Tag Archives: microsoft
Autofill feature
Hi,
I am trying to fill a column on a spreadsheet with over 2,000 rows. Is there a way to auto fill the column efficiently? I just need to fill the column on this specific table, not the entire worksheet.
Hi, I am trying to fill a column on a spreadsheet with over 2,000 rows. Is there a way to auto fill the column efficiently? I just need to fill the column on this specific table, not the entire worksheet. Read More
Pictionary on Microsoft Teams
We want to play Pictionary on Microsoft Teams. I want to know, is there a built-in feature for this game in the Teams desktop version?
Thank you.
We want to play Pictionary on Microsoft Teams. I want to know, is there a built-in feature for this game in the Teams desktop version?Thank you. Read More
Setting up Sentinel for Kubernetes Monitoring
A guide to using Microsoft Sentinel for monitoring the security of your containerized applications and orchestration platforms.
Part 3 of 3 part series about security monitoring of your Kubernetes Clusters and CI/CD pipelines by @singhabhi and @Umesh_Nagdev , Security GBB
Link to Part 1
Link to Part 2
Introduction
In part 1 and part 2 of this series, we discussed the type of log sources you should consider for monitoring the security of your Kubernetes environment, most pertinent risks (and corresponding use cases) in your AKS environment, and log sources to ingest data. This blog will demonstrate how to configure Azure Sentinel to derive identify the risks.
More specifically we will show:
Mapping of container security risks with Microsoft Defender for Cloud
Data connectors to ingest AKS data
Container Security Workbooks in Sentinel
Search queries to mine specific log tables for more pressing risks
How Microsoft Defender for Cloud addresses container risks
Microsoft Defender for Containers is a security solution designed specifically for containerized environments. Microsoft Defender for Containers provides several key capabilities to enhance container security:
Real-time protection: Defender for Containers offers real-time protection by continuously monitoring container activities, network traffic, and system events. It uses machine learning algorithms and heuristics to detect and respond to potential threats promptly.
Vulnerability management: The solution helps identify vulnerabilities in container images and runtime environments. It can scan container images for known vulnerabilities, misconfigurations, and insecure dependencies, allowing organizations to address these issues before deploying containers into production.
Malware detection: Defender for Containers can detect and block malicious code, malware, and suspicious activities within containers. It leverages signature-based detection, behavioral analysis, and sandboxing techniques to identify and mitigate threats.
File integrity monitoring: The solution includes file integrity monitoring capabilities to detect unauthorized changes or tampering within containerized environments. It monitors critical system files, configuration files, and application binaries for any suspicious modifications.
Network security: Defender for Containers helps secure container network traffic by enforcing access controls, segmenting network traffic, and detecting anomalies or suspicious network behavior. It can detect and block malicious network activities, such as port scanning, denial-of-service attacks, and lateral movement attempts.
Integration with Azure Security Center: Defender for Containers integrates seamlessly with Azure Security Center, providing centralized visibility, monitoring, and management of container security across hybrid and multi-cloud environments. It leverages Azure’s cloud-native security capabilities and threat intelligence to enhance container security posture.
Incident response and remediation: In case of security incidents or suspicious activities, Defender for Containers provides tools for incident investigation, threat hunting, and automated remediation actions. It helps security teams quickly respond to security incidents and mitigate potential risks.
There are several alerts https://learn.microsoft.com/en-us/azure/defender-for-cloud/alerts-reference#alerts-for-containers—kubernetes-clusters that you get out of the box.
Additionally, you can secure the Kubernetes Control Plane using Azure Policy (https://learn.microsoft.com/en-us/azure/aks/use-azure-policy).
This resource https://techcommunity.microsoft.com/t5/microsoft-defender-for-cloud/leveraging-defender-for-containers-to-simplify-policy-management/ba-p/3755757 provides additional background on how Azure Policies work to protect your Kubernetes Control Plane.
There are several out of the box policies that can quickly get you started https://learn.microsoft.com/en-us/azure/aks/policy-reference
The table below shows a mapping of container risks to MDC alerts and Azure Policies. You will see that with the help of Defender for Containers you will get a great coverage across several risks that we discussed in blog part 2
#
Kubernetes Risk
Risk Area
MDC Alert(s)
Azure Policy(s)
1
Detect unauthorized or suspicious pods running in the cluster.
Pod Security Monitoring
Attempt to create a new Linux namespace from a container detected
Anomalous pod deployment (Preview)
Anomalous secret access (Preview)
Behavior similar to common Linux bots detected (Preview)
Command within a container running with high privileges
Container running in privileged mode
Container with a sensitive volume mount detected
Kubernetes cluster containers should only pull images when image pull secrets are present
Kubernetes cluster containers CPU and memory resource limits should not exceed the specified limits
Kubernetes cluster containers should only use allowed capabilities
Kubernetes cluster containers should only use allowed images
Kubernetes cluster containers should only use allowed pull policy
Kubernetes cluster containers should run with a read only root file system
Kubernetes cluster pod hostPath volumes should only use allowed host paths
Kubernetes cluster pods and containers should only run with approved user and group IDs
2
Monitor for privilege escalation attempts within pods.
Pod Security Monitoring
Attempt to create a new Linux namespace from a container detected
Anomalous secret access (Preview)
Command within a container running with high privileges
Container running in privileged mode
Container with a sensitive volume mount detected
Detected file download from a known malicious source
Excessive role permissions assigned in Kubernetes cluster (Preview)
Privileged container detected
Kubernetes cluster containers should only pull images when image pull secrets are present
Kubernetes cluster containers CPU and memory resource limits should not exceed the specified limits
Kubernetes cluster containers should only use allowed capabilities
Kubernetes cluster containers should only use allowed images
Kubernetes cluster containers should only use allowed pull policy
Kubernetes cluster containers should run with a read only root file system
Kubernetes cluster pod hostPath volumes should only use allowed host paths
Kubernetes cluster pods and containers should only run with approved user and group IDs
3
Track and alert on changes to pod security policies.
Pod Security Monitoring
None
None
4
Identify and alert on unexpected network traffic patterns.
Network Security Monitoring
An uncommon connection attempt detected
CoreDNS modification in Kubernetes detected
K8S API requests from proxy IP address detected
Potential reverse shell detected
Potential port forwarding to external IP address
Suspicious use of DNS over HTTPS
None
5
Monitor for unauthorized ingress and egress traffic.
Network Security Monitoring
An uncommon connection attempt detected
CoreDNS modification in Kubernetes detected
K8S API requests from proxy IP address detected
Potential reverse shell detected
Potential port forwarding to external IP address
Suspicious use of DNS over HTTPS
None
6
Detect and investigate potential denial-of-service (DoS) attacks.
Network Security Monitoring
Indicators associated with DDOS toolkit detected
None
7
Scan container images for vulnerabilities before deployment.
Container Image Security
None (Gating when released)
Scanning is automatically done as part of ACR
Running container images should have vulnerability findings resolved
Running container images should have vulnerability findings resolved (powered by Microsoft Defender Vulnerability Management)
8
Monitor for unauthorized or unsigned images.
Container Image Security
None
Kubernetes cluster containers should only use allowed images
Kubernetes clusters should only use images signed by notation
[Preview]: Deploy Image Integrity on Azure Kubernetes Service
9
Track changes to container image repositories.
