Category: News
Does Embedded Coder support Infineon Aurix Devices?
Hi There,
I am heading System Applications Team at Infineon India.
Some of our customers are keen to have MATLAB support for our Aurix Microcontrollers.
Would like to know what support is currently available & what are the options?
Thanks,
AvinashHi There,
I am heading System Applications Team at Infineon India.
Some of our customers are keen to have MATLAB support for our Aurix Microcontrollers.
Would like to know what support is currently available & what are the options?
Thanks,
Avinash Hi There,
I am heading System Applications Team at Infineon India.
Some of our customers are keen to have MATLAB support for our Aurix Microcontrollers.
Would like to know what support is currently available & what are the options?
Thanks,
Avinash infineon, aurix MATLAB Answers — New Questions
Problem 56313. Find Air Temperature from Cricket Stridulation Rate
function y = getTemperature_F(nchirps_in_14s)
x=[20 30 40 50]
F=0;
y=x;
y=fliplr(y);
while F<=50
F=F+110;
y=F-y;
end
end
%whats wrong with my answer i am not getting it.function y = getTemperature_F(nchirps_in_14s)
x=[20 30 40 50]
F=0;
y=x;
y=fliplr(y);
while F<=50
F=F+110;
y=F-y;
end
end
%whats wrong with my answer i am not getting it. function y = getTemperature_F(nchirps_in_14s)
x=[20 30 40 50]
F=0;
y=x;
y=fliplr(y);
while F<=50
F=F+110;
y=F-y;
end
end
%whats wrong with my answer i am not getting it. homework MATLAB Answers — New Questions
how to ask to the user to insert a command while a function is being executing?
In a previous version of my code, I implemented a function which reads data from serial port. While the function was storing and managing data received through the serial port, the user can each time insert a command "stop" which advice the connected device to stop the communication. The code was this:
configureCallback(controller,"byte",1,@readData)
%%
val = input(‘Comando: ‘,’s’);
% command start
writeline(controller, val);
%%
val = input(‘Comando: ‘,’s’);
% command stop
writeline(controller, val);
I’m trying to do the same but with my peripheral connected to my pc through bluetooth low energy.
However, I don’t know how to make the funcion works and the script asking for the command simultaneously, it seems like configureCallback function is not working in this case.
%% write START
val = input(‘Comando: ‘,’s’);
% Convert string to uint8 array
val_bytes = uint8(val);
% command start
write(c_write,val_bytes,’WithoutResponse’);
%% read data
if finished==0
% Set the callback function for the characteristic
c_read.DataAvailableFcn = @bleDataReceived;
end
%% write STOP
val = input(‘Comando: ‘,’s’);
% Convert string to uint8 array
val_bytes = uint8(val);
% command start
write(c_write,val_bytes,’WithoutResponse’);
i wrote this, but the function is continuosly reading after command start is sent without letting me the chance to insert the command stop.In a previous version of my code, I implemented a function which reads data from serial port. While the function was storing and managing data received through the serial port, the user can each time insert a command "stop" which advice the connected device to stop the communication. The code was this:
configureCallback(controller,"byte",1,@readData)
%%
val = input(‘Comando: ‘,’s’);
% command start
writeline(controller, val);
%%
val = input(‘Comando: ‘,’s’);
% command stop
writeline(controller, val);
I’m trying to do the same but with my peripheral connected to my pc through bluetooth low energy.
However, I don’t know how to make the funcion works and the script asking for the command simultaneously, it seems like configureCallback function is not working in this case.
%% write START
val = input(‘Comando: ‘,’s’);
% Convert string to uint8 array
val_bytes = uint8(val);
% command start
write(c_write,val_bytes,’WithoutResponse’);
%% read data
if finished==0
% Set the callback function for the characteristic
c_read.DataAvailableFcn = @bleDataReceived;
end
%% write STOP
val = input(‘Comando: ‘,’s’);
% Convert string to uint8 array
val_bytes = uint8(val);
% command start
write(c_write,val_bytes,’WithoutResponse’);
i wrote this, but the function is continuosly reading after command start is sent without letting me the chance to insert the command stop. In a previous version of my code, I implemented a function which reads data from serial port. While the function was storing and managing data received through the serial port, the user can each time insert a command "stop" which advice the connected device to stop the communication. The code was this:
configureCallback(controller,"byte",1,@readData)
%%
val = input(‘Comando: ‘,’s’);
% command start
writeline(controller, val);
%%
val = input(‘Comando: ‘,’s’);
% command stop
writeline(controller, val);
I’m trying to do the same but with my peripheral connected to my pc through bluetooth low energy.
However, I don’t know how to make the funcion works and the script asking for the command simultaneously, it seems like configureCallback function is not working in this case.
