microsoft Entra ID integration
16
Detect and alert on unauthorized access attempts.
RBAC (Role-Based Access Control) Monitoring
Role binding to the cluster-admin role detected
AKS clusters should be set up to use Azure AD Authentication
https://techcommunity.microsoft.com/t5/fasttrack-for-azure/azure-kubernetes-service-rbac-options-in-practice/ba-p/3684276
Azure Kubernetes Service Clusters should enable Microsoft Entra ID integration
17
Track role binding changes and escalations.
RBAC (Role-Based Access Control) Monitoring
Role binding to the cluster-admin role detected
Kubernetes clusters should minimize wildcard use in role and cluster role
18
Monitor for unauthorized access to Kubernetes secrets and ConfigMaps.
Secrets and ConfigMap Access Monitoring
Anomalous secret access (Preview)
Process seen accessing the SSH authorized keys file in an unusual way
Defender for Key Vault also detects unusual access patterns
None
19
Detect changes to sensitive configuration data.
Secrets and ConfigMap Access Monitoring
None
Should be using Key Vault for Sensitive Data
Defender for Key Vault also detects unusual access patterns
None
20
Track usage patterns of sensitive information.
Secrets and ConfigMap Access Monitoring
None
Should be using Key Vault for Sensitive Data
Defender for Key Vault also detects unusual access patterns
None
21
Enable and monitor Kubernetes audit logs for cluster-wide activities.
Audit Logging
A history file has been cleared
Kubernetes events deleted
Possible Log Tampering Activity Detected
Deploy – Configure diagnostic settings for Azure Kubernetes Service to Log Analytics workspace
22
Correlate audit logs to identify security events and policy violations.
Audit Logging
Done natively by Defender for Container alerts
Deploy – Configure diagnostic settings for Azure Kubernetes Service to Log Analytics workspace
23
Regularly review audit logs for anomalies and potential threats.
Audit Logging
Not applicable
Not applicable
24
Ensure compliance with security standards and policies.
Compliance Monitoring
Defender for CSPM Regulatory Recommendations
None
25
Monitor for deviations from security best practices.
Compliance Monitoring
Defender for CSPM Regulatory Recommendations
None
26
Generate reports on compliance status and potential risks.
Compliance Monitoring
Defender for CSPM Regulatory Recommendations
None
27
Monitor runtime activities of containers for abnormal behavior.
Container Runtime Security
“K8S_*” Alerts
None
28
Detect and alert on suspicious system calls within containers.
Container Runtime Security
“K8S_*” Alerts
None
29
Integrate with container runtime security tools for enhanced monitoring.
Container Runtime Security
“K8S_*” Alerts
None
30
Develop and test incident response plans for Kubernetes security incidents.
Incident Response and Forensics
Not applicable
Not applicable
31
Monitor for indicators of compromise (IoCs) and initiate investigations.
Incident Response and Forensics
Done natively by Defender for Container alerts
Not applicable
32
Collect and analyze forensics data in the event of a security incident
Incident Response and Forensics
Done natively by Defender for Container alerts
Not applicable
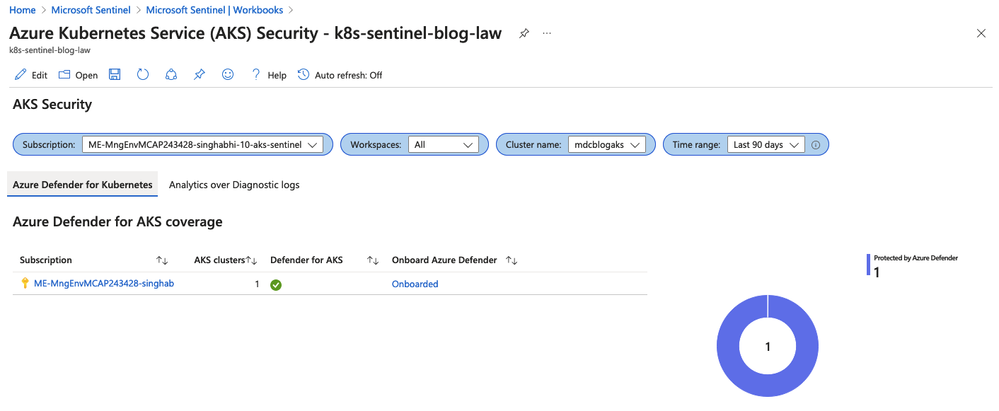
AKS Security Workbook
There is an out of the box work that you can enable once you deploy the AKS Connector from Content Hub. If you are not familiar with Sentinel workbooks please refer to this resource https://techcommunity.microsoft.com/t5/microsoft-sentinel-blog/azure-sentinel-workbooks-101-with-sample-workbook/ba-p/1409216 to learn about how to enable and leverage workbooks.