Container Image Security
None
Configure container registries to disable anonymous authentication
Configure container registries to disable ARM audience token authentication.
Configure container registries to disable local admin account.
Container registries should be encrypted with a customer-managed key
Container registries should have anonymous authentication disabled.
10
Monitor kubelet logs for signs of compromise or unauthorized access.
Kubelet Activity Monitoring
Possible credential access tool detected
Abnormal Kubernetes service account operation detected
Anomalous secret access (Preview)
Creation of admission webhook configuration detected
None
11
Detect abnormal activities related to node management.
Kubelet Activity Monitoring
“K8S.NODE_” Alerts
[Preview]: Cannot Edit Individual Nodes
[Preview]: Kubernetes clusters should restrict creation of given resource type
Azure Kubernetes Clusters should enable Container Storage Interface(CSI)
Azure Kubernetes Clusters should enable Key Management Service (KMS)
Azure Kubernetes Clusters should use Azure CNI
Azure Kubernetes Service Clusters should enable node os auto-upgrade
Azure Role-Based Access Control (RBAC) should be used on Kubernetes Services
Both operating systems and data disks in Azure Kubernetes Service clusters should be encrypted by customer-managed keys
Configure Node OS Auto upgrade on Azure Kubernetes Cluster
Deploy Azure Policy Add-on to Azure Kubernetes Service clusters
Kubernetes cluster containers CPU and memory resource limits should not exceed the specified limits
Kubernetes clusters should not allow container privilege escalation
Kubernetes clusters should not allow endpoint edit permissions of ClusterRole/system:aggregate-to-edit
Kubernetes clusters should not grant CAP_SYS_ADMIN security capabilities
Kubernetes clusters should use internal load balancers
12
Monitor Kubernetes API server logs for suspicious activities.
API Server Security
“K8S_*” Alerts
None
13
Track and alert on failed authentication attempts.
API Server Security
AKS clusters should be set up to use Azure AD Authentication
https://techcommunity.microsoft.com/t5/fasttrack-for-azure/azure-kubernetes-service-rbac-options-in-practice/ba-p/3684275
Azure Kubernetes Service Clusters should enable Microsoft Entra ID integration
14
Detect unusual API server request patterns.
API Server Security
“K8S_*” Alerts
None
15
Monitor changes to RBAC policies and roles.
RBAC (Role-Based Access Control) Monitoring
Role binding to the cluster-admin role detected
AKS clusters should be set up to use Azure AD Authentication
https://techcommunity.microsoft.com/t5/fasttrack-for-azure/azure-kubernetes-service-rbac-options-in-practice/ba-p/3684275
Azure Kubernetes Service Clusters should enable Microsoft Entra ID integration
16
Detect and alert on unauthorized access attempts.
RBAC (Role-Based Access Control) Monitoring
Role binding to the cluster-admin role detected
AKS clusters should be set up to use Azure AD Authentication
https://techcommunity.microsoft.com/t5/fasttrack-for-azure/azure-kubernetes-service-rbac-options-in-practice/ba-p/3684276
Azure Kubernetes Service Clusters should enable Microsoft Entra ID integration
17
Track role binding changes and escalations.
RBAC (Role-Based Access Control) Monitoring
Role binding to the cluster-admin role detected
Kubernetes clusters should minimize wildcard use in role and cluster role
18
Monitor for unauthorized access to Kubernetes secrets and ConfigMaps.
Secrets and ConfigMap Access Monitoring
Anomalous secret access (Preview)
Process seen accessing the SSH authorized keys file in an unusual way
Defender for Key Vault also detects unusual access patterns
None
19
Detect changes to sensitive configuration data.
Secrets and ConfigMap Access Monitoring
None
Should be using Key Vault for Sensitive Data
Defender for Key Vault also detects unusual access patterns
None
20
Track usage patterns of sensitive information.
Secrets and ConfigMap Access Monitoring
None
Should be using Key Vault for Sensitive Data
Defender for Key Vault also detects unusual access patterns
None
21
Enable and monitor Kubernetes audit logs for cluster-wide activities.
Audit Logging
A history file has been cleared
Kubernetes events deleted
Possible Log Tampering Activity Detected
Deploy – Configure diagnostic settings for Azure Kubernetes Service to Log Analytics workspace
22
Correlate audit logs to identify security events and policy violations.
Audit Logging
Done natively by Defender for Container alerts
Deploy – Configure diagnostic settings for Azure Kubernetes Service to Log Analytics workspace
23
Regularly review audit logs for anomalies and potential threats.
Audit Logging
Not applicable
Not applicable
24
Ensure compliance with security standards and policies.
Compliance Monitoring
Defender for CSPM Regulatory Recommendations
None
25
Monitor for deviations from security best practices.
Compliance Monitoring
Defender for CSPM Regulatory Recommendations
None
26
Generate reports on compliance status and potential risks.
Compliance Monitoring
Defender for CSPM Regulatory Recommendations
None
27
Monitor runtime activities of containers for abnormal behavior.
Container Runtime Security
“K8S_*” Alerts
None
28
Detect and alert on suspicious system calls within containers.
Container Runtime Security
“K8S_*” Alerts
None
29
Integrate with container runtime security tools for enhanced monitoring.
Container Runtime Security
“K8S_*” Alerts
None
30
Develop and test incident response plans for Kubernetes security incidents.
Incident Response and Forensics
Not applicable
Not applicable
31
Monitor for indicators of compromise (IoCs) and initiate investigations.
Incident Response and Forensics
Done natively by Defender for Container alerts
Not applicable
32
Collect and analyze forensics data in the event of a security incident
Incident Response and Forensics
Done natively by Defender for Container alerts
Not applicable
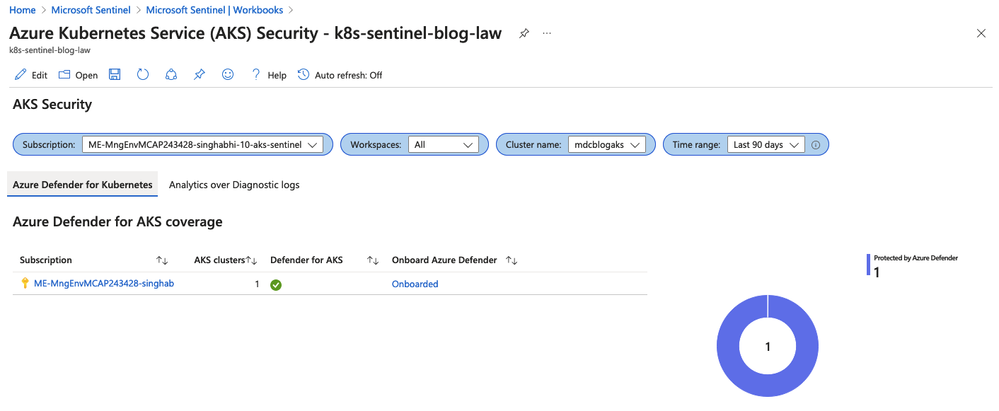
AKS Security Workbook
There is an out of the box work that you can enable once you deploy the AKS Connector from Content Hub. If you are not familiar with Sentinel workbooks please refer to this resource https://techcommunity.microsoft.com/t5/microsoft-sentinel-blog/azure-sentinel-workbooks-101-with-sample-workbook/ba-p/1409216 to learn about how to enable and leverage workbooks.