%% write START
val = input(‘Comando: ‘,’s’);
% Convert string to uint8 array
val_bytes = uint8(val);
% command start
write(c_write,val_bytes,’WithoutResponse’);
%% read data
if finished==0
% Set the callback function for the characteristic
c_read.DataAvailableFcn = @bleDataReceived;
end
%% write STOP
val = input(‘Comando: ‘,’s’);
% Convert string to uint8 array
val_bytes = uint8(val);
% command start
write(c_write,val_bytes,’WithoutResponse’);
i wrote this, but the function is continuosly reading after command start is sent without letting me the chance to insert the command stop. matlab, functions, function, callback, ble, bluetooth MATLAB Answers — New Questions
Private Teams not sending chat to external teams
I got a new laptop that has Teams (private) on it. I have tried sending a chat to my work email, but the chat won’t show up. I get an email (work) saying to join teams to see the chat. When I click the join button, it brings me to my work teams but no chat is there. If I send a chat from work to personal account, I see a message come in from ‘Unknown User’. If I click on it, I get a message to either block or accept the user. If I click accept, I see an error saying something went wrong and to try again – it never accepts.
How do I get this to send/receive correctly?
I got a new laptop that has Teams (private) on it. I have tried sending a chat to my work email, but the chat won’t show up. I get an email (work) saying to join teams to see the chat. When I click the join button, it brings me to my work teams but no chat is there. If I send a chat from work to personal account, I see a message come in from ‘Unknown User’. If I click on it, I get a message to either block or accept the user. If I click accept, I see an error saying something went wrong and to try again – it never accepts. How do I get this to send/receive correctly? Read More
Querying for config options that aren’t reported by “mdatp health”
Hello. Is there a way to query for existing config options that are not reported by “mdatp health”? For example, maximum-on-demand-scan-threads is not reported by “mdatp health.”
The “mdatp config” command only lets you change the value, but doesn’t provide a way to determine its current value. For example:
$ mdatp config maximum-on-demand-scan-threads
Configure maximum number of threads used in on-demand scans:
–value arg Numerical value between 1 and 64
There appears to be a way to brute force it, by supplying all possible options until the command fails because the new setting is the same as the current setting:
$ sudo mdatp config maximum-on-demand-scan-threads –value 16
Configuration property updated.
$ sudo mdatp config maximum-on-demand-scan-threads –value 16
Configuration not updated
New setting value is the same as the current value
Is there any better way to learn the current value?
Hello. Is there a way to query for existing config options that are not reported by “mdatp health”? For example, maximum-on-demand-scan-threads is not reported by “mdatp health.” The “mdatp config” command only lets you change the value, but doesn’t provide a way to determine its current value. For example: $ mdatp config maximum-on-demand-scan-threads
Configure maximum number of threads used in on-demand scans:
–value arg Numerical value between 1 and 64 There appears to be a way to brute force it, by supplying all possible options until the command fails because the new setting is the same as the current setting: $ sudo mdatp config maximum-on-demand-scan-threads –value 16
Configuration property updated.
$ sudo mdatp config maximum-on-demand-scan-threads –value 16
Configuration not updated
New setting value is the same as the current value Is there any better way to learn the current value? Read More
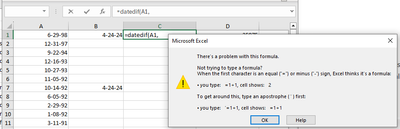
Can’t use the datedif function
Hello, I’m trying to get average age from date of birth in an Excel sheet (Microsoft 365) and the function to be used is datedif but nothing works, I always get this message. Help!
Hello, I’m trying to get average age from date of birth in an Excel sheet (Microsoft 365) and the function to be used is datedif but nothing works, I always get this message. Help! Read More
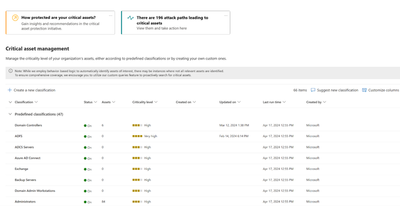
New Blog | Microsoft Security Exposure Management introduces: Critical asset protection
In recent years, enterprises attack surface has exploded in volume and diversification. Security teams are struggling to keep pace with the technological advancements and changes occurring daily. New technologies, emerging work trends (such as remote work and distributed teams), expansion of the supply chain, cloud adoption, and more have led to an exponential growth in the size and complexity of the enterprise attack surface.
This rapid expansion has brought about new risks, and in turn, new tools to deal with these risks. The rapid increase of the attack surface has led to a rapid proliferation of security tools. The numbers are truly staggering with large organizations often using dozens of security tools. Combined with the shortage of security personnel and knowledge gaps, security teams are experiencing more than just alarm fatigue; they are facing risk fatigue.
If everything is important, then nothing is.