Let’s do a walkthrough of the AKS Security Workbook
Understanding the security coverage
As we showcased above, Defender for Cloud provides a great coverage for your container security related risks.
The first part would be to understand where you might have some blind spots that is the AKS clusters that are currently not being monitored by Defender for Cloud. The workbook allows you to look at the data across different subscriptions and the coverage table provides insights into where coverage is lacking.
Note: The is a drop down for selecting the Time Range so you can see the items like alerts, recommendations etc. for that time period.
Looking at the Overview of security alerts
For the given time period as we discussed earlier, you will see the security state of your clusters. This dashboard helps you understand where you have the most exposure across container image repos and clusters.
You can also see how alerts have changed over period of time.
Diving deeper into specific alerts
Now that we understand our AKS Cluster coverage and areas of risk exposures, this next section shows you security alerts that exists in your environment. This way you can quickly prioritize where it would make sense to start to close most gaps.
Search queries for security monitoring
In this section we will talk about building custom content to search for common use cases.
1. Identifying the Users and IPs who have most number of denies
You would want to understand who is trying to get situational awareness of your AKS environment. This can be an existing user or a script that’s trying to query your cluster.
//API Authorization Deny by User, Source IP
AKSAudit
| where TimeGenerated > ago (1h)
| extend authorizationDecision = parse_json(Annotations)
| extend user = parse_json(User)
| extend sourceIps = parse_json(SourceIps)
| project TimeGenerated, PodName, Verb, sourceIps[0],user.username, authorizationDecision[“authorization.k8s.io/decision”], RequestUri
| order by TimeGenerated asc
2. Users that are assigned to Cluster Roles
A ClusterRole can be used to grant the same permissions as a Role. Because ClusterRoles are cluster-scoped, you can also use them to grant access to:
cluster-scoped resources (like nodes)
non-resource endpoints (like /healthz)
namespaced resources (like Pods), across all namespaces
You should not assign users to cluster roles. The following query shows you the users are aligned to a Cluster Role
AKSAudit
| where TimeGenerated > ago (1h)
| where RequestObject.kind == “ClusterRoleBinding”
| where ResponseObject.subjects[0].name != “aks-support”
| project TimeGenerated, PodName, Verb, SourceIP=SourceIps[0],User=ResponseObject.subjects[0].name,ClusterRoleBinding=ResponseObject.metadata.name,ClusterRole=RequestObject.roleRef.name
| order by TimeGenerated asc
3. Users that have Admin Access
Users should not be part of system:masters and system:accounts. Any user who is a member of this group bypasses all RBAC rights checks and will always have unrestricted superuser access, which cannot be revoked by removing RoleBindings or ClusterRoleBindings.
//Users part of system:masters or Users that are part of system:accounts
AKSAudit
| where TimeGenerated > ago (1h)
| extend authorizationDecision = parse_json(Annotations)
| extend user = parse_json(User)
| extend sourceIps = parse_json(SourceIps)
| where user.groups[0] in (“system:masters”,”system:accounts”) or user.groups[1] in (“system:masters”,”system:accounts”)
| where user.username !in (“aksService”,”system:apiserver”,”aksProblemDetector”)
| project TimeGenerated, PodName, Verb, SourceIP=sourceIps[0],Username=user.username, AuthorizationDecision=authorizationDecision[“authorization.k8s.io/decision”], AuthorizationDecisionReason=authorizationDecision[“authorization.k8s.io/reason”], RequestUri
| order by TimeGenerated asc
4. Resources that can run unauthenticated and anonymous API calls
You would want to know who is part of system:unauthenticated group and remove them where possible, as this gives access to anyone who can contact the API server at a network level.