Let’s do a walkthrough of the AKS Security Workbook
Understanding the security coverage
As we showcased above, Defender for Cloud provides a great coverage for your container security related risks.
The first part would be to understand where you might have some blind spots that is the AKS clusters that are currently not being monitored by Defender for Cloud. The workbook allows you to look at the data across different subscriptions and the coverage table provides insights into where coverage is lacking.
Note: The is a drop down for selecting the Time Range so you can see the items like alerts, recommendations etc. for that time period.
Looking at the Overview of security alerts
For the given time period as we discussed earlier, you will see the security state of your clusters. This dashboard helps you understand where you have the most exposure across container image repos and clusters.
You can also see how alerts have changed over period of time.
Diving deeper into specific alerts
Now that we understand our AKS Cluster coverage and areas of risk exposures, this next section shows you security alerts that exists in your environment. This way you can quickly prioritize where it would make sense to start to close most gaps.
Search queries for security monitoring
In this section we will talk about building custom content to search for common use cases.
1. Identifying the Users and IPs who have most number of denies
You would want to understand who is trying to get situational awareness of your AKS environment. This can be an existing user or a script that’s trying to query your cluster.
//API Authorization Deny by User, Source IP
AKSAudit
| where TimeGenerated > ago (1h)
| extend authorizationDecision = parse_json(Annotations)
| extend user = parse_json(User)
| extend sourceIps = parse_json(SourceIps)
| project TimeGenerated, PodName, Verb, sourceIps[0],user.username, authorizationDecision[“authorization.k8s.io/decision”], RequestUri
| order by TimeGenerated asc
2. Users that are assigned to Cluster Roles
A ClusterRole can be used to grant the same permissions as a Role. Because ClusterRoles are cluster-scoped, you can also use them to grant access to:
cluster-scoped resources (like nodes)
non-resource endpoints (like /healthz)
namespaced resources (like Pods), across all namespaces
You should not assign users to cluster roles. The following query shows you the users are aligned to a Cluster Role
AKSAudit
| where TimeGenerated > ago (1h)
| where RequestObject.kind == “ClusterRoleBinding”
| where ResponseObject.subjects[0].name != “aks-support”
| project TimeGenerated, PodName, Verb, SourceIP=SourceIps[0],User=ResponseObject.subjects[0].name,ClusterRoleBinding=ResponseObject.metadata.name,ClusterRole=RequestObject.roleRef.name
| order by TimeGenerated asc
3. Users that have Admin Access
Users should not be part of system:masters and system:accounts. Any user who is a member of this group bypasses all RBAC rights checks and will always have unrestricted superuser access, which cannot be revoked by removing RoleBindings or ClusterRoleBindings.
//Users part of system:masters or Users that are part of system:accounts
AKSAudit
| where TimeGenerated > ago (1h)
| extend authorizationDecision = parse_json(Annotations)
| extend user = parse_json(User)
| extend sourceIps = parse_json(SourceIps)
| where user.groups[0] in (“system:masters”,”system:accounts”) or user.groups[1] in (“system:masters”,”system:accounts”)
| where user.username !in (“aksService”,”system:apiserver”,”aksProblemDetector”)
| project TimeGenerated, PodName, Verb, SourceIP=sourceIps[0],Username=user.username, AuthorizationDecision=authorizationDecision[“authorization.k8s.io/decision”], AuthorizationDecisionReason=authorizationDecision[“authorization.k8s.io/reason”], RequestUri
| order by TimeGenerated asc
4. Resources that can run unauthenticated and anonymous API calls
You would want to know who is part of system:unauthenticated group and remove them where possible, as this gives access to anyone who can contact the API server at a network level.
/Bindings of system:unauthenticated and system:anonymous group
AKSAudit
| where TimeGenerated > ago (1h)
| where PodName !startswith “kube-apiserver”
| extend authorizationDecision = parse_json(Annotations)
| extend user = parse_json(User)
| extend sourceIps = parse_json(SourceIps)
| extend ObjectRef = parse_json(ObjectRef)
| where user.groups[0] in (“system:unauthenticated”,”system:anonymous”) or user.groups[1] in (“system:unauthenticated”,”system:anonymous”)
| project TimeGenerated, PodName, Verb, Resource=ObjectRef.resource, SourceIP=sourceIps[0],Username=user.username, AuthorizationDecision=authorizationDecision[“authorization.k8s.io/decision”], AuthorizationDecisionReason=authorizationDecision[“authorization.k8s.io/reason”], RequestUri
| order by TimeGenerated asc
5. Users that are trying to get secrets
There are not many common use cases where a user is getting Kubernetes secrets.
//Users that have executed ‘kubectl get secrets’
AKSAudit
| where TimeGenerated > ago (1h)
| where Verb == “get”
| extend authorizationDecision = parse_json(Annotations)
| extend user = parse_json(User)
| extend sourceIps = parse_json(SourceIps)
| extend ObjectRef = parse_json(ObjectRef)
| where ObjectRef.resource == “secrets”
| where user.username !startswith “system:serviceaccount”
| project TimeGenerated, PodName, Verb, SourceIP=sourceIps[0],Username=user.username, AuthorizationDecision=authorizationDecision[“authorization.k8s.io/decision”], AuthorizationDecisionReason=authorizationDecision[“authorization.k8s.io/reason”], RequestUri
| order by TimeGenerated asc
6. Users that are trying to bind to Cluster Admin roles
Like we discussed above Cluster Admin roles should be used sparingly. You would want to know who is trying to bind to Cluster Roles
//Users that have executed Cluster Role Binding on cluster admin
AKSAudit
| where TimeGenerated > ago (1h)
| where Verb == “create”
| extend authorizationDecision = parse_json(Annotations)
| extend user = parse_json(User)
| extend sourceIps = parse_json(SourceIps)
| extend ObjectRef = parse_json(ObjectRef)
| where user.username != “aksService”
| where ObjectRef.resource startswith “clusterrole”
| project TimeGenerated, PodName, Verb, Resource=ObjectRef.resource, SourceIP=sourceIps[0],Username=user.username, AuthorizationDecision=authorizationDecision[“authorization.k8s.io/decision”], AuthorizationDecisionReason=authorizationDecision[“authorization.k8s.io/reason”], RequestUri
| order by TimeGenerated asc
7. Pods that are in default namespace
In Kubernetes, namespaces provides a mechanism for isolating groups of resources within a single cluster. Namespaces are a way to divide cluster resources between multiple users. Kubernetes includes the default namespace so that you can start using your new cluster without first creating a namespace. Unless a namespace is specified when creating a resource Kubernetes assumes the default namespace. As a result users will deploy their resources in Default Namespace and can make potentially malicious changes to running applications in the default namespace.
ContainerLogV2
| where TimeGenerated > ago (1h)
| where LogSource == “stdout”
| where PodNamespace == “default”
| extend ContainerHostName1 = tostring(LogMessage.hostname)
| join ContainerInventory on $left.ContainerHostName1 == $right.ContainerHostname
| summarize dcount(Image) by ContainerHostname, Repository, Image
| project ContainerHostname, Repository, Image
Conclusion
In this document we showed you:
How to set up Azure Sentinel to monitor security risks in Azure Kubernetes Services (AKS) clusters. It also discusses the container security risks and how Microsoft Defender for Cloud addresses them.