Risk fatigue occurs when there are so many potential risks or security issues to address that it becomes overwhelming, leading to decreased effectiveness in risk management efforts. Risk fatigue is a direct consequence of the inability to single out exposures with the highest potential impact; those that truly pose a tangible risk, from the entire exposure surface. Without context to support their decisions, security teams are forced to rely on inaccurate and suboptimal prioritization. Addressing the wrong issues results in a double loss – wasted team time and unresolved actual risks.
To effectively address risk fatigue, security teams should embrace a contextual risk-based approach. This entails thorough consideration of various security-related contexts, including the business criticality of an asset and the likelihood of it being compromised. By doing so, teams can strategically prioritize activities that yield the greatest security impact, bolstering the organization’s overall resilience. In this blog post, we will explore how Microsoft Security Exposure Management helps enterprises in identifying and managing their most critical assets and in focusing on mitigating risks to these assets.
Not all assets are created equal
As mentioned, a crucial aspect of adopting a contextual risk-based approach involves considering the business criticality of each asset and responding accordingly. Identifying critical assets isn’t just a recommended strategy for supporting risk-based prioritization; it is crucial in adopting the mindset of potential adversaries. Attackers often target critical assets in malicious operations like data theft, cyber espionage, disruption, ransomware attacks, and more. Given that attackers are laser-focused on critical assets, it’s imperative for defenders to mirror this focus.
However, in today’s highly complex, distributed, and dynamic enterprise environments, keeping pace is nearly impossible. This, combined with the above-mentioned shortage of security personnel, and knowledge gaps around adversary techniques, makes it highly challenging for organizations to identify, manage, monitor, and prioritize their business-critical assets. That’s where Microsoft Security Exposure Management comes in!
Focus first on what matters most with Microsoft Security Exposure Management
Microsoft Security Exposure Management provides users with everything they need to prioritize their business-critical assets. This includes a comprehensive out-of-the-box library of predefined classifications designed to identify and label your most critical devices, identities, and cloud resources. This includes classification for domain controllers, Azure AD Connect, ADFS servers, Backup servers, security administrators, domain administrators, databases with sensitive data and many more.
Creating these predefined classifications is no simple task, especially if you aim to accurately mark only critical assets that “meet the criteria”. For example, the process of identifying a critical domain controller involves a robust data collection procedure from Windows servers and workstations. Initially, various logics are implemented to identify devices offering Active Directory services. Next, different types of telemetry data, such as user-login events, device domain membership information, and various network signals, are processed to create a comprehensive understanding of the criticality of each domain entity. This process enables us to classify the domain controllers managing these domains as critical assets, regardless of whether they are onboarded to Microsoft Defender for Endpoint or not, across organizations of all sizes.
Figure 1: The critical asset management screen in Microsoft Security Exposure Management
Read the full post here: Microsoft Security Exposure Management introduces: Critical asset protection
By Dean Rubinstein
In recent years, enterprises attack surface has exploded in volume and diversification. Security teams are struggling to keep pace with the technological advancements and changes occurring daily. New technologies, emerging work trends (such as remote work and distributed teams), expansion of the supply chain, cloud adoption, and more have led to an exponential growth in the size and complexity of the enterprise attack surface.
This rapid expansion has brought about new risks, and in turn, new tools to deal with these risks. The rapid increase of the attack surface has led to a rapid proliferation of security tools. The numbers are truly staggering with large organizations often using dozens of security tools. Combined with the shortage of security personnel and knowledge gaps, security teams are experiencing more than just alarm fatigue; they are facing risk fatigue.
If everything is important, then nothing is.
Risk fatigue occurs when there are so many potential risks or security issues to address that it becomes overwhelming, leading to decreased effectiveness in risk management efforts. Risk fatigue is a direct consequence of the inability to single out exposures with the highest potential impact; those that truly pose a tangible risk, from the entire exposure surface. Without context to support their decisions, security teams are forced to rely on inaccurate and suboptimal prioritization. Addressing the wrong issues results in a double loss – wasted team time and unresolved actual risks.
To effectively address risk fatigue, security teams should embrace a contextual risk-based approach. This entails thorough consideration of various security-related contexts, including the business criticality of an asset and the likelihood of it being compromised. By doing so, teams can strategically prioritize activities that yield the greatest security impact, bolstering the organization’s overall resilience. In this blog post, we will explore how Microsoft Security Exposure Management helps enterprises in identifying and managing their most critical assets and in focusing on mitigating risks to these assets.
Not all assets are created equal
As mentioned, a crucial aspect of adopting a contextual risk-based approach involves considering the business criticality of each asset and responding accordingly. Identifying critical assets isn’t just a recommended strategy for supporting risk-based prioritization; it is crucial in adopting the mindset of potential adversaries. Attackers often target critical assets in malicious operations like data theft, cyber espionage, disruption, ransomware attacks, and more. Given that attackers are laser-focused on critical assets, it’s imperative for defenders to mirror this focus.