/Bindings of system:unauthenticated and system:anonymous group
AKSAudit
| where TimeGenerated > ago (1h)
| where PodName !startswith “kube-apiserver”
| extend authorizationDecision = parse_json(Annotations)
| extend user = parse_json(User)
| extend sourceIps = parse_json(SourceIps)
| extend ObjectRef = parse_json(ObjectRef)
| where user.groups[0] in (“system:unauthenticated”,”system:anonymous”) or user.groups[1] in (“system:unauthenticated”,”system:anonymous”)
| project TimeGenerated, PodName, Verb, Resource=ObjectRef.resource, SourceIP=sourceIps[0],Username=user.username, AuthorizationDecision=authorizationDecision[“authorization.k8s.io/decision”], AuthorizationDecisionReason=authorizationDecision[“authorization.k8s.io/reason”], RequestUri
| order by TimeGenerated asc
5. Users that are trying to get secrets
There are not many common use cases where a user is getting Kubernetes secrets.
//Users that have executed ‘kubectl get secrets’
AKSAudit
| where TimeGenerated > ago (1h)
| where Verb == “get”
| extend authorizationDecision = parse_json(Annotations)
| extend user = parse_json(User)
| extend sourceIps = parse_json(SourceIps)
| extend ObjectRef = parse_json(ObjectRef)
| where ObjectRef.resource == “secrets”
| where user.username !startswith “system:serviceaccount”
| project TimeGenerated, PodName, Verb, SourceIP=sourceIps[0],Username=user.username, AuthorizationDecision=authorizationDecision[“authorization.k8s.io/decision”], AuthorizationDecisionReason=authorizationDecision[“authorization.k8s.io/reason”], RequestUri
| order by TimeGenerated asc
6. Users that are trying to bind to Cluster Admin roles
Like we discussed above Cluster Admin roles should be used sparingly. You would want to know who is trying to bind to Cluster Roles
//Users that have executed Cluster Role Binding on cluster admin
AKSAudit
| where TimeGenerated > ago (1h)
| where Verb == “create”
| extend authorizationDecision = parse_json(Annotations)
| extend user = parse_json(User)
| extend sourceIps = parse_json(SourceIps)
| extend ObjectRef = parse_json(ObjectRef)
| where user.username != “aksService”
| where ObjectRef.resource startswith “clusterrole”
| project TimeGenerated, PodName, Verb, Resource=ObjectRef.resource, SourceIP=sourceIps[0],Username=user.username, AuthorizationDecision=authorizationDecision[“authorization.k8s.io/decision”], AuthorizationDecisionReason=authorizationDecision[“authorization.k8s.io/reason”], RequestUri
| order by TimeGenerated asc
7. Pods that are in default namespace
In Kubernetes, namespaces provides a mechanism for isolating groups of resources within a single cluster. Namespaces are a way to divide cluster resources between multiple users. Kubernetes includes the default namespace so that you can start using your new cluster without first creating a namespace. Unless a namespace is specified when creating a resource Kubernetes assumes the default namespace. As a result users will deploy their resources in Default Namespace and can make potentially malicious changes to running applications in the default namespace.
ContainerLogV2
| where TimeGenerated > ago (1h)
| where LogSource == “stdout”
| where PodNamespace == “default”
| extend ContainerHostName1 = tostring(LogMessage.hostname)
| join ContainerInventory on $left.ContainerHostName1 == $right.ContainerHostname
| summarize dcount(Image) by ContainerHostname, Repository, Image
| project ContainerHostname, Repository, Image
Conclusion
In this document we showed you:
How to set up Azure Sentinel to monitor security risks in Azure Kubernetes Services (AKS) clusters. It also discusses the container security risks and how Microsoft Defender for Cloud addresses them.
Provide you a map of 32 container risks and how Microsoft Defender for Cloud alerts and Azure Policies provide a great coverage. It covers the areas of pod security, network security, container image security, kubelet activity, API server security, RBAC monitoring, secrets and ConfigMap access, audit logging, compliance monitoring, container runtime security, and incident response and forensics.
Showed you how to configure your environment to monitor AKS. The data connectors to ingest AKS data, setting up the diagnostic settings for the AKS cluster and enabling Container Insights to get the pod level data. Showed you how to enable the AKS Connector from Content Hub, which provides a workbook, hunting queries, and a data connector.
We show how to use the out-of-the-box workbook that comes with the AKS Connector. The workbook helps to understand the AKS cluster coverage, the security state, the security alerts, and the security recommendations. It also provides filters and drill-downs for further analysis.
Provide some examples of custom search queries that can be used to mine the log tables for more pressing risks. The queries can help to identify unauthorized or suspicious pods, privilege escalation attempts, changes to pod security policies, unexpected network traffic patterns, unauthorized access to secrets, and more.
Microsoft Tech Community – Latest Blogs –Read More