Provide you a map of 32 container risks and how Microsoft Defender for Cloud alerts and Azure Policies provide a great coverage. It covers the areas of pod security, network security, container image security, kubelet activity, API server security, RBAC monitoring, secrets and ConfigMap access, audit logging, compliance monitoring, container runtime security, and incident response and forensics.
Showed you how to configure your environment to monitor AKS. The data connectors to ingest AKS data, setting up the diagnostic settings for the AKS cluster and enabling Container Insights to get the pod level data. Showed you how to enable the AKS Connector from Content Hub, which provides a workbook, hunting queries, and a data connector.
We show how to use the out-of-the-box workbook that comes with the AKS Connector. The workbook helps to understand the AKS cluster coverage, the security state, the security alerts, and the security recommendations. It also provides filters and drill-downs for further analysis.
Provide some examples of custom search queries that can be used to mine the log tables for more pressing risks. The queries can help to identify unauthorized or suspicious pods, privilege escalation attempts, changes to pod security policies, unexpected network traffic patterns, unauthorized access to secrets, and more.
Microsoft Tech Community – Latest Blogs –Read More
Introducing the Microsoft Purview Audit Search Graph API
Microsoft Purview Audit provides an integrated solution to help organizations effectively respond to security incidents, forensic investigations, internal investigations, and compliance obligations.
Thousands of user and admin operations performed in dozens of Microsoft 365 services and solutions are captured, recorded, and retained in your organization’s unified audit log. Audit records for these events are searchable by security ops, IT admins, insider risk teams, and compliance and legal investigators in your organization. This capability provides visibility into the activities performed across your Microsoft 365 organization.
Today, we are excited to announce the upcoming launch of the Microsoft Purview Audit Search Graph API, a new capability that is currently in Public Preview and will be Generally Available by June 2024. With this release, Microsoft Purview Audit will offer a new API available through Microsoft Graph to programmatically search and retrieve relevant audit logs with improvements in search completeness, reliability, and performance. This API serves as an improved alternative to the existing PowerShell cmdlet, Search-UnifiedAuditLog.
What are the advantages of using this new API over the existing Search-UnifiedAuditLog cmdlet?
Microsoft Graph offers a single endpoint to provide access to rich data and insights across the Microsoft ecosystem. The Microsoft Audit Search Graph API is designed to provide a more efficient and reliable way to search audit logs, making it easier for customers and partners to monitor and investigate security incidents. With this new feature, users can expect faster search times, more complete search results, and a more robust and reliable search experience.
Highlights of the API with improvements over the existing Search-UnifiedAuditLog cmdlet are listed below:
The API offers an asynchronous Audit search experience with support for automation – accessible by both users and applications
A more reliable Audit search experience with fewer timeouts and improved search completeness
New granular permissions have been introduced for the Audit workloads (Exchange, Entra, OneDrive, SPO, Intune, CRM) which allow you to grant workload-scoped access to your security admins for the very first time
Ability to programmatically filter Audit logs using 10 parameters with 4 new filter options to be added soon
New granular permissions
The new API allows you to scope access to Audit logs at a workload level for the very first time. The following seven permissions have been introduced:
Microsoft 365 service
Permission string
Microsoft OneDrive
AuditLogsQuery-OneDrive.Read.All
Microsoft Exchange
AuditLogsQuery-Exchange.Read.All
Microsoft SharePoint
AuditLogsQuery-SharePoint.Read.All
Microsoft Intune
AuditLogsQuery-Endpoint.Read.All
Microsoft Dynamics CRM
AuditLogsQuery-CRM.Read.All
Microsoft Entra
AuditLogsQuery-Entra.Read.All
All Audit Logs
AuditLogsQuery.Read.All
Get Started
Explore how to use the API by referring to the API documentation available here.
The Audit Search Graph API is currently in Public Preview and is planned to be Generally Available by June 2024.
We encourage existing users of the Search-UnifiedAuditLog cmdlet to switch over to the new Audit Search Graph API to take advantage of these improvements. This new API will provide a better overall experience for our customers and partners and help effectively monitor and protect their environments.
There is an easy way for eligible customers to try Microsoft Purview solutions directly in the Microsoft Purview compliance portal with a free trial. By enabling the trial in the compliance portal, you can quickly start using all capabilities of Microsoft Purview, including Insider Risk Management, Records Management, Audit, eDiscovery, Communication Compliance, Information Protection, Data Lifecycle Management, Data Loss Prevention, and Compliance Manager.
Microsoft Tech Community – Latest Blogs –Read More
MVP’s Favorite Content: GenAI, D365, Semantic Kernel, Learn
In this blog series dedicated to Microsoft’s technical articles, we’ll highlight our MVPs’ favorite article along with their personal insights.
Yoshitaka Seo, AI MVP, Japan
“This is a collection about the Azure OpenAI Service. You can learn in sequence about how to use the playground, prompt engineering, how to integrate OpenAI into applications with C# or Python, and generating images and code. Please learn everything from the basics to practical content of OpenAI through explanations and exercises in each module.”
(In Japanese: Azure OpenAI Serviceについてのコレクションです。プレイグラウンドの使い方、プロンプトエンジニアリング、C#やPythonでOpenAIをアプリケーションに統合する方法、画像やコードの生成を順に学べます。それぞれのモジュールの解説と演習とを通してOpenAIの基本から実用的な内容まで学習してください。)
*Relevant Activity: ChatGPTからCopilotまで最新のAIを語ろう – Global AI Bootcamp – connpass
Parag Chapre, Business Applications MVP, Australia
Set up the components of a job – Human Resources | Dynamics 365 | Microsoft Learn
“I highly recommend exploring the content on “Generating Job Descriptions Using AI in Dynamics 365 Human Resources” for several compelling reasons. Firstly, in today’s fast-paced business landscape, efficiency is paramount. With AI-driven solutions embedded in Dynamics 365 Human Resources, the process of crafting job descriptions is streamlined, saving valuable time and resources for HR professionals. Secondly, the use of AI ensures accuracy and consistency in job descriptions, minimizing errors and discrepancies that may arise from manual input.
Moreover, leveraging AI technology enables organizations to create tailored job descriptions that align with evolving industry trends and organizational needs, ultimately attracting top talent and enhancing recruitment outcomes. Additionally, by automating the job description generation process, HR teams can focus their efforts on more strategic initiatives, such as talent development and retention.
Furthermore, the integration of AI in Dynamics 365 Human Resources empowers HR professionals with valuable insights derived from data analytics, enabling them to make data-driven decisions and optimize workforce planning. Overall, exploring this content provides valuable insights into leveraging AI technology to revolutionize the job description creation process, ultimately driving efficiency, accuracy, and strategic HR outcomes within organizations.”
*Relevant Blog: Generating Job Descriptions Using AI in Dynamics 365 Human Resources – Parag Chapre
Tomomitsu Kusaba, Developer Technologies MVP, Japan
semantic-kernel/dotnet/notebooks at main · microsoft/semantic-kernel (github.com)
“To start with Semantic Kernel, I recommend starting with this content. By learning this content thoroughly, you can grasp an overview of Semantic Kernel.”