However, in today’s highly complex, distributed, and dynamic enterprise environments, keeping pace is nearly impossible. This, combined with the above-mentioned shortage of security personnel, and knowledge gaps around adversary techniques, makes it highly challenging for organizations to identify, manage, monitor, and prioritize their business-critical assets. That’s where Microsoft Security Exposure Management comes in!
Focus first on what matters most with Microsoft Security Exposure Management
Microsoft Security Exposure Management provides users with everything they need to prioritize their business-critical assets. This includes a comprehensive out-of-the-box library of predefined classifications designed to identify and label your most critical devices, identities, and cloud resources. This includes classification for domain controllers, Azure AD Connect, ADFS servers, Backup servers, security administrators, domain administrators, databases with sensitive data and many more.
Creating these predefined classifications is no simple task, especially if you aim to accurately mark only critical assets that “meet the criteria”. For example, the process of identifying a critical domain controller involves a robust data collection procedure from Windows servers and workstations. Initially, various logics are implemented to identify devices offering Active Directory services. Next, different types of telemetry data, such as user-login events, device domain membership information, and various network signals, are processed to create a comprehensive understanding of the criticality of each domain entity. This process enables us to classify the domain controllers managing these domains as critical assets, regardless of whether they are onboarded to Microsoft Defender for Endpoint or not, across organizations of all sizes.
Figure 1: The critical asset management screen in Microsoft Security Exposure Management
Read the full post here: Microsoft Security Exposure Management introduces: Critical asset protection
Add a banner in Microsoft Teams
We are planning to implement a retention policy on Microsoft Teams that will automatically delete chats older than XX days. We would like to inform all Teams users about this change and are exploring options for doing so. Is it possible to add a banner within Microsoft Teams to notify all users? We would like the banner to display a message stating that starting January 1st, all chats will be deleted according to this new retention policy.
We are planning to implement a retention policy on Microsoft Teams that will automatically delete chats older than XX days. We would like to inform all Teams users about this change and are exploring options for doing so. Is it possible to add a banner within Microsoft Teams to notify all users? We would like the banner to display a message stating that starting January 1st, all chats will be deleted according to this new retention policy. Read More
New planner sorting by Source
In the new planner I can order by name, priority and date due
Why can I not also order by the Source field?
In the new planner I can order by name, priority and date dueWhy can I not also order by the Source field? Read More
How to create an autonumbering formula based on three columns
Hi All, I’m trying to create a formula that will automatically generate a numeric code for each combination of columns. The first column is populated by a dropdown list, so that’s an easy if-then formula (make in the attached image). The hard part is assigning column B a value that restarts when there is a new “make”, and yet assigns the same value if that make is already entered. And then tougher yet is to assign a colour code that also restarts when there is a new model.
So, in the table below in column A, users pick their make. Honda will auto populate “1.” into column D. Then the user enters the make into column B. Row 2 will add “1.” into the code for the first entry (Accord), “2.” for the second entry, etc. But if one of those models gets entered again in a lower row, the code will remember what was already assigned.
Same idea for column D.
I can’t make only drop-down lists for the model and colour column – users need to be able to enter custom values (it’s not for make-model-colour – I’m just using that as an example to show what I need).
I’ve tried using countif and if-then statements using arrays, but it’s not working. Any solutions would be greatly appreciated.
A
B
C
D
Make
Model
Colour
Code
Honda
Accord
Black
1.1.1
Honda
Civic
Red
1.2.1
Toyota
Rav4
Silver
2.1.1
Honda
Accord
Blue
1.1.2
Ford
F-150
Onyx
3.1.1
Ford
F-150
White
3.1.2
Chevrolet
Silverado
Moonlight
4.1.1
Ford
F-150
Steel
3.1.3
Chevrolet
Silverado
Pearl
4.1.2
Audi
Q4
Midnight
5.1.1
Audi
Q4
Chrome
5.1.2
Audi
Q8
Night
5.2.1
Audi
Q4
Gunmetal
5.1.3
Hi All, I’m trying to create a formula that will automatically generate a numeric code for each combination of columns. The first column is populated by a dropdown list, so that’s an easy if-then formula (make in the attached image). The hard part is assigning column B a value that restarts when there is a new “make”, and yet assigns the same value if that make is already entered. And then tougher yet is to assign a colour code that also restarts when there is a new model. So, in the table below in column A, users pick their make. Honda will auto populate “1.” into column D. Then the user enters the make into column B. Row 2 will add “1.” into the code for the first entry (Accord), “2.” for the second entry, etc. But if one of those models gets entered again in a lower row, the code will remember what was already assigned.Same idea for column D.I can’t make only drop-down lists for the model and colour column – users need to be able to enter custom values (it’s not for make-model-colour – I’m just using that as an example to show what I need).I’ve tried using countif and if-then statements using arrays, but it’s not working. Any solutions would be greatly appreciated. ABCDMakeModelColourCodeHondaAccordBlack1.1.1HondaCivicRed1.2.1ToyotaRav4Silver2.1.1HondaAccordBlue1.1.2FordF-150Onyx3.1.1FordF-150White3.1.2ChevroletSilveradoMoonlight4.1.1FordF-150Steel3.1.3ChevroletSilveradoPearl4.1.2AudiQ4Midnight5.1.1AudiQ4Chrome5.1.2AudiQ8Night5.2.1AudiQ4Gunmetal5.1.3 Read More
Limit usage of Security Group
I have a security group in Azure that dynamically holds all users for Region X.
