New Blog | Microsoft Security Exposure Management introduces: Critical asset protection
In recent years, enterprises attack surface has exploded in volume and diversification. Security teams are struggling to keep pace with the technological advancements and changes occurring daily. New technologies, emerging work trends (such as remote work and distributed teams), expansion of the supply chain, cloud adoption, and more have led to an exponential growth in the size and complexity of the enterprise attack surface.
This rapid expansion has brought about new risks, and in turn, new tools to deal with these risks. The rapid increase of the attack surface has led to a rapid proliferation of security tools. The numbers are truly staggering with large organizations often using dozens of security tools. Combined with the shortage of security personnel and knowledge gaps, security teams are experiencing more than just alarm fatigue; they are facing risk fatigue.
If everything is important, then nothing is.
Risk fatigue occurs when there are so many potential risks or security issues to address that it becomes overwhelming, leading to decreased effectiveness in risk management efforts. Risk fatigue is a direct consequence of the inability to single out exposures with the highest potential impact; those that truly pose a tangible risk, from the entire exposure surface. Without context to support their decisions, security teams are forced to rely on inaccurate and suboptimal prioritization. Addressing the wrong issues results in a double loss – wasted team time and unresolved actual risks.
To effectively address risk fatigue, security teams should embrace a contextual risk-based approach. This entails thorough consideration of various security-related contexts, including the business criticality of an asset and the likelihood of it being compromised. By doing so, teams can strategically prioritize activities that yield the greatest security impact, bolstering the organization’s overall resilience. In this blog post, we will explore how Microsoft Security Exposure Management helps enterprises in identifying and managing their most critical assets and in focusing on mitigating risks to these assets.
Not all assets are created equal
As mentioned, a crucial aspect of adopting a contextual risk-based approach involves considering the business criticality of each asset and responding accordingly. Identifying critical assets isn’t just a recommended strategy for supporting risk-based prioritization; it is crucial in adopting the mindset of potential adversaries. Attackers often target critical assets in malicious operations like data theft, cyber espionage, disruption, ransomware attacks, and more. Given that attackers are laser-focused on critical assets, it’s imperative for defenders to mirror this focus.
However, in today’s highly complex, distributed, and dynamic enterprise environments, keeping pace is nearly impossible. This, combined with the above-mentioned shortage of security personnel, and knowledge gaps around adversary techniques, makes it highly challenging for organizations to identify, manage, monitor, and prioritize their business-critical assets. That’s where Microsoft Security Exposure Management comes in!
Focus first on what matters most with Microsoft Security Exposure Management
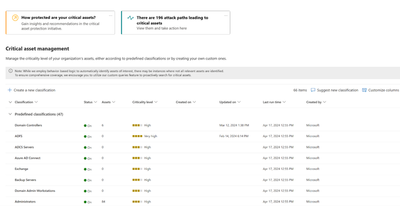
Microsoft Security Exposure Management provides users with everything they need to prioritize their business-critical assets. This includes a comprehensive out-of-the-box library of predefined classifications designed to identify and label your most critical devices, identities, and cloud resources. This includes classification for domain controllers, Azure AD Connect, ADFS servers, Backup servers, security administrators, domain administrators, databases with sensitive data and many more.
Creating these predefined classifications is no simple task, especially if you aim to accurately mark only critical assets that “meet the criteria”. For example, the process of identifying a critical domain controller involves a robust data collection procedure from Windows servers and workstations. Initially, various logics are implemented to identify devices offering Active Directory services. Next, different types of telemetry data, such as user-login events, device domain membership information, and various network signals, are processed to create a comprehensive understanding of the criticality of each domain entity. This process enables us to classify the domain controllers managing these domains as critical assets, regardless of whether they are onboarded to Microsoft Defender for Endpoint or not, across organizations of all sizes.
Figure 1: The critical asset management screen in Microsoft Security Exposure Management
Read the full post here: Microsoft Security Exposure Management introduces: Critical asset protection
By Dean Rubinstein
In recent years, enterprises attack surface has exploded in volume and diversification. Security teams are struggling to keep pace with the technological advancements and changes occurring daily. New technologies, emerging work trends (such as remote work and distributed teams), expansion of the supply chain, cloud adoption, and more have led to an exponential growth in the size and complexity of the enterprise attack surface.
This rapid expansion has brought about new risks, and in turn, new tools to deal with these risks. The rapid increase of the attack surface has led to a rapid proliferation of security tools. The numbers are truly staggering with large organizations often using dozens of security tools. Combined with the shortage of security personnel and knowledge gaps, security teams are experiencing more than just alarm fatigue; they are facing risk fatigue.
If everything is important, then nothing is.
Risk fatigue occurs when there are so many potential risks or security issues to address that it becomes overwhelming, leading to decreased effectiveness in risk management efforts. Risk fatigue is a direct consequence of the inability to single out exposures with the highest potential impact; those that truly pose a tangible risk, from the entire exposure surface. Without context to support their decisions, security teams are forced to rely on inaccurate and suboptimal prioritization. Addressing the wrong issues results in a double loss – wasted team time and unresolved actual risks.
To effectively address risk fatigue, security teams should embrace a contextual risk-based approach. This entails thorough consideration of various security-related contexts, including the business criticality of an asset and the likelihood of it being compromised. By doing so, teams can strategically prioritize activities that yield the greatest security impact, bolstering the organization’s overall resilience. In this blog post, we will explore how Microsoft Security Exposure Management helps enterprises in identifying and managing their most critical assets and in focusing on mitigating risks to these assets.
Not all assets are created equal
As mentioned, a crucial aspect of adopting a contextual risk-based approach involves considering the business criticality of each asset and responding accordingly. Identifying critical assets isn’t just a recommended strategy for supporting risk-based prioritization; it is crucial in adopting the mindset of potential adversaries. Attackers often target critical assets in malicious operations like data theft, cyber espionage, disruption, ransomware attacks, and more. Given that attackers are laser-focused on critical assets, it’s imperative for defenders to mirror this focus.
However, in today’s highly complex, distributed, and dynamic enterprise environments, keeping pace is nearly impossible. This, combined with the above-mentioned shortage of security personnel, and knowledge gaps around adversary techniques, makes it highly challenging for organizations to identify, manage, monitor, and prioritize their business-critical assets. That’s where Microsoft Security Exposure Management comes in!
Focus first on what matters most with Microsoft Security Exposure Management
Microsoft Security Exposure Management provides users with everything they need to prioritize their business-critical assets. This includes a comprehensive out-of-the-box library of predefined classifications designed to identify and label your most critical devices, identities, and cloud resources. This includes classification for domain controllers, Azure AD Connect, ADFS servers, Backup servers, security administrators, domain administrators, databases with sensitive data and many more.
Creating these predefined classifications is no simple task, especially if you aim to accurately mark only critical assets that “meet the criteria”. For example, the process of identifying a critical domain controller involves a robust data collection procedure from Windows servers and workstations. Initially, various logics are implemented to identify devices offering Active Directory services. Next, different types of telemetry data, such as user-login events, device domain membership information, and various network signals, are processed to create a comprehensive understanding of the criticality of each domain entity. This process enables us to classify the domain controllers managing these domains as critical assets, regardless of whether they are onboarded to Microsoft Defender for Endpoint or not, across organizations of all sizes.
Figure 1: The critical asset management screen in Microsoft Security Exposure Management
Read the full post here: Microsoft Security Exposure Management introduces: Critical asset protection