(In Japanese: Semantic Kernelを始めるにあたってまずはおすすめのコンテンツ。これを一通り学習することによってSemantic Kernelの概要をつかむことができます。)
Sergio Parra Guerra, Microsoft Azure MVP, Spain
“All training in Microsoft products and certifications is essential to stay up to date with the latest technologies. Always learning!”
(In Spanish: Toda la formación en productos Microsoft y Certificaciones, esencial para estar siempre reciclado en las últimas tecnologías. Always learning!)
Microsoft Tech Community – Latest Blogs –Read More
Unlocking industrial data for AI: Microsoft partners with leading connectivity providers
Microsoft is partnering with leading industrial connectivity partners Advantech, PTC, and Softing to unlock industrial data for AI and accelerate digital transformation for industrial customers leveraging Azure IoT Operations through Azure’s adaptive cloud approach.
We are committed to empowering customers to achieve more with their data and unlocking new insights and opportunities across the industrial ecosystem. This includes overcoming the challenges of proprietary interfaces and data models from an array of industrial assets on the factory floor. We believe that the key to addressing those challenges is enabling data to flow consistently and securely to the people and places where it’s needed to drive collaboration and better decision-making, leveraging open standards like OPC UA and MQTT. This is why we are working closely with our connectivity partners, who play a vital role in bridging the gap between legacy or proprietary assets and our standardized edge interfaces. They provide data translation and normalization to open, standardized data models across heterogeneous environments.
The adaptive cloud approach brings just enough Azure and its capabilities to any environment, from the factory floor to both 1st party and 3rd party cloud infrastructure, using Kubernetes and other open technologies. We enable interoperability and integration across diverse edge devices and applications, providing a single control and management plane using Azure IoT Operations (Preview), enabled by Azure Arc. We aim to unify siloed teams, distributed sites, and sprawling systems and to provide our customers with an open, interoperable, and secure Industrial IoT platform that can scale to meet their current and future needs quickly.
We are leveraging leading solutions from our connectivity partners Advantech, PTC, and Softing to achieve the necessary frictionless data flow that our customers need. Each connectivity partner is integrated with Azure IoT Operations to enable data interoperability and management across the industrial edge and cloud.
Advantech is a leader in Industrial IoT, providing comprehensive system integration, hardware, software, and customer-centric design services. Their iFactory solution offers device-to-cloud visibility and a strong hardware-led connectivity story. Advantech has integrated their iFactory solution with Azure IoT Operations, enabling data flow from their edge devices and applications to Azure. They are also exploring to build an Akri connector for LoRaWAN, enabling an integration with Azure Resource Manager and benefiting from Azure’s security, monitoring, and management features.
“Azure IoT Operations offers a highly flexible approach to swiftly onboard IoT assets within the same network hierarchy. Data from devices can be easily captured using Akri discovery plugins and visualized in Grafana for user consumption. With the Azure AIO solution stack, our customers can seamlessly transition to a digital operational environment with success.”
– Ihen Tsai, Product Manager of WISE-iFactory, Advantech
PTC Kepware is a premier provider of industrial connectivity software, and their solutions access data from virtually any device – legacy or modern – and seamlessly and securely move the data to other OT and IT software applications. Their flagship product, Kepware+, enables secure and reliable data transfer between industrial assets and Azure IoT Operations, leveraging MQTT and OPC UA. Customers can ingest, process, and publish OPC UA data to services such as Azure Data Explorer or Microsoft Fabric, and can leverage Microsoft’s AI capabilities.
“PTC is proud of our long collaboration with Microsoft to accelerate digital transformation for industrial companies with our portfolio of manufacturing solutions. The announcement of Azure IoT Operations marks a significant milestone in empowering companies to leverage data for innovation and heightened efficiency. Together, PTC Kepware+ and Azure IoT Operations seamlessly and securely integrate to access, normalize, and process asset data at the edge and derive insights in the cloud.”
– Ted Kerkam, Senior Director of Product Strategy, PTC Kepware
Softing is a leading provider of industrial connectivity. Their edgeConnector, edgeAggregator and dataFEED OPC Suite family of products offer access to process and machine data in PLCs from various vendors such as Siemens, Rockwell, Schneider, Beckhoff, Mitsubishi, Fanuc, Omron, and more. Softing has integrated their connectivity product portfolio with Azure IoT Operations, enabling data flow from OT assets via open standards OPC UA and MQTT. This allows customers to send their asset data to services such as Azure Data Explorer or Microsoft Fabric, and they can leverage Microsoft’s AI capabilities.
“Our customers require standards-based and scalable machine connectivity for their Industrial IoT solutions. Microsoft’s adaptive cloud approach supports Kubernetes, MQTT and OPC UA on edge level, so we can offer a seamless integration of our dataFEED products into the Azure platform meeting our customers’ critical requirements regarding connectivity and efficient operation.”
– Thomas Hilz, Managing Director at Softing Industrial Automation GmbH
Engage with Microsoft on our adaptive cloud approach and data connectivity
We believe when working together across a robust partner ecosystem, Microsoft can deliver the best possible solutions to our customers and help them realize the full potential of their data across the industrial edge and cloud. We are also committed to supporting open standards and protocols and providing a single management and control plane, to enable a seamless and secure data flow from assets to the cloud.
To learn more, visit the Microsoft booth at Hannover Messe (Hall 17, Stand G06) from April 22-26. We invite you to come see us and our partners, and we will be showcasing our connectivity partner solutions. You can learn more about our adaptive cloud approach and discuss your Industrial IoT opportunities with our experts.
We hope to see you there!
Microsoft Tech Community – Latest Blogs –Read More
Correct Board for T-SQL??
Is this the correct board for asking T-SQL questions?? I have a complex query, which I think could be simplified. I posted it on Stack Overflow and the moderators closed it because it was an “opinion question and did not involve facts”.
Is this the correct board for asking T-SQL questions?? I have a complex query, which I think could be simplified. I posted it on Stack Overflow and the moderators closed it because it was an “opinion question and did not involve facts”. Read More
Resolving AADB2C90205 error during immediate sign-in with new Azure B2C App Registration
We are developing a multi-tenant application where users can request new business tenants through the main domain by specifying a subdomain for each. We use Graph API to automate the creation of specific App Registrations in Azure AD B2C for each tenant’s subdomain.
After the App Registration is created, attempting an immediate sign-in with Azure B2C results in a failure with the following error:
https://webuilduat.b2clogin.com/webuilduat.onmicrosoft.com/b2c_1_susi/oauth2/v2.0/token 400 (Bad Request) “AADB2C90205: This application does not have sufficient permissions against this web resource to perform the operation.”
This error persists until about 30 minutes post-creation, after which sign-in functions normally. We ensure that all required scopes are correctly configured in the App Registration. This delay leads us to suspect issues with resource propagation.
What causes the AADB2C90205 error specifically when attempting immediate sign-ins post-App Registration creation?
Are there known strategies to mitigate this delay or expedite the propagation process so that authentication becomes promptly available after creating a new App Registration?
Your insights on this would be greatly appreciated as they could significantly improve our application’s user experience by reducing wait times for new tenant setups.
We are developing a multi-tenant application where users can request new business tenants through the main domain by specifying a subdomain for each. We use Graph API to automate the creation of specific App Registrations in Azure AD B2C for each tenant’s subdomain.After the App Registration is created, attempting an immediate sign-in with Azure B2C results in a failure with the following error:https://webuilduat.b2clogin.com/webuilduat.onmicrosoft.com/b2c_1_susi/oauth2/v2.0/token 400 (Bad Request) “AADB2C90205: This application does not have sufficient permissions against this web resource to perform the operation.”This error persists until about 30 minutes post-creation, after which sign-in functions normally. We ensure that all required scopes are correctly configured in the App Registration. This delay leads us to suspect issues with resource propagation.What causes the AADB2C90205 error specifically when attempting immediate sign-ins post-App Registration creation?Are there known strategies to mitigate this delay or expedite the propagation process so that authentication becomes promptly available after creating a new App Registration?Your insights on this would be greatly appreciated as they could significantly improve our application’s user experience by reducing wait times for new tenant setups. Read More
On prem domain – AD Connect Writeback to enable Intune/Defender and increased ASM
We are a small financial institution and are looking to increase our security. Our on prem domain and on prem servers are not moving to cloud, but we are looking to strengthen our endpoint security for a hybrid workforce. Intune and Defender for Endpoint offers a lot of what we need, and we have to upgrade to Microsoft E3/E5 anyway to meet audit requirement for Mobile Application Management anyway.
In order to be able to access on premise printers and file shares, I need to enable password and device writeback in our AD Connect and change our hybrid joined devices to Azure domain joined. This seems to increase our attack surface and ASM. We do not have a website so our current lack of attack surface is an asset. We are concerned with opening our attack surface, but I believe the addition of the capabilities of Intune and Defender for endpoint are worth the increased attack surface.
1. Am I correct in this assessment that the reward is worth the risk?
2. What can I do to lock down the attack surface so we don’t have external attacks on our on premise assets or our accounts via O365?
We are a small financial institution and are looking to increase our security. Our on prem domain and on prem servers are not moving to cloud, but we are looking to strengthen our endpoint security for a hybrid workforce. Intune and Defender for Endpoint offers a lot of what we need, and we have to upgrade to Microsoft E3/E5 anyway to meet audit requirement for Mobile Application Management anyway. In order to be able to access on premise printers and file shares, I need to enable password and device writeback in our AD Connect and change our hybrid joined devices to Azure domain joined. This seems to increase our attack surface and ASM. We do not have a website so our current lack of attack surface is an asset. We are concerned with opening our attack surface, but I believe the addition of the capabilities of Intune and Defender for endpoint are worth the increased attack surface.1. Am I correct in this assessment that the reward is worth the risk?2. What can I do to lock down the attack surface so we don’t have external attacks on our on premise assets or our accounts via O365? Read More
0x80070422 cant log in to insider program
windows 11 23h2 cant log into my insider account, says 0x80070422
windows 11 23h2 cant log into my insider account, says 0x80070422 Read More
Azure USBX hub issues with full speed devices
We have a project using Azure USBX with a STM32H7 processor and a Microchip 2514 USB HUB.
The STM hcd driver is initialized and the software initializes UsbX support for a hub, multiple CDC ACMs, a HID Keyboard and MSC devices. All the devices can be discovered and work as expected.
There is an issue when a FULL SPEED device (CDC ACM and HID Keyboard) is unplugged and then plugged back in again causes the USB bus to become unresponsive. The only current solution is to reset the USB2514 Hub.
Has anybody seen this or have any suggestions?
We have a project using Azure USBX with a STM32H7 processor and a Microchip 2514 USB HUB. The STM hcd driver is initialized and the software initializes UsbX support for a hub, multiple CDC ACMs, a HID Keyboard and MSC devices. All the devices can be discovered and work as expected. There is an issue when a FULL SPEED device (CDC ACM and HID Keyboard) is unplugged and then plugged back in again causes the USB bus to become unresponsive. The only current solution is to reset the USB2514 Hub. Has anybody seen this or have any suggestions? Read More
Removal of LIcence “Phone System” with Powershell
Hello
I would like to remove a “Microsoft 365-Telefonsystem” (E5 or E3 with Powershell.
Is it possible. Using this information Assign Teams add-on licenses to users – Microsoft Teams | Microsoft Learn would remove the whole E5
but I just want to remove “Phone System”
How do I do that with Powershell
Regards
JFM_12
Hello I would like to remove a “Microsoft 365-Telefonsystem” (E5 or E3 with Powershell.Is it possible. Using this information Assign Teams add-on licenses to users – Microsoft Teams | Microsoft Learn would remove the whole E5 but I just want to remove “Phone System”How do I do that with PowershellRegardsJFM_12 Read More
Do you know how to convert binary numbers to decimal?
It’s easy with the BIN2DEC function, but there’s a limitation and an easy way to make a mistake and get a wrong result. The limitation is that it can’t convert a number with more than 10 bits. If you try, it will give an error. There’s also an easy way to make a mistake. If you use numbers that have 10 bits, they may be converted to a negative number. For an explanation, you need to understand the “Two’s complement” method of representing binary integers.
I found this article by Excel MVP Frédéric LE GUEN, that provides a workaround to the 10 bit limitation of the BIN2DEC function:
Convert Binary Number to Decimal in Excel :keycap_0: :keycap_1: (excel-tutorial.com)
It’s easy with the BIN2DEC function, but there’s a limitation and an easy way to make a mistake and get a wrong result. The limitation is that it can’t convert a number with more than 10 bits. If you try, it will give an error. There’s also an easy way to make a mistake. If you use numbers that have 10 bits, they may be converted to a negative number. For an explanation, you need to understand the “Two’s complement” method of representing binary integers. I found this article by Excel MVP Frédéric LE GUEN, that provides a workaround to the 10 bit limitation of the BIN2DEC function: Convert Binary Number to Decimal in Excel :keycap_0: :keycap_1: (excel-tutorial.com) Read More
Using Microsoft Project for the Web Built in Power Apps. New Project not adding Calendar id.
Hopefully my post is in the correct category. Tried posting this to Power Apps.
I am using Project for the Web
I am using the Microsoft Project Power Apps Model Driven App and have customized it out extensively for my companies use.
However I have seem to run into a bug when adding projects. I have already added 257 projects no issue. However now when adding new projects it will say “Calendar Id: Required fields must be filled in.” and I know how to unlock it to it’s not read only however in the past new projects would auto populate this information. Even when unlocked it doesn’t auto populate. Please Note: This field was previously hidden in the form view until I started receiving the error when trying to save new projects.
Also previously these fields on the form were hidden and I had never had to input this information before but I unhid them because I was also having an issue with the “hours per day” not being filled out. Again this hadn’t been an issue before.
Thanks.
Hopefully my post is in the correct category. Tried posting this to Power Apps. I am using Project for the Web I am using the Microsoft Project Power Apps Model Driven App and have customized it out extensively for my companies use. However I have seem to run into a bug when adding projects. I have already added 257 projects no issue. However now when adding new projects it will say “Calendar Id: Required fields must be filled in.” and I know how to unlock it to it’s not read only however in the past new projects would auto populate this information. Even when unlocked it doesn’t auto populate. Please Note: This field was previously hidden in the form view until I started receiving the error when trying to save new projects. Also previously these fields on the form were hidden and I had never had to input this information before but I unhid them because I was also having an issue with the “hours per day” not being filled out. Again this hadn’t been an issue before. Thanks. Read More
Mise à jour
Hello, I have my update which is stuck at 0%
we know how to help
Hello, I have my update which is stuck at 0%we know how to help Read More
Clearing an Intune configured Scheduled Reboot
Hello,
I set a daily reboot for all devices via Intune Device Config setting, which is great.
However the default ‘is to run task if missed’ ticked.
I have worked out how to deploy this with PS to untick this.
BUT i need to remove the old Intune Devcie Config reboot task – is there a way to do this?
I have looked at:
schtasks /Delete /TN “MicrosoftWindowsEnterpriseMgmt7930FBB0-6F88-4001-8B77-C35D67AE8960RebootRebootCSP daily recurrent reboot” /F
But the GUID is different per machine….. :
Intune documents says to replace it with a null value – im assuming that is: 0000-00-00T00:00:00Z
Any assistance appreciated!
Hello, I set a daily reboot for all devices via Intune Device Config setting, which is great. However the default ‘is to run task if missed’ ticked. I have worked out how to deploy this with PS to untick this. BUT i need to remove the old Intune Devcie Config reboot task – is there a way to do this? I have looked at: schtasks /Delete /TN “MicrosoftWindowsEnterpriseMgmt7930FBB0-6F88-4001-8B77-C35D67AE8960RebootRebootCSP daily recurrent reboot” /F But the GUID is different per machine….. : Intune documents says to replace it with a null value – im assuming that is: 0000-00-00T00:00:00Z Any assistance appreciated! Read More
Enable Copilot for Microsoft 365 FAST
Roll out Microsoft Copilot for Microsoft 365 at scale in three quick steps. See the methods for each to efficiently enable Copilot services:
1. Optimize Search with data controls in place to limit exposure of information in search.
2. Update Your Apps — both on desktop and mobile — so they are ready for integrated Copilot experiences.
3. Grant Access to Copilot services quickly to large groups in your organization via Microsoft Entra controls.
We’re also introducing a new capability with Restricted SharePoint Search, which enables SharePoint administrators to define the sites where every user in the organization is allowed to files and data using search, without impacting access to sites and files for people working in sites, which are not allowed for everyone to search.
With Copilot for Microsoft 365 services in place, track adoption and impact, and see how different groups in your organization are benefitting from Copilot services with the Microsoft Copilot Dashboard powered by Viva Insights. Now, even if you don’t currently own Viva Insights, there is an offer for Microsoft Copilot customers to get these services included with your Copilot subscription: https://www.microsoft.com/en-us/microsoft-365/blog/2024/04/11/enabling-your-ai-transformation-journey-with-microsoft-viva/
Update desktop and mobile apps on your managed devices.
Quick access to integrated Copilot for Microsoft 365 experiences. Check it out.
Grant access to Copilot services at scale to the right people in your organization.
Pro tip for assigning licenses at scale using Groups in Microsoft Entra. Get started.
New Restricted SharePoint Search option.
SharePoint administrators can define allowed sites available to everyone in search, including Copilot retrieval, microsoft365.com and in apps. Take a look.
Watch our video here:
QUICK LINKS:
00:00 — Steps to deploy Copilot for Microsoft 365
01:01 — How to quickly optimize search
02:24 — How to set up Restricted SharePoint Search
03:23 — Update Microsoft 365 apps on managed devices
05:34 — Grant access to Copilot services
06:20 — Copilot Dashboard included with any Microsoft 365 subscription
07:00 — Copilot Dashboard powered by Viva Insights subscription
08:38 — Wrap Up
Link References:
Get started at https://aka.ms/DeployCopilotforM365
Watch how to get ready for Copilot at https://aka.ms/CopilotSecurityMechanics
For more resources go to https://adoption.microsoft.com/copilot
Unfamiliar with Microsoft Mechanics?
As Microsoft’s official video series for IT, you can watch and share valuable content and demos of current and upcoming tech from the people who build it at Microsoft.
Subscribe to our YouTube: https://www.youtube.com/c/MicrosoftMechanicsSeries
Talk with other IT Pros, join us on the Microsoft Tech Community: https://techcommunity.microsoft.com/t5/microsoft-mechanics-blog/bg-p/MicrosoftMechanicsBlog
Watch or listen from anywhere, subscribe to our podcast: https://microsoftmechanics.libsyn.com/podcast
Keep getting this insider knowledge, join us on social:
Follow us on Twitter: https://twitter.com/MSFTMechanics
Share knowledge on LinkedIn: https://www.linkedin.com/company/microsoft-mechanics/
Enjoy us on Instagram: https://www.instagram.com/msftmechanics/
Loosen up with us on TikTok: https://www.tiktok.com/@msftmechanics
Video Transcript:
-Copilot for Microsoft 365 is here. And today, I’m going to walk through the three quickest steps to get everything up and running the way you want with your organization’s data. First by quickly optimizing search so that Copilot from Microsoft 365 only retrieves the data that you don’t mind all users seeing.
-Second, by updating your apps in both desktop and mobile devices, so they can get the latest Copilot experiences. And third, by granting access at scale to the right people in your organization. Once you’ve taken these steps, the advantage of Copilot for Microsoft 365 is that it has protections uniquely built in to respect the security and compliance policies you have in place for your data in Microsoft 365.
-Additionally, to manage your rollout, we give you full visibility to track deployment readiness as well as the apps in use with Copilot. And you can also get deep insights on how people across your organization may be benefiting from their Copilot for Microsoft 365 experience. So let’s now get into this starting with our first quick deployment step, how to quickly optimize search.
-As you interact with Copilot, search can be used as part of the Copilot grounding process, where relevant information in your organization can be discovered and used to ground the large language model to augment user prompts with more context in order to return more relevant results. Now, if your organization wants to scope or limit the discoverability of certain content, the fastest way to do this, with a new option called Restricted SharePoint Search.
-Now this helps you define and curate a list of sites allowed to work with organization-wide search, where everything else is restricted to prevent the over exposure of site content for information that might be sensitive. That way, Copilot will only retrieve SharePoint information from the sites that you’ve allowed.
-And users will see a message on their Copilot experiences advising them that certain sites have been restricted when responding to their prompts. And over time, as you right-size both site and file access, you can increase organization-wide information results at your pace. It’s worth noting that beyond Copilot for Microsoft 365, this approach also works across other SharePoint search experiences in Microsoft 365 and in apps to limit over exposure of information.
-And to be clear, individuals are still able to reference the sites and content that they already frequently work with. Let me show you how to set up Restricted SharePoint Search. This capability is initially rolling out with a SharePoint Online PowerShell set of cmdlets to define your allowed sites.
-Once you’ve connected to your tenant with admin permissions, you’ll run the Set-SPOTenantRestrictedSearchMode cmdlet with the -mode switch to enable it. And once it’s enabled, we’re ready to define our sites and there are two different options.
-The first option is to use a CSV file like this one where you can list up to 100 different sites in the first column then you can store this file on your local disk. And in PowerShell you’ll run the Add-SPOTenantRestrictedSearchAllowedList cmdlet with the -SitesListFileUrl switch and the path to your CSV file.
-Now from there you can use the get cmdlet to confirm your sites were added. Or another option is to use the SitesList switch using the @ symbol, then open parentheses, then all of your sites in quotes separated by commas, then close parentheses and you’re done.
-Then our next quick step is to update Microsoft 365 apps on your managed devices, and this applies to both desktop and mobile apps with integrated Copilot experiences. Let’s start with your desktop apps on Windows. So these need to be running either Monthly Enterprise Channel, Current Channel, or Current Channel Preview.
-Note Semi-Annual Enterprise Channel will not get integrated Copilot experiences. If you already have one of the supported update channels in place, then there’s nothing to do, you can skip to the next step. Otherwise, you can change to a supported update channel using any policy mechanism that leverages group policy ADMX templates for Office 2016 and newer with a simple policy.
-So I’ll show you this using Microsoft Intune, but the same settings are also available for Group Policy, Configuration Manager, and others. So I’m in Devices under Windows, and Configuration profiles and I’m going to add a new policy and choose Windows 10 and later. Then under Profile type, I’ll choose Templates, then Administrative templates, and I’m going to give it a name, Microsoft 365 Apps channel update.
-Then in Configuration Settings, the quickest way to find the right policy is just to search for update channel. And you’re going to see that there are two options. So I’m going to pick the option that’s called Update Channel . Then, like any other policy, you’ll enable it first, and by doing that it’s going to expose a dropdown and then you can choose any of the three options on top. Here, I’ll choose Monthly Enterprise Channel.
-Next, I’ll skip Scope tags. And, in my case, I’ll add all users for the groups in scope for this policy. And of course, you can scope the right groups for your case. From there, I just need to review and create, and that’s it, step two for Windows is done. Then for macOS, as long as you’re using Microsoft 365 apps for your managed macs you’re all set, they don’t have the same update channel options.
-Next, for your mobile devices running iOS and Android, if you already have the individual mobile apps, like you see here with iOS and iPadOS apps for Word, Excel, PowerPoint, or OneNote, you want to make sure that the Microsoft Copilot and Microsoft 365 apps are available. And just like you saw for iOS, the same is true for your managed Android devices.
-Now with steps one and two complete, you have the major prerequisites in place to move on to step three where you’ll grant access to Copilot services then, after you’ve acquired the licenses you need, aside from using things like PowerShell for bulk license assignments, one of the quickest ways to assign licenses to a large number of users is in the Microsoft Entra admin center, where using groups you can create the groups you need either manually or dynamically based on user attributes.
-Then for security or Microsoft 365 groups, directly from that group, you can navigate to Licenses, then Add new assignments and select Microsoft Copilot for Microsoft 365 and save and that’s it. And with that, our three step quick deployment is complete.
-And as your users start to use Microsoft Copilot beyond the basic usage data in the admin center, we also have tools to help see how things are going. The Microsoft Copilot dashboard gives you two options powered by Viva Insights. The one I’ll start with is included with any Microsoft 365 or Office 365 subscription.
-This is a purpose-built experience to view readiness and track your Copilot rollout. In the Readiness tab, you can start to assess the potential impact of Copilot by looking across activities like meetings, chat, email, and documents. And this is all based on your app usage and what controlled research has uncovered, and there are links to explore that research.
-Now the second option is available with a Viva Insights subscription. If you’re not familiar with Viva Insights, this gives your organization a great way to understand how people connect, collaborate, and also get work done. So it’s a natural fit for Microsoft Copilot.
-And, as you can see, it gives a deeper level of visibility into specific outcomes when adopting Copilot. It has detailed breakdowns of usage by feature across integrated experiences, how different groups within your organization are currently using Copilot capabilities. And there are additional filtering options to also show usage, for example, by a job function or level, along with group comparisons.
-And this information can help you understand where Copilot is adding the most value and where you can also help drive more benefit. Under Impact the insights help identify how Copilot is saving people time, like summaries and meetings, documents, email and chat, generating draft content. And Copilot responses with search or graph grounded chat. And you can dig deeper into each of these areas to understand how workplace behaviors are changing, like blocking uninterrupted focus time, or less time spent multitasking during meetings.
-And you can compare Copilot actions across groups and see how usage compares between them. This information helps you to gauge the benefit of Copilot and also helps active users share their experience with others as they get onboarded. Speaking of which, we also have a complete set of resources at adoption.microsoft.com/copilot for onboarding by role to get users up to speed quickly. So those are the quick steps to deploy Copilot for Microsoft 365 at scale and help ensure that your users are getting the most out of the service.
-To learn more, check out aka.ms/DeployCopilotforM365. And from here, there’s even more you can do to achieve just enough access to information in your organization, as well as labeling and data security policies. In fact, we just published a dedicated show on this at aka.ms/CopilotSecurityMechanics. Be sure to subscribe for the latest updates and I’ll see you next time.
Microsoft Tech Community – Latest Blogs –Read More
What’d be CLI code to set the system’s time to the H/W one
What’d be Windows’ way by CLI or GUI, to perform Linux ‘hwclock -s –localtime’
I.e. to set the system’s local time to the previously correctly set hardware clock time ?
What’d be Windows’ way by CLI or GUI, to perform Linux ‘hwclock -s –localtime’I.e. to set the system’s local time to the previously correctly set hardware clock time ? Read More
Power Apps-customized form access by external users
Power Apps-customized form access by external users
I have a document library in SharePoin online. I have created a Power Apps-customized form for the metadata columns. When a folder or a file in this document library is shared (through the share option, next to file or folder) with external users they cannot open the Power Apps-customized form.
A message of “Sign in required” is appearing.
Do they need to have Powerapps license ? Do I need to make any other change in order for external users to be able to access the Power Apps-customized form ?
Can someone help, please?
Power Apps-customized form access by external usersI have a document library in SharePoin online. I have created a Power Apps-customized form for the metadata columns. When a folder or a file in this document library is shared (through the share option, next to file or folder) with external users they cannot open the Power Apps-customized form.A message of “Sign in required” is appearing. Do they need to have Powerapps license ? Do I need to make any other change in order for external users to be able to access the Power Apps-customized form ?Can someone help, please? Read More
outlook issues in code
We have a server (multi-session) where multiple users login using their own credentials and run a custom application. This application has some Outlook Integration code (Exchange Online) and Outlook per se is logged in using a service account. Everything works perfectly fine but when the server gets rebooted planned/unplanned, Outlook Integration fails and we manually have to login into the server first using service account, start Outlook and finally log off. After that all users can again run their application successfully with Outlook Integration. We tried to create a scheduled task that starts the Outlook process with service account credentials but that doesn’t seem to be enough as it doesn’t login the user. Is there any way to automate this so that we don’t have to login and start Outlook manually after server gets rebooted or point us in the right direction.
We have a server (multi-session) where multiple users login using their own credentials and run a custom application. This application has some Outlook Integration code (Exchange Online) and Outlook per se is logged in using a service account. Everything works perfectly fine but when the server gets rebooted planned/unplanned, Outlook Integration fails and we manually have to login into the server first using service account, start Outlook and finally log off. After that all users can again run their application successfully with Outlook Integration. We tried to create a scheduled task that starts the Outlook process with service account credentials but that doesn’t seem to be enough as it doesn’t login the user. Is there any way to automate this so that we don’t have to login and start Outlook manually after server gets rebooted or point us in the right direction. Read More