This group is used to grant access within our SharePoint environment to large sets of users, but we found that our users discovered the group, and began assigning it inappropriately.
Is there a way to limit who can use this group? I want to make it so only a set of IT administrators can place this group in the permission set of a SharePoint site, folder, or file.
This would be similar to the functionality of limiting who can email a distribution list.
I feel with the roll-out of Copilot, it is important to restrict the users ability to use the “everyone” groups.
I have a security group in Azure that dynamically holds all users for Region X. This group is used to grant access within our SharePoint environment to large sets of users, but we found that our users discovered the group, and began assigning it inappropriately. Is there a way to limit who can use this group? I want to make it so only a set of IT administrators can place this group in the permission set of a SharePoint site, folder, or file. This would be similar to the functionality of limiting who can email a distribution list. I feel with the roll-out of Copilot, it is important to restrict the users ability to use the “everyone” groups. Read More
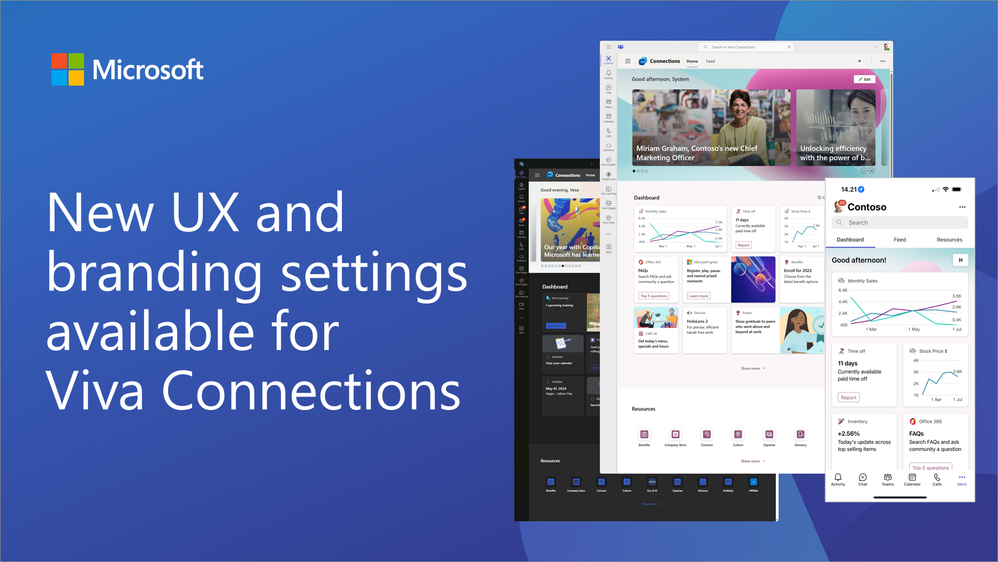
New UX and branding settings now available for the Viva Connections
We are excited to announce new UX and branding capabilities and options for our customers within the Viva Connections enabling customers to adjust the experience based on their company brand and end users to select the best suitable experience for them.
Viva Connections is a company-branded employee experience destination that seamlessly integrates news, conversations, and resources within the apps and devices you use daily. It is designed to foster a culture of inclusion, allowing everyone’s ideas and voices to matter, while providing employees with the flexibility to engage and participate from anywhere.
With the latest updates, the change a look feature has been fully released across the world for all Viva Connections instances. This will enable customers to select the theme color based on the company branding with support on custom themes. We are also rolling out a dark mode support for the Viva Connections desktop experience as an option for end users.
Different branding options in the Viva Connections:
Custom icon for Viva Connections – This can be configured in the Viva Connections app settings
Custom name for Viva Connections – This can be configured in the Viva Connections app settings
Hero section image – This can be configured by the dashboard operators in the Viva Connections UI
Theme color – This can be configured by the dashboard operators in the Viva Connections UI
Custom fonts (soon) – This will be coming soon as an option for dashboard operators when the brand center is rolling out
Imaginary used within the dashboard cards – You can configure out of the box and custom cards to use your company images and colors, optimizing the experience for your company brand
Here’s an example of the dark mode rending from the Microsoft’s own Viva Connections deployment. Dark mode rendering will be automatically adopted based on the Microsoft Teams settings done by the end user.
Resources
Here are the key resources to get started with the Viva Connections and the new capabilities.
Microsoft Viva Connections – Product overview
Overview of Viva Connections – Microsoft Learn documentation
Customize and edit the Viva Connections experience – Microsoft Learn documentation
Introduction to change the look feature in Viva Connections – YouTube video
SharePoint site theming – Microsoft Learn documentation
Fluent UI Theme Designer – Tool to generate custom themes
SharePoint Online PowerShell cmdlets for theme handling – Commands to install themes in tenant level
Overview of Viva Connections extensibility – Build custom experiences for the Viva Connections and integrate it with your Microsoft Teams and SharePoint solutions
Viva Connections partner apps in the Microsoft store / AppSource – available to be installed to your dashboard
Frequently asked questions
Q: Is it possible to use custom theme with the Viva Connections with our company color
A: Yes. Available themes are coming from the SharePoint side, which is also powering Viva Connections. You can create a custom theme based on your company colors and install that to be available within your tenant using SharePoint Online PowerShell.
Q: Can I use our company brand image on the header section?
A: Absolutely. Microsoft is providing set of stock images which can be used, but you can absolutely also upload your custom brand image and use that in the header section. This will be then used within desktop, table and mobile experiences.
Q: I don’t see the dark mode yet working in my tenant – when is it rolling out?
A: We are starting this gradually within April 2024, so it can take a while for this feature to be available within your tenant.
Let us know what you think. Your feedback is more than welcome 🧡
Microsoft Tech Community – Latest Blogs –Read More
Sync Up Episode 10: Data on the Move – Migrating to OneDrive
Sync Up Episode 10 is now available on all your favorite podcast apps! This month, Arvind Mishra and I are talking with Vishal Lodha and Yogesh Ratnaparkhi about how to migrate your company’s data to OneDrive and SharePoint! After a brief detour (in which we learn that Arvind wants to go to Egypt and Stephen wants to go to space), we jump in and bust some common data migration myths and then offer migration tips and best practices. The video for this episode will be available in YouTube in the coming weeks!
Show: https://aka.ms/SyncUp | Apple Podcasts: https://aka.ms/SyncUp/Apple | Spotify: https://aka.ms/SyncUp/Spotify | RSS: https://aka.ms/SyncUp/RSS
OneDrive migration myths
Here’s a quick look at the migration myths that we cover in this episode.
Myth #1: Is migration only for on-premise customers, or customers who are trying to move between tenants?
Busted! Migration is not only for these customers, but also for those who might be coming from other cloud providers!
Myth #2: Migration is only for large enterprises or customers.
Busted! Migration is important for customers of ALL sizes, and Microsoft 365 provides unique value, regardless of your organization’s size.
Myth #3: Throttling during migration is really bad.
Busted! Throttling is essential to ensuring that all of our customers have a fast experience using our product. We’ve continued to improve our service to ensure that you, or our partners, can get the maximum throughput possible.
Myth #4: Migration takes years.
Busted! Like anything in life, migrations will always go smoother if you plan ahead of time! Customers who come in with a plan are often able to migrate quickly, even when they have large amounts of data.
Myth #5: Microsoft will only help me migrate if I’m a large company.
Busted! While services like FastTrack are limited to customers of a certain size, the M365 admin center offers tooling and guidance for migration that ALL customers can take advantage of! We also work closely with many third-party providers to ensure all customers have options. Plus, you can join our monthly OneDrive office hours to ask questions.
10 practical tips for migrating files to OneDrive
When planning your migration to OneDrive, consider these best practices and tips.
Assess and plan: Before beginning your migration, thoroughly assess your current data and IT infrastructure. Understanding what you have helps in planning the migration effectively, ensuring minimal disruption.
Understand the benefits: The benefits of migrating to Microsoft 365 include integrated security and compliance features, seamless collaboration between apps, AI assistance with Copilot, and a reduction in total cost of ownership.
Use Microsoft tools: Leverage the tools provided by Microsoft for migration, available through the Microsoft Admin Center. These tools are designed to simplify the migration process from different sources, including on-premises environments and other cloud services.
Consider third-party tools: For specific needs not addressed by Microsoft’s tools, consider third-party solutions. These can offer specialized features and may integrate well with existing IT systems.
Plan for small businesses: If you’re a small business, take advantage of Microsoft’s migration services tailored for smaller organizations, which are designed to handle less complex environments with fewer resources.
Handle throttling smartly: Understand that throttling mechanisms are in place to ensure service quality for all users. Plan your migration strategy to mitigate any potential issues this could cause, such as scheduling migrations during off-peak hours.
Continuous migration: Keep the migration process ongoing without large gaps. This helps in utilizing the full capacity of available resources and reduces the time frame of the migration project.
Prepare for change: Migration may have challenges, but many can be overcome with preparation. Work with your team to understand what your unique challenges might be.
Leverage FastTrack and partner services: For eligible organizations, the Microsoft FastTrack service offers guidance and direct support. Additionally, a vast partner ecosystem is available to assist with more tailored needs.
Monitor and adjust: After migrating, continue to monitor the performance and leverage the OneDrive Adoption Hub to help onboard your users. Be prepared to make adjustments as necessary to optimize the use of new features and integrations.
As always, we hope you enjoy this episode! Let us know what you think in the comments below!
Microsoft Tech Community – Latest Blogs –Read More
Need help with counting the last digit of a number
Hi team!
Respectfully request help with the following:
Need a formula in cell D3 of Sheet2 that accomplishes the following:
If Sheet1 column D says, “Acme”, count the number of times the last digit of the number in Sheet1 column C matches the number in Sheet2 column B.
Can’t find a way to attach a sample. I’ll try to post, and then edit, and see if the system allows me to attach.
Hi team! Respectfully request help with the following: Need a formula in cell D3 of Sheet2 that accomplishes the following: If Sheet1 column D says, “Acme”, count the number of times the last digit of the number in Sheet1 column C matches the number in Sheet2 column B. Can’t find a way to attach a sample. I’ll try to post, and then edit, and see if the system allows me to attach. Read More
Word table formula with SEQ operators not working properly on one computer but fine on others
I’m trying to resolve an issue for a customer with a document that uses SEQ formula operators.
I’ve created an invoice document template and the table uses some SEQ formula operators to calculate the invoice total, amongst some other things, but the template doesn’t work correctly on my clients machine. When the fields are updated using F9, the dollar symbols are repeated and decimal places are introduced even when these are zero.
To be clear, the template works correctly on my computer. It also works correctly on my client’s colleagues computer too.
I’m confused as to what the problem is. We’re both using Windows 11 and we’re both using the latest version of Microsoft Office 365 but there must be something different between the two installations? Here’s some things I’ve already tried to resolve the problem:
Client was previously on ‘Microsoft Office Mondo 2016’ which was thought to be the source of the problem but we’ve now installed a trial of the latest Microsoft Office 365. Before they updated from Mondo, we were getting messages about the contents of the file being unreadable, but these now don’t appear.Verified that ‘Protected View’ or anything to do with the Trust Centre is blocking the formulas.Disabled any Add-Ins.Ran the Word Document in safe mode.Stripped all formatting from the document to rule out other conflictsThe document was sent to the client via email, I tried sending via WeTransfer instead, incase email was corrupting the file.
Does anyone have any suggestions?
Here’s what formula code I’m using in one of the cells. I’m not an expert in these SEQ operators but I built this based off some other formulas I found on StackExchange, basically it multiplies three cells together to create a total for the row, it works relatively so the same code can be used in all total cells and it won’t break if other rows above or below are deleted.
${ =({ QUOTE “D{ =1+{ SEQ row * Arabic } * Arabic }” }*{ QUOTE “E{ =1+{ SEQ row c * Arabic } * Arabic }” }*{ QUOTE “F{ =1+{ SEQ row c * Arabic}* Arabic }” }) }
Here’s a video of what happens, we’re using a stripped back version of the template in that example. I’ve also uploaded an anonymised version of the file to WeTransfer if anyone wants to test the file directly.
I’m trying to resolve an issue for a customer with a document that uses SEQ formula operators.I’ve created an invoice document template and the table uses some SEQ formula operators to calculate the invoice total, amongst some other things, but the template doesn’t work correctly on my clients machine. When the fields are updated using F9, the dollar symbols are repeated and decimal places are introduced even when these are zero. To be clear, the template works correctly on my computer. It also works correctly on my client’s colleagues computer too. I’m confused as to what the problem is. We’re both using Windows 11 and we’re both using the latest version of Microsoft Office 365 but there must be something different between the two installations? Here’s some things I’ve already tried to resolve the problem: Client was previously on ‘Microsoft Office Mondo 2016’ which was thought to be the source of the problem but we’ve now installed a trial of the latest Microsoft Office 365. Before they updated from Mondo, we were getting messages about the contents of the file being unreadable, but these now don’t appear.Verified that ‘Protected View’ or anything to do with the Trust Centre is blocking the formulas.Disabled any Add-Ins.Ran the Word Document in safe mode.Stripped all formatting from the document to rule out other conflictsThe document was sent to the client via email, I tried sending via WeTransfer instead, incase email was corrupting the file.Does anyone have any suggestions? Here’s what formula code I’m using in one of the cells. I’m not an expert in these SEQ operators but I built this based off some other formulas I found on StackExchange, basically it multiplies three cells together to create a total for the row, it works relatively so the same code can be used in all total cells and it won’t break if other rows above or below are deleted.${ =({ QUOTE “D{ =1+{ SEQ row * Arabic } * Arabic }” }*{ QUOTE “E{ =1+{ SEQ row c * Arabic } * Arabic }” }*{ QUOTE “F{ =1+{ SEQ row c * Arabic}* Arabic }” }) }Here’s a video of what happens, we’re using a stripped back version of the template in that example. I’ve also uploaded an anonymised version of the file to WeTransfer if anyone wants to test the file directly. Read More
Shared voicemail greeting for no agents – automatically switches to off
Good afternoon,
I’m trying to adjust our Global Voice Application Policy and for some reason, every time I set “Shared voicemail greeting for no agents” to on after a few seconds it switches back off. Is there a different method of setting this that will allow the setting to stay?
Good afternoon,I’m trying to adjust our Global Voice Application Policy and for some reason, every time I set “Shared voicemail greeting for no agents” to on after a few seconds it switches back off. Is there a different method of setting this that will allow the setting to stay? Read More
Copilot sidebar in Edge “unable to connect to the service”
Hello Everyone,
We are having intermittent issues with the Copilot sidebar in Edge. It works sometimes, and other times we get an error that says “We’re sorry but we’re unable to connect to the service at this time.” It has a refresh button which doesn’t help. What’s weird, is that we have Copilot licenses enabled for our users and going to https://bing.com/chat works fine in all cases (and shows the user signed in and “protected” as expected).
Anyone else have this issue? Any suggestions to fix this issue?
Brian
Hello Everyone, We are having intermittent issues with the Copilot sidebar in Edge. It works sometimes, and other times we get an error that says “We’re sorry but we’re unable to connect to the service at this time.” It has a refresh button which doesn’t help. What’s weird, is that we have Copilot licenses enabled for our users and going to https://bing.com/chat works fine in all cases (and shows the user signed in and “protected” as expected). Anyone else have this issue? Any suggestions to fix this issue? Brian Read More
Extract certain values in .mat file
Hi,
I have a mat file with 1250×1 data and I want to extract specific values from the 1250. For example I want to extract every 2nd or every 5th values.
As an example, the mat file contains the following values:
-0.13793 -0.114746 -0.204773 -0.224304 -0.181274 -0.192566 -0.159912 -0.174866 -0.134888 -0.148926
For every 2nd I want to read: -0.114746 -0.224304 -0.192566 -0.174866 -0.148926
For every 5th I want to read: -0.181274 -0.148926
What is the best command to do this? Thank you.Hi,
I have a mat file with 1250×1 data and I want to extract specific values from the 1250. For example I want to extract every 2nd or every 5th values.
As an example, the mat file contains the following values:
-0.13793 -0.114746 -0.204773 -0.224304 -0.181274 -0.192566 -0.159912 -0.174866 -0.134888 -0.148926
For every 2nd I want to read: -0.114746 -0.224304 -0.192566 -0.174866 -0.148926
For every 5th I want to read: -0.181274 -0.148926
What is the best command to do this? Thank you. Hi,
I have a mat file with 1250×1 data and I want to extract specific values from the 1250. For example I want to extract every 2nd or every 5th values.
As an example, the mat file contains the following values:
-0.13793 -0.114746 -0.204773 -0.224304 -0.181274 -0.192566 -0.159912 -0.174866 -0.134888 -0.148926
For every 2nd I want to read: -0.114746 -0.224304 -0.192566 -0.174866 -0.148926
For every 5th I want to read: -0.181274 -0.148926
What is the best command to do this? Thank you. extract data MATLAB Answers — New Questions
Function definitions are not permitted in this context.
help me
Function definitions are not permitted in this context.help me
Function definitions are not permitted in this context. help me
Function definitions are not permitted in this context. matlab, matlab 2014b MATLAB Answers — New Questions
Error when installing NCORR Program in MATLAB for DIC
Hello,
I want to use DIC in MATLAB. I tried to import/install NCORR program to MATLAB but I get these two errors (screeshots below) that I need help resolving.
The .cpp files in my PC (screenshot-top) does not appear the same as in the reference tutorial i was seeing (screenshot-bottom).
Can someone pls tell me how to fix it. Thankyou!Hello,
I want to use DIC in MATLAB. I tried to import/install NCORR program to MATLAB but I get these two errors (screeshots below) that I need help resolving.
The .cpp files in my PC (screenshot-top) does not appear the same as in the reference tutorial i was seeing (screenshot-bottom).
Can someone pls tell me how to fix it. Thankyou! Hello,
I want to use DIC in MATLAB. I tried to import/install NCORR program to MATLAB but I get these two errors (screeshots below) that I need help resolving.
The .cpp files in my PC (screenshot-top) does not appear the same as in the reference tutorial i was seeing (screenshot-bottom).
Can someone pls tell me how to fix it. Thankyou! ncorr, compiler MATLAB Answers — New